Spring Security自定义登录认证校验用户名、密码,自定义密码加密方式,以及在前后端分离的情况下认证失败或成功处理返回json格式数据等
Spring Security 自定义登录认证处理
基本环境
- spring-boot 2.4.1 (最新版本,如有问题,后期会调整)
- mybatis-plus 2.2.0 (没有采用最新版本,后期会弄个简单的代码生成器)
- mysql
- maven项目
数据库用户信息表t_sys_user 本人采用的是5.6还是5.7版本来的,不是8.0
SET NAMES utf8mb4; SET FOREIGN_KEY_CHECKS = 0; -- ---------------------------- -- Table structure for t_sys_user -- ---------------------------- DROP TABLE IF EXISTS `t_sys_user`; CREATE TABLE `t_sys_user` ( `id` int(11) NOT NULL AUTO_INCREMENT COMMENT '主键ID', `username` varchar(100) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '账号', `password` varchar(100) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '登录密码', `nick_name` varchar(50) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '昵称', `sex` varchar(1) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '性别 0:男 1:女', `phone` varchar(11) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '手机号码', `email` varchar(50) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '邮箱', `avatar` varchar(255) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '头像', `flag` varchar(1) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '状态', `salt` varchar(50) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '盐值', `token` varchar(200) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT 'token', `qq_oppen_id` varchar(100) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT 'QQ 第三方登录Oppen_ID唯一标识', `pwd` varchar(100) CHARACTER SET utf8 COLLATE utf8_general_ci NULL DEFAULT NULL COMMENT '明文密码', `gmt_create` datetime(0) NULL DEFAULT NULL COMMENT '创建时间', `gmt_modified` datetime(0) NULL DEFAULT NULL COMMENT '更新时间', PRIMARY KEY (`id`) USING BTREE ) ENGINE = InnoDB AUTO_INCREMENT = 4 CHARACTER SET = utf8 COLLATE = utf8_general_ci COMMENT = '系统管理-用户基础信息表' ROW_FORMAT = DYNAMIC; -- ---------------------------- -- Records of t_sys_user -- ---------------------------- INSERT INTO `t_sys_user` VALUES (1, 'admin', '97ba1ef7f148b2aec1c61303a7d88d0967825495', '郑某某', '0', '15183303003', '10086@qq.com', 'http://qzapp.qlogo.cn/qzapp/101536330/86F96F92387D69BD7659C4EC3CD6BD69/100', '1', 'zhengqing', '20820cef877355ad636b9e938c533e5cc1152e4f', '', '123456', '2019-05-05 16:09:06', '2019-10-23 17:26:30'); INSERT INTO `t_sys_user` VALUES (2, 'test', '97ba1ef7f148b2aec1c61303a7d88d0967825495', '测试号', '0', '10000', '10000@qq.com', 'https://wpimg.wallstcn.com/f778738c-e4f8-4870-b634-56703b4acafe.gif', '1', 'zhengqing', '2425fb04b4bcb140e05d22d46baa9c257ceed879', NULL, '123456', '2019-05-05 16:15:06', '2019-10-23 16:56:38'); SET FOREIGN_KEY_CHECKS = 1;
到此步需要使用的pom.xml文件
<properties> <java.version>1.8</java.version> <project.build.sourceEncoding>UTF-8</project.build.sourceEncoding> <project.reporting.outputEncoding>UTF-8</project.reporting.outputEncoding> <spring-boot.version>2.4.1</spring-boot.version> </properties> <dependencies> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-web</artifactId> </dependency> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-test</artifactId> <scope>test</scope> </dependency> <!-- Spring Security依赖 --> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-security</artifactId> </dependency> <!-- mybatis-plus begin =================================== --> <dependency> <groupId>com.baomidou</groupId> <artifactId>mybatis-plus-boot-starter</artifactId> <version>2.2.0</version> </dependency> <!-- ========================= 数据库相关 ========================== --> <dependency> <groupId>mysql</groupId> <artifactId>mysql-connector-java</artifactId> </dependency> <!-- 阿里数据库连接池 --> <dependency> <groupId>com.alibaba</groupId> <artifactId>druid</artifactId> <version>1.0.18</version> </dependency> <!-- swagger --> <dependency> <groupId>io.springfox</groupId> <artifactId>springfox-swagger2</artifactId> <version>2.6.1</version> <exclusions> <exclusion> <groupId>org.mapstruct</groupId> <artifactId>mapstruct</artifactId> </exclusion> </exclusions> </dependency> <!-- swagger-ui --> <dependency> <groupId>io.springfox</groupId> <artifactId>springfox-swagger-ui</artifactId> <version>2.6.1</version> </dependency> <dependency> <groupId>io.springfox</groupId> <artifactId>springfox-bean-validators</artifactId> <version>2.6.1</version> </dependency> <!-- lombok --> <dependency> <groupId>org.projectlombok</groupId> <artifactId>lombok</artifactId> <optional>true</optional> </dependency> <!-- 阿里FastJson转换工具依赖 --> <dependency> <groupId>com.alibaba</groupId> <artifactId>fastjson</artifactId> <version>1.2.13</version> </dependency> <!-- AOP依赖 【注:系统日记需要此依赖】 --> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-aop</artifactId> </dependency> <!-- Hibernate Validator提供的注解进行参数校验 --> <dependency> <groupId>javax.validation</groupId> <artifactId>validation-api</artifactId> <version>2.0.1.Final</version> <optional>true</optional> </dependency> <dependency> <groupId>org.hibernate.validator</groupId> <artifactId>hibernate-validator</artifactId> <version>6.0.18.Final</version> </dependency> </dependencies> <dependencyManagement> <dependencies> <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-dependencies</artifactId> <version>${spring-boot.version}</version> <type>pom</type> <scope>import</scope> </dependency> </dependencies> </dependencyManagement> <build> <plugins> <plugin> <groupId>org.apache.maven.plugins</groupId> <artifactId>maven-compiler-plugin</artifactId> <version>3.8.1</version> <configuration> <source>1.8</source> <target>1.8</target> <encoding>UTF-8</encoding> </configuration> </plugin> </plugins> </build>
