msf自动连接postgresql配置
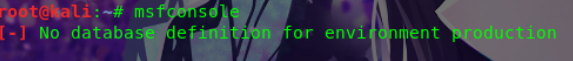
今天做了一下msf连接数据库的配置,中间碰到了一些坑点这里就不详细叙述了,开始正确的操作方式。
首先对postgresql进行配置以方便连接。
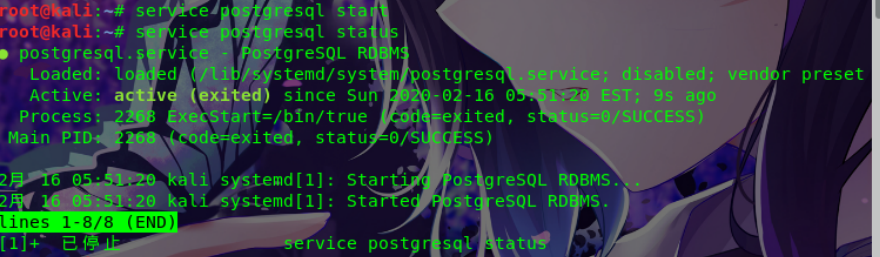
root@kali:~# service postgresql start #启动数据库
root@kali:~# service postgresql status
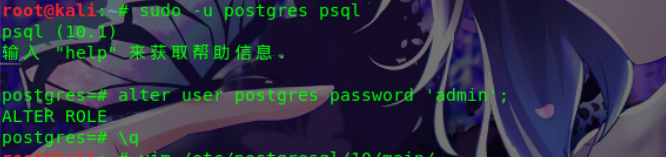
root@kali:~# sudo -u postgres psql
psql (10.1)
输入 "help" 来获取帮助信息.
postgres=# alter user postgres password 'admin';
ALTER ROLE
postgres=# \q
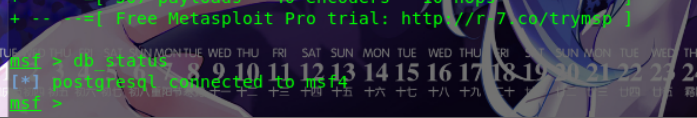
root@kali:~# msfconsole #测试数据库连接状态 ### ### msf > db_connect msf:admin@localhost/msf [*] Rebuilding the module cache in the background... msf > db_status [*] postgresql connected to msf msf > search 2015-0531 [!] Module database cache not built yet, using slow search #这里要稍等一下才会正常,可以考虑关闭应用重启一下 msf > exit
修改数据库文件:postgresql.conf和pg_hba.conf
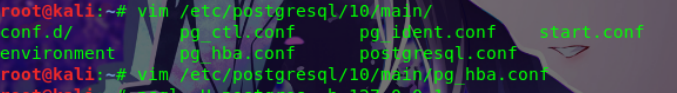
文件第一处(59行)
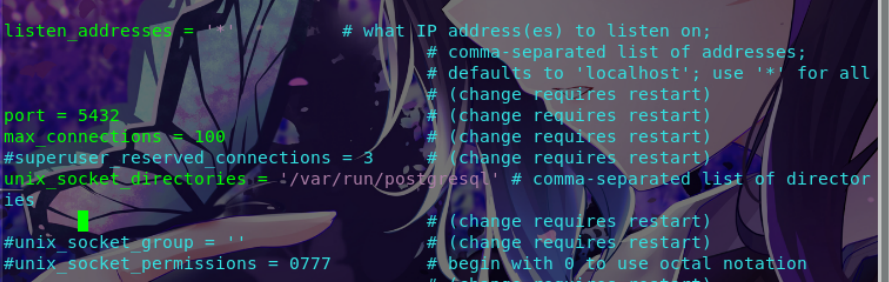
文件第二处 (88行)

第二个文件最会添加。
在文档最后添加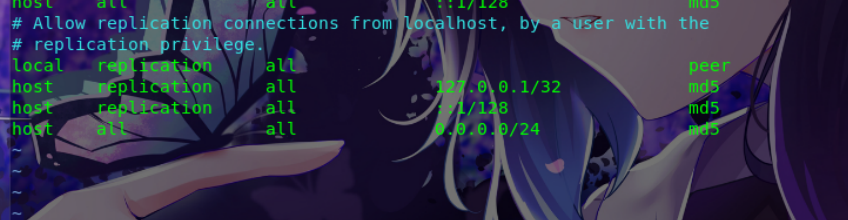
连接数据库
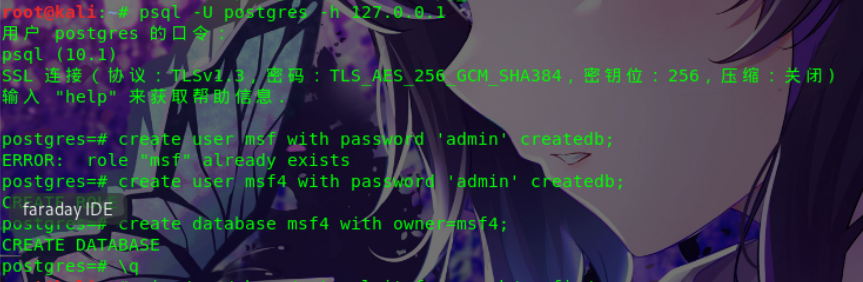
这里因为之前有msf了所以从新创一个msf4(正常的可略过)
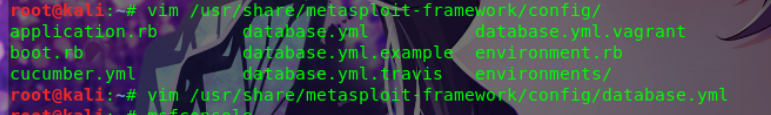
这里如果没有database.yml文件可以先cp database.yml.example database.yml 然后进行修改。

root@kali:/usr/share/metasploit-framework/config# cp database.yml.example database.yml root@kali:/usr/share/metasploit-framework/config# vi database.yml root@kali:/usr/share/metasploit-framework/config# cat database.yml # Please only use postgresql bound to a TCP port. # Only postgresql is