2017-2018-1 20155202 20155239 实验二 固件程序设计
2017-2018-1 20155202 20155202 实验二 固件程序设计
实验1,2,3,5 搭档写,博客链接:20155239
实验四:国密算法
-
四个算法的用途:
-
SM1对称分组算法
-
用途:芯片、智能IC卡、智能密码钥匙、加密卡、加密机等安全产品,广泛应用于电子政务、电子商务及国民经济的各个应用领域(包括国家政务通、警务通等重要领域)。
-
密码学对应算法:DES,AES
-
SM2椭圆曲线公钥密码算法
-
用途:密钥管理,数字签名,电子商务,PKI,信息及身份认证等信息安全应用领域
-
密码学对应算法:ECC椭圆曲线算法
sm2:
// \file:sm2.c
//SM2 Algorithm
//2011-11-10
//author:goldboar
//email:goldboar@163.com
//depending:opnessl library
//SM2 Standards: http://www.oscca.gov.cn/News/201012/News_1197.htm
#include <limits.h>
//#include <openssl/ec.h>
#include <openssl/bn.h>
#include <openssl/rand.h>
#include <openssl/err.h>
#include <openssl/ecdsa.h>
#include <openssl/ecdh.h>
#include "kdf.h"
#define NID_X9_62_prime_field 406
static void BNPrintf(BIGNUM* bn)
{
char *p=NULL;
p=BN_bn2hex(bn);
printf("%s",p);
OPENSSL_free(p);
}
static int sm2_sign_setup(EC_KEY *eckey, BN_CTX *ctx_in, BIGNUM **kp, BIGNUM **rp)
{
BN_CTX *ctx = NULL;
BIGNUM *k = NULL, *r = NULL, *order = NULL, *X = NULL;
EC_POINT *tmp_point=NULL;
const EC_GROUP *group;
int ret = 0;
if (eckey == NULL || (group = EC_KEY_get0_group(eckey)) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_PASSED_NULL_PARAMETER);
return 0;
}
if (ctx_in == NULL)
{
if ((ctx = BN_CTX_new()) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP,ERR_R_MALLOC_FAILURE);
return 0;
}
}
else
ctx = ctx_in;
k = BN_new(); /* this value is later returned in *kp */
r = BN_new(); /* this value is later returned in *rp */
order = BN_new();
X = BN_new();
if (!k || !r || !order || !X)
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_MALLOC_FAILURE);
goto err;
}
if ((tmp_point = EC_POINT_new(group)) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_EC_LIB);
goto err;
}
if (!EC_GROUP_get_order(group, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_EC_LIB);
goto err;
}
do
{
/* get random k */
do
if (!BN_rand_range(k, order))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ECDSA_R_RANDOM_NUMBER_GENERATION_FAILED);
goto err;
}
while (BN_is_zero(k));
/* compute r the x-coordinate of generator * k */
if (!EC_POINT_mul(group, tmp_point, k, NULL, NULL, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_EC_LIB);
goto err;
}
if (EC_METHOD_get_field_type(EC_GROUP_method_of(group)) == NID_X9_62_prime_field)
{
if (!EC_POINT_get_affine_coordinates_GFp(group,
tmp_point, X, NULL, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP,ERR_R_EC_LIB);
goto err;
}
}
else /* NID_X9_62_characteristic_two_field */
{
if (!EC_POINT_get_affine_coordinates_GF2m(group,
tmp_point, X, NULL, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP,ERR_R_EC_LIB);
goto err;
}
}
if (!BN_nnmod(r, X, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_BN_LIB);
goto err;
}
}
while (BN_is_zero(r));
/* compute the inverse of k */
// if (!BN_mod_inverse(k, k, order, ctx))
// {
// ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_BN_LIB);
// goto err;
// }
/* clear old values if necessary */
if (*rp != NULL)
BN_clear_free(*rp);
if (*kp != NULL)
BN_clear_free(*kp);
/* save the pre-computed values */
*rp = r;
*kp = k;
ret = 1;
err:
if (!ret)
{
if (k != NULL) BN_clear_free(k);
if (r != NULL) BN_clear_free(r);
}
if (ctx_in == NULL)
BN_CTX_free(ctx);
if (order != NULL)
BN_free(order);
if (tmp_point != NULL)
EC_POINT_free(tmp_point);
if (X)
BN_clear_free(X);
return(ret);
}
static ECDSA_SIG *sm2_do_sign(const unsigned char *dgst, int dgst_len, const BIGNUM *in_k, const BIGNUM *in_r, EC_KEY *eckey)
{
int ok = 0, i;
BIGNUM *k=NULL, *s, *m=NULL,*tmp=NULL,*order=NULL;
const BIGNUM *ck;
BN_CTX *ctx = NULL;
const EC_GROUP *group;
ECDSA_SIG *ret;
//ECDSA_DATA *ecdsa;
const BIGNUM *priv_key;
BIGNUM *r,*x=NULL,*a=NULL; //new added
//ecdsa = ecdsa_check(eckey);
group = EC_KEY_get0_group(eckey);
priv_key = EC_KEY_get0_private_key(eckey);
if (group == NULL || priv_key == NULL /*|| ecdsa == NULL*/)
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_PASSED_NULL_PARAMETER);
return NULL;
}
ret = ECDSA_SIG_new();
if (!ret)
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_MALLOC_FAILURE);
return NULL;
}
s = ret->s;
r = ret->r;
if ((ctx = BN_CTX_new()) == NULL || (order = BN_new()) == NULL ||
(tmp = BN_new()) == NULL || (m = BN_new()) == NULL ||
(x = BN_new()) == NULL || (a = BN_new()) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_MALLOC_FAILURE);
goto err;
}
if (!EC_GROUP_get_order(group, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_EC_LIB);
goto err;
}
// for(i=0;i<dgst_len;i++)
// printf("%02X",dgst[i]);
// printf("\n");
i = BN_num_bits(order);
/* Need to truncate digest if it is too long: first truncate whole
* bytes.
*/
if (8 * dgst_len > i)
dgst_len = (i + 7)/8;
if (!BN_bin2bn(dgst, dgst_len, m))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
/* If still too long truncate remaining bits with a shift */
if ((8 * dgst_len > i) && !BN_rshift(m, m, 8 - (i & 0x7)))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
// fprintf(stdout,"m: ");
// BNPrintf(m);
// fprintf(stdout,"\n");
do
{
if (in_k == NULL || in_r == NULL)
{
if (!sm2_sign_setup(eckey, ctx, &k, &x))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN,ERR_R_ECDSA_LIB);
goto err;
}
ck = k;
}
else
{
ck = in_k;
if (BN_copy(x, in_r) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_MALLOC_FAILURE);
goto err;
}
}
//r=(e+x1) mod n
if (!BN_mod_add_quick(r, m, x, order))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
// BNPrintf(r);
// fprintf(stdout,"\n");
if(BN_is_zero(r) )
continue;
BN_add(tmp,r,ck);
if(BN_ucmp(tmp,order) == 0)
continue;
if (!BN_mod_mul(tmp, priv_key, r, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
if (!BN_mod_sub_quick(s, ck, tmp, order))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
BN_one(a);
//BN_set_word((a),1);
if (!BN_mod_add_quick(tmp, priv_key, a, order))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
/* compute the inverse of 1+dA */
if (!BN_mod_inverse(tmp, tmp, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_SIGN_SETUP, ERR_R_BN_LIB);
goto err;
}
// BNPrintf(tmp);
// fprintf(stdout,"\n");
if (!BN_mod_mul(s, s, tmp, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_BN_LIB);
goto err;
}
if (BN_is_zero(s))
{
/* if k and r have been supplied by the caller
* don't to generate new k and r values */
if (in_k != NULL && in_r != NULL)
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ECDSA_R_NEED_NEW_SETUP_VALUES);
goto err;
}
}
else
/* s != 0 => we have a valid signature */
break;
}
while (1);
ok = 1;
err:
if (!ok)
{
ECDSA_SIG_free(ret);
ret = NULL;
}
if (ctx)
BN_CTX_free(ctx);
if (m)
BN_clear_free(m);
if (tmp)
BN_clear_free(tmp);
if (order)
BN_free(order);
if (k)
BN_clear_free(k);
if (x)
BN_clear_free(x);
if (a)
BN_clear_free(a);
return ret;
}
static int sm2_do_verify(const unsigned char *dgst, int dgst_len,
const ECDSA_SIG *sig, EC_KEY *eckey)
{
int ret = -1, i;
BN_CTX *ctx;
BIGNUM *order, *R, *m, *X,*t;
EC_POINT *point = NULL;
const EC_GROUP *group;
const EC_POINT *pub_key;
/* check input values */
if (eckey == NULL || (group = EC_KEY_get0_group(eckey)) == NULL ||
(pub_key = EC_KEY_get0_public_key(eckey)) == NULL || sig == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ECDSA_R_MISSING_PARAMETERS);
return -1;
}
ctx = BN_CTX_new();
if (!ctx)
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_MALLOC_FAILURE);
return -1;
}
BN_CTX_start(ctx);
order = BN_CTX_get(ctx);
R = BN_CTX_get(ctx);
t = BN_CTX_get(ctx);
m = BN_CTX_get(ctx);
X = BN_CTX_get(ctx);
if (!X)
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_BN_LIB);
goto err;
}
if (!EC_GROUP_get_order(group, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_EC_LIB);
goto err;
}
if (BN_is_zero(sig->r) || BN_is_negative(sig->r) ||
BN_ucmp(sig->r, order) >= 0 || BN_is_zero(sig->s) ||
BN_is_negative(sig->s) || BN_ucmp(sig->s, order) >= 0)
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ECDSA_R_BAD_SIGNATURE);
ret = 0; /* signature is invalid */
goto err;
}
//t =(r+s) mod n
if (!BN_mod_add_quick(t, sig->s, sig->r,order))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_BN_LIB);
goto err;
}
if (BN_is_zero(t))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ECDSA_R_BAD_SIGNATURE);
ret = 0; /* signature is invalid */
goto err;
}
//point = s*G+t*PA
if ((point = EC_POINT_new(group)) == NULL)
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_MALLOC_FAILURE);
goto err;
}
if (!EC_POINT_mul(group, point, sig->s, pub_key, t, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_EC_LIB);
goto err;
}
if (EC_METHOD_get_field_type(EC_GROUP_method_of(group)) == NID_X9_62_prime_field)
{
if (!EC_POINT_get_affine_coordinates_GFp(group,
point, X, NULL, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_EC_LIB);
goto err;
}
}
else /* NID_X9_62_characteristic_two_field */
{
if (!EC_POINT_get_affine_coordinates_GF2m(group,
point, X, NULL, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_EC_LIB);
goto err;
}
}
i = BN_num_bits(order);
/* Need to truncate digest if it is too long: first truncate whole
* bytes.