yml的配置
server: port: 8083 spring: application: name: security # 配置数据源 datasource: # MySQL在高版本需要指明是否进行SSL连接 解决则加上 &useSSL=false url: jdbc:mysql://127.0.0.1:3306/white_jotter?allowMultiQueries=true&useUnicode=true&characterEncoding=UTF8&zeroDateTimeBehavior=convertToNull&useSSL=false&serverTimezone=UTC name: white_jotter username: root password: 123456 # mysql5连接驱动 driverClassName: com.mysql.cj.jdbc.Driver maxActive: 20 initialSize: 1 maxWait: 60000 minIdle: 1 timeBetweenEvictionRunsMillis: 60000 minEvictableIdleTimeMillis: 300000 validationQuery: select 'x' testWhileIdle: true testOnBorrow: false testOnReturn: false poolPreparedStatements: true maxOpenPreparedStatements: 20 security: user: name: admin # 用户名 password: 123456 # 密码 # 关闭安全验证 management: security: enabled: false # mybatis-plus相关配置 mybatis-plus: # xml扫描,多个目录用逗号或者分号分隔(告诉 Mapper 所对应的 XML 文件位置) mapper-locations: classpath:cn/com/sercurity/cyy/**/mapper/xml/*Mapper.xml # 以下配置均有默认值,可以不设置 global-config: #主键类型 0:"数据库ID自增", 1:"用户输入ID",2:"全局唯一ID (数字类型唯一ID)", 3:"全局唯一ID UUID"; id-type: 0 #字段策略 0:"忽略判断",1:"非 NULL 判断"),2:"非空判断" field-strategy: 2 #驼峰下划线转换 db-column-underline: true #刷新mapper 调试神器 refresh-mapper: false #数据库大写下划线转换 #capital-mode: true #序列接口实现类配置 #key-generator: com.baomidou.springboot.xxx #逻辑删除配置 #logic-delete-value: 0 # 逻辑已删除值(默认为 1) #logic-not-delete-value: 1 # 逻辑未删除值(默认为 0) #自定义填充策略接口实现 # meta-object-handler: xxxxxx #自定义SQL注入器 #sql-injector: com.baomidou.springboot.xxx configuration: # 是否开启自动驼峰命名规则映射:从数据库列名到Java属性驼峰命名的类似映射 map-underscore-to-camel-case: true cache-enabled: false # 如果查询结果中包含空值的列,则 MyBatis 在映射的时候,不会映射这个字段 # call-setters-on-nulls: true # 这个配置会将执行的sql打印出来,在开发或测试的时候可以用 # log-impl: org.apache.ibatis.logging.stdout.StdOutImpl # 解决oracle更新数据为null时无法转换报错,mysql不会出现此情况 jdbc-type-for-null: 'null' cyy: swagger: title: 测试项目demo接口文档 description: 测试项目demo接口文档 version: 1.0.0 termsOfServiceUrl: contactName: contactUrl: contactEmail: license: licenseUrl: #安全认证 auth: # token过期时间(分钟) tokenExpireTime: 60 # 用户选择保存登录状态对应token过期时间(天) saveLoginTime: 7 # 限制用户登陆错误次数(次) loginTimeLimit: 10 # 错误超过次数后多少分钟后才能继续登录(分钟) loginAfterTime: 10 ignoreUrls: - /login - /api/system/user/getCurrentUserInfo - /index - /logout - /swagger-ui.html # - /swagger-resources/** - /swagger-resources/configuration/ui - /swagger-resources - /v2/api-docs - /swagger-resources/configuration/security # - /swagger/** # - /**/v2/api-docs - /**/*.js - /**/*.css - /**/*.png - /**/*.ico
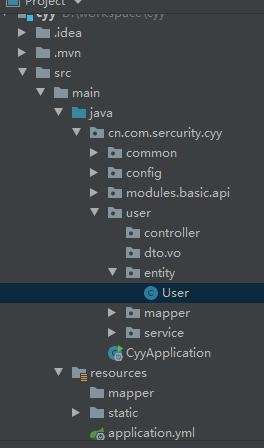
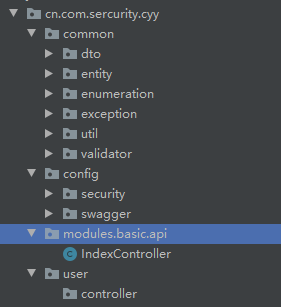
接下来的代码可能会有些乱,在这里贴一下项目目录吧,方便大家查看
t_sys_user表的实体类
import cn.com.sercurity.cyy.common.entity.BaseEntity; import cn.com.sercurity.cyy.common.validator.Create; import cn.com.sercurity.cyy.common.validator.FieldRepeatValidator; import cn.com.sercurity.cyy.common.validator.Update; import com.baomidou.mybatisplus.annotations.TableField; import com.baomidou.mybatisplus.annotations.TableId; import com.baomidou.mybatisplus.annotations.TableName; import com.baomidou.mybatisplus.enums.IdType; import io.swagger.annotations.ApiModel; import io.swagger.annotations.ApiModelProperty; import lombok.Data; import org.hibernate.validator.constraints.Length; import javax.validation.constraints.Email; import javax.validation.constraints.NotBlank; import javax.validation.constraints.NotNull; import javax.validation.constraints.Pattern; import java.io.Serializable; /** * <p> * user实体类 * </p> * * @author cyy * @since 2020-12-30 13:34 */ /** * <p> 系统管理-用户基础信息表 </p> * * @author : cyy * @date : 2020/12/30 15:40 */ @Data @ApiModel(description = "系统管理-用户基础信息表") @TableName("t_sys_user") /** * 对注解分组的排序,可以通脱他判断先后顺序 * @GroupSequence({FieldRepeatValidator.class,NotNull.class, Default.class}) */ @FieldRepeatValidator(field = "username", message = "账号重复,请重新输入账号!") public class User extends BaseEntity<User> { private static final long serialVersionUID = 1L; /** * 主键ID groups:标识在更新的时候才能验证非空 */ @ApiModelProperty(value = "主键ID") @TableId(value="id", type= IdType.AUTO) @NotNull(message = "用户id不能为空", groups={Update.class}) private Integer id; /** * 账号 */ @ApiModelProperty(value = "账号") @TableField("username") @NotBlank(message = "账号不能为空", groups = {Create.class, Update.class}) @Length(max = 100, message = "账号不能超过100个字符") @Pattern(regexp = "^[\\u4E00-\\u9FA5A-Za-z0-9\\*]*$", message = "账号限制:最多100字符,包含文字、字母和数字") private String username; /** * 登录密码 */ @ApiModelProperty(value = "登录密码") @TableField("password") private String password; /** * 明文密码 - QQ第三方授权登录时用 */ @ApiModelProperty(value = "明文密码") @TableField("pwd") @NotBlank(message = "密码不能为空") // @FieldRepeatValidator(className = "com.zhengqing.modules.system.entity.User", field = "pwd", message = "密码重复!") // @FieldRepeatValidator(className = "com.zhengqing.modules.system.entity.User", field = "pwd", message = "密码重复!",groups={FieldRepeatValidator.class}) private String pwd; /** * 昵称 */ @ApiModelProperty(value = "昵称") @TableField("nick_name") @NotBlank(message = "昵称不能为空") private String nickName; /** * 性别 0:男 1:女 */ @ApiModelProperty(value = "性别 0:男 1:女") @TableField("sex") private String sex; /** * 手机号码 */ @ApiModelProperty(value = "手机号码") @TableField("phone") @NotBlank(message = "手机号不能为空") @Pattern(regexp = "^[1][3,4,5,6,7,8,9][0-9]{9}$", message = "手机号格式有误") private String phone; /** * 邮箱 */ @ApiModelProperty(value = "邮箱") @TableField("email") @NotBlank(message = "联系邮箱不能为空") @Email(message = "邮箱格式不对") private String email; /** * 头像 */ @ApiModelProperty(value = "头像") @TableField("avatar") private String avatar; /** * 状态 */ @ApiModelProperty(value = "状态") @TableField("flag") private String flag; /** * 盐值 */ @ApiModelProperty(value = "盐值") @TableField("salt") private String salt; /** * token */ @ApiModelProperty(value = "token") @TableField("token") private String token; @ApiModelProperty(value = "QQ 第三方登录Oppen_ID唯一标识") @TableField("qq_oppen_id") private String qqOppenId; @Override protected Serializable pkVal() { return this.id; } }
