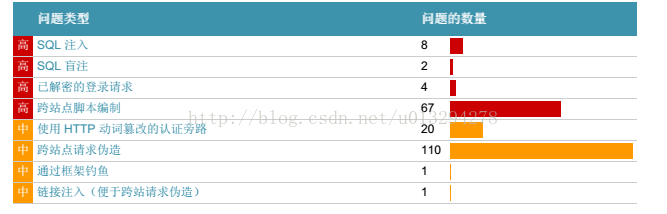
最近手上负责一个的项目要进行等保评测。请的第三方公司采用IBM Security AppScan Standard对项目进行安全测试。测试报告高危漏洞主要包含sql注入、sql盲注、跨站点脚本编制如下图
AppScan破解版安装
首先下载
http://pan.baidu.com/s/1slmcHzR 密码: xtyf
直接点击AppScan_Std_9.0.3.5_Eval_Win.exe安装
安装成功之后把LicenseProvider.dll拷贝到AppScan安装目录。覆盖原来的LicenseProvider.dll
比如我的目录是C:\Program Files (x86)\IBM\AppScan Standard
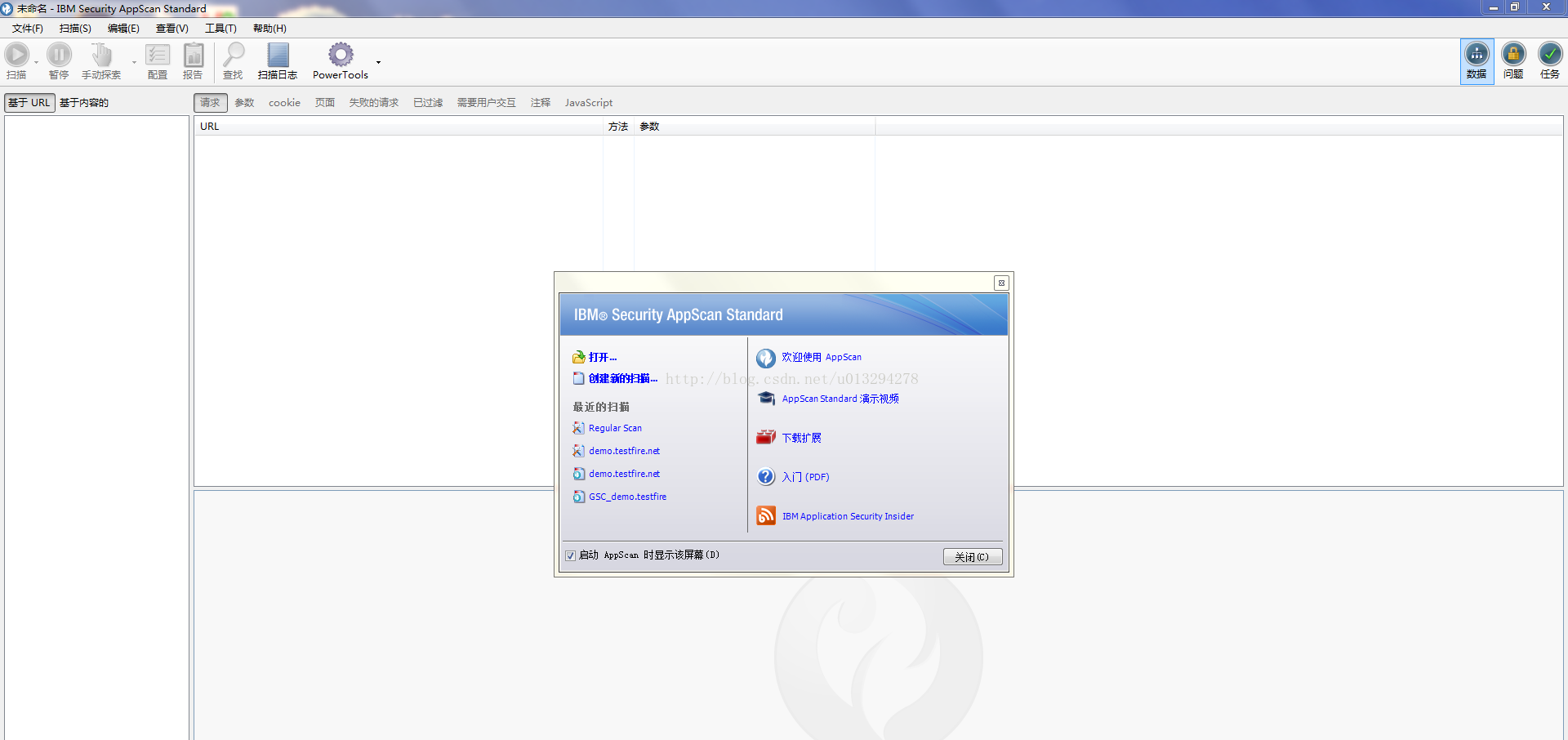
运行AppScan
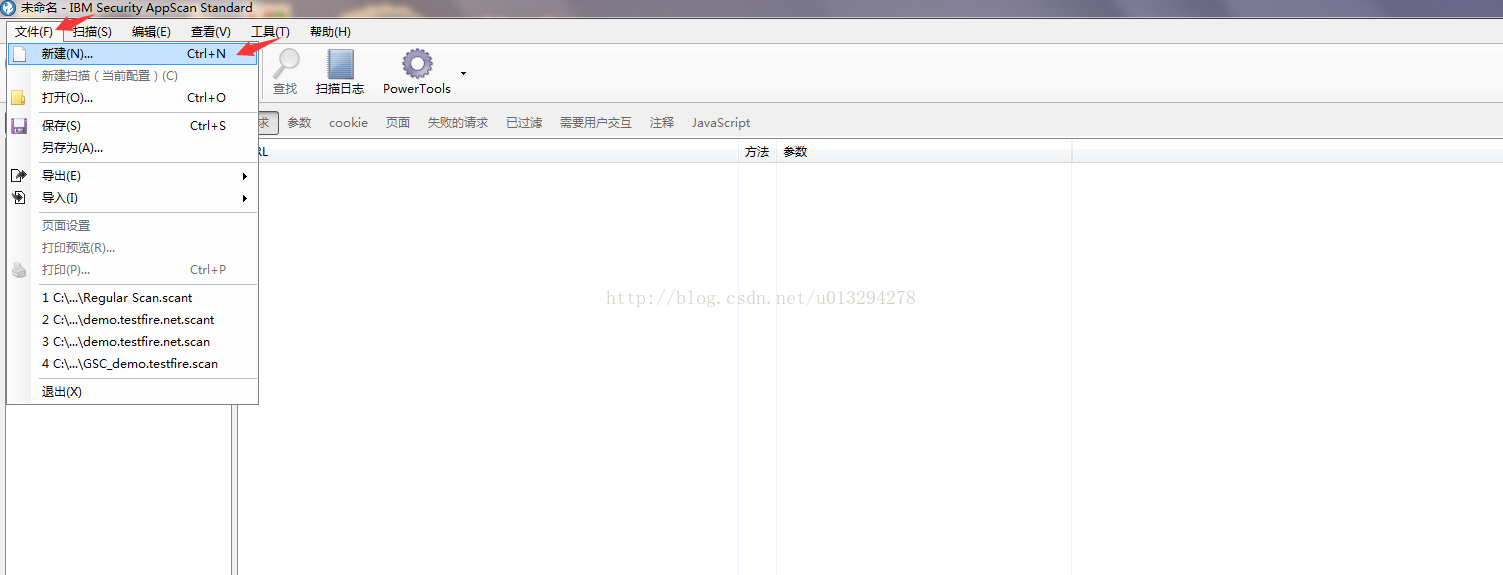
接下来构建一个简单的扫描任务
选择常规扫描,然后一直“下一步“,配置项目URL
登录管理配置,输入你要测试项目的用户名与密码能够成功登录就行。这里的扫描的项目最好是在测试环境进行
成功登录测试项目之后AppScan会记录登录
然后一直点击下一步直到完成
环境定义根据自己的实际情况来设定
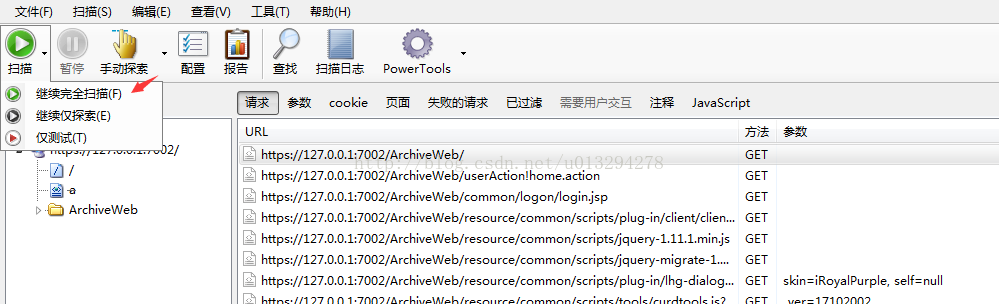
定义好环境点击扫描选择继续完全扫描
至此就默默的等待就OK拉。等扫描完成之后点击报告生成PDF就知道自己的项目存在多少漏洞。
LZ针对扫描的高危漏洞主要修改策略:
1、配置https
2、过滤危险字符
3、配置http-only
4、请求方式更改为post
对于危险字符过滤,可以参考以下过滤逻辑
import java.util.ArrayList;
import java.util.List;
import java.util.regex.Matcher;
import java.util.regex.Pattern;
import org.apache.commons.lang.StringUtils;
/**
* ClassName: XssShieldUtil
* @Description: 处理非法字符
* @author JornTang
* @date 2017年9月6日
*/
public class XssShieldUtil {
private static List<Pattern> patterns = null;
private static List<Pattern> sqlPatterns = null;
/**
* @Description: 获取正则表达式
* @return
* @return List<Object[]>
* @throws
* Pattern.CASE_INSENSITIVE 默认情况下,大小写不敏感的匹配只适用于US-ASCII字符集。这个标志能让表达式忽略大小写进行匹配
* Pattern.MULTILINE 在这种模式下,'^'和'$'分别匹配一行的开始和结束。此外,'^'仍然匹配字符串的开始,'$'也匹配字符串的结束默认情况下,这两个表达式仅仅匹配字符串的开始和结束。
* Pattern.DOTALL 在这种模式下,表达式'.'可以匹配任意字符,包括表示一行的结束符。默认情况下,表达式'.'不匹配行的结束符
* @author JornTang
* @date 2017年9月6日
*/
private static List<Object[]> getXssPatternList() {
List<Object[]> ret = new ArrayList<Object[]>();
//xss脚本编制过滤
ret.add(new Object[]{"<(no)?script[^>]*>.*?</(no)?script>", Pattern.CASE_INSENSITIVE});
