简介
Snort是美国Sourcefire公司开发的发布在GPL v2下的IDS(Intrusion Detection System)软件,在1998年,Marty Roesch先生用C语言开发了开放源代码(Open Source)的入侵检测系统Snort.直至今天,Snort已发展成为一个多平台(Multi-Platform),实时(Real-Time)流量分析,网络IP数据包(Pocket)记录等特性的强大的网络入侵检测/防御系统(Network Intrusion Detection/Prevention System),即NIDS/NIPS
工作原理
Snort通过在网络TCP/IP的5层结构的数据链路层进行抓取网络数据包,抓包时需将网卡设置为混杂模式,根据操作系统的不同采用libpcap或winpcap函数从网络中捕获数据包;然后将捕获的数据包送到包解码器进行解码。网络中的数据包有可能是以太网包、令牌环包、TCP/IP包、802.11包等格式。在这一过程包解码器将其解码成Snort认识的统一的格式;之后就将数据包送到预处理器进行处理,预处理包括能分片的数据包进行重新组装,处理一些明显的错误等问题。预处理的过程主要是通过插件来完成,比如Http预处理器完成对Http请求解码的规格化,Frag2事务处理器完成数据包的组装,Stream4预处理器用来使Snort状态化,端口扫描预处理器能检测端口扫描的能力等;对数据包进行了解码,过滤,预处理后,进入了Snort的最重要一环,进行规则的建立及根据规则进行检测。规则检测是Snort中最重要的部分,作用是检测数据包中是否包含有入侵行为。例如规则alert tcp any any ->202.12.1.0/24 80(msg:”misc large tcp packet”;dsize:>3000;)这条规则的意思是,当一个流入202.12.1.0这个网段的TCP包长度超过3000B时就发出警报。规则语法涉及到协议的类型、内容、长度、报头等各种要素。处理规则文件的时候,用三维链表来存规则信息以便和后面的数据包进行匹配,三维链表一旦构建好了,就通过某种方法查找三维链表并进行匹配和发生响应。规则检测的处理能力需要根据规则的数量,运行Snort机器的性能,网络负载等因素决定;最后一步就是输出模块,经过检测后的数据包需要以各种形式将结果进行输出,输出形式可以是输出到alert文件、其它日志文件、数据库UNIX域或Socket等。
安装(ubuntu14.04)
安装snort前,首先需要安装一些依赖包 数据采集库(DAQ))用于一个调用包捕获库的抽象层
https://www.snort.org/downloads/snort/daq-2.0.6.tar.gz
解压并运行./configure、make、make install来安装DAQ。然而,DAQ要求其他的工具,因此,./configure脚本会生成下面的错误
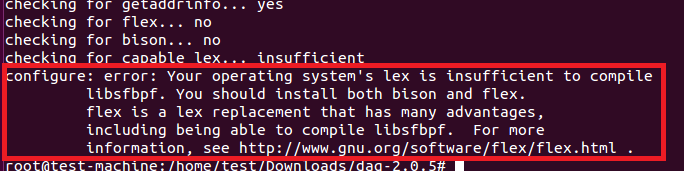
因此在安装DAQ之前先安装flex/bison和libcap
apt-get install flex apt-get install bison apt-get install libcap-dev
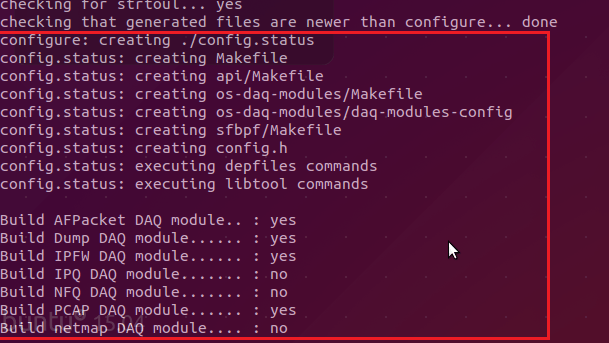
安装完必要的工具后,再次运行./configure脚本,将会显示下面的输出, 然后使用make和make install 命令进行编译

成功安装DAQ之后,我们现在安装snort
https://www.cnblogs.com/lcamry/p/6339475.html
apt-get install snort
snort命令参数详解
snort -[options] <filters>

root@ubuntu-virtual-machine:~# snort --help ,,_ -*> Snort! <*- o" )~ Version 2.9.6.0 GRE (Build 47) '''' By Martin Roesch & The Snort Team: http://www.snort.org/snort/snort-team Copyright (C) 2014 Cisco and/or its affiliates. All rights reserved. Copyright (C) 1998-2013 Sourcefire, Inc., et al. Using libpcap version 1.5.3 Using PCRE version: 8.31 2012-07-06 Using ZLIB version: 1.2.8 USAGE: snort [-options] <filter options> Options: -A #设置报警模式 Set alert mode: fast, full, console, test or none (alert file alerts only) "unsock" enables UNIX socket logging (experimental). -b #用二进制文件保存网络数据包,以应付高吞吐量的网络 Log packets in tcpdump format (much faster!) -B <mask> #将IP地址信息抹掉,去隐私化 Obfuscated IP addresses in alerts and packet dumps using CIDR mask -c <rules> #使用配置文件规则,使得snort进入IDS模式 Use Rules File <rules> -C #打印出只有字符数据的有效载荷(无十六进制) Print