第4篇创建harbor私有镜像库
一、部署准备:
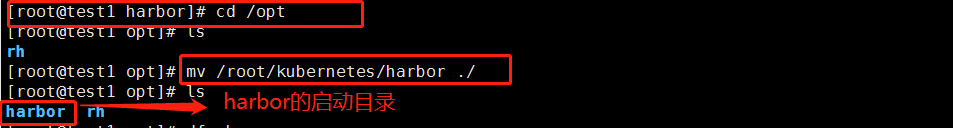
1、准备harbor软件包
在部署节点上:

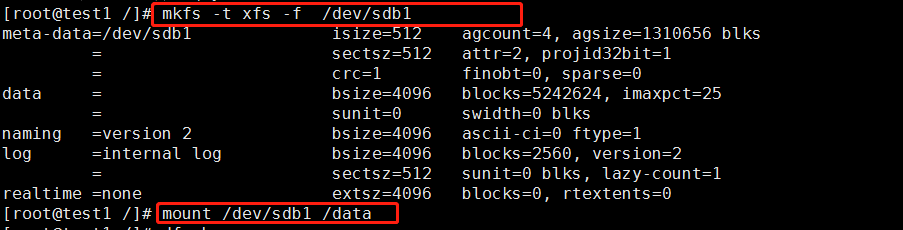
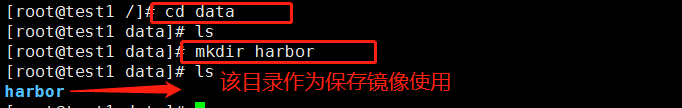
2、挂载一个磁盘,专门存储harbor镜像和文件
3、进入到/etc/docker/harbor/目录,修改如下配置文件
找到如下参数,并修为如下配置:
hostname = reg.yunwei.edu ui_url_protocol = https ssl_cert = /data/harbor/cert/harbor.crt ssl_cert_key = /data/harbor/cert/harbor.key secretkey_path = /data/harbor harbor_admin_password = admin ssl_cert = /data/harbor/cert/harbor.crt ssl_cert_key = /data/harbor/cert/harbor.key 以上为ca证书名称,必须与实际文件同名 secretkey_path = /data/harbor 为ca证书目录
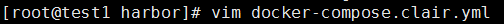
找到如下参数,并修为如下配置: /data/harbor/clair-db:/var/lib/postgresql/data:z
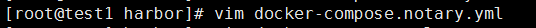
找到如下参数,并修为如下配置: /data/harbor/notary-db:/var/lib/mysql:z

找到如下参数,并修为如下配置: /data/harbor/:/var/log/docker/:z /data/harbor/registry:/storage:z /data/harbor/database:/var/lib/mysql:z /data/harbor/config/:/etc/adminserver/config/:z /data/harbor/secretkey:/etc/adminserver/key:z /data/harbor/:/data/:z /data/harbor/secretkey:/etc/ui/key:z /data/harbor/ca_download/:/etc/ui/ca/:z /data/harbor/psc/:/etc/ui/token/:z /data/harbor/job_logs:/var/log/jobs:z /data/harbor/secretkey:/etc/jobservice/key:z
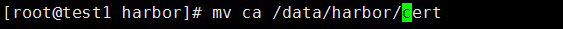
4、获取证书目录ca/,移动到/data/harbor/下并重命名为cert。
与harbor.cfg文件相互对应

