openssl搭建CA证书服务器
安全机制概述
信息安全防护的目标
- 保密性 Confidentiality
- 完整性 Integrity
- 可用性 Usability
- 可控制性Controlability
- 不可否认性 Non-repudiation
安全防护环节
- 物理安全:各种设备/主机、机房环境
- 系统安全:主机或设备的操作系统
- 应用安全:各种网络服务、应用程序
- 网络安全:对网络访问的控制、防火墙规则
- 数据安全:信息的备份与恢复、加密解密
- 管理安全:各种保障性的规范、流程、方法安全
安全攻击: STRIDE
- Spoofing 假冒
- Tampering 篡改
- Repudiation 否认
- Information Disclosure 信息泄漏
- Denial of Service 拒绝服务
- Elevation of Privilege 提升权限
5安全设计基本原则
- 使用成熟的安全系统
- 以小人之心度输入数据
- 外部系统是不安全的
- 最小授权
- 减少外部接口
- 缺省使用安全模式
- 安全不是似是而非
- 从STRIDE思考
- 在入口处检查
- 从管理上保护好你的系统
安全算法
常用安全技术
- 认证
- 授权
- 审计
- 安全通信
密码算法和协议:
- 对称加密
- 公钥加密
- 单向加密
- 认证协议
Linux系统:OpenSSL, gpg(pgp协议的实现)
加密需要
不加密流量的易受攻击性
- 密码/数据嗅探
- 数据操作
- 验证操作
- 相当于邮寄明信片
不安全的传统协议
- telnet、FTP、POP3等等;不安全密码
- http、smtp、NFS等等;不安全信息
- Ldap、NIS、rsh等等;不安全验证
对称加密算法
对称加密:加密和解密使用同一个密钥
DES:Data Encryption Standard,56bits
3DES:
AES:Advanced (128, 192, 256bits)
Blowfish,Twofish
IDEA,RC6,CAST5
特性:
- 加密、解密使用同一个密钥,效率高
- 将原始数据分割成固定大小的块,逐个进行加密
缺陷:
- 密钥过多
- 密钥分发
- 数据来源无法确认10
非对称加密算法
公钥加密:密钥是成对出现
公钥:公开给所有人;public key
私钥:自己留存,必须保证其私密性;secret key
特点:
- 用公钥加密数据,只能使用与之配对的私钥解密;反之亦然
功能:
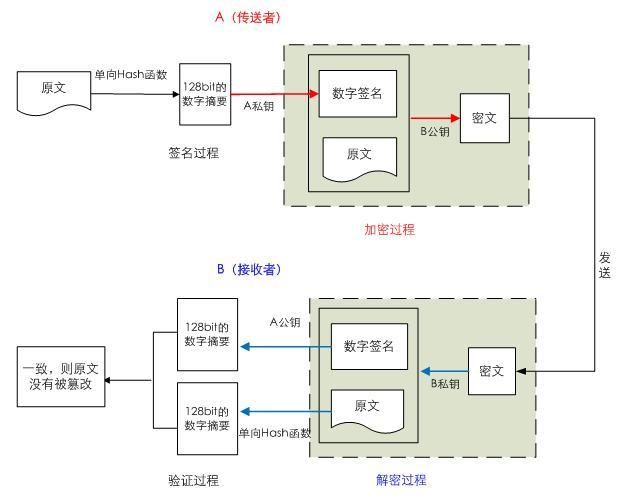
- 数字签名:主要在于让接收方确认发送方身份
- 对称密钥交换:发送方用对方的公钥加密一个对称密钥后发送给对方
- 数据加密:适合加密较小数据
缺点:
- 密钥长,加密解密效率低下
算法:
- RSA(加密,数字签名),DSA(数字签名),ELGamal
非对称加密
基于一对公钥/密钥对
用密钥对中的一个加密,另一个解密
实现加密:
接收者
- 生成公钥/密钥对:P和S
- 公开公钥P,保密密钥S
发送者
- 使用接收者的公钥来加密消息M
- 将P(M)发送给接收者
接收者
- 使用密钥S来解密:M=S(P(M))
实现数字签名:
发送者
- 生成公钥/密钥对:P和S
- 公开公钥P,保密密钥S
- 使用密钥S来加密消息M
- 发送给接收者S(M)
接收者
- 使用发送者的公钥来解密M=P(S(M))
- 结合签名和加密
- 分离签名
CA和证书
PKI: Public Key Infrastructure
- 签证机构:CA(Certificate Authority)
- 注册机构:RA
- 证书吊销列表:CRL
- 证书存取库
X.509:定义了证书的结构以及认证协议标准
- 版本号
- 序列号
- 签名算法
- 颁发者
- 有效期限
- 主体名称
- 主体公钥
- CRL分发点
- 扩展信息
- 发行者签名
证书获取
证书类型:
- 证书授权机构的证书
- 服务器
- 用户证书
获取证书两种方法:
- 使用证书授权机构
- 生成签名请求(csr)
- 将csr发送给CA
- 从CA处接收签名
自签名的证书
- 自已签发自己的公钥
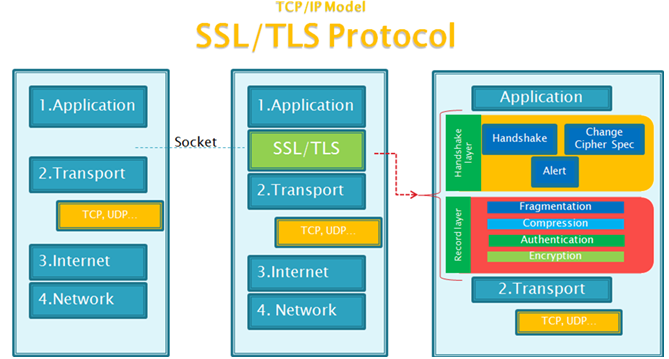
安全协议
- SSL: Secure Socket Layer
- TLS: Transport Layer Security
-
- 1995:SSL 2.0 Netscape
- 1996: SSL 3.0
- 1999: TLS 1.0
- 2006: TLS 1.1 IETF(Internet工程任务组) RFC 4346