import com.baomidou.mybatisplus.activerecord.Model; import com.baomidou.mybatisplus.annotations.TableField; import com.baomidou.mybatisplus.enums.FieldFill; import io.swagger.annotations.ApiModelProperty; import lombok.Getter; import lombok.Setter; import java.util.Date; @Getter @Setter public abstract class BaseEntity<T extends Model> extends BaseAddEntity<T> { /** * 修改时间 - 过去分词表示被动更新 */ @ApiModelProperty(value = "修改时间") @TableField(value = "gmt_modified", fill = FieldFill.INSERT_UPDATE) private Date gmtModified; }
import com.baomidou.mybatisplus.activerecord.Model; import com.baomidou.mybatisplus.annotations.TableField; import com.baomidou.mybatisplus.enums.FieldFill; import io.swagger.annotations.ApiModelProperty; import lombok.Getter; import lombok.Setter; import javax.validation.constraints.Past; import java.util.Date; @Getter @Setter public abstract class BaseAddEntity<T extends Model> extends Model<T>{ /** * 创建日期 - 现在时表示主动创建 */ @ApiModelProperty(value = "创建日期") @TableField(value = "gmt_create", fill = FieldFill.INSERT) @Past(message = "创建时间必须是过去时间") private Date gmtCreate; }
import javax.validation.groups.Default; /** * <p> 使用groups的校验 </p> * * @description : 同一个对象要复用,比如UserDTO在更新时候要校验userId,在保存的时候不需要校验userId,在两种情况下都要校验username,那就用上groups了 * 在需要校验的地方@Validated声明校验组 ` update(@RequestBody @Validated(Update.class) UserDTO userDTO) ` * 在DTO中的字段上定义好groups = {}的分组类型 ` @NotNull(message = "用户id不能为空", groups = Update.class) 或 groups = {Create.class, Update.class} * private Long userId; ` * 【注】注意:在声明分组的时候尽量加上 extend javax.validation.groups.Default 否则,在你声明@Validated(Update.class)的时候,就会出现你在默认没添加groups = {}的时候的校验组@Email(message = "邮箱格式不对"),会不去校验,因为默认的校验组是groups = {Default.class}.*/ public interface Create extends Default { }
import javax.validation.groups.Default; /** * <p> 使用groups的校验 </p> * * @description : 同一个对象要复用,比如UserDTO在更新时候要校验userId,在保存的时候不需要校验userId,在两种情况下都要校验username,那就用上groups了 * 在需要校验的地方@Validated声明校验组 ` update(@RequestBody @Validated(Update.class) UserDTO userDTO) ` * 在DTO中的字段上定义好groups = {}的分组类型 ` @NotNull(message = "用户id不能为空", groups = Update.class) 或 groups = {Create.class, Update.class} * private Long userId; ` * 【注】注意:在声明分组的时候尽量加上 extend javax.validation.groups.Default 否则,在你声明@Validated(Update.class)的时候,就会出现你在默认没添加groups = {}的时候的校验组@Email(message = "邮箱格式不对"),会不去校验,因为默认的校验组是groups = {Default.class}*/ public interface Update extends Default{ }
import javax.validation.Constraint; import javax.validation.Payload; import java.lang.annotation.*; /** * <p> 自定义字段对应数据库内容重复校验 注解 </p> * */ // 元注解: 给其他普通的标签进行解释说明 【@Retention、@Documented、@Target、@Inherited、@Repeatable】 @Documented /** * 指明生命周期: * RetentionPolicy.SOURCE 注解只在源码阶段保留,在编译器进行编译时它将被丢弃忽视。 * RetentionPolicy.CLASS 注解只被保留到编译进行的时候,它并不会被加载到 JVM 中。 * RetentionPolicy.RUNTIME 注解可以保留到程序运行的时候,它会被加载进入到 JVM 中,所以在程序运行时可以获取到它们。 */ @Retention(RetentionPolicy.RUNTIME) /** * 指定注解运用的地方: * ElementType.ANNOTATION_TYPE 可以给一个注解进行注解 * ElementType.CONSTRUCTOR 可以给构造方法进行注解 * ElementType.FIELD 可以给属性进行注解 * ElementType.LOCAL_VARIABLE 可以给局部变量进行注解 * ElementType.METHOD 可以给方法进行注解 * ElementType.PACKAGE 可以给一个包进行注解 * ElementType.PARAMETER 可以给一个方法内的参数进行注解 * ElementType.TYPE 可以给一个类型进行注解,比如类、接口、枚举 * @Repeatable(LinkVals.class)(可重复注解同一字段,或者类,java1.8后支持) * @author : cyy */ @Target({ElementType.PARAMETER, ElementType.FIELD, ElementType.TYPE}) @Constraint(validatedBy = FieldRepeatValidatorClass.class) public @interface FieldRepeatValidator { /** * 实体类id字段 - 默认为id (该值可无) * @return * @author : cyy */ String id() default "id";; /** * 注解属性 - 对应校验字段 * @return * @author : cyy */ String field(); /** * 默认错误提示信息 * @return * @author : cyy */ String message() default "字段内容重复!"; Class<?>[] groups() default {}; Class<? extends Payload>[] payload() default {}; }
关于实体类所涉及到的代码如上,如果有缺少部分,请留言,会补充的
1、Security 核心配置类 配置用户密码校验过滤器
import cn.com.sercurity.cyy.config.security.filter.AdminAuthenticationProcessingFilter; import org.springframework.context.annotation.Configuration; import org.springframework.http.HttpMethod; import org.springframework.security.config.annotation.method.configuration.EnableGlobalMethodSecurity; import org.springframework.security.config.annotation.web.builders.HttpSecurity; import org.springframework.security.config.annotation.web.configuration.EnableWebSecurity; import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter; import org.springframework.security.config.annotation.web.configurers.ExpressionUrlAuthorizationConfigurer; import org.springframework.security.web.authentication.UsernamePasswordAuthenticationFilter; @Configuration @EnableWebSecurity @EnableGlobalMethodSecurity(prePostEnabled = true) public class SecurityConfig extends WebSecurityConfigurerAdapter { /** * 用户密码校验过滤器 */ private final AdminAuthenticationProcessingFilter adminAuthenticationProcessingFilter; public