5、执行脚本,安装harbor
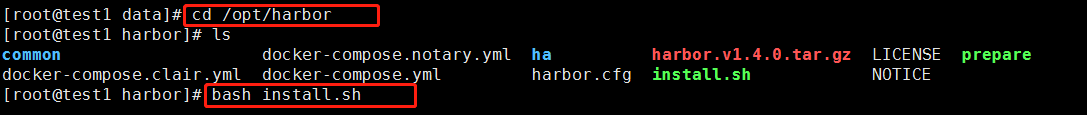
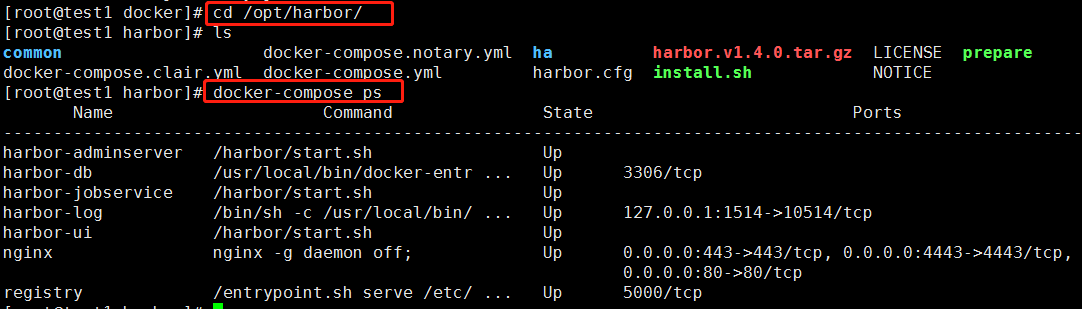
6、验证harbor是否部署成功:必须在/opt/harbor/目录下执行
docker-compose:批量管理docker的工具,执行的目录中必须要有docker-compose文件。
dockers-compose --help可以查看命令
注:docker-compose开启的docker只能用该命令停止或者删除,不能用docker rm
#docker-compose ps
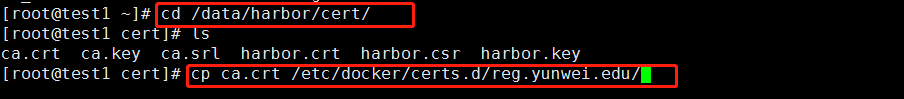
7、将证书的ca.crt文件拷贝到/etc/docker/certs.d/reg.yunwei.edu/下
注:此文件安装harbor过程有可能已经做过,查看目录,如做过,可省略
8、将证书文件发送给各个节点,保证各个节点都能访问到镜像库,并下载镜像

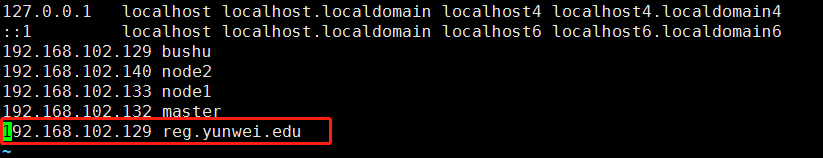
9、将部署镜像库的节点,进行域名解析,这里ansible节点与私有镜像库节点为同一台机器,故ip一样