ret.add(new Object[]{"(eval\\(\\(.*?\\)\\)|eval\\(.*?\\)|eval|function|aegncy|script)+", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL});
ret.add(new Object[]{"expression\\(\\(.*?\\)\\)", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL});
ret.add(new Object[]{"(javascript:|vbscript:|view-source:|valueOf:.*?)+", Pattern.CASE_INSENSITIVE});
ret.add(new Object[]{"(window\\.location|window\\.|\\.location|document\\.cookie|document\\.|alert\\(.*?\\)|window\\.open\\(|window\\[.*?\\])+", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL});
ret.add(new Object[]{"<+\\s*\\w*\\s*(src|oncontrolselect|oncopy|oncut|ondataavailable|ondatasetchanged|ondatasetcomplete|ondblclick|ondeactivate|ondrag|ondragend|ondragenter|ondragleave|ondragover|ondragstart|ondrop|onerror=|onerroupdate|onfilterchange|onfinish|onfocus|onfocusin|onfocusout|onhelp|onkeydown|onkeypress|onkeyup|onlayoutcomplete|onload|onlosecapture|onmousedown|onmouseenter|onmouseleave|onmousemove|onmousout|onmouseover|onmouseup|onmousewheel|onmove|onmoveend|onmovestart|onabort|onactivate|onafterprint|onafterupdate|onbefore|onbeforeactivate|onbeforecopy|onbeforecut|onbeforedeactivate|onbeforeeditocus|onbeforepaste|onbeforeprint|onbeforeunload|onbeforeupdate|onblur|onbounce|oncellchange|onchange|onclick|oncontextmenu|onpaste|onpropertychange|onreadystatechange|onreset|onresize|onresizend|onresizestart|onrowenter|onrowexit|onrowsdelete|onrowsinserted|onscroll|onselect|onselectionchange|onselectstart|onstart|onstop|onsubmit|onunload)+\\s*=+", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL});