SecurityConfig(AdminAuthenticationProcessingFilter adminAuthenticationProcessingFilter) { this.adminAuthenticationProcessingFilter = adminAuthenticationProcessingFilter; } /** * 权限配置 * @param http * @throws Exception */ @Override protected void configure(HttpSecurity http) throws Exception { ExpressionUrlAuthorizationConfigurer<HttpSecurity>.ExpressionInterceptUrlRegistry registry = http.antMatcher("/**").authorizeRequests(); // 禁用CSRF 开启跨域 http.csrf().disable().cors(); // 登录处理 - 前后端一体的情况下 // registry.and().formLogin().loginPage("/login").defaultSuccessUrl("/").permitAll() // // 自定义登陆用户名和密码属性名,默认为 username和password // .usernameParameter("username").passwordParameter("password") // // 异常处理 // .failureUrl("/login/error").permitAll() // // 退出登录 // .and().logout().permitAll(); // 标识只能在 服务器本地ip[127.0.0.1或localhost] 访问`/home`接口,其他ip地址无法访问 registry.antMatchers("/home").hasIpAddress("127.0.0.1"); // 允许匿名的url - 可理解为放行接口 - 多个接口使用,分割 registry.antMatchers("/login", "/index").permitAll(); // OPTIONS(选项):查找适用于一个特定网址资源的通讯选择。 在不需执行具体的涉及数据传输的动作情况下, 允许客户端来确定与资源相关的选项以及 / 或者要求, 或是一个服务器的性能 registry.antMatchers(HttpMethod.OPTIONS, "/**").denyAll(); // 自动登录 - cookie储存方式 registry.and().rememberMe(); // 其余所有请求都需要认证 registry.anyRequest().authenticated(); // 防止iframe 造成跨域 registry.and().headers().frameOptions().disable(); // 自定义过滤器认证用户名密码 http.addFilterAt(adminAuthenticationProcessingFilter, UsernamePasswordAuthenticationFilter.class); } }
2、自定义用户密码校验过滤器
import cn.com.sercurity.cyy.common.util.Constants; import cn.com.sercurity.cyy.common.util.MultiReadHttpServletRequest; import cn.com.sercurity.cyy.config.security.login.AdminAuthenticationFailureHandler; import cn.com.sercurity.cyy.config.security.login.AdminAuthenticationSuccessHandler; import cn.com.sercurity.cyy.config.security.login.CusAuthenticationManager; import cn.com.sercurity.cyy.user.entity.User; import com.alibaba.fastjson.JSONObject; import lombok.extern.slf4j.Slf4j; import org.springframework.security.authentication.AuthenticationServiceException; import org.springframework.security.authentication.UsernamePasswordAuthenticationToken; import org.springframework.security.core.Authentication; import org.springframework.security.core.AuthenticationException; import org.springframework.security.web.authentication.AbstractAuthenticationProcessingFilter; import org.springframework.security.web.util.matcher.AntPathRequestMatcher; import org.springframework.stereotype.Component; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; @Slf4j @Component public class AdminAuthenticationProcessingFilter extends AbstractAuthenticationProcessingFilter { /** * @param authenticationManager: 认证管理器 * @param adminAuthenticationSuccessHandler: 认证成功处理 * @param adminAuthenticationFailureHandler: 认证失败处理 */ public AdminAuthenticationProcessingFilter(CusAuthenticationManager authenticationManager, AdminAuthenticationSuccessHandler adminAuthenticationSuccessHandler, AdminAuthenticationFailureHandler adminAuthenticationFailureHandler) { super(new AntPathRequestMatcher("/login", "POST")); this.setAuthenticationManager(authenticationManager); this.setAuthenticationSuccessHandler(adminAuthenticationSuccessHandler); this.setAuthenticationFailureHandler(adminAuthenticationFailureHandler); } @Override public Authentication attemptAuthentication(HttpServletRequest request, HttpServletResponse response) throws AuthenticationException { if (request.getContentType() == null || !request.getContentType().contains(Constants.REQUEST_HEADERS_CONTENT_TYPE)) { throw new AuthenticationServiceException("请求头类型不支持: " + request.getContentType()); } UsernamePasswordAuthenticationToken authRequest; try { MultiReadHttpServletRequest wrappedRequest = new MultiReadHttpServletRequest(request); // 将前端传递的数据转换成jsonBean数据格式 User user = JSONObject.parseObject(wrappedRequest.getBodyJsonStrByJson(wrappedRequest), User.class); authRequest = new UsernamePasswordAuthenticationToken(user.getUsername(), user.getPassword(), null); authRequest.setDetails(authenticationDetailsSource.buildDetails(wrappedRequest)); } catch (Exception e) { throw new AuthenticationServiceException(e.getMessage()); } return this.getAuthenticationManager().authenticate(authRequest); } }
3、自定义认证管理器
import org.springframework.security.authentication.AuthenticationManager; import org.springframework.security.authentication.ProviderNotFoundException; import org.springframework.security.core.Authentication; import org.springframework.security.core.AuthenticationException; import org.springframework.stereotype.Component; import java.util.Objects; @Component public class CusAuthenticationManager implements AuthenticationManager { private final AdminAuthenticationProvider adminAuthenticationProvider; public CusAuthenticationManager(AdminAuthenticationProvider adminAuthenticationProvider) { this.adminAuthenticationProvider = adminAuthenticationProvider; } @Override public Authentication authenticate(Authentication authentication) throws AuthenticationException { Authentication result = adminAuthenticationProvider.authenticate(authentication); if (Objects.nonNull(result)) { return result; } throw new ProviderNotFoundException("Authentication failed!"); } }
认证成功处理