out payloads with character data only (no hex) -d #显示包的应用层数据 Dump the Application Layer -D #后台运行snort,如无指定,Alerts将写到/var/log/snort/alert Run Snort in background (daemon) mode -e #显示数据链路层信息 Display the second layer header info -f #激活PCAP行缓冲(line buffering) Turn off fflush() calls after binary log writes -F <bpf> #指定BPF过滤器 Read BPF filters from file <bpf> -g <gname> #初始化Snort后以组ID(group ID)运行 Run snort gid as <gname> group (or gid) after initialization -G <0xid> #为事件生成设置一个基础事件id值 Log Identifier (to uniquely id events for multiple snorts) -h <hn> #设置本地网络为hn,如192.168.1.0/24 Set home network = <hn> (for use with -l or -B, does NOT change $HOME_NET in IDS mode) -H # Make hash tables deterministic. -i <if> #设置网络接口为<if>。可以用-W选项查询网络接口列表,然后用接口序号index指定接口。如-i 2 Listen on interface <if> -I #报警时附加上接口信息 Add Interface name to alert output -k <mode> #为all,noip,notcp,noudp,noicmp,or none设置校验和模式 Checksum mode (all,noip,notcp,noudp,noicmp,none) -K <mode> #设置保存文件的格式:pcap,ascii, none。pcap是默认格式,同于-b选项的格式。ascii是老的模式格式。none则关闭数据包记录 Logging mode (pcap[default],ascii,none) -l <ld> #设置数据包文件存放目录<ld>。默认目录是/var/log/snort Log to directory <ld> -L <file> #设置二进制输出文件的文件名为<fn> Log to this tcpdump file -M #当以非后台模式daemon运行时,保存信息到syslog Log messages to syslog (not alerts) -m <umask> #设置snort输出文件的权限位 Set umask = <umask> -n <cnt> #出来<count>个报文后终止程序 Exit after receiving <cnt> packets -N #关闭保存日志包功能 Turn off logging (alerts still work) -O #在ASCII数据包捕获模式下混淆IP地址 Obfuscate the logged IP addresses -p #关闭混杂模式 Disable promiscuous mode sniffing -P <snap> #设置snaplen,默认值是当前网卡的MTU Set explicit snaplen of packet (default: 1514) -q #安静模式,不显示标志和状态报告 Quiet. Don't show banner and status report -Q #当在线(in-line)运行时,从iptables/IPQ中读取数据包 Enable inline mode operation. -r <tf> #从pcap格式的文件中读取数据包 Read and process tcpdump file <tf> -R <id> # 为snort pidfile增加下标 Include 'id' in snort_intf<id>.pid file name -s #使snort把报警消息发送到syslog,默认的设备是LOG_AUTHPRIV和LOG_ALERT。可以修改snort.conf文件修改其配置 Log alert messages to syslog -S <n=v> #为变量n设置值为v Set rules file variable n equal to value v -t <dir> #初始化后将Snort的根目录改变为<chroot> Chroots process to <dir> after initialization -T # 以自检测模式启动Snort Test and report on the current Snort configuration -u <uname> #初始化后改变Snort的UID Run snort uid as <uname> user (or uid) after initialization -U #在时间戳上用UTC时间代替本地时间 Use UTC for timestamps -v #从网络上读出数据包然后显示在你的控制台上 Be verbose -V #查看版本号并退出 Show version number -X #显示包括数据链路层的原始数据包 Dump the raw packet data starting