*/
if (8 * dgst_len > i)
dgst_len = (i + 7)/8;
if (!BN_bin2bn(dgst, dgst_len, m))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_BN_LIB);
goto err;
}
/* If still too long truncate remaining bits with a shift */
if ((8 * dgst_len > i) && !BN_rshift(m, m, 8 - (i & 0x7)))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_BN_LIB);
goto err;
}
/* R = m + X mod order */
if (!BN_mod_add_quick(R, m, X, order))
{
ECDSAerr(ECDSA_F_ECDSA_DO_VERIFY, ERR_R_BN_LIB);
goto err;
}
/* if the signature is correct R is equal to sig->r */
ret = (BN_ucmp(R, sig->r) == 0);
err:
BN_CTX_end(ctx);
BN_CTX_free(ctx);
if (point)
EC_POINT_free(point);
return ret;
}
EC_POINT *sm2_compute_key(const EC_POINT *b_pub_key_r, const EC_POINT *b_pub_key, const BIGNUM *a_r,EC_KEY *a_eckey)
{
BN_CTX *ctx;
EC_POINT *tmp=NULL;
BIGNUM *x=NULL, *y=NULL, *order=NULL,*z=NULL;
const BIGNUM *priv_key;
const EC_GROUP* group;
EC_POINT *ret= NULL;
/* size_t buflen, len;*/
unsigned char *buf=NULL;
int i, j;
//char *p=NULL;
BIGNUM *x1,*x2,*t,*h;
if ((ctx = BN_CTX_new()) == NULL) goto err;
BN_CTX_start(ctx);
x = BN_CTX_get(ctx);
y = BN_CTX_get(ctx);
order = BN_CTX_get(ctx);
z = BN_CTX_get(ctx);
x1 = BN_CTX_get(ctx);
x2 = BN_CTX_get(ctx);
t = BN_CTX_get(ctx);
h = BN_CTX_get(ctx);
priv_key = EC_KEY_get0_private_key(a_eckey);
if (priv_key == NULL)
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_NO_PRIVATE_VALUE);
goto err;
}
group = EC_KEY_get0_group(a_eckey);
if ((tmp=EC_POINT_new(group)) == NULL)
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ERR_R_MALLOC_FAILURE);
goto err;
}
if (!EC_POINT_mul(group, tmp, a_r, NULL, NULL, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
if (EC_METHOD_get_field_type(EC_GROUP_method_of(group)) == NID_X9_62_prime_field)
{
if (!EC_POINT_get_affine_coordinates_GFp(group, tmp, x, NULL, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
}
else
{
if (!EC_POINT_get_affine_coordinates_GF2m(group, tmp, x, NULL, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
}
if (!EC_GROUP_get_order(group, order, ctx))
{
ECDSAerr(ECDSA_F_ECDSA_DO_SIGN, ERR_R_EC_LIB);
goto err;
}
i = BN_num_bits(order);
j = i/2 -1;
BN_mask_bits(x,j);
BN_set_word(y,2);
BN_set_word(z,j);
BN_exp(y,y,z,ctx);
BN_add(x1,x,y);
// fprintf(stdout,"X1=: ");
// BNPrintf(x1);
// fprintf(stdout,"\n");
BN_mod_mul(t,x1,a_r,order,ctx);
BN_mod_add_quick(t,t,priv_key,order);
//
// fprintf(stdout,"ta=: ");
// BNPrintf(t);
// fprintf(stdout,"\n");
if (EC_METHOD_get_field_type(EC_GROUP_method_of(group)) == NID_X9_62_prime_field)
{
if (!EC_POINT_get_affine_coordinates_GFp(group, b_pub_key_r, x, NULL, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
}
else
{
if (!EC_POINT_get_affine_coordinates_GF2m(group, b_pub_key_r, x, NULL, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
}
i = BN_num_bits(order);
j = i/2 -1;
BN_mask_bits(x,j);
BN_set_word(y,2);
BN_set_word(z,j);
BN_exp(y,y,z,ctx);
BN_add(x2,x,y);
// fprintf(stdout,"X2=: ");
// BNPrintf(x2);
// fprintf(stdout,"\n");
//x2*Rb+Pb;
if (!EC_POINT_mul(group, tmp, NULL,b_pub_key_r,x2,ctx) )
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
if ((ret=EC_POINT_new(group)) == NULL)
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ERR_R_MALLOC_FAILURE);
goto err;
}
if (!EC_POINT_add(group, ret, b_pub_key, tmp, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
if (!EC_POINT_get_affine_coordinates_GFp(group,ret, x, y, ctx))
{
goto err;
}
// fprintf(stdout, "\nTesting x2*Rb+Pb Key Point\n x = 0x");
// BNPrintf(x);
// fprintf(stdout, "\n y = 0x");
// BNPrintf( y);
// fprintf(stdout, "\n");
//
if(!EC_GROUP_get_cofactor(group, h, ctx))
{
goto err;
}
BN_mul(t,t,h,ctx);
//h*t*(x2*Rb+Pb)
if (!EC_POINT_mul(group, ret, NULL,ret,t,ctx) )
{
goto err;
}
if (!EC_POINT_get_affine_coordinates_GFp(group,ret, x, y, ctx))
{
goto err;
}
// fprintf(stdout, "\nTesting ret Key Point\n x = 0x");
// BNPrintf(x);
// fprintf(stdout, "\n y = 0x");
// BNPrintf( y);
// fprintf(stdout, "\n");
err:
if (tmp) EC_POINT_free(tmp);
if (ctx) BN_CTX_end(ctx);
if (ctx) BN_CTX_free(ctx);
if (buf) OPENSSL_free(buf);
return(ret);
}
/** SM2_sign_setup
* precompute parts of the signing operation.
* \param eckey pointer to the EC_KEY object containing a private EC key
* \param ctx pointer to a BN_CTX object (may be NULL)
* \param k pointer to a BIGNUM pointer for the inverse of k
* \param rp pointer to a BIGNUM pointer for x coordinate of k * generator
* \return 1 on success and 0 otherwise
*/
int SM2_sign_setup(EC_KEY *eckey, BN_CTX *ctx_in, BIGNUM **kinvp, BIGNUM **rp)
{
// ECDSA_DATA *ecdsa = ecdsa_check(eckey);
// if (ecdsa == NULL)
// return 0;
return SM2_sign_setup(eckey, ctx_in, kinvp, rp);
}
/** SM2_sign_ex
* computes ECDSA signature of a given hash value using the supplied
* private key (note: sig must point to ECDSA_size(eckey) bytes of memory).
* \param type this parameter is ignored
* \param dgst pointer to the hash value to sign
* \param dgstlen length of the hash value
* \param sig buffer to hold the DER encoded signature
* \param siglen pointer to the length of the returned signature
* \param k optional pointer to a pre-computed inverse k
* \param rp optional pointer to the pre-computed rp value (see
* ECDSA_sign_setup
* \param eckey pointer to the EC_KEY object containing a private EC key
* \return 1 on success and 0 otherwise
*/
int SM2_sign_ex(int type, const unsigned char *dgst, int dlen, unsigned char
*sig, unsigned int *siglen, const BIGNUM *kinv, const BIGNUM *r,
EC_KEY *eckey)
{
ECDSA_SIG *s;
RAND_seed(dgst, dlen);
s = sm2_do_sign(dgst, dlen, kinv, r, eckey);
if (s == NULL)
{
*siglen=0;
return 0;
}
*siglen = i2d_ECDSA_SIG(s, &sig);
ECDSA_SIG_free(s);
return 1;
}
/** SM2_sign
* computes ECDSA signature of a given hash value using the supplied
* private key (note: sig must point to ECDSA_size(eckey) bytes of memory).