import cn.com.sercurity.cyy.common.dto.ApiResult; import cn.com.sercurity.cyy.common.util.ResponseUtils; import cn.com.sercurity.cyy.config.security.dto.SecurityUser; import cn.com.sercurity.cyy.user.entity.User; import org.springframework.security.core.Authentication; import org.springframework.security.web.authentication.AuthenticationSuccessHandler; import org.springframework.stereotype.Component; import javax.servlet.ServletException; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; import java.io.IOException; @Component public class AdminAuthenticationSuccessHandler implements AuthenticationSuccessHandler { @Override public void onAuthenticationSuccess(HttpServletRequest httpServletRequest, HttpServletResponse response, Authentication auth) throws IOException, ServletException { User user = new User(); SecurityUser securityUser = ((SecurityUser) auth.getPrincipal()); user.setToken(securityUser.getCurrentUserInfo().getToken()); ResponseUtils.out(response, ApiResult.ok("登录成功!", user)); } }
认证失败处理 - 前后端分离情况下返回json数据格式
import cn.com.sercurity.cyy.common.dto.ApiResult; import cn.com.sercurity.cyy.common.util.ResponseUtils; import lombok.extern.slf4j.Slf4j; import org.springframework.security.authentication.*; import org.springframework.security.core.AuthenticationException; import org.springframework.security.core.userdetails.UsernameNotFoundException; import org.springframework.security.web.authentication.AuthenticationFailureHandler; import org.springframework.stereotype.Component; import javax.servlet.ServletException; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; import java.io.IOException; @Slf4j @Component public class AdminAuthenticationFailureHandler implements AuthenticationFailureHandler { @Override public void onAuthenticationFailure(HttpServletRequest httpServletRequest, HttpServletResponse response, AuthenticationException e) throws IOException, ServletException { ApiResult result; if (e instanceof UsernameNotFoundException || e instanceof BadCredentialsException) { result = ApiResult.fail(e.getMessage()); } else if (e instanceof LockedException) { result = ApiResult.fail("账户被锁定,请联系管理员!"); } else if (e instanceof CredentialsExpiredException) { result = ApiResult.fail("证书过期,请联系管理员!"); } else if (e instanceof AccountExpiredException) { result = ApiResult.fail("账户过期,请联系管理员!"); } else if (e instanceof DisabledException) { result = ApiResult.fail("账户被禁用,请联系管理员!"); } else { log.error("登录失败:", e); result = ApiResult.fail("登录失败!"); } ResponseUtils.out(response, result); } }
全局常用变量
import java.util.HashMap; import java.util.Map; public class Constants { /** * 接口url */ public static Map<String,String> URL_MAPPING_MAP = new HashMap<>(); /** * 获取项目根目录 */ public static String PROJECT_ROOT_DIRECTORY = System.getProperty("user.dir"); /** * 密码加密相关 */ public static String SALT = "cyy"; public static final int HASH_ITERATIONS = 1; /** * 请求头 - token */ public static final String REQUEST_HEADER = "X-Token"; /** * 请求头类型: * application/x-www-form-urlencoded : form表单格式 * application/json : json格式 */ public static final String REQUEST_HEADERS_CONTENT_TYPE = "application/json"; /** * 登录者角色 */ public static final String ROLE_LOGIN = "role_login"; }
多次读写BODY用HTTP REQUEST - 解决流只能读一次问题
import com.alibaba.fastjson.JSONObject; import lombok.extern.slf4j.Slf4j; import javax.servlet.ReadListener; import javax.servlet.ServletInputStream; import javax.servlet.ServletRequest; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletRequestWrapper; import java.io.*; import java.nio.charset.Charset; import java.util.Enumeration; import java.util.HashMap; import java.util.Map; @Slf4j public class MultiReadHttpServletRequest extends HttpServletRequestWrapper { private final byte[] body; public MultiReadHttpServletRequest(HttpServletRequest request) throws IOException { super(request); body = getBodyString(request).getBytes(Charset.forName("UTF-8")); } @Override public BufferedReader getReader() throws IOException { return new BufferedReader(new InputStreamReader(getInputStream())); } @Override public ServletInputStream getInputStream() throws IOException { final ByteArrayInputStream bais = new ByteArrayInputStream(body); return new ServletInputStream() { @Override public int read() throws IOException { return bais.read(); } @Override public boolean isFinished() { return false; } @Override public boolean isReady() { return false; } @Override public void setReadListener(ReadListener readListener) { } }; } /** * 获取请求Body * * @param request * @return */ private String getBodyString(ServletRequest request) { StringBuilder sb = new StringBuilder(); InputStream inputStream = null; BufferedReader reader = null; try { inputStream = request.getInputStream(); reader = new BufferedReader(new InputStreamReader(inputStream, Charset.forName("UTF-8"))); String line = ""; while ((line = reader.readLine()) != null) { sb.append(line); } } catch (IOException e) { e.printStackTrace(); } finally { if (inputStream != null) { try { inputStream.close(); } catch (IOException e) { e.printStackTrace(); } } if (reader != null) { try { reader.close(); } catch (IOException e) { e.printStackTrace(); } } } return sb.toString(); } /** * 将前端请求的表单数据转换成json字符串 - 前后端一体的情况下使用 * @param request: * @return: java.lang.String */ public String getBodyJsonStrByForm(ServletRequest request){ Map<String, Object> bodyMap = new HashMap<>(16); try { // 参数定义 String paraName = null; // 获取请求参数并转换 Enumeration<String> e = request.getParameterNames(); while (e.hasMoreElements()) { paraName = e.nextElement(); bodyMap.put(paraName, request.getParameter(paraName)); } } catch(Exception e) { log.error("请求参数转换错误!",e); } return JSONObject.toJSONString(bodyMap); } /** * 将前端传递的json数据转换成json字符串 - 前后端分离的情况下使用 * @param request: * @return: java.lang.String */ public String getBodyJsonStrByJson(ServletRequest request){ StringBuffer json = new StringBuffer(); String line = null; try { BufferedReader reader = request.getReader(); while((line = reader.readLine()) != null) { json.append(line); } } catch(Exception e) { log.error("请求参数转换错误!",e); } return json.toString(); } }