at the link layer -x #如果出现Snort配置问题,请退出 Exit if Snort configuration problems occur -y #在时间戳里显示年份 Include year in timestamp in the alert and log files -Z <file> #设置性能监视器(perfmon)路径 Set the performonitor preprocessor file path and name -? #帮助信息 Show this information <Filter Options> are standard BPF options, as seen in TCPDump Longname options and their corresponding single char version --logid <0xid> Same as -G --perfmon-file <file> Same as -Z --pid-path <dir> #为SnortPID文件指定路径 Specify the directory for the Snort PID file --snaplen <snap> Same as -P --help Same as -? --version Same as -V --alert-before-pass #在pass之前处理alert, drop, sdrop, or reject. 默认是pass before alert, drop, etc. Process alert, drop, sdrop, or reject before pass, default is pass before alert, drop,... --treat-drop-as-alert #将drop处理为alert Converts drop, sdrop, and reject rules into alert rules during startup --treat-drop-as-ignore Use drop, sdrop, and reject rules to ignore session traffic when not inline. --process-all-events Process all queued events (drop, alert,...), default stops after 1st action group --enable-inline-test Enable Inline-Test Mode Operation --dynamic-engine-lib <file> Load a dynamic detection engine --dynamic-engine-lib-dir <path> Load all dynamic engines from directory --dynamic-detection-lib <file> Load a dynamic rules library --dynamic-detection-lib-dir <path> Load all dynamic rules libraries from directory --dump-dynamic-rules <path> Creates stub rule files of all loaded rules libraries --dynamic-preprocessor-lib <file> Load a dynamic preprocessor library --dynamic-preprocessor-lib-dir <path> Load all dynamic preprocessor libraries from directory --dynamic-output-lib <file> Load a dynamic output library --dynamic-output-lib-dir <path> Load all dynamic output libraries from directory --create-pidfile Create PID file, even when not in Daemon mode --nolock-pidfile Do not try to lock Snort PID file --no-interface-pidfile Do not include the interface name in Snort PID file --disable-attribute-reload-thread Do not create a thread to reload the attribute table --pcap-single <tf> #读取单个pcap文件 Same as -r. --pcap-file <file> #读取多个pcap文件 file that contains a list of pcaps to read - read mode is implied. --pcap-list "<list>" #以列表的形式在命令行读取 a space separated list of pcaps to read - read mode is implied. --pcap-dir <dir> #读取指定目录下的所有pcap文件 a directory to recurse to look for pcaps - read mode is implied. --pcap-filter <filter> #用过滤方式读取pcap文件 