* \param type this parameter is ignored
* \param dgst pointer to the hash value to sign
* \param dgstlen length of the hash value
* \param sig buffer to hold the DER encoded signature
* \param siglen pointer to the length of the returned signature
* \param eckey pointer to the EC_KEY object containing a private EC key
* \return 1 on success and 0 otherwise
*/
int SM2_sign(int type, const unsigned char *dgst, int dlen, unsigned char
*sig, unsigned int *siglen, EC_KEY *eckey)
{
return SM2_sign_ex(type, dgst, dlen, sig, siglen, NULL, NULL, eckey);
}
/** SM2_verify
* verifies that the given signature is valid ECDSA signature
* of the supplied hash value using the specified public key.
* \param type this parameter is ignored
* \param dgst pointer to the hash value
* \param dgstlen length of the hash value
* \param sig pointer to the DER encoded signature
* \param siglen length of the DER encoded signature
* \param eckey pointer to the EC_KEY object containing a public EC key
* \return 1 if the signature is valid, 0 if the signature is invalid and -1 on error
*/
int SM2_verify(int type, const unsigned char *dgst, int dgst_len,
const unsigned char *sigbuf, int sig_len, EC_KEY *eckey)
{
ECDSA_SIG *s;
int ret=-1;
s = ECDSA_SIG_new();
if (s == NULL) return(ret);
if (d2i_ECDSA_SIG(&s, &sigbuf, sig_len) == NULL) goto err;
ret=sm2_do_verify(dgst, dgst_len, s, eckey);
err:
ECDSA_SIG_free(s);
return(ret);
}
int SM2_DH_key(const EC_GROUP * group, const EC_POINT *b_pub_key_r, const EC_POINT *b_pub_key, const BIGNUM *a_r,EC_KEY *a_eckey,
unsigned char *outkey,size_t keylen)
{
EC_POINT *dhpoint = NULL;
BN_CTX * ctx;
EC_POINT *P;
BIGNUM *x, *y;
int ret = 0;
unsigned char in[128];
int inlen;
int len;
P = EC_POINT_new(group);
if (!P ) goto err;
ctx = BN_CTX_new();
x = BN_new();
y = BN_new();
if (!x || !y ) goto err;
dhpoint = sm2_compute_key(b_pub_key_r,b_pub_key,a_r,a_eckey);
if (EC_METHOD_get_field_type(EC_GROUP_method_of(group)) == NID_X9_62_prime_field)
{
if (!EC_POINT_get_affine_coordinates_GFp(group,dhpoint, x, y, ctx))
{
fprintf(stdout, " failed\n");
goto err;
}
}
else
{
if (!EC_POINT_get_affine_coordinates_GF2m(group,dhpoint, x, y, ctx))
{
ECDHerr(ECDH_F_ECDH_COMPUTE_KEY,ECDH_R_POINT_ARITHMETIC_FAILURE);
goto err;
}
}
// if (!EC_POINT_get_affine_coordinates_GFp(group,dhpoint, x, y, ctx))
// {
// fprintf(stdout, " failed\n");
// goto err;
// }
fprintf(stdout, "\nTesting DH Point\n Xv = 0x");
BNPrintf(x);
fprintf(stdout, "\n Yv = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
len = BN_bn2bin(x,in);
inlen =BN_bn2bin(y,in+len);
inlen = inlen + len;
ret = x9_63_kdf(EVP_sha256(),in,inlen,keylen,outkey);
//ret = 1;
err:
EC_POINT_free(P);
EC_POINT_free(dhpoint);
BN_CTX_free(ctx);
return ret;
}
sm2 test:
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <time.h>
#include <openssl/bn.h>
#include <openssl/ec.h>
#include <openssl/rand.h>
#include <openssl/err.h>
#include <openssl/ecdsa.h>
#include <openssl/ecdh.h>
#include "sm2.h"
#pragma comment(lib,"libeay32.lib")
#define ABORT do { \
fflush(stdout); \
fprintf(stderr, "%s:%d: ABORT\n", __FILE__, __LINE__); \
ERR_print_errors_fp(stderr); \
exit(1); \
} while (0)
static const char rnd_seed[] = "string to make the random number generator think it has entropy";
void BNPrintf(BIGNUM* bn)
{
char *p=NULL;
p=BN_bn2hex(bn);
printf("%s",p);
OPENSSL_free(p);
}
int SM2_Test_Vecotor()
{
BN_CTX *ctx = NULL;
BIGNUM *p, *a, *b;
EC_GROUP *group;
EC_POINT *P, *Q, *R;
BIGNUM *x, *y, *z;
EC_KEY *eckey = NULL;
unsigned char digest[20];
unsigned char *signature = NULL;
int sig_len;
CRYPTO_set_mem_debug_functions(0, 0, 0, 0, 0);
CRYPTO_mem_ctrl(CRYPTO_MEM_CHECK_ON);
ERR_load_crypto_strings();
RAND_seed(rnd_seed, sizeof rnd_seed); /* or BN_generate_prime may fail */
ctx = BN_CTX_new();
if (!ctx) ABORT;
/* Curve SM2 (Chinese National Algorithm) */
//http://www.oscca.gov.cn/News/201012/News_1197.htm
p = BN_new();
a = BN_new();
b = BN_new();
if (!p || !a || !b) ABORT;
group = EC_GROUP_new(EC_GFp_mont_method()); /* applications should use EC_GROUP_new_curve_GFp
* so that the library gets to choose the EC_METHOD */
if (!group) ABORT;
if (!BN_hex2bn(&p, "8542D69E4C044F18E8B92435BF6FF7DE457283915C45517D722EDB8B08F1DFC3")) ABORT;
if (1 != BN_is_prime_ex(p, BN_prime_checks, ctx, NULL)) ABORT;
if (!BN_hex2bn(&a, "787968B4FA32C3FD2417842E73BBFEFF2F3C848B6831D7E0EC65228B3937E498")) ABORT;
if (!BN_hex2bn(&b, "63E4C6D3B23B0C849CF84241484BFE48F61D59A5B16BA06E6E12D1DA27C5249A")) ABORT;
if (!EC_GROUP_set_curve_GFp(group, p, a, b, ctx)) ABORT;
P = EC_POINT_new(group);
Q = EC_POINT_new(group);
R = EC_POINT_new(group);
if (!P || !Q || !R) ABORT;
x = BN_new();
y = BN_new();
z = BN_new();
if (!x || !y || !z) ABORT;
// sm2 testing P256 Vetor
// p£º8542D69E4C044F18E8B92435BF6FF7DE457283915C45517D722EDB8B08F1DFC3
// a£º787968B4FA32C3FD2417842E73BBFEFF2F3C848B6831D7E0EC65228B3937E498
// b£º63E4C6D3B23B0C849CF84241484BFE48F61D59A5B16BA06E6E12D1DA27C5249A
// xG 421DEBD61B62EAB6746434EBC3CC315E32220B3BADD50BDC4C4E6C147FEDD43D
// yG 0680512BCBB42C07D47349D2153B70C4E5D7FDFCBFA36EA1A85841B9E46E09A2
// n: 8542D69E4C044F18E8B92435BF6FF7DD297720630485628D5AE74EE7C32E79B7
if (!BN_hex2bn(&x, "421DEBD61B62EAB6746434EBC3CC315E32220B3BADD50BDC4C4E6C147FEDD43D")) ABORT;
if (!EC_POINT_set_compressed_coordinates_GFp(group, P, x, 0, ctx)) ABORT;
if (!EC_POINT_is_on_curve(group, P, ctx)) ABORT;
if (!BN_hex2bn(&z, "8542D69E4C044F18E8B92435BF6FF7DD297720630485628D5AE74EE7C32E79B7")) ABORT;
if (!EC_GROUP_set_generator(group, P, z, BN_value_one())) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group, P, x, y, ctx)) ABORT;
fprintf(stdout, "\nChinese sm2 algorithm test -- Generator:\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
/* G_y value taken from the standard: */
if (!BN_hex2bn(&z, "0680512BCBB42C07D47349D2153B70C4E5D7FDFCBFA36EA1A85841B9E46E09A2")) ABORT;
if (0 != BN_cmp(y, z)) ABORT;
fprintf(stdout, "verify degree ...");
if (EC_GROUP_get_degree(group) != 256) ABORT;
fprintf(stdout, " ok\n");
fprintf(stdout, "verify group order ...");
