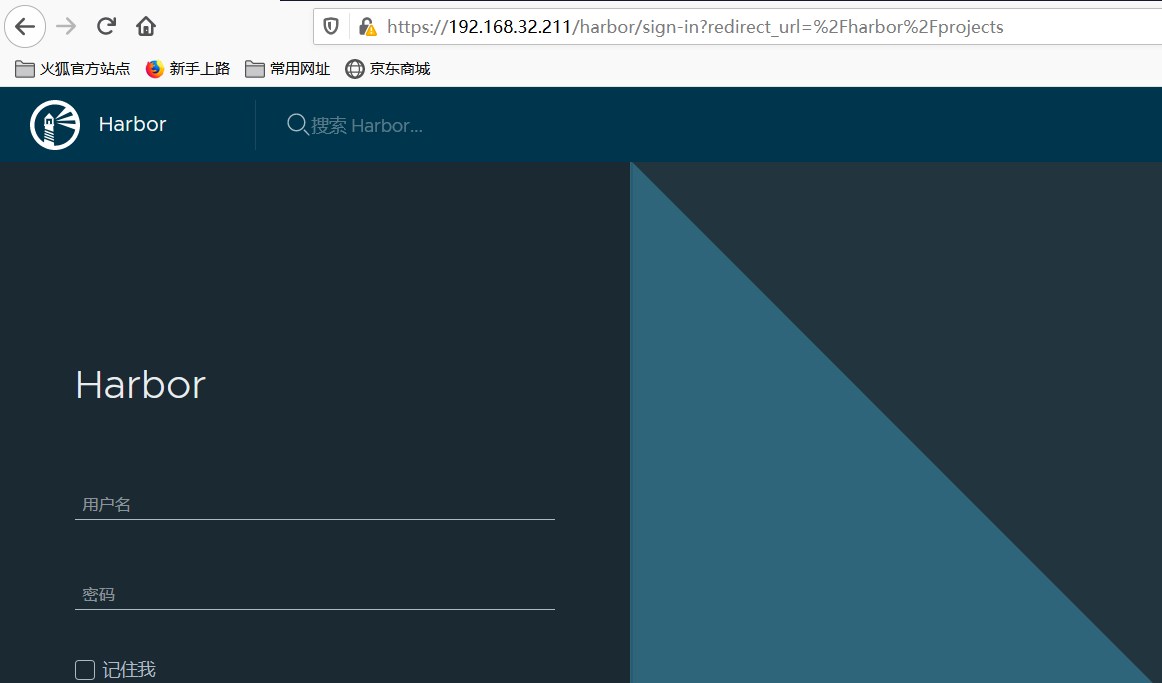
十三、搭建SSL的私有harbor仓库
System OS: CentOS Linux release 7.6.1810 (Core) docker version: Docker version 20.10.1 node1 192.168.32.211 docker+harbor node2 192.168.32.212 docker harbor软件版本: harbor-offline-installer-v2.1.2
1、安装docker
#下载docker-ce的yum源 wget -O /etc/yum.repos.d/docker-ce.repo https://mirrors.tuna.tsinghua.edu.cn/docker-ce/linux/centos/docker-ce.repo #把docker-ce源的地址修改为清华源的地址 sed -i 's#download.docker.com#mirrors.tuna.tsinghua.edu.cn/docker-ce#g' /etc/yum.repos.d/docker-ce.repo #更新docker-ce.repo yum makecache fast #安装docker-ce yum install -y docker-ce
方法一: https://github.com/docker/compose/releases 方法二: yum install -y docker-compose [root@node1 ~]# docker-compose -v docker-compose version 1.18.0, build 8dd22a9
#上传harbor-offline-installer-v2.1.2.tgz cd /app tar harbor-offline-installer-v2.1.2.tgz cd harbor cp harbor.yml.tmpl harbor.yml ########################################harbor.yml配置文件###################################### vim harbor.yml # Configuration file of Harbor # The IP address or hostname to access admin UI and registry service. # DO NOT use localhost or 127.0.0.1, because Harbor needs to be accessed by external clients. hostname: 192.168.32.211 # http related config http: # port for http, default is 80. If https enabled, this port will redirect to https port port: 80 # https related config #https: # https port for harbor, default is 443 # port: 443 # The path of cert and key files for nginx # certificate: /your/certificate/path # private_key: /your/private/key/path # # Uncomment following will enable tls communication between all harbor components # internal_tls: # # set enabled to true means internal tls is enabled # enabled: true # # put your cert and key files on dir # dir: /etc/harbor/tls/internal # Uncomment external_url if you want to enable external proxy # And when it enabled the hostname will no longer used # external_url: https://reg.mydomain.com:8433 # The initial password of Harbor admin # It only works in first time to install harbor # Remember Change the admin password from UI after launching Harbor. harbor_admin_password: 123456 ...... ####################################end################################################### ./prepare ./install.sh
[root@node1 harbor]# docker ps CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES 4289e237bf1e goharbor/harbor-jobservice:v2.1.2 "/harbor/entrypoint.…" 3 minutes ago Up 3 minutes (healthy) harbor-jobservice 775f3d56527f goharbor/nginx-photon:v2.1.2 "nginx -g 'daemon of…" 3 minutes ago Up 3 minutes (healthy) 0.0.0.0:80->8080/tcp nginx 3fa161a8dd62 goharbor/harbor-core:v2.1.2 "/harbor/entrypoint.…" 3 minutes ago Up 3 minutes (healthy) harbor-core 518b19e39709 goharbor/harbor-registryctl:v2.1.2 "/home/harbor/start.…" 3 minutes ago Up 3 minutes (healthy) registryctl decebb8bffd5 goharbor/harbor-db:v2.1.2 "/docker-entrypoint.…" 3 minutes ago Up 3 minutes (healthy) harbor-db 0393da381782 goharbor/redis-photon:v2.1.2 "redis-server /etc/r…" 3 minutes ago Up 3 minutes (healthy) redis 8aac2bb9c083 goharbor/registry-photon:v2.1.2 "/home/harbor/entryp…" 3 minutes ago Up 3 minutes (healthy) registry 48b17d48e306 goharbor/harbor-portal:v2.1.2 "nginx -g 'daemon of…" 3 minutes ago Up 3 minutes (healthy) harbor-portal 25e5d96537ca goharbor/harbor-log:v2.1.2 "/bin/sh -c /usr/loc…" 3 minutes ago Up 3 minutes (healthy) 127.0.0.1:1514->10514/tcp harbor-log