- 2008:TLS 1.2 当前使用
- 2015: TLS 1.3
功能:
- 机密性,认证,完整性,重放保护
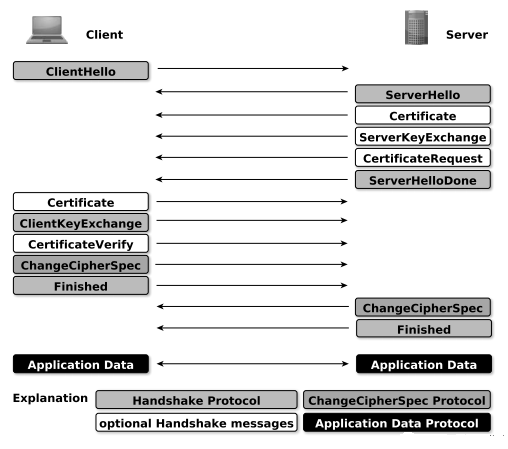
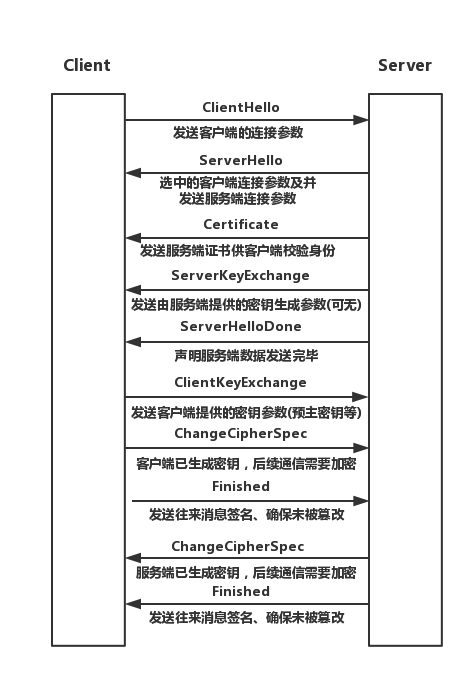
两阶段协议,分为握手阶段和应用阶段
- 握手阶段(协商阶段):客户端和服务器端认证对方身份(依赖于PKI体系,利用数字证书进行身份认证),并协商通信中使用的安全参数、密码套件以及主密钥。后续通信使用的所有密钥都是通过MasterSecret生成。
- 应用阶段:在握手阶段完成后进入,在应用阶段通信双方使用握手阶段协商好的密钥进行安全通信
SSL/TLS
- Handshake协议:包括协商安全参数和密码套件、服务器身份认证(客户端身份认证可选)、密钥交换
- ChangeCipherSpec 协议:一条消息表明握手协议已经完成
- Alert 协议:对握手协议中一些异常的错误提醒,分为fatal和warning两个级别,fatal类型错误会直接中断SSL链接,而warning级别的错误SSL链接仍可继续,只是会给出错误警告
- Record 协议:包括对消息的分段、压缩、消息认证和完整性保护、加密等
- HTTPS 协议:就是“HTTP 协议”和“SSL/TLS 协议”的组合。HTTP over SSL”或“HTTP over TLS”,对http协议的文本数据进行加密处理后,成为二进制形式传输
OpenSSL
OpenSSL:开源项目
三个组件:
- openssl: 多用途的命令行工具,包openssl
- libcrypto: 加密算法库,包openssl-libs
- libssl:加密模块应用库,实现了ssl及tls,包nss
SSH
ssh: secure shell, protocol, 22/tcp, 安全的远程登录
具体的软件实现:
- OpenSSH: ssh协议的开源实现,CentOS默认安装
- dropbear:另一个开源实现
SSH协议版本
- v1: 基于CRC-32做MAC,不安全;man-in-middle
- v2:双方主机协议选择安全的MAC方式
- 基于DH算法做密钥交换,基于RSA或DSA实现身份认证
两种方式的用户登录认证:
- 基于password
- 基于key
openssl命令:
两种运行模式:交互模式和批处理模式
openssl version:程序版本号
标准命令、消息摘要命令、加密命令
标准命令:enc, ca, req, ...
对称加密:
工具:openssl enc, gpg
算法:3des, aes, blowfish, twofish
enc命令:
帮助: man enc
加密: openssl enc -e -des3 -a -salt -in testfile -out test.cipher
解密: openssl enc -d -des3 -a -salt –in test.cipher -out testfile
单向加密
工具:md5sum, sha1sum, sha224sum,sha256sum…openssl dgst
dgst命令:
帮助: man dgst
openssl dgst -md5 [-hex默认] /PATH/SOMEFILE openssl dgst -md5 testfile md5sum /PATH/TO/SOMEFILE
MAC: Message Authentication Code,单向加密的一种延伸应用,用于实现网络通信中保证所传输数据的完整性机制CBC-MAC
HMAC:使用md5或sha1算法31
生成用户密码
passwd命令:
帮助: man sslpasswd
openssl passwd -1 -salt SALT(最多8位) openssl passwd -1 –salt centos
生成随机数
帮助: man sslrand
openssl rand -base64|-hex NUM
NUM: 表示字节数;-hex时,每个字符为十六进制,相当于4位二进制,出现的字符数为NUM*232
生成密钥对
公钥加密
算法:RSA, ELGamal
工具:gpg, openssl rsautl(man rsautl)
数字签名:
算法:RSA, DSA, ELGamal
密钥交换:
算法:dh
DSA: Digital Signature Algorithm
DSS:Digital Signature Standard
RSA:33
生成私钥