fflush(stdout);
if (!EC_GROUP_get_order(group, z, ctx)) ABORT;
if (!EC_GROUP_precompute_mult(group, ctx)) ABORT;
if (!EC_POINT_mul(group, Q, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_is_at_infinity(group, Q)) ABORT;
fflush(stdout);
fprintf(stdout, " ok\n");
//testing ECDSA for SM2
/* create new ecdsa key */
if ((eckey = EC_KEY_new()) == NULL)
goto builtin_err;
if (EC_KEY_set_group(eckey, group) == 0)
{
fprintf(stdout," failed\n");
goto builtin_err;
}
/* create key */
if (!EC_KEY_generate_key(eckey))
{
fprintf(stdout," failed\n");
goto builtin_err;
}
/* check key */
if (!EC_KEY_check_key(eckey))
{
fprintf(stdout," failed\n");
goto builtin_err;
}
/* create signature */
sig_len = ECDSA_size(eckey);
fprintf(stdout,"Siglength is: %d \n",sig_len);
if (!RAND_pseudo_bytes(digest, 20))
{
fprintf(stdout," failed\n");
goto builtin_err;
}
if ((signature = OPENSSL_malloc(sig_len)) == NULL)
goto builtin_err;
if (!SM2_sign(0, digest, 20, signature, &sig_len, eckey))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
fprintf(stdout, "ECSign OK\n");
/* verify signature */
if (SM2_verify(0, digest, 20, signature, sig_len, eckey) != 1)
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
fprintf(stdout, "ECVerify OK\n");
/* cleanup */
OPENSSL_free(signature);
signature = NULL;
EC_KEY_free(eckey);
eckey = NULL;
builtin_err:
EC_POINT_free(P);
EC_POINT_free(Q);
EC_POINT_free(R);
EC_GROUP_free(group);
BN_CTX_free(ctx);
return 0;
}
int SM2_Test_Vecotor2()
{
BN_CTX *ctx = NULL;
BIGNUM *p, *a, *b;
EC_GROUP *group;
EC_POINT *P, *Q, *R;
BIGNUM *x, *y, *z;
EC_KEY *eckey = NULL;
unsigned char *signature;
unsigned char digest[32] = "\xB5\x24\xF5\x52\xCD\x82\xB8\xB0\x28\x47\x6E\x00\x5C\x37\x7F\xB1\x9A\x87\xE6\xFC\x68\x2D\x48\xBB\x5D\x42\xE3\xD9\xB9\xEF\xFE\x76";
int sig_len;
BIGNUM *kinv, *rp,*order;
ECDSA_SIG *ecsig = ECDSA_SIG_new();
EC_POINT * DHPoint = NULL;
// unsigned char *in="123456";
// size_t inlen = 6;
size_t outlen = 256;
unsigned char outkey[256];
size_t keylen = 256;
size_t i;
CRYPTO_set_mem_debug_functions(0, 0, 0, 0, 0);
CRYPTO_mem_ctrl(CRYPTO_MEM_CHECK_ON);
ERR_load_crypto_strings();
RAND_seed(rnd_seed, sizeof rnd_seed); /* or BN_generate_prime may fail */
ctx = BN_CTX_new();
if (!ctx) ABORT;
/* Curve SM2 (Chinese National Algorithm) */
//http://www.oscca.gov.cn/News/201012/News_1197.htm
p = BN_new();
a = BN_new();
b = BN_new();
if (!p || !a || !b) ABORT;
group = EC_GROUP_new(EC_GFp_mont_method()); /* applications should use EC_GROUP_new_curve_GFp
* so that the library gets to choose the EC_METHOD */
if (!group) ABORT;
if (!BN_hex2bn(&p, "8542D69E4C044F18E8B92435BF6FF7DE457283915C45517D722EDB8B08F1DFC3")) ABORT;
if (1 != BN_is_prime_ex(p, BN_prime_checks, ctx, NULL)) ABORT;
if (!BN_hex2bn(&a, "787968B4FA32C3FD2417842E73BBFEFF2F3C848B6831D7E0EC65228B3937E498")) ABORT;
if (!BN_hex2bn(&b, "63E4C6D3B23B0C849CF84241484BFE48F61D59A5B16BA06E6E12D1DA27C5249A")) ABORT;
if (!EC_GROUP_set_curve_GFp(group, p, a, b, ctx)) ABORT;
P = EC_POINT_new(group);
Q = EC_POINT_new(group);
R = EC_POINT_new(group);
if (!P || !Q || !R) ABORT;
x = BN_new();
y = BN_new();
z = BN_new();
if (!x || !y || !z) ABORT;
// sm2 testing P256 Vetor
// p£º8542D69E4C044F18E8B92435BF6FF7DE457283915C45517D722EDB8B08F1DFC3
// a£º787968B4FA32C3FD2417842E73BBFEFF2F3C848B6831D7E0EC65228B3937E498
// b£º63E4C6D3B23B0C849CF84241484BFE48F61D59A5B16BA06E6E12D1DA27C5249A
// xG 421DEBD61B62EAB6746434EBC3CC315E32220B3BADD50BDC4C4E6C147FEDD43D
// yG 0680512BCBB42C07D47349D2153B70C4E5D7FDFCBFA36EA1A85841B9E46E09A2
// n: 8542D69E4C044F18E8B92435BF6FF7DD297720630485628D5AE74EE7C32E79B7
if (!BN_hex2bn(&x, "421DEBD61B62EAB6746434EBC3CC315E32220B3BADD50BDC4C4E6C147FEDD43D")) ABORT;
if (!EC_POINT_set_compressed_coordinates_GFp(group, P, x, 0, ctx)) ABORT;
if (!EC_POINT_is_on_curve(group, P, ctx)) ABORT;
if (!BN_hex2bn(&z, "8542D69E4C044F18E8B92435BF6FF7DD297720630485628D5AE74EE7C32E79B7")) ABORT;
if (!EC_GROUP_set_generator(group, P, z, BN_value_one())) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group, P, x, y, ctx)) ABORT;
fprintf(stdout, "\nChinese sm2 algorithm test -- Generator:\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
/* G_y value taken from the standard: */
if (!BN_hex2bn(&z, "0680512BCBB42C07D47349D2153B70C4E5D7FDFCBFA36EA1A85841B9E46E09A2")) ABORT;
if (0 != BN_cmp(y, z)) ABORT;
fprintf(stdout, "verify degree ...");
if (EC_GROUP_get_degree(group) != 256) ABORT;
fprintf(stdout, " ok\n");
fprintf(stdout, "verify group order ...");
fflush(stdout);
if (!EC_GROUP_get_order(group, z, ctx)) ABORT;
if (!EC_GROUP_precompute_mult(group, ctx)) ABORT;
if (!EC_POINT_mul(group, Q, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_is_at_infinity(group, Q)) ABORT;
fflush(stdout);
fprintf(stdout, " ok\n");
//testing ECDSA for SM2
/* create new ecdsa key */
if ((eckey = EC_KEY_new()) == NULL)
goto builtin_err;
if (EC_KEY_set_group(eckey, group) == 0)
{
fprintf(stdout," failed\n");
goto builtin_err;
}
/* create key */
if (!BN_hex2bn(&z, "128B2FA8BD433C6C068C8D803DFF79792A519A55171B1B650C23661D15897263")) ABORT;
if (!EC_POINT_mul(group,P, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group,P, x, y, ctx)) ABORT;
fprintf(stdout, "\nTesting ECKey Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
EC_KEY_set_private_key(eckey,z);
EC_KEY_set_public_key(eckey, P);
/* check key */
if (!EC_KEY_check_key(eckey))
{
fprintf(stdout," failed\n");
goto builtin_err;
}
/* create signature */
sig_len = ECDSA_size(eckey);
//fprintf(stdout,"Siglength is: %d \n",sig_len);
if ((signature = OPENSSL_malloc(sig_len)) == NULL)
goto builtin_err;
rp = BN_new();
kinv = BN_new();
order = BN_new();
if (!BN_hex2bn(&z, "6CB28D99385C175C94F94E934817663FC176D925DD72B727260DBAAE1FB2F96F")) ABORT;
if (!EC_POINT_mul(group, Q, z, NULL, NULL, ctx))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
if (!EC_POINT_get_affine_coordinates_GFp(group,Q, x, y, ctx))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
fprintf(stdout, "\nTesting K Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
