Linux shell command chmod All In One
Linux shell command chmod All In One
chmod 755 / chmod +x
chmod 755 === chmod +x
# a
# +x === 755
$ chmod a+x
chmod 777 vs chmod 755
# 读、写、执行 => 二进制表示 => 十进制表示
# rwx => 111 => 7
# r-x => 101 => 5
# r-x => 101 => 5
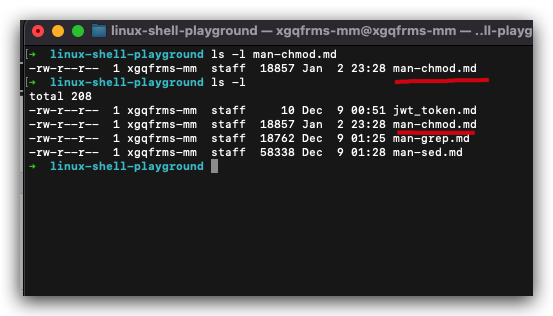
$ ls -al
# 755
-rwxr-xr-x
# 777
-rwxrwxrwx
``sh
$ touch test.sh
$ ls -l test.sh
```sh
$ chmod 755
# 等价于
$ chmod u=rwx,go=rx
$ chmod 777
# 等价于
$ chmod ugo=rwx
$ chmod u=rwx,g=rwx,o=rwx
$ chmod +x
# 等价于
$ chmod ugo+x
# $ chmod ugo=rwx ???
chmod
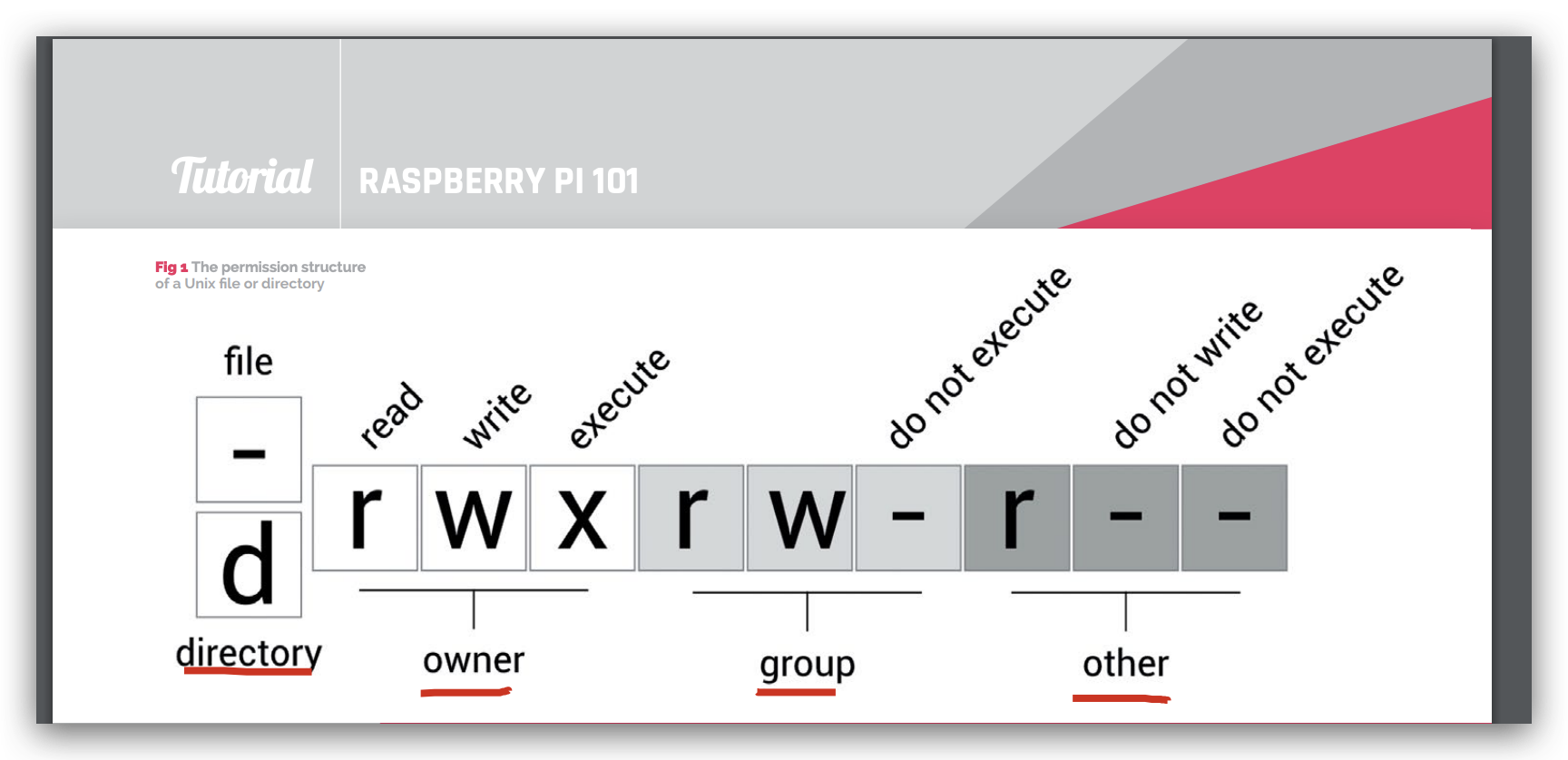
前 10 位符号分组:[-] [---] [---] [---]
- (占1 位符号) 文件类型:
文件/文件夹 - (每组占3 位符号)
r、w、x:读、写、执行/4、 2、 1 - 每 3 位符号为一组,共分成 3 组:
owner、group、other
N Description ls binary
0 No permissions at all --- 000
1 Only execute --x 001
2 Only write -w- 010
3 Write and execute -wx 011
4 Only read r-- 100
5 Read and execute r-x 101
6 Read and write rw- 110
7 Read, write, and execute rwx 111
范例1:-rwx-wx-wx => 文件755
范例2:-rw-r--r-- => 文件544
$ ls -l filename.txt
-rw-r--r-- 12 linuxize users 12.0K Apr 8 20:51 filename.txt
[-][---][---][---] [-] [------] [---]
| | | | | | |
| | | | | | +-------------> 7. Group
| | | | | +--------------------> 6. Owner
| | | | +--------------------------> 5. Alternate Access Method
| | | +--------------------------------> 4. Others Permissions (3 位符号,other 权限)
| | +-------------------------------------> 3. Group Permissions (3 位符号,group 权限)
| +------------------------------------------> 2. Owner Permissions (3 位符号,owner 权限)
+----------------------------------------------> 1. File Type (1 位符号,文件类型)
demos
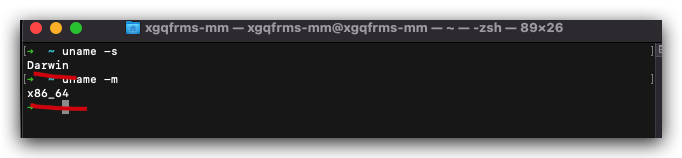