openssl genrsa -out /PATH/TO/PRIVATEKEY.FILE NUM_BITS (umask 077; openssl genrsa –out test.key –des 2048) openssl rsa -in test.key –out test2.key 将加密key解密
从私钥中提取出公钥
openssl rsa -in PRIVATEKEYFILE –pubout –out PUBLICKEYFILE Openssl rsa –in test.key –pubout –out test.key.pub
OpenSSL证书服务器搭建
PKI:Public Key Infrastructure
- CA
- RA
- CRL
- 证书存取库
证书申请及签署步骤:
- 生成申请请求
- RA核验
- CA签署
- 获取证书35
创建CA
openssl的配置文件: /etc/pki/tls/openssl.cnf

HOME = . oid_section = new_oids openssl_conf = default_modules [ default_modules ] ssl_conf = ssl_module [ ssl_module ] system_default = crypto_policy [ crypto_policy ] .include /etc/crypto-policies/back-ends/opensslcnf.config [ new_oids ] tsa_policy1 = 1.2.3.4.1 tsa_policy2 = 1.2.3.4.5.6 tsa_policy3 = 1.2.3.4.5.7 [ ca ] # 语句块 default_ca = CA_default # The default ca section [ CA_default ] # 语句块 dir = /etc/pki/CA # ca 相关的具体路径 证书 certs = $dir/certs # 存放证书的目录 crl_dir = $dir/crl # 证书兑换列表 database = $dir/index.txt # 数据库 存放所有证书的信息 自动更新 # several certs with same subject. new_certs_dir = $dir/newcerts #新证书存放的路径 certificate = $dir/cacert.pem # The CA certificate serial = $dir/serial # 编号 存放下一个要颁发的编号 crlnumber = $dir/crlnumber # 吊销列表的标号 # must be commented out to leave a V1 CRL crl = $dir/crl.pem # 证书吊销列表文件名 private_key = $dir/private/cakey.pem# 私钥文件 x509_extensions = usr_cert # The extensions to add to the cert name_opt = ca_default # Subject Name options cert_opt = ca_default # Certificate field options default_days = 365 # 默认有效期 default_crl_days= 30 # 30天发布一次私钥信息 default_md = sha256 # 默认加密算法 preserve = no # policy = policy_match # 策略匹配 [ policy_match ] countryName = match # 必须有的信息 国家 stateOrProvinceName = match # 省市 organizationName = match # 公司 organizationalUnitName = optional commonName = supplied # 通用名 域名 emailAddress = optional # [ policy_anything ] # 策略可以不一样 countryName = optional stateOrProvinceName = optional localityName = optional organizationName = optional organizationalUnitName = optional commonName = supplied emailAddress = optional [ req ] default_bits = 2048 default_md = sha256 default_keyfile = privkey.pem