supportable for metasploit-framework # these days. (No SQLite, no MySQL). # # To set up a metasploit database, follow the directions hosted at: # http://r-7.co/MSF-DEV#set-up-postgresql development: &pgsql adapter: postgresql database: msf #修改这里 username: msf #这里 password: admin #还有这里 host: localhost port: 5432 pool: 5 #这里看心情 timeout: 5 # You will often want to seperate your databases between dev # mode and prod mode. Absent a production db, though, defaulting # to dev is pretty sensible for many developer-users. production: &production <<: *pgsql # Warning: The database defined as "test" will be erased and # re-generated from your development database when you run "rake". # Do not set this db to the same as development or production. # # Note also, sqlite3 is totally unsupported by Metasploit now. test: <<: *pgsql database: metasploit_framework_test username: metasploit_framework_test password: ___________________________
最后如重新启动msf就可以了,当然还可以在配置下数据库自动开启
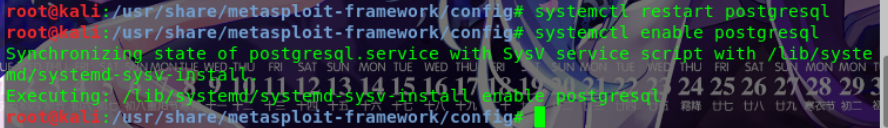
root@kali:~# systemctl start postgresql
root@kali:~# systemctl enable postgresql
root@kali:~# msfconsole #进入msf看效果
### ### msf > db_status [*] postgresql connected to msf msf > search CVE-2015-0311 Matching Modules ================ Name Disclosure Date Rank Description ---- --------------- ---- ----------- exploit/multi/browser/adobe_flash_uncompress_zlib_uaf 2014-04-28 great Adobe Flash Player ByteArray UncompressViaZlibVariant Use After Free msf >