ret.add(new Object[]{"(src|oncontrolselect|oncopy|oncut|ondataavailable|ondatasetchanged|ondatasetcomplete|ondblclick|ondeactivate|ondrag|ondragend|ondragenter|ondragleave|ondragover|ondragstart|ondrop|onerror=|onerroupdate|onfilterchange|onfinish|onfocus|onfocusin|onfocusout|onhelp|onkeydown|onkeypress|onkeyup|onlayoutcomplete|onload|onlosecapture|onmousedown|onmouseenter|onmouseleave|onmousemove|onmousout|onmouseover|onmouseup|onmousewheel|onmove|onmoveend|onmovestart|onabort|onactivate|onafterprint|onafterupdate|onbefore|onbeforeactivate|onbeforecopy|onbeforecut|onbeforedeactivate|onbeforeeditocus|onbeforepaste|onbeforeprint|onbeforeunload|onbeforeupdate|onblur|onbounce|oncellchange|onchange|onclick|oncontextmenu|onpaste|onpropertychange|onreadystatechange|onreset|onresize|onresizend|onresizestart|onrowenter|onrowexit|onrowsdelete|onrowsinserted|onscroll|onselect|onselectionchange|onselectstart|onstart|onstop|onsubmit|onunload)+\\s*=+", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL});
return ret;
}
/**
* @Description: 获取sql注入正则表达式
* @return
* @return List<Object[]>
* @throws
* @author JornTang
* @date 2017年9月20日
*/
private static List<Object[]> getSqlPatternList() {
List<Object[]> ret = new ArrayList<Object[]>();
//sql注入特殊字符过滤
//|chr|mid|char|use|net
ret.add(new Object[]{"(and |exec |execute |insert |select |create |delete |update |table |master |truncate |declare|sitename|substr\\(|drop table| count\\(| from )+", Pattern.CASE_INSENSITIVE});
ret.add(new Object[]{"(xp_cmdshell| like |grant |group_concat |column_name |information_schema.columns)+", Pattern.CASE_INSENSITIVE});
ret.add(new Object[]{"(table_schema|union |union all |where |order by|truncate |declare |or )+", Pattern.CASE_INSENSITIVE});
return ret;
}
public static void main(String[] args) {
boolean value = false;
value = XssShieldUtil.stripXss("eval()");
System.out.println("type-1: '" + value + "'");
}
/**
* @Description: 获取sql注入patterns