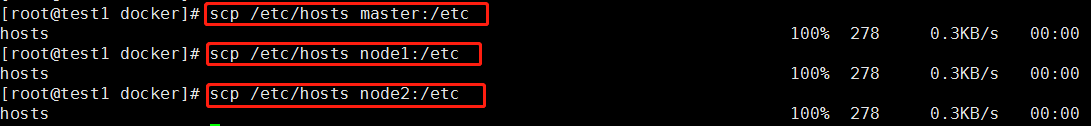
10、将/etc/hosts文件分发到各个节点
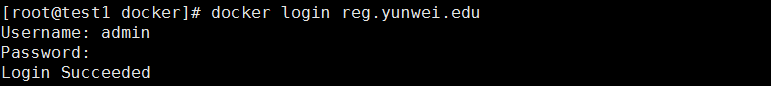
11、在部署节点进行登陆测试,成功即可。用户名和密码均为admin,密码在harbor.cfg文件中进行过修改
浏览器中直接输入ip即可访问
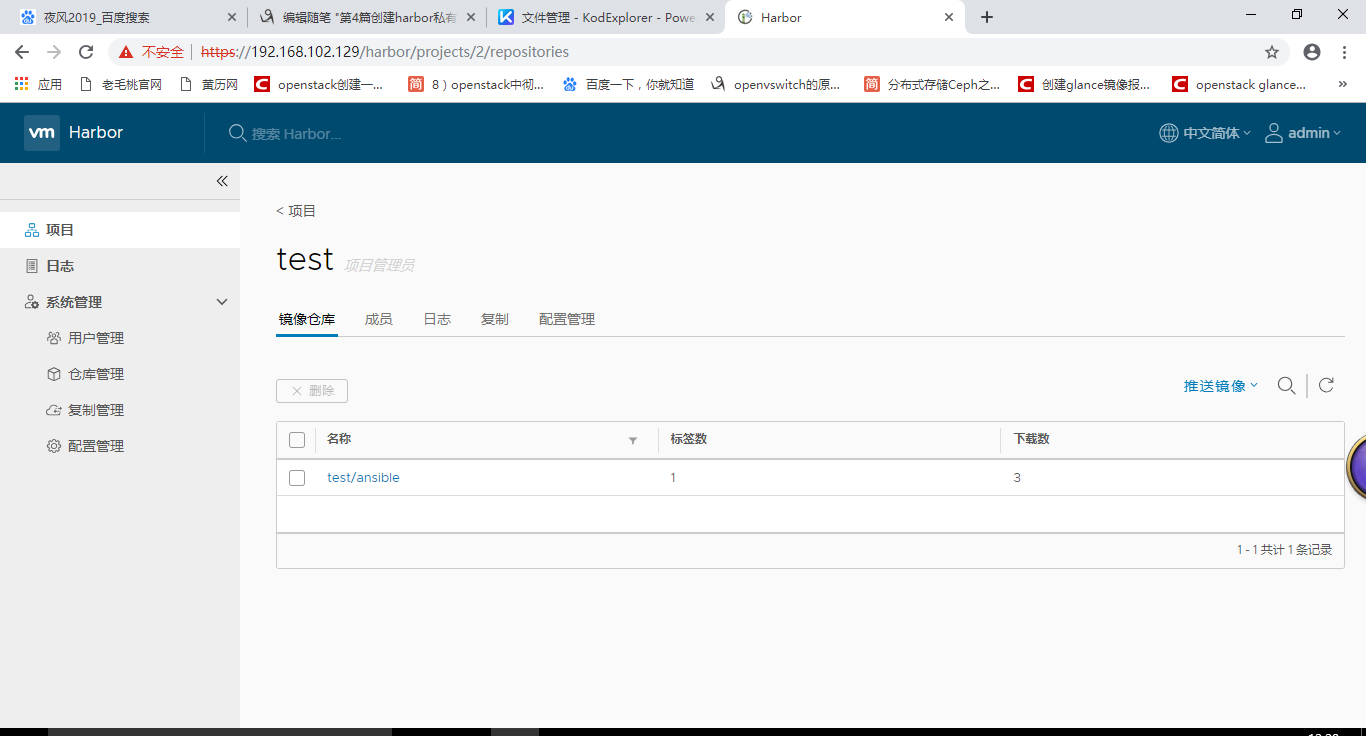
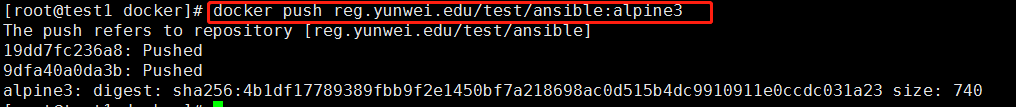
12、上传镜像测试

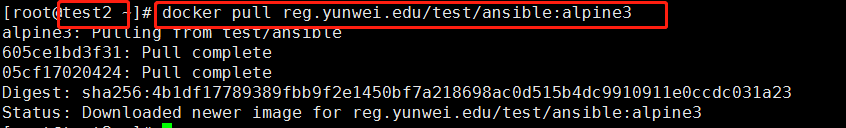
13、下载镜像测试(在其他节点)



 浙公网安备 33010602011771号
浙公网安备 33010602011771号