distinguished_name = req_distinguished_name attributes = req_attributes x509_extensions = v3_ca # The extensions to add to the self signed cert string_mask = utf8only [ req_distinguished_name ] countryName = Country Name (2 letter code) countryName_default = XX countryName_min = 2 countryName_max = 2 stateOrProvinceName = State or Province Name (full name) localityName = Locality Name (eg, city) localityName_default = Default City 0.organizationName = Organization Name (eg, company) 0.organizationName_default = Default Company Ltd organizationalUnitName = Organizational Unit Name (eg, section) commonName = Common Name (eg, your name or your server\'s hostname) commonName_max = 64 emailAddress = Email Address emailAddress_max = 64 [ req_attributes ] challengePassword = A challenge password challengePassword_min = 4 challengePassword_max = 20 unstructuredName = An optional company name [ usr_cert ] basicConstraints=CA:FALSE nsComment = "OpenSSL Generated Certificate" subjectKeyIdentifier=hash authorityKeyIdentifier=keyid,issuer [ v3_req ] basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment [ v3_ca ] subjectKeyIdentifier=hash authorityKeyIdentifier=keyid:always,issuer basicConstraints = critical,CA:true [ crl_ext ] authorityKeyIdentifier=keyid:always [ proxy_cert_ext ] basicConstraints=CA:FALSE nsComment = "OpenSSL Generated Certificate" subjectKeyIdentifier=hash authorityKeyIdentifier=keyid,issuer proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo [ tsa ] default_tsa = tsa_config1 # the default TSA section [ tsa_config1 ] dir = /etc/pki/CA # TSA root directory serial = $dir/tsaserial # The current serial number (mandatory) crypto_device = builtin # OpenSSL engine to use for signing signer_cert = $dir/tsacert.pem # The TSA signing certificate # (optional) certs = $dir/cacert.pem # Certificate chain to include in reply # (optional) signer_key = $dir/private/tsakey.pem # The TSA private key (optional) signer_digest = sha256 # Signing digest to use. (Optional) default_policy = tsa_policy1 # Policy if request did not specify it # (optional) other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional) digests = sha1, sha256, sha384, sha512 # Acceptable message digests (mandatory) accuracy = secs:1, millisecs:500, microsecs:100 # (optional) clock_precision_digits = 0 # number of digits after dot. (optional) ordering = yes # Is ordering defined for timestamps? # (optional, default: no) tsa_name = yes # Must the TSA name be included in the reply? # (optional, default: no) ess_cert_id_chain = no # Must the ESS cert id chain be included? # (optional, default: no) ess_cert_id_alg = sha1 # algorithm to compute certificate # identifier (optional, default: sha1)
创建所需要的文件
mkdir /etc/pki/CA/
mkdir /etc/pki/CA/{certs,crl,newcerts,private}
[root@djcy-200 CA]# tree
.
├── certs
├── crl
├── newcerts
└── private
mkdir /etc/pki/CA/crlnumber
touch /etc/pki/CA/index.txt 生成证书索引数据库文件
echo 01 > /etc/pki/CA/serial 指定第一个颁发证书的序列号
CA生成私钥
# 输入密码 每次签发证书都需认证
[root@djcy-200 CA]# (umask 066; openssl genrsa -out private/cakey.pem -des3 2048)
Generating RSA private key, 2048 bit long modulus (2 primes)
...................................+++++
..................................+++++
e is 65537 (0x010001)
Enter pass phrase for private/cakey.pem:
Verifying - Enter pass phrase for private/cakey.pem:
[root@djcy-200 CA]# tree
.
├── certs
├── crl
├── newcerts
└── private
└── cakey.pem
CA自签证书
参数说明:
-new: 生成新证书签署请求
-x509: 专用于CA生成自签证书
-key: 生成请求时用到的私钥文件
-days n:证书的有效期限
-out /PATH/TO/SOMECERTFILE: 证书的保存路径
[root@djcy-200 CA]# openssl req -new -x509 -key private/cakey.pem -days 18250 -out /etc/pki/CA/cacert.pem
Enter pass phrase for private/cakey.pem:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:BeiJing
Locality Name (eg, city) [Default City]:BeiJing
Organization Name (eg, company) [Default Company Ltd]:devops
Organizational Unit Name (eg, section) []:ops
Common Name (eg, your name or your server's hostname) []:ca.devops.com
Email Address []:admin@devops.com
[root@djcy-200 CA]# tree
.