EC_GROUP_get_order(group, order, ctx);
if (!BN_nnmod(rp, x, order, ctx))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
if (!BN_copy(kinv, z ))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
// for(i=0;i<32;i++)
// printf("%02X",digest[i]);
// printf("\n");
if (!SM2_sign_ex(1, digest, 32, signature, &sig_len, kinv, rp, eckey))
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
fprintf(stdout, "ECSign OK\n");
/* verify signature */
if (SM2_verify(1, digest, 32, signature, sig_len, eckey) != 1)
{
fprintf(stdout, " failed\n");
goto builtin_err;
}
fprintf(stdout, "ECVerify OK\n r = 0x");
d2i_ECDSA_SIG(&ecsig, &signature, sig_len);
BNPrintf(ecsig->r);
fprintf(stdout,"\n s = 0x");
BNPrintf(ecsig->s);
fprintf(stdout,"\n");
//testing SM2DH vector
/* create key */
if (!BN_hex2bn(&z, "6FCBA2EF9AE0AB902BC3BDE3FF915D44BA4CC78F88E2F8E7F8996D3B8CCEEDEE")) ABORT;
if (!EC_POINT_mul(group,P, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group,P, x, y, ctx)) ABORT;
fprintf(stdout, "\nTesting A Key Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
EC_KEY_set_private_key(eckey,z);
EC_KEY_set_public_key(eckey, P);
if (!BN_hex2bn(&z, "5E35D7D3F3C54DBAC72E61819E730B019A84208CA3A35E4C2E353DFCCB2A3B53")) ABORT;
if (!EC_POINT_mul(group,Q, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group,Q, x, y, ctx)) ABORT;
fprintf(stdout, "\nTesting B Key Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
//EC_KEY_set_private_key(eckey,z);
//EC_KEY_set_public_key(eckey, P);
if (!BN_hex2bn(&z, "33FE21940342161C55619C4A0C060293D543C80AF19748CE176D83477DE71C80")) ABORT;
if (!EC_POINT_mul(group,P, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group,P, x, y, ctx)) ABORT;
fprintf(stdout, "\nTesting Rb Key Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
if (!BN_hex2bn(&z, "83A2C9C8B96E5AF70BD480B472409A9A327257F1EBB73F5B073354B248668563")) ABORT;
if (!EC_POINT_mul(group,R, z, NULL, NULL, ctx)) ABORT;
if (!EC_POINT_get_affine_coordinates_GFp(group,R, x, y, ctx)) ABORT;
fprintf(stdout, "\nTesting Ra Key Point\n x = 0x");
BNPrintf(x);
fprintf(stdout, "\n y = 0x");
BNPrintf( y);
fprintf(stdout, "\n");
SM2_DH_key(group,P, Q, z,eckey,outkey,keylen);
fprintf(stdout,"\nExchange key --KDF(Xv||Yv)-- :");
for(i=0; i<outlen; i++)
printf("%02X",outkey[i]);
printf("\n");
builtin_err:
OPENSSL_free(signature);
signature = NULL;
EC_POINT_free(P);
EC_POINT_free(Q);
EC_POINT_free(R);
EC_POINT_free(DHPoint);
EC_KEY_free(eckey);
eckey = NULL;
EC_GROUP_free(group);
BN_CTX_free(ctx);
return 0;
}
int main()
{
CRYPTO_set_mem_debug_functions(0, 0, 0, 0, 0);
CRYPTO_mem_ctrl(CRYPTO_MEM_CHECK_ON);
ERR_load_crypto_strings();
RAND_seed(rnd_seed, sizeof rnd_seed);
SM2_Test_Vecotor2();
CRYPTO_cleanup_all_ex_data();
ERR_free_strings();
ERR_remove_state(0);
CRYPTO_mem_leaks_fp(stderr);
return 0;
}
- SM3杂凑算法
- 用途:商用密码应用中的数字签名和验证,消息认证码的生成与验证以及随机数的生成。
- 密码学对应算法:SHA-1,SHA-3,MD5
sm3:
/*
* SM3 Hash alogrith
* thanks to Xyssl
* author:goldboar
* email:goldboar@163.com
* 2011-10-26
*/
//Testing data from SM3 Standards
//http://www.oscca.gov.cn/News/201012/News_1199.htm
// Sample 1
// Input:"abc"
// Output:66c7f0f4 62eeedd9 d1f2d46b dc10e4e2 4167c487 5cf2f7a2 297da02b 8f4ba8e0
// Sample 2
// Input:"abcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcdabcd"
// Outpuf:debe9ff9 2275b8a1 38604889 c18e5a4d 6fdb70e5 387e5765 293dcba3 9c0c5732
#include "sm3.h"
#include <string.h>
#include <stdio.h>
/*
* 32-bit integer manipulation macros (big endian)
*/
#ifndef GET_ULONG_BE
#define GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << 24 ) \
| ( (unsigned long) (b)[(i) + 1] << 16 ) \
| ( (unsigned long) (b)[(i) + 2] << 8 ) \
| ( (unsigned long) (b)[(i) + 3] ); \
}
#endif
#ifndef PUT_ULONG_BE
#define PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> 24 ); \
(b)[(i) + 1] = (unsigned char) ( (n) >> 16 ); \
(b)[(i) + 2] = (unsigned char) ( (n) >> 8 ); \
(b)[(i) + 3] = (unsigned char) ( (n) ); \
}
#endif
/*
* SM3 context setup
*/
void sm3_starts( sm3_context *ctx )
{
ctx->total[0] = 0;
ctx->total[1] = 0;
ctx->state[0] = 0x7380166F;
ctx->state[1] = 0x4914B2B9;
ctx->state[2] = 0x172442D7;
ctx->state[3] = 0xDA8A0600;
ctx->state[4] = 0xA96F30BC;
ctx->state[5] = 0x163138AA;
ctx->state[6] = 0xE38DEE4D;
ctx->state[7] = 0xB0FB0E4E;
}
static void sm3_process( sm3_context *ctx, unsigned char data[64] )
{
unsigned long SS1, SS2, TT1, TT2, W[68],W1[64];
unsigned long A, B, C, D, E, F, G, H;
unsigned long T[64];
unsigned long Temp1,Temp2,Temp3,Temp4,Temp5;
int j;
#ifdef _DEBUG
int i;
#endif
// for(j=0; j < 68; j++)
// W[j] = 0;
// for(j=0; j < 64; j++)
// W1[j] = 0;
for(j = 0; j < 16; j++)
T[j] = 0x79CC4519;
for(j =16; j < 64; j++)
T[j] = 0x7A879D8A;
GET_ULONG_BE( W[ 0], data, 0 );
GET_ULONG_BE( W[ 1], data, 4 );
GET_ULONG_BE( W[ 2], data, 8 );
GET_ULONG_BE( W[ 3], data, 12 );
GET_ULONG_BE( W[ 4], data, 16 );
GET_ULONG_BE( W[ 5], data, 20 );
GET_ULONG_BE( W[ 6], data, 24 );
GET_ULONG_BE( W[ 7], data, 28 );
GET_ULONG_BE( W[ 8], data, 32 );
GET_ULONG_BE( W[ 9], data, 36 );
GET_ULONG_BE( W[10], data, 40 );
GET_ULONG_BE( W[11], data, 44 );
GET_ULONG_BE( W[12], data, 48 );
GET_ULONG_BE( W[13], data, 52 );
GET_ULONG_BE( W[14], data, 56 );
GET_ULONG_BE( W[15], data, 60 );
#ifdef _DEBUG
printf("Message with padding:\n");
for(i=0; i< 8; i++)
printf("%08x ",W[i]);
printf("\n");
for(i=8; i< 16; i++)
printf("%08x ",W[i]);
printf("\n");
#endif
#define FF0(x,y,z) ( (x) ^ (y) ^ (z))
#define FF1(x,y,z) (((x) & (y)) | ( (x) & (z)) | ( (y) & (z)))
#define GG0(x,y,z) ( (x) ^ (y) ^ (z))
#define GG1(x,y,z) (((x) & (y)) | ( (~(x)) & (z)) )
#define SHL(x,n) (((x) & 0xFFFFFFFF) << n)
#define ROTL(x,n) (SHL((x),n) | ((x) >> (32 - n)))
#define P0(x) ((x) ^ ROTL((x),9) ^ ROTL((x),17))
#define P1(x) ((x) ^ ROTL((x),15) ^ ROTL((x),23))
for(j = 16; j < 68; j++ )
{
//W[j] = P1( W[j-16] ^ W[j-9] ^ ROTL(W[j-3],15)) ^ ROTL(W[j - 13],7 ) ^ W[j-6];
//Why thd release's result is different with the debug's ?
//Below is okay. Interesting, Perhaps VC6 has a bug of Optimizaiton.