API返回参数
import cn.com.sercurity.cyy.common.enumeration.ResultCode; import io.swagger.annotations.ApiModel; import io.swagger.annotations.ApiModelProperty; @ApiModel(value = "API返回参数") public class ApiResult { /** * 消息内容 */ @ApiModelProperty(value = "响应消息", required = false) private String message; /** * 响应码:参考`ResultCode` */ @ApiModelProperty(value = "响应码", required = true) private Integer code; /** * 响应中的数据 */ @ApiModelProperty(value = "响应数据", required = false) private Object data; /*** * 过期 * * @param message: */ public static ApiResult expired(String message) { return new ApiResult(ResultCode.UN_LOGIN.getCode(), message, null); } public static ApiResult fail(String message) { return new ApiResult(ResultCode.FAILURE.getCode(), message, null); } /*** * 自定义错误返回码 * * @param code * @param message: */ public static ApiResult fail(Integer code, String message) { return new ApiResult(code, message, null); } public static ApiResult ok(String message) { return new ApiResult(ResultCode.SUCCESS.getCode(), message, null); } public static ApiResult ok() { return new ApiResult(ResultCode.SUCCESS.getCode(), "OK", null); } public static ApiResult build(Integer code, String msg, Object data) { return new ApiResult(ResultCode.SUCCESS.getCode(), msg, data); } public static ApiResult ok(String message, Object data) { return new ApiResult(ResultCode.SUCCESS.getCode(), message, data); } /** * 自定义返回码 */ public static ApiResult ok(Integer code, String message) { return new ApiResult(code, message); } /** * 自定义 * * @param code:验证码 * @param message:返回消息内容 * @param data:返回数据 */ public static ApiResult ok(Integer code, String message, Object data) { return new ApiResult(code, message, data); } public ApiResult() { } public static ApiResult build(Integer code, String msg) { return new ApiResult(code, msg, null); } public ApiResult(Integer code, String msg, Object data) { this.code = code; this.message = msg; this.data = data; } public ApiResult(Object data) { this.code = ResultCode.SUCCESS.getCode(); this.message = "OK"; this.data = data; } public ApiResult(String message) { this(ResultCode.SUCCESS.getCode(), message, null); } public ApiResult(String message, Integer code) { this.message = message; this.code = code; } public ApiResult(Integer code, String message) { this.code = code; this.message = message; } public String getMessage() { return message; } public void setMessage(String message) { this.message = message; } public Integer getCode() { return code; } public void setCode(Integer code) { this.code = code; } public Object getData() { return data; } public void setData(Object data) { this.data = data; } }
响应码枚举
public enum ResultCode { //成功 SUCCESS( 200, "SUCCESS" ), //失败 FAILURE( 400, "FAILURE" ), // 未登录 UN_LOGIN( 401, "未登录" ), //未认证(签名错误、token错误) UNAUTHORIZED( 403, "未认证或Token失效" ), //未通过认证 USER_UNAUTHORIZED( 402, "用户名或密码不正确" ), //接口不存在 NOT_FOUND( 404, "接口不存在" ), //服务器内部错误 INTERNAL_SERVER_ERROR( 500, "服务器内部错误" ); private int code; private String desc; ResultCode(int code, String desc) { this.code = code; this.desc = desc; } public int getCode() { return code; } public void setCode(int code) { this.code = code; } public String getDesc() { return desc; } public void setDesc(String desc) { this.desc = desc; } }
使用response输出JSON
import cn.com.sercurity.cyy.common.dto.ApiResult; import com.alibaba.fastjson.JSON; import com.alibaba.fastjson.JSONObject; import lombok.extern.slf4j.Slf4j; import javax.servlet.ServletResponse; import javax.servlet.http.HttpServletResponse; import java.io.IOException; import java.io.PrintWriter; @Slf4j public class ResponseUtils { /** * 使用response输出JSON * * @param response * @param result */ public static void out(ServletResponse response, ApiResult result) { PrintWriter out = null; try { response.setCharacterEncoding("UTF-8"); response.setContentType("application/json"); out = response.getWriter(); out.println(JSON.toJSONString(result)); } catch (Exception e) { log.error(e + "输出JSON出错"); } finally { if (out != null) { out.flush(); out.close(); } } } /** * 响应内容 * @param httpServletResponse * @param msg * @param status */ public static void getResponse(HttpServletResponse httpServletResponse, String msg, Integer status){ PrintWriter writer = null; httpServletResponse.setCharacterEncoding("UTF-8"); httpServletResponse.setContentType("application/json; charset=utf-8"); try { writer = httpServletResponse.getWriter(); writer.print(JSONObject.toJSONString(new ApiResult(status,msg,null))); } catch (IOException e) { log.error("响应报错", e.getMessage()); } finally { if (writer != null){ writer.close(); } } } }
4、自定义认证处理