4.1搭建CA服务器
CA服务器上操作,本操作为node1
#安装openssl yum -y install openssl #openssl配置文件信息 ##################################################### vim /etc/pki/tls/openssl.cnf [CA_default] dir :ca的工作目录变量。被下方参数引用(注意:centos5上,此参数要改成绝对路径,不能用相对路径); certs :证书存放位置; crl_dir :吊销证书的存放位置; database :索引文件数据库。签署的所有证书索引文件。自动生成; new_certs_dir :刚签署的证书存放位置; certificate :ca自己的证书位置; serial :下一个证书的编号; crlnumber :已吊销证书的证书编号; crl :当前正在使用的证书吊销列表文件; private_key :ca自己的私钥,安全性很高(可以加密私钥位置文件,让别人拿到也看不了。但是每次使用都得 解密); ##################################end############################### #进入CA的工作目录 mkdir /harbor_CA cd /harbor_CA #创建自己的CA证书(不使用第三方权威机构的CA来认证,自己充当CA的角色) (umask 077; openssl genrsa -out ca.key 2048) 生成自签名证书(使用已有私钥cakey.pem自行签发根证书) openssl req -x509 -new -nodes -key ca.key -days 10000 -out ca.crt ###########################需要填写的信息############################# Country Name (2 letter code) [XX]:CN #国家代码 State or Province Name (full name) []:SC #所在省份 Locality Name (eg, city) [Default City]:CD #所在城市 Organization Name (eg, company) [Default Company Ltd]:test #机构名称 Organizational Unit Name (eg, section) []:test #部门名称 Common Name (eg, your name or your server's hostname) []:www.ywx.com #主机名称(重要) Email Address []:test@163.com #邮箱地址 #########################end############################################ cd /harbor_CA #创建索引文件 touch index.txt #证书编号位置 touch serial #自定义开始证书编号 echo 01 > serial #已吊销证书编号文件 touch crlnumber
本操作为node1
#创建证书目录并进入 mkdir /root/harbor_ssl cd /root/harbor_ssl #生成harbor私钥 (umask 077; openssl genrsa -out harbor.key 1024) #根据私钥,创建证书申请文件 openssl req -new -nodes -key /root/harbor_ssl/harbor.key -out /root/harbor_ssl/harbor.csr -days 365 ###########################填写信息############################ You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:CN #国家代码 State or Province Name (full name) []:SC #所在省份 Locality Name (eg, city) [Default City]:SC #所在城市 Organization Name (eg, company) [Default Company Ltd]:TEST #机构名称 Organizational Unit Name (eg, section) []:TEST #部门名称 Common Name (eg, your name or your server's hostname) []:www.ywx.com #主机名称(重要) Email Address []:test@163.com #邮箱地址 Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: #空 An optional company name []: #空 [root@node1 harbor_ssl]# #############################end###################################
4.3 将harbor证书申请文件复制到CA服务器上,有CA进行数字签名
本操作在node1
1) 如果您使用的是像reg.yourdomain.com这样的FQDN 来连接您的注册表主机,请运行以下命令以生成注册表主机的证书:
openssl x509 -req -days 365 -in yourdomain.com.csr -CA /harbor_CA/ca.crt -CAkey /harbor_CA/ca.key -CAcreateserial -out yourdomain.com.crt
2) 如果你使用IP,比如192.168.32.211来连接你的注册表主机,你可以运行下面的命令:
echo subjectAltName = IP:192.168.32.211 > extfile.cnf openssl x509 -req -in /root/harbor_ssl/harbor.csr -CA /harbor_CA/ca.crt -CAkey /harbor_CA/ca.key -CAcreateserial -extfile /root/harbor_ssl/extfile.cnf -days 365 -out /root/harbor_ssl/harbor.crt
4.4修改harbar的配置文件并重新安装部署
本操作在node1
#配置文件修改 cd /app/harbor/ vim harbor.yaml ##############################配置文件修改################## # Configuration file of Harbor # The IP address or hostname to access admin UI and registry service. # DO NOT use localhost or 127.0.0.1, because Harbor needs to be accessed by external clients. hostname: 192.168.32.211 # http related config http: # port for http, default is 80. If https enabled, this port will redirect to https port port: 80 # https related config #https: # https port for harbor, default is 443 port: 443 # The path of cert and key files for nginx certificate: /root/harbor_ssl/harbor.crt private_key: /root/harbor_ssl/harbor.key # # Uncomment following will enable tls communication between all harbor components # internal_tls: # # set enabled to true means internal tls is enabled # enabled: true # # put your cert and key files on dir # dir: /etc/harbor/tls/internal # Uncomment external_url if you want to enable external proxy # And when it enabled the hostname will no longer used # external_url: https://reg.mydomain.com:8433 # The initial password of Harbor admin # It only works in first time to install harbor # Remember Change the admin password from UI after launching Harbor. harbor_admin_password: 123456 。。。。 ###########################################end################################### #重新部署https的harbor ./prepare ./install.sh #重启harbor的容器 docker-compose down docker-compose up -d
6、把harbor.crt证书拷贝到docker主机
在具有Docker守护进程的机器上,确保选项“-insecure-registry”不存在,并且您必须将上述步骤中生成的harbor.crt复制到/etc/docker/certs.d/reg.yourdomain.com(或您的注册表主机IP),如果该目录不存在,请创建它。如果您将nginx端口443映射到另一个端口,则应改为创建/etc/docker/certs.d/reg.yourdomain.com:port(或您的注册表主机IP:端口)目录。然后运行任何docker命令来验证设置。
#创建证书目录 [root@node2 docker]# mkdir -p /etc/docker/certs.d/192.168.32.211 #从192.168.32.211上拉取harbor.crt证书 [root@node2 docker]# cd /etc/docker/certs.d/192.168.32.211 [root@node2 192.168.32.211]# scp -r 192.168.32.211:/root/harbor_ssl/harbor.crt ./ [root@node2 192.168.32.211]# ls harbor.crt #重启docker [root@node2 192.168.32.211]# systemctl restart docker
本操作在node2
上传镜像文件
[root@node2 ~]# docker login https://192.168.32.211 Authenticating with existing credentials... WARNING! Your password will be stored unencrypted in /root/.docker/config.json. Configure a credential helper to remove this warning. See https://docs.docker.com/engine/reference/commandline/login/#credentials-store Login Succeeded [root@node2 ~]# docker tag busybox:latest 192.168.32.211/library/busybox:latest [root@node2 ~]# docker push 192.168.32.211/library/busybox:latest The push refers to repository [192.168.32.211/library/busybox] de168d3b8ec4: Pushed latest: digest: sha256:31a54a0cf86d7354788a8265f60ae6acb4b348a67efbcf7c1007dd3cf7af05ab size: 527
下载镜像文件
[root@node2 ~]# docker rmi 192.168.32.211/busybox Untagged: 192.168.32.211/busybox:latest [root@node2 ~]# docker rmi 192.168.32.211/library/busybox Untagged: 192.168.32.211/library/busybox:latest Untagged: 192.168.32.211/library/busybox@sha256:31a54a0cf86d7354788a8265f60ae6acb4b348a67efbcf7c1007dd3cf7af05ab [root@node2 ~]# docker images REPOSITORY TAG IMAGE ID CREATED SIZE 192.168.32.211/nginx latest ae2feff98a0c 9 days ago 133MB nginx latest ae2feff98a0c 9 days ago 133MB busybox latest 219ee5171f80 3 weeks ago 1.23MB 下载镜像文件 [root@node2 ~]# docker pull 192.168.32.211/library/busybox:latest latest: Pulling from library/busybox Digest: sha256:31a54a0cf86d7354788a8265f60ae6acb4b348a67efbcf7c1007dd3cf7af05ab Status: Downloaded newer image for 192.168.32.211/library/busybox:latest 192.168.32.211/library/busybox:latest [root@node2 ~]# docker images REPOSITORY TAG IMAGE ID CREATED SIZE 192.168.32.211/nginx latest ae2feff98a0c 9 days ago 133MB nginx latest ae2feff98a0c 9 days ago 133MB 192.168.32.211/library/busybox latest 219ee5171f80 3 weeks ago 1.23MB busybox latest 219ee5171f80 3 weeks ago 1.23MB
I have a dream so I study hard!!!


 浙公网安备 33010602011771号
浙公网安备 33010602011771号