Temp1 = W[j-16] ^ W[j-9];
Temp2 = ROTL(W[j-3],15);
Temp3 = Temp1 ^ Temp2;
Temp4 = P1(Temp3);
Temp5 = ROTL(W[j - 13],7 ) ^ W[j-6];
W[j] = Temp4 ^ Temp5;
}
#ifdef _DEBUG
printf("Expanding message W0-67:\n");
for(i=0; i<68; i++)
{
printf("%08x ",W[i]);
if(((i+1) % 8) == 0) printf("\n");
}
printf("\n");
#endif
for(j = 0; j < 64; j++)
{
W1[j] = W[j] ^ W[j+4];
}
#ifdef _DEBUG
printf("Expanding message W'0-63:\n");
for(i=0; i<64; i++)
{
printf("%08x ",W1[i]);
if(((i+1) % 8) == 0) printf("\n");
}
printf("\n");
#endif
A = ctx->state[0];
B = ctx->state[1];
C = ctx->state[2];
D = ctx->state[3];
E = ctx->state[4];
F = ctx->state[5];
G = ctx->state[6];
H = ctx->state[7];
#ifdef _DEBUG
printf("j A B C D E F G H\n");
printf(" %08x %08x %08x %08x %08x %08x %08x %08x\n",A,B,C,D,E,F,G,H);
#endif
for(j =0; j < 16; j++)
{
SS1 = ROTL((ROTL(A,12) + E + ROTL(T[j],j)), 7);
SS2 = SS1 ^ ROTL(A,12);
TT1 = FF0(A,B,C) + D + SS2 + W1[j];
TT2 = GG0(E,F,G) + H + SS1 + W[j];
D = C;
C = ROTL(B,9);
B = A;
A = TT1;
H = G;
G = ROTL(F,19);
F = E;
E = P0(TT2);
#ifdef _DEBUG
printf("%02d %08x %08x %08x %08x %08x %08x %08x %08x\n",j,A,B,C,D,E,F,G,H);
#endif
}
for(j =16; j < 64; j++)
{
SS1 = ROTL((ROTL(A,12) + E + ROTL(T[j],j)), 7);
SS2 = SS1 ^ ROTL(A,12);
TT1 = FF1(A,B,C) + D + SS2 + W1[j];
TT2 = GG1(E,F,G) + H + SS1 + W[j];
D = C;
C = ROTL(B,9);
B = A;
A = TT1;
H = G;
G = ROTL(F,19);
F = E;
E = P0(TT2);
#ifdef _DEBUG
printf("%02d %08x %08x %08x %08x %08x %08x %08x %08x\n",j,A,B,C,D,E,F,G,H);
#endif
}
ctx->state[0] ^= A;
ctx->state[1] ^= B;
ctx->state[2] ^= C;
ctx->state[3] ^= D;
ctx->state[4] ^= E;
ctx->state[5] ^= F;
ctx->state[6] ^= G;
ctx->state[7] ^= H;
#ifdef _DEBUG
printf(" %08x %08x %08x %08x %08x %08x %08x %08x\n",ctx->state[0],ctx->state[1],ctx->state[2],
ctx->state[3],ctx->state[4],ctx->state[5],ctx->state[6],ctx->state[7]);
#endif
}
/*
* SM3 process buffer
*/
void sm3_update( sm3_context *ctx, unsigned char *input, int ilen )
{
int fill;
unsigned long left;
if( ilen <= 0 )
return;
left = ctx->total[0] & 0x3F;
fill = 64 - left;
ctx->total[0] += ilen;
ctx->total[0] &= 0xFFFFFFFF;
if( ctx->total[0] < (unsigned long) ilen )
ctx->total[1]++;
if( left && ilen >= fill )
{
memcpy( (void *) (ctx->buffer + left),
(void *) input, fill );
sm3_process( ctx, ctx->buffer );
input += fill;
ilen -= fill;
left = 0;
}
while( ilen >= 64 )
{
sm3_process( ctx, input );
input += 64;
ilen -= 64;
}
if( ilen > 0 )
{
memcpy( (void *) (ctx->buffer + left),
(void *) input, ilen );
}
}
static const unsigned char sm3_padding[64] =
{
0x80, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0
};
/*
* SM3 final digest
*/
void sm3_finish( sm3_context *ctx, unsigned char output[32] )
{
unsigned long last, padn;
unsigned long high, low;
unsigned char msglen[8];
high = ( ctx->total[0] >> 29 )
| ( ctx->total[1] << 3 );
low = ( ctx->total[0] << 3 );
PUT_ULONG_BE( high, msglen, 0 );
PUT_ULONG_BE( low, msglen, 4 );
last = ctx->total[0] & 0x3F;
padn = ( last < 56 ) ? ( 56 - last ) : ( 120 - last );
sm3_update( ctx, (unsigned char *) sm3_padding, padn );
sm3_update( ctx, msglen, 8 );
PUT_ULONG_BE( ctx->state[0], output, 0 );
PUT_ULONG_BE( ctx->state[1], output, 4 );
PUT_ULONG_BE( ctx->state[2], output, 8 );
PUT_ULONG_BE( ctx->state[3], output, 12 );
PUT_ULONG_BE( ctx->state[4], output, 16 );
PUT_ULONG_BE( ctx->state[5], output, 20 );
PUT_ULONG_BE( ctx->state[6], output, 24 );
PUT_ULONG_BE( ctx->state[7], output, 28 );
}
/*
* output = SM3( input buffer )
*/
void sm3( unsigned char *input, int ilen,
unsigned char output[32] )
{
sm3_context ctx;
sm3_starts( &ctx );
sm3_update( &ctx, input, ilen );
sm3_finish( &ctx, output );
memset( &ctx, 0, sizeof( sm3_context ) );
}
/*
* output = SM3( file contents )
*/
int sm3_file( char *path, unsigned char output[32] )
{
FILE *f;
size_t n;
sm3_context ctx;
unsigned char buf[1024];
if( ( f = fopen( path, "rb" ) ) == NULL )
return( 1 );
sm3_starts( &ctx );
while( ( n = fread( buf, 1, sizeof( buf ), f ) ) > 0 )
sm3_update( &ctx, buf, (int) n );
sm3_finish( &ctx, output );
memset( &ctx, 0, sizeof( sm3_context ) );
if( ferror( f ) != 0 )
{
fclose( f );
return( 2 );
}
fclose( f );
return( 0 );
}
/*
* SM3 HMAC context setup
*/
void sm3_hmac_starts( sm3_context *ctx, unsigned char *key, int keylen )
{
int i;
unsigned char sum[32];
if( keylen > 64 )
{
sm3( key, keylen, sum );
keylen = 32;
//keylen = ( is224 ) ? 28 : 32;
key = sum;
}
memset( ctx->ipad, 0x36, 64 );
memset( ctx->opad, 0x5C, 64 );
for( i = 0; i < keylen; i++ )
{
ctx->ipad[i] = (unsigned char)( ctx->ipad[i] ^ key[i] );
ctx->opad[i] = (unsigned char)( ctx->opad[i] ^ key[i] );
}
sm3_starts( ctx);
sm3_update( ctx, ctx->ipad, 64 );
memset( sum, 0, sizeof( sum ) );
}
/*
* SM3 HMAC process buffer
*/
void sm3_hmac_update( sm3_context *ctx, unsigned char *input, int ilen )
{
sm3_update( ctx, input, ilen );
}
/*
* SM3 HMAC final digest
*/
void sm3_hmac_finish( sm3_context *ctx, unsigned char output[32] )
{
int hlen;
unsigned char tmpbuf[32];
//is224 = ctx->is224;
hlen = 32;
sm3_finish( ctx, tmpbuf );
sm3_starts( ctx );
sm3_update( ctx, ctx->opad, 64 );
sm3_update( ctx, tmpbuf, hlen );
sm3_finish( ctx, output );
memset( tmpbuf, 0, sizeof( tmpbuf ) );
}
/*
* output = HMAC-SM#( hmac key, input buffer )
*/
void sm3_hmac( unsigned char *key, int keylen,
unsigned char *input, int ilen,
unsigned char output[32] )
{
sm3_context ctx;
sm3_hmac_starts( &ctx, key, keylen);
sm3_hmac_update( &ctx, input, ilen );
sm3_hmac_finish( &ctx, output );
memset( &ctx, 0, sizeof( sm3_context ) );
}
sm3test
#include <string.h>
#include <stdio.h>
#include "sm3.h"
int main( int argc, char *argv[] )
{
unsigned char *input = "abc";
int ilen = 3;
unsigned char output[32];
int i;
sm3_context ctx;
printf("Message:\n");
printf("%s\n",input);
sm3(input, ilen, output);
printf("Hash:\n ");
for(i=0; i<32; i++)
{
printf("%02x",output[i]);
if (((i+1) % 4 ) == 0) printf(" ");
}
printf("\n");
printf("Message:\n");
for(i=0; i < 16; i++)
printf("abcd");
printf("\n");
sm3_starts( &ctx );
for(i=0; i < 16; i++)
sm3_update( &ctx, "abcd", 4 );
sm3_finish( &ctx, output );
memset( &ctx, 0, sizeof( sm3_context ) );
printf("Hash:\n ");
for(i=0; i<32; i++)
{
printf("%02x",output[i]);
if (((i+1) % 4 ) == 0) printf(" ");
}
printf("\n");
//getch(); //VS2008
}
- SM4对称分组算法
- 用途:无线局域网产品。