import cn.com.sercurity.cyy.common.util.PasswordUtils; import cn.com.sercurity.cyy.config.security.dto.SecurityUser; import cn.com.sercurity.cyy.config.security.service.impl.UserDetailsServiceImpl; import cn.com.sercurity.cyy.user.entity.User; import cn.com.sercurity.cyy.user.mapper.UserMapper; import org.springframework.beans.factory.annotation.Autowired; import org.springframework.security.authentication.AuthenticationProvider; import org.springframework.security.authentication.BadCredentialsException; import org.springframework.security.authentication.UsernamePasswordAuthenticationToken; import org.springframework.security.core.Authentication; import org.springframework.security.core.AuthenticationException; import org.springframework.stereotype.Component; @Component public class AdminAuthenticationProvider implements AuthenticationProvider { @Autowired UserDetailsServiceImpl userDetailsService; @Autowired private UserMapper userMapper; @Override public Authentication authenticate(Authentication authentication) throws AuthenticationException { // 获取前端表单中输入后返回的用户名、密码 String userName = (String) authentication.getPrincipal(); String password = (String) authentication.getCredentials(); SecurityUser userInfo = (SecurityUser) userDetailsService.loadUserByUsername(userName); boolean isValid = PasswordUtils.isValidPassword(password, userInfo.getPassword(), userInfo.getCurrentUserInfo().getSalt()); // 验证密码 if (!isValid) { throw new BadCredentialsException("密码错误!"); } // 前后端分离情况下 处理逻辑... // 更新登录令牌 - 之后访问系统其它接口直接通过token认证用户权限... String token = PasswordUtils.encodePassword(System.currentTimeMillis() + userInfo.getCurrentUserInfo().getSalt(), userInfo.getCurrentUserInfo().getSalt()); User user = userMapper.selectById(userInfo.getCurrentUserInfo().getId()); user.setToken(token); userMapper.updateById(user); userInfo.getCurrentUserInfo().setToken(token); return new UsernamePasswordAuthenticationToken(userInfo, password, userInfo.getAuthorities()); } @Override public boolean supports(Class<?> aClass) { return true; } }
加密处理
import lombok.extern.slf4j.Slf4j; import org.springframework.security.crypto.codec.Hex; import java.security.MessageDigest; @Slf4j public class PasswordUtils { /** * 校验密码是否一致 * * @param password: 前端传过来的密码 * @param hashedPassword:数据库中储存加密过后的密码 * @param salt:盐值 * @return */ public static boolean isValidPassword(String password, String hashedPassword, String salt) { return hashedPassword.equalsIgnoreCase(encodePassword(password, salt)); } /** * 通过SHA1对密码进行编码 * * @param password:密码 * @param salt:盐值 * @return */ public static String encodePassword(String password, String salt) { String encodedPassword; try { MessageDigest digest = MessageDigest.getInstance("SHA-1"); if (salt != null) { digest.reset(); digest.update(salt.getBytes()); } byte[] hashed = digest.digest(password.getBytes()); int iterations = Constants.HASH_ITERATIONS - 1; for (int i = 0; i < iterations; ++i) { digest.reset(); hashed = digest.digest(hashed); } encodedPassword = new String(Hex.encode(hashed)); } catch (Exception e) { log.error("验证密码异常:", e); return null; } return encodedPassword; } }
安全认证用户详情
import cn.com.sercurity.cyy.user.entity.User; import lombok.Data; import lombok.extern.slf4j.Slf4j; import org.springframework.security.core.GrantedAuthority; import org.springframework.security.core.authority.SimpleGrantedAuthority; import org.springframework.security.core.userdetails.UserDetails; import java.util.ArrayList; import java.util.Collection; @Data @Slf4j public class SecurityUser implements UserDetails { /** * 当前登录用户 */ private transient User currentUserInfo; public SecurityUser() { } public SecurityUser(User user) { if (user != null) { this.currentUserInfo = user; } } @Override public Collection<? extends GrantedAuthority> getAuthorities() { Collection<GrantedAuthority> authorities = new ArrayList<>(); SimpleGrantedAuthority authority = new SimpleGrantedAuthority("admin"); authorities.add(authority); return authorities; } @Override public String getPassword() { return currentUserInfo.getPassword(); } @Override public String getUsername() { return currentUserInfo.getUsername(); } @Override public boolean isAccountNonExpired() { return true; } @Override public boolean isAccountNonLocked() { return true; } @Override public boolean isCredentialsNonExpired() { return true; } @Override public boolean isEnabled() { return true; } }
自定义userDetailsService - 认证用户详情
import cn.com.sercurity.cyy.config.security.dto.SecurityUser; import cn.com.sercurity.cyy.user.entity.User; import cn.com.sercurity.cyy.user.mapper.UserMapper; import com.baomidou.mybatisplus.mapper.EntityWrapper; import org.springframework.beans.factory.annotation.Autowired; import org.springframework.security.core.userdetails.UserDetails; import org.springframework.security.core.userdetails.UserDetailsService; import org.springframework.security.core.userdetails.UsernameNotFoundException; import org.springframework.stereotype.Service; import org.springframework.util.CollectionUtils; import java.util.List; @Service("userDetailsService") public class UserDetailsServiceImpl implements UserDetailsService { @Autowired private UserMapper userMapper; /*** * 根据账号获取用户信息 * @param username: * @return: org.springframework.security.core.userdetails.UserDetails */ @Override public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException { // 从数据库中取出用户信息 List<User> userList = userMapper.selectList(new EntityWrapper<User>().eq("username", username)); User user; // 判断用户是否存在 if (!CollectionUtils.isEmpty(userList)){ user = userList.get(0); } else { throw new UsernameNotFoundException("用户名不存在!"); } // 返回UserDetails实现类 return new SecurityUser(user); } }