├── cacert.pem
├── certs
├── crl
├── newcerts
└── private
└── cakey.pem
4 directories, 2 files查看
查看证书信息
[root@djcy-200 CA]# openssl x509 -in cacert.pem -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
11:10:a5:ca:51:77:cb:43:06:61:42:27:9d:ec:5e:35:d7:9b:61:17
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = BeiJing, L = BeiJing, O = devops, OU = ops, CN = ca.devops.com, emailAddress = admin@devops.com
Validity
Not Before: Aug 2 13:34:53 2020 GMT
Not After : Jul 21 13:34:53 2070 GMT
Subject: C = CN, ST = BeiJing, L = BeiJing, O = devops, OU = ops, CN = ca.devops.com, emailAddress = admin@devops.com
'''''''' 省略
# 只查看某些内容
[root@djcy-200 CA]# openssl x509 -in cacert.pem -noout -dates
notBefore=Aug 2 13:34:53 2020 GMT
notAfter=Jul 21 13:34:53 2070 GMT
客户端请求颁发证书
生成私钥
[root@djcy-62 ~]# mkdir ca [root@djcy-62 ~]# cd ca/ [root@djcy-62 ca]# (umask 066;openssl genrsa -out app.key 1024) Generating RSA private key, 1024 bit long modulus (2 primes) ............+++++ ......................+++++ e is 65537 (0x010001) [root@djcy-62 ca]# ll total 4 -rw------- 1 root root 891 Aug 2 21:43 app.key
使用私钥生成请求
[root@djcy-62 ca]# openssl req -new -key app.key -out app.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:CN # 必须跟CA服务器一致 State or Province Name (full name) []:BeiJing # 必须跟CA服务器一致 Locality Name (eg, city) [Default City]:ChaoYang Organization Name (eg, company) [Default Company Ltd]:devops # 必须跟CA服务器一致 Organizational Unit Name (eg, section) []:webdev Common Name (eg, your name or your server's hostname) []:www.devops.com # 颁发的域名 Email Address []:dev@devops.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []: [root@djcy-62 ca]# ll total 8 -rw-r--r-- 1 root root 700 Aug 2 21:47 app.csr -rw------- 1 root root 891 Aug 2 21:43 app.key
发送请求秘钥到CA服务器
[root@djcy-62 ca]# scp app.csr bjcy-200.host.io:/etc/pki/CA/
查看服务器颁发的密码
[root@djcy-62 ca]# openssl x509 -in app.crt -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 1 (0x1)
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = BeiJing, L = BeiJing, O = devops, OU = ops, CN = ca.devops.com, emailAddress = admin@devops.com
Validity
Not Before: Aug 2 14:01:05 2020 GMT
Not After : Jul 31 14:01:05 2030 GMT
Subject: C = CN, ST = BeiJing, O = devops, OU = webdev, CN = www.devops.com, emailAddress = dev@devops.com
Subject Public Key Info:
''''''' 省略'
CA授权客户端
[root@djcy-200 CA]# touch index.txt # 数据库文件存放着所有的申请授权信息
[root@djcy-200 CA]# echo 01 > /etc/pki/CA/serial # 开始申请的编号 每次都会增加
[root@djcy-200 CA]# openssl ca -in app.csr -out certs/app.crt -days 3650 # 开始授权
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/cakey.pem:
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Aug 2 14:01:05 2020 GMT
Not After : Jul 31 14:01:05 2030 GMT
Subject:
countryName = CN
stateOrProvinceName = BeiJing
organizationName = devops
organizationalUnitName = webdev
commonName = www.devops.com
emailAddress = dev@devops.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
BF:F7:D0:7A:0B:B8:11:6E:27:64:69:C2:7D:3D:38:62:69:E7:4A:10
X509v3 Authority Key Identifier:
keyid:31:BC:8B:B0:A6:F8:FF:B7:6E:F9:B2:E5:7C:80:B8:47:6C:AA:AB:1D
Certificate is to be certified until Jul 31 14:01:05 2030 GMT (3650 days)
Sign the certificate? [y/n]:y # 是否授权
1 out of 1 certificate requests certified, commit? [y/n]y # 确认
Write out database with 1 new entries
Data Base Updated
[root@djcy-200 CA]# tree
.
├── app.csr
├── cacert.pem
├── certs
│ └── app.crt # 生产的私钥文件
├── crl
├── index.txt
├── index.txt.attr
├── index.txt.old
├── newcerts
│ └── 01.pem # 和 certs下的 app.crt 是同一个文件
├── private
│ └── cakey.pem
├── serial
└── serial.old
4 directories, 10 files
[root@djcy-200 CA]# cat index.txt # 数据库文件
V 300731140105Z 01 unknown /C=CN/ST=BeiJing/O=devops/OU=webdev/CN=www.devops.com/emailAddress=dev@devops.com
[root@djcy-200 CA]# cat serial # 下次申请的编号
02
CA吊销证书
[root@djcy-200 CA]# echo 01 > /etc/pki/CA/crlnumber
[root@djcy-200 CA]# openssl ca -revoke newcerts/01.pem 指定吊销证书
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/cakey.pem:
Revoking Certificate 01.