- 密码学对应算法:DES,AES
SM4:
/*
* SM4 Encryption alogrithm (SMS4 algorithm)
* GM/T 0002-2012 Chinese National Standard ref:http://www.oscca.gov.cn/
* thanks to Xyssl
* thnaks and refers to http://hi.baidu.com/numax/blog/item/80addfefddfb93e4cf1b3e61.html
* author:goldboar
* email:goldboar@163.com
* 2012-4-20
*/
// Test vector 1
// plain: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// key: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// round key and temp computing result:
// rk[ 0] = f12186f9 X[ 0] = 27fad345
// rk[ 1] = 41662b61 X[ 1] = a18b4cb2
// rk[ 2] = 5a6ab19a X[ 2] = 11c1e22a
// rk[ 3] = 7ba92077 X[ 3] = cc13e2ee
// rk[ 4] = 367360f4 X[ 4] = f87c5bd5
// rk[ 5] = 776a0c61 X[ 5] = 33220757
// rk[ 6] = b6bb89b3 X[ 6] = 77f4c297
// rk[ 7] = 24763151 X[ 7] = 7a96f2eb
// rk[ 8] = a520307c X[ 8] = 27dac07f
// rk[ 9] = b7584dbd X[ 9] = 42dd0f19
// rk[10] = c30753ed X[10] = b8a5da02
// rk[11] = 7ee55b57 X[11] = 907127fa
// rk[12] = 6988608c X[12] = 8b952b83
// rk[13] = 30d895b7 X[13] = d42b7c59
// rk[14] = 44ba14af X[14] = 2ffc5831
// rk[15] = 104495a1 X[15] = f69e6888
// rk[16] = d120b428 X[16] = af2432c4
// rk[17] = 73b55fa3 X[17] = ed1ec85e
// rk[18] = cc874966 X[18] = 55a3ba22
// rk[19] = 92244439 X[19] = 124b18aa
// rk[20] = e89e641f X[20] = 6ae7725f
// rk[21] = 98ca015a X[21] = f4cba1f9
// rk[22] = c7159060 X[22] = 1dcdfa10
// rk[23] = 99e1fd2e X[23] = 2ff60603
// rk[24] = b79bd80c X[24] = eff24fdc
// rk[25] = 1d2115b0 X[25] = 6fe46b75
// rk[26] = 0e228aeb X[26] = 893450ad
// rk[27] = f1780c81 X[27] = 7b938f4c
// rk[28] = 428d3654 X[28] = 536e4246
// rk[29] = 62293496 X[29] = 86b3e94f
// rk[30] = 01cf72e5 X[30] = d206965e
// rk[31] = 9124a012 X[31] = 681edf34
// cypher: 68 1e df 34 d2 06 96 5e 86 b3 e9 4f 53 6e 42 46
//
// test vector 2
// the same key and plain 1000000 times coumpting
// plain: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// key: 01 23 45 67 89 ab cd ef fe dc ba 98 76 54 32 10
// cypher: 59 52 98 c7 c6 fd 27 1f 04 02 f8 04 c3 3d 3f 66
#include "sm4.h"
#include <string.h>
#include <stdio.h>
/*
* 32-bit integer manipulation macros (big endian)
*/
#ifndef GET_ULONG_BE
#define GET_ULONG_BE(n,b,i) \
{ \
(n) = ( (unsigned long) (b)[(i) ] << 24 ) \
| ( (unsigned long) (b)[(i) + 1] << 16 ) \
| ( (unsigned long) (b)[(i) + 2] << 8 ) \
| ( (unsigned long) (b)[(i) + 3] ); \
}
#endif
#ifndef PUT_ULONG_BE
#define PUT_ULONG_BE(n,b,i) \
{ \
(b)[(i) ] = (unsigned char) ( (n) >> 24 ); \
(b)[(i) + 1] = (unsigned char) ( (n) >> 16 ); \
(b)[(i) + 2] = (unsigned char) ( (n) >> 8 ); \
(b)[(i) + 3] = (unsigned char) ( (n) ); \
}
#endif
/*
*rotate shift left marco definition
*
*/
#define SHL(x,n) (((x) & 0xFFFFFFFF) << n)
#define ROTL(x,n) (SHL((x),n) | ((x) >> (32 - n)))
#define SWAP(a,b) { unsigned long t = a; a = b; b = t; t = 0; }
/*
* Expanded SM4 S-boxes
/* Sbox table: 8bits input convert to 8 bits output*/
static const unsigned char SboxTable[16][16] =
{
{0xd6,0x90,0xe9,0xfe,0xcc,0xe1,0x3d,0xb7,0x16,0xb6,0x14,0xc2,0x28,0xfb,0x2c,0x05},
{0x2b,0x67,0x9a,0x76,0x2a,0xbe,0x04,0xc3,0xaa,0x44,0x13,0x26,0x49,0x86,0x06,0x99},
{0x9c,0x42,0x50,0xf4,0x91,0xef,0x98,0x7a,0x33,0x54,0x0b,0x43,0xed,0xcf,0xac,0x62},
{0xe4,0xb3,0x1c,0xa9,0xc9,0x08,0xe8,0x95,0x80,0xdf,0x94,0xfa,0x75,0x8f,0x3f,0xa6},
{0x47,0x07,0xa7,0xfc,0xf3,0x73,0x17,0xba,0x83,0x59,0x3c,0x19,0xe6,0x85,0x4f,0xa8},
{0x68,0x6b,0x81,0xb2,0x71,0x64,0xda,0x8b,0xf8,0xeb,0x0f,0x4b,0x70,0x56,0x9d,0x35},
{0x1e,0x24,0x0e,0x5e,0x63,0x58,0xd1,0xa2,0x25,0x22,0x7c,0x3b,0x01,0x21,0x78,0x87},
{0xd4,0x00,0x46,0x57,0x9f,0xd3,0x27,0x52,0x4c,0x36,0x02,0xe7,0xa0,0xc4,0xc8,0x9e},
{0xea,0xbf,0x8a,0xd2,0x40,0xc7,0x38,0xb5,0xa3,0xf7,0xf2,0xce,0xf9,0x61,0x15,0xa1},
{0xe0,0xae,0x5d,0xa4,0x9b,0x34,0x1a,0x55,0xad,0x93,0x32,0x30,0xf5,0x8c,0xb1,0xe3},
{0x1d,0xf6,0xe2,0x2e,0x82,0x66,0xca,0x60,0xc0,0x29,0x23,0xab,0x0d,0x53,0x4e,0x6f},
{0xd5,0xdb,0x37,0x45,0xde,0xfd,0x8e,0x2f,0x03,0xff,0x6a,0x72,0x6d,0x6c,0x5b,0x51},
{0x8d,0x1b,0xaf,0x92,0xbb,0xdd,0xbc,0x7f,0x11,0xd9,0x5c,0x41,0x1f,0x10,0x5a,0xd8},
{0x0a,0xc1,0x31,0x88,0xa5,0xcd,0x7b,0xbd,0x2d,0x74,0xd0,0x12,0xb8,0xe5,0xb4,0xb0},
{0x89,0x69,0x97,0x4a,0x0c,0x96,0x77,0x7e,0x65,0xb9,0xf1,0x09,0xc5,0x6e,0xc6,0x84},
{0x18,0xf0,0x7d,0xec,0x3a,0xdc,0x4d,0x20,0x79,0xee,0x5f,0x3e,0xd7,0xcb,0x39,0x48}
};
/* System parameter */
static const unsigned long FK[4] = {0xa3b1bac6,0x56aa3350,0x677d9197,0xb27022dc};
/* fixed parameter */
static const unsigned long CK[32] =
{
0x00070e15,0x1c232a31,0x383f464d,0x545b6269,
0x70777e85,0x8c939aa1,0xa8afb6bd,0xc4cbd2d9,
0xe0e7eef5,0xfc030a11,0x181f262d,0x343b4249,
0x50575e65,0x6c737a81,0x888f969d,0xa4abb2b9,
0xc0c7ced5,0xdce3eaf1,0xf8ff060d,0x141b2229,
0x30373e45,0x4c535a61,0x686f767d,0x848b9299,
0xa0a7aeb5,0xbcc3cad1,0xd8dfe6ed,0xf4fb0209,
0x10171e25,0x2c333a41,0x484f565d,0x646b7279
};
/*
* private function:
* look up in SboxTable and get the related value.
* args: [in] inch: 0x00~0xFF (8 bits unsigned value).
*/
static unsigned char sm4Sbox(unsigned char inch)
{
unsigned char *pTable = (unsigned char *)SboxTable;
unsigned char retVal = (unsigned char)(pTable[inch]);
return retVal;
}
/*
* private F(Lt) function:
* "T algorithm" == "L algorithm" + "t algorithm".
* args: [in] a: a is a 32 bits unsigned value;
* return: c: c is calculated with line algorithm "L" and nonline algorithm "t"
*/
static unsigned long sm4Lt(unsigned long ka)
{
unsigned long bb = 0;
unsigned long c = 0;
unsigned char a[4];
unsigned char b[4];
PUT_ULONG_BE(ka,a,0)
b[0] = sm4Sbox(a[0]);
b[1] = sm4Sbox(a[1]);
b[2] = sm4Sbox(a[2]);
b[3] = sm4Sbox(a[3]);
GET_ULONG_BE(bb,b,0)
c =bb^(ROTL(bb, 2))^(ROTL(bb, 10))^(ROTL(bb, 18))^(ROTL(bb, 24));
return c;
}
/*
* private F function:
* Calculating and getting encryption/decryption contents.
* args: [in] x0: original contents;
* args: [in] x1: original contents;
* args: [in] x2: original contents;
* args: [in] x3: original contents;
* args: [in] rk: encryption/decryption key;
* return the contents of encryption/decryption contents.
*/
static unsigned long sm4F(unsigned long x0, unsigned long x1, unsigned long x2, unsigned long x3, unsigned long rk)
{
return (x0^sm4Lt(x1^x2^x3^rk));
}
/* private function:
* Calculating round encryption key.
* args: [in] a: a is a 32 bits unsigned value;
* return: sk[i]: i{0,1,2,3,...31}.