* @return
* @return List<Pattern>
* @throws
* @author JornTang
* @date 2017年9月20日
*/
private static List<Pattern> getSqlPatterns(){
if (sqlPatterns == null) {
List<Pattern> list = new ArrayList<Pattern>();
for(Object[] arr : getSqlPatternList()) {
String regex = (String)arr[0];
Integer flag = (Integer)arr[1];
list.add(Pattern.compile(regex, flag));
}
sqlPatterns = list;
}
return sqlPatterns;
}
private static List<Pattern> getPatterns() {
if (patterns == null) {
List<Pattern> list = new ArrayList<Pattern>();
String regex = null;
Integer flag = null;
int arrLength = 0;
for(Object[] arr : getXssPatternList()) {
// arrLength = arr.length;
// for(int i = 0; i < arrLength; i++) {
//
// }
regex = (String)arr[0];
flag = (Integer)arr[1];
list.add(Pattern.compile(regex, flag));
}
patterns = list;
}
return patterns;
}
/**
* @Description: 检测sql注入特殊字符
* @param value
* @return
* @return boolean
* @throws
* @author JornTang
* @date 2017年9月20日
*/
public static boolean stripSql(String value){
boolean flag= false;
if(StringUtils.isNotBlank(value)) {
Matcher matcher = null;
for(Pattern pattern : getSqlPatterns()) {
matcher = pattern.matcher(value);
// 匹配
boolean ism= matcher.find();
if(ism) {
flag= true;
break;
}
}
}
return flag;
}
public static boolean stripXss(String value) {
boolean flag= false;
if(StringUtils.isNotBlank(value)) {
Matcher matcher = null;
for(Pattern pattern : getPatterns()) {
matcher = pattern.matcher(value);
// 匹配
boolean ism= matcher.find();
if(ism) {
flag= true;
break;
// 删除相关字符串
//value = matcher.replaceAll("");
}
}
//value = value.replaceAll("<", "<").replaceAll(">", ">");
}
// if (LOG.isDebugEnabled())
// LOG.debug("strip value: " + value);
return flag;
}
}
一旦发现用户输入包含以上规则,直接返回响应。提示用户存在危险输入,禁止操作
以上修改基本测试不会再出现高危漏洞