import cn.com.sercurity.cyy.user.entity.User; import com.baomidou.mybatisplus.mapper.BaseMapper; import org.apache.ibatis.annotations.Mapper; /** * * <p> 系统管理-用户基础信息表 Mapper 接口 </p> **/ @Mapper public interface UserMapper extends BaseMapper<User> { }
前端页面
这里2个简单的html页面模拟前后端分离情况下登陆处理场景
1、登陆页
login.html
<!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> <title>Login</title> </head> <body> <h1>Spring Security</h1> <form method="post" action="" onsubmit="return false"> <div> 用户名:<input type="text" name="username" id="username"> </div> <div> 密码:<input type="password" name="password" id="password"> </div> <div> <!-- <label><input type="checkbox" name="remember-me" id="remember-me"/>自动登录</label>--> <button onclick="login()">登陆</button> </div> </form> </body> <script src="http://libs.baidu.com/jquery/1.9.0/jquery.js" type="text/javascript"></script> <script type="text/javascript"> function login() { var username = document.getElementById("username").value; var password = document.getElementById("password").value; // var rememberMe = document.getElementById("remember-me").value; $.ajax({ async: false, type: "POST", dataType: "json", url: '/login', contentType: "application/json", data: JSON.stringify({ "username": username, "password": password // "remember-me": rememberMe }), success: function (result) { console.log(result) if (result.code == 200) { alert("登陆成功"); window.location.href = "../home.html"; } else { alert(result.message) } } }); } </script> </html>
2、首页
home.html
<!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> <title>Title</title> </head> <body> <h3>您好,登陆成功</h3> <button onclick="window.location.href='/logout'">退出登录</button> </body> </html>
测试接口
import cn.com.sercurity.cyy.common.dto.ApiResult; import cn.com.sercurity.cyy.common.util.ResponseUtils; import lombok.extern.slf4j.Slf4j; import org.springframework.security.access.prepost.PreAuthorize; import org.springframework.security.core.AuthenticationException; import org.springframework.security.core.context.SecurityContextHolder; import org.springframework.web.bind.annotation.GetMapping; import org.springframework.web.bind.annotation.RequestMapping; import org.springframework.web.bind.annotation.RestController; import org.springframework.web.servlet.ModelAndView; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletResponse; @Slf4j @RestController public class IndexController { @GetMapping("/") public ModelAndView showHome() { return new ModelAndView("home.html"); } @GetMapping("/index") public String index() { return "Hello World ~"; } @GetMapping("/login") public ModelAndView login() { return new ModelAndView("login.html"); } @GetMapping("/home") public String home() { String name = SecurityContextHolder.getContext().getAuthentication().getName(); log.info("登陆人:" + name); return "Hello~ " + name; } @GetMapping(value ="/admin") // 访问路径`/admin` 具有`crud`权限 @PreAuthorize("hasPermission('/admin','crud')") public String admin() { return "Hello~ 管理员"; } @GetMapping("/test") // @PreAuthorize("hasPermission('/test','t')") public String test() { return "Hello~ 测试权限访问接口"; } /** * 登录异常处理 - 前后端一体的情况下 * @param request * @param response */ @RequestMapping("/login/error") public void loginError(HttpServletRequest request, HttpServletResponse response) { AuthenticationException e = (AuthenticationException) request.getSession().getAttribute("SPRING_SECURITY_LAST_EXCEPTION"); log.error(e.getMessage()); ResponseUtils.out(response, ApiResult.fail(e.getMessage())); } }
使用response输出JSON
import cn.com.sercurity.cyy.common.dto.ApiResult; import com.alibaba.fastjson.JSON; import com.alibaba.fastjson.JSONObject; import lombok.extern.slf4j.Slf4j; import javax.servlet.ServletResponse; import javax.servlet.http.HttpServletResponse; import java.io.IOException; import java.io.PrintWriter; @Slf4j public class ResponseUtils { /** * 使用response输出JSON * * @param response * @param result */ public static void out(ServletResponse response, ApiResult result) { PrintWriter out = null; try { response.setCharacterEncoding("UTF-8"); response.setContentType("application/json"); out = response.getWriter(); out.println(JSON.toJSONString(result)); } catch (Exception e) { log.error(e + "输出JSON出错"); } finally { if (out != null) { out.flush(); out.close(); } } } /** * 响应内容 * @param httpServletResponse * @param msg * @param status */ public static void getResponse(HttpServletResponse httpServletResponse, String msg, Integer status){ PrintWriter writer = null; httpServletResponse.setCharacterEncoding("UTF-8"); httpServletResponse.setContentType("application/json; charset=utf-8"); try { writer = httpServletResponse.getWriter(); writer.print(JSONObject.toJSONString(new ApiResult(status,msg,null))); } catch (IOException e) { log.error("响应报错", e.getMessage()); } finally { if (writer != null){ writer.close(); } } } }
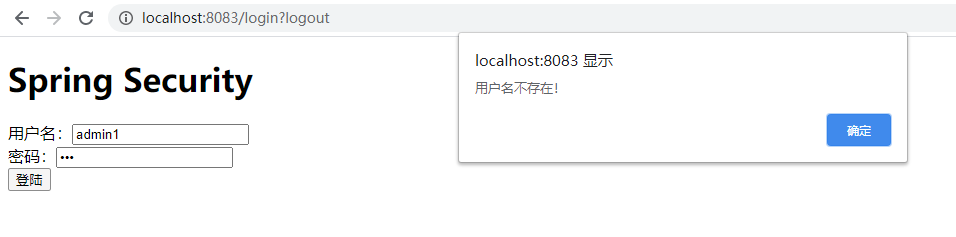
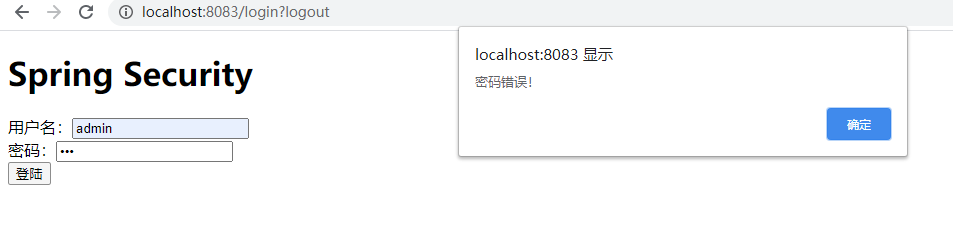
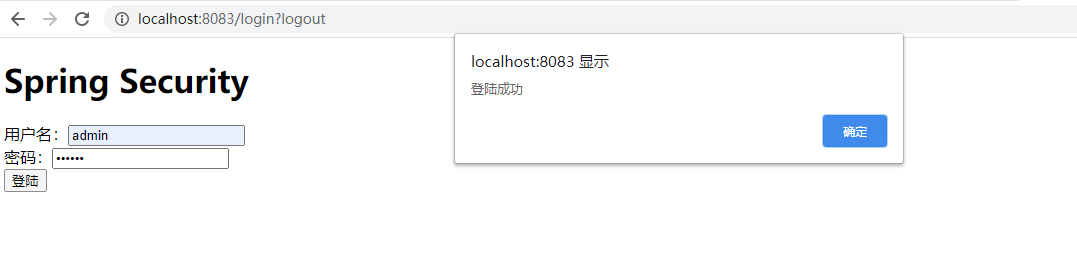
测试访问效果
数据库账号:admin 密码:123456
1. 输入错误用户名提示该用户不存在
2. 输入错误密码提示密码错误
3. 输入正确用户名和账号,提示登陆成功,然后跳转到首页
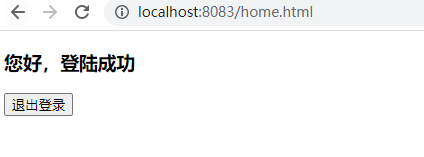
登陆成功后即可正常访问其他接口,如果是未登录情况下将访问不了
总结
- 在
Spring Security核心配置类中设置自定义的用户密码校验过滤器(AdminAuthenticationProcessingFilter) - 在自定义的用户密码校验过滤器中配置
认证管理器(CusAuthenticationManager)、认证成功处理(AdminAuthenticationSuccessHandler)和认证失败处理(AdminAuthenticationFailureHandler)等 - 在自定义的认证管理器中配置自定义的
认证处理(AdminAuthenticationProvider) - 然后就是在认证处理中实现自己的相应业务逻辑等
如果缺少什么了,欢迎大家留言,我会及时补充的