Data Base Updated
[root@djcy-200 CA]# tree
.
├── app.csr
├── cacert.pem
├── certs
│ └── app.crt
├── crl
├── crlnumber
├── index.txt
├── index.txt.attr
├── index.txt.attr.old
├── index.txt.old
├── newcerts
│ └── 01.pem
├── private
│ └── cakey.pem
├── serial
└── serial.old
4 directories, 12 files
[root@djcy-200 CA]# openssl ca -gencrl -out crl.pem # 生成证书吊销列表
Using configuration from /etc/pki/tls/openssl.cnf
Enter pass phrase for /etc/pki/CA/private/cakey.pem:
[root@djcy-200 CA]# tree
.
├── app.csr
├── cacert.pem
├── certs
│ └── app.crt
├── crl
├── crlnumber
├── crlnumber.old
├── crl.pem
├── index.txt
├── index.txt.attr
├── index.txt.attr.old
├── index.txt.old
├── newcerts
│ └── 01.pem
├── private
│ └── cakey.pem
├── serial
└── serial.old
4 directories, 14 files
[root@djcy-200 CA]# # 查看吊销列表文件
[root@djcy-200 CA]# openssl crl -in crl
crl/ crlnumber crlnumber.old crl.pem
[root@djcy-200 CA]# openssl crl -in crl.pem -noout -text
Certificate Revocation List (CRL):
Version 2 (0x1)
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = BeiJing, L = BeiJing, O = devops, OU = ops, CN = ca.devops.com, emailAddress = admin@devops.com
Last Update: Aug 2 14:21:56 2020 GMT
Next Update: Sep 1 14:21:56 2020 GMT
CRL extensions:
X509v3 CRL Number:
1
Revoked Certificates:
Serial Number: 01
Revocation Date: Aug 2 14:20:37 2020 GMT
Signature Algorithm: sha256WithRSAEncryption
29:af:64:35:f5:aa:48:dd:7b:9d:0e:2c:a0:73:95:a1:e3:9a:
fc:16:a9:e0:51:7d:a8:ee:f1:c4:f1:83:f9:b3:88:f2:f5:12:
06:27:f7:f0:92:19:91:7b:f6:bc:30:ed:c6:34:ed:26:2d:ae:
a7:2b:a2:7f:c2:60:9b:e1:24:2d:23:34:7b:7c:5e:ee:66:07:
da:2f:c5:8e:35:e8:65:aa:89:da:d7:1f:df:53:9b:c6:4a:78:
a8:09:fe:f3:0d:f4:0d:d6:65:48:0b:3d:75:73:19:26:db:ba:
d0:0d:74:0c:c2:89:30:e5:33:f4:db:fd:73:e8:1e:07:30:1c:
05:03:47:df:b3:82:26:e7:73:64:14:07:b9:f3:70:eb:8d:c0:
fb:74:07:d8:22:ad:ce:3c:2e:ad:4a:00:cb:6c:9e:60:6c:dd:
8c:14:ea:95:69:4a:be:ab:57:25:2d:ed:54:5a:45:04:13:4c:
3a:90:23:96:d8:1b:01:c3:c6:a3:55:cf:8e:8b:c7:85:08:9b:
44:ab:e8:eb:0f:c5:7c:8d:05:ef:d8:db:45:2c:36:32:f9:0c:
56:db:6b:aa:72:1d:68:a8:4c:3f:7a:58:fc:26:cf:0c:53:d1:
d2:57:33:4a:22:44:89:49:74:7a:1b:4f:91:0d:0f:59:5d:b0:
83:28:66:02
作者:闫世成
出处:http://cnblogs.com/yanshicheng
本文版权归作者和博客园共有,欢迎转载,但未经作者同意必须保留此段声明,且在文章页面明显位置给出原文连接。如有问题或建议,请联系上述邮箱,非常感谢。