filter to apply when getting pcaps from file or directory. --pcap-no-filter #用非过滤方式读取pcap文件 reset to use no filter when getting pcaps from file or directory. --pcap-loop <count> this option will read the pcaps specified on command line continuously. for <count> times. A value of 0 will read until Snort is terminated. --pcap-reset if reading multiple pcaps, reset snort to post-configuration state before reading next pcap. --pcap-reload if reading multiple pcaps, reload snort config between pcaps. --pcap-show print a line saying what pcap is currently being read. --exit-check <count> Signal termination after <count> callbacks from DAQ_Acquire(), showing the time it takes from signaling until DAQ_Stop() is called. --conf-error-out Same as -x --enable-mpls-multicast Allow multicast MPLS --enable-mpls-overlapping-ip Handle overlapping IPs within MPLS clouds --max-mpls-labelchain-len Specify the max MPLS label chain --mpls-payload-type Specify the protocol (ipv4, ipv6, ethernet) that is encapsulated by MPLS --require-rule-sid Require that all snort rules have SID specified. --daq <type> Select packet acquisition module (default is pcap). --daq-mode <mode> Select the DAQ operating mode. --daq-var <name=value> Specify extra DAQ configuration variable. --daq-dir <dir> Tell snort where to find desired DAQ. --daq-list[=<dir>] List packet acquisition modules available in dir. Default is static modules only. --dirty-pig Don't flush packets and release memory on shutdown. --cs-dir <dir> Directory to use for control socket. --ha-peer Activate live high-availability state sharing with peer. --ha-out <file> Write high-availability events to this file. --ha-in <file> Read high-availability events from this file on startup (warm-start).
工作原理(嗅探器、数据包记录器、网络入侵检测系统)
嗅探器
snort从网络上读出数据包然后显示在你的控制台上

数据包记录器
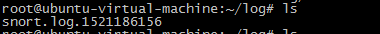
如果要把所有的包记录到硬盘上,你需要指定一个日志目录,snort就会自动记录数据包
snort -dev -l ./log
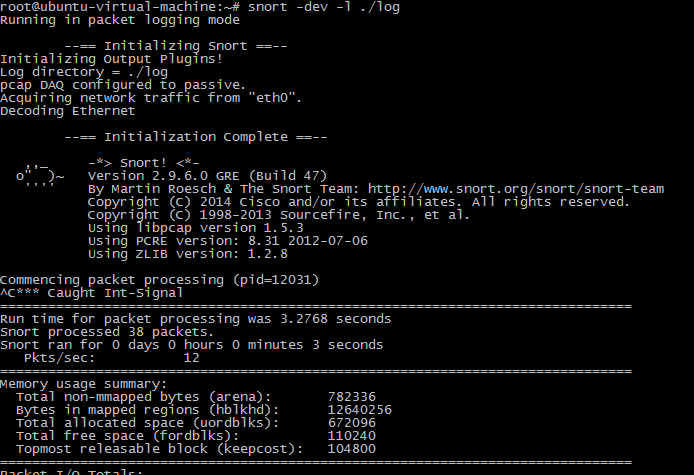
snort -dev -l ./log -h 192.168.1.0/24 这个命令告诉snort把进入C类网络192.168.1的所有包的数据链路、TCP/IP以及应用层的数据记录到目录./log中。
网络入侵检测系统
snort最重要的用途还是作为网络入侵检测系统(NIDS),使用下面命令行可以启动这种模式
snort -dev -l ./log -h 192.168.1.0/24 -c snort.conf snort.conf是规则集文件。snort会对每个包和规则集进行匹配,发现这样的包就采取相应的行动。如果你不指定输出目录,snort就输出到/var/log/snort目录。 注意:如果你想长期使用snort作为自己的入侵检测系统,最好不要使用-v选项。因为使用这个选项,使snort向屏幕上输出一些信息,会大大降低snort的处理速度,从而在向显示器输出的过程中丢弃一些包。 此外,在绝大多数情况下,也没有必要记录数据链路层的包头,所以-e选项也可以不用 snort -d -h 192.168.1.0/24 -l ./log -c snort.conf