*/
static unsigned long sm4CalciRK(unsigned long ka)
{
unsigned long bb = 0;
unsigned long rk = 0;
unsigned char a[4];
unsigned char b[4];
PUT_ULONG_BE(ka,a,0)
b[0] = sm4Sbox(a[0]);
b[1] = sm4Sbox(a[1]);
b[2] = sm4Sbox(a[2]);
b[3] = sm4Sbox(a[3]);
GET_ULONG_BE(bb,b,0)
rk = bb^(ROTL(bb, 13))^(ROTL(bb, 23));
return rk;
}
static void sm4_setkey( unsigned long SK[32], unsigned char key[16] )
{
unsigned long MK[4];
unsigned long k[36];
unsigned long i = 0;
GET_ULONG_BE( MK[0], key, 0 );
GET_ULONG_BE( MK[1], key, 4 );
GET_ULONG_BE( MK[2], key, 8 );
GET_ULONG_BE( MK[3], key, 12 );
k[0] = MK[0]^FK[0];
k[1] = MK[1]^FK[1];
k[2] = MK[2]^FK[2];
k[3] = MK[3]^FK[3];
for(; i<32; i++)
{
k[i+4] = k[i] ^ (sm4CalciRK(k[i+1]^k[i+2]^k[i+3]^CK[i]));
SK[i] = k[i+4];
}
}
/*
* SM4 standard one round processing
*
*/
static void sm4_one_round( unsigned long sk[32],
unsigned char input[16],
unsigned char output[16] )
{
unsigned long i = 0;
unsigned long ulbuf[36];
memset(ulbuf, 0, sizeof(ulbuf));
GET_ULONG_BE( ulbuf[0], input, 0 )
GET_ULONG_BE( ulbuf[1], input, 4 )
GET_ULONG_BE( ulbuf[2], input, 8 )
GET_ULONG_BE( ulbuf[3], input, 12 )
while(i<32)
{
ulbuf[i+4] = sm4F(ulbuf[i], ulbuf[i+1], ulbuf[i+2], ulbuf[i+3], sk[i]);
// #ifdef _DEBUG
// printf("rk(%02d) = 0x%08x, X(%02d) = 0x%08x \n",i,sk[i], i, ulbuf[i+4] );
// #endif
i++;
}
PUT_ULONG_BE(ulbuf[35],output,0);
PUT_ULONG_BE(ulbuf[34],output,4);
PUT_ULONG_BE(ulbuf[33],output,8);
PUT_ULONG_BE(ulbuf[32],output,12);
}
/*
* SM4 key schedule (128-bit, encryption)
*/
void sm4_setkey_enc( sm4_context *ctx, unsigned char key[16] )
{
ctx->mode = SM4_ENCRYPT;
sm4_setkey( ctx->sk, key );
}
/*
* SM4 key schedule (128-bit, decryption)
*/
void sm4_setkey_dec( sm4_context *ctx, unsigned char key[16] )
{
int i;
ctx->mode = SM4_ENCRYPT;
sm4_setkey( ctx->sk, key );
for( i = 0; i < 16; i ++ )
{
SWAP( ctx->sk[ i ], ctx->sk[ 31-i] );
}
}
/*
* SM4-ECB block encryption/decryption
*/
void sm4_crypt_ecb( sm4_context *ctx,
int mode,
int length,
unsigned char *input,
unsigned char *output)
{
while( length > 0 )
{
sm4_one_round( ctx->sk, input, output );
input += 16;
output += 16;
length -= 16;
}
}
/*
* SM4-CBC buffer encryption/decryption
*/
void sm4_crypt_cbc( sm4_context *ctx,
int mode,
int length,
unsigned char iv[16],
unsigned char *input,
unsigned char *output )
{
int i;
unsigned char temp[16];
if( mode == SM4_ENCRYPT )
{
while( length > 0 )
{
for( i = 0; i < 16; i++ )
output[i] = (unsigned char)( input[i] ^ iv[i] );
sm4_one_round( ctx->sk, output, output );
memcpy( iv, output, 16 );
input += 16;
output += 16;
length -= 16;
}
}
else /* SM4_DECRYPT */
{
while( length > 0 )
{
memcpy( temp, input, 16 );
sm4_one_round( ctx->sk, input, output );
for( i = 0; i < 16; i++ )
output[i] = (unsigned char)( output[i] ^ iv[i] );
memcpy( iv, temp, 16 );
input += 16;
output += 16;
length -= 16;
}
}
}
sm4test
/*
* SM4/SMS4 algorithm test programme
* 2012-4-21
*/
#include <string.h>
#include <stdio.h>
#include "sm4.h"
int main()
{
unsigned char key[16] = {0x01,0x23,0x45,0x67,0x89,0xab,0xcd,0xef,0xfe,0xdc,0xba,0x98,0x76,0x54,0x32,0x10};
unsigned char input[16] = {0x01,0x23,0x45,0x67,0x89,0xab,0xcd,0xef,0xfe,0xdc,0xba,0x98,0x76,0x54,0x32,0x10};
unsigned char output[16];
sm4_context ctx;
unsigned long i;
//encrypt standard testing vector
sm4_setkey_enc(&ctx,key);
sm4_crypt_ecb(&ctx,1,16,input,output);
for(i=0;i<16;i++)
printf("%02x ", output[i]);
printf("\n");
//decrypt testing
sm4_setkey_dec(&ctx,key);
sm4_crypt_ecb(&ctx,0,16,output,output);
for(i=0;i<16;i++)
printf("%02x ", output[i]);
printf("\n");
//decrypt 1M times testing vector based on standards.
i = 0;
sm4_setkey_enc(&ctx,key);
while (i<1000000)
{
sm4_crypt_ecb(&ctx,1,16,input,input);
i++;
}
for(i=0;i<16;i++)
printf("%02x ", input[i]);
printf("\n");
return 0;
}
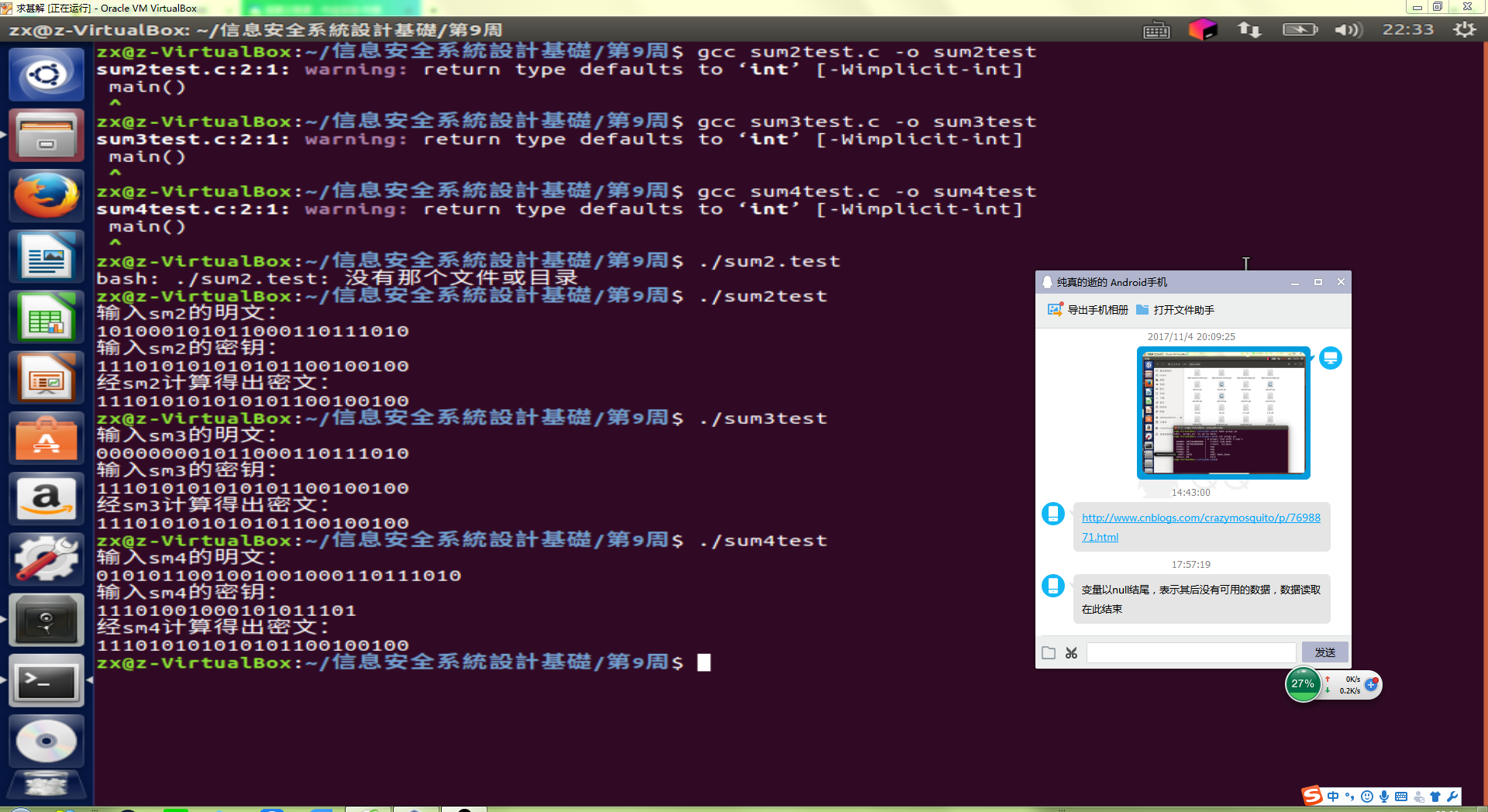
运行截图:
实验感想:
- 实验比较简单,一步一步走就完成了实验,对此我还是比较满意的。因为这次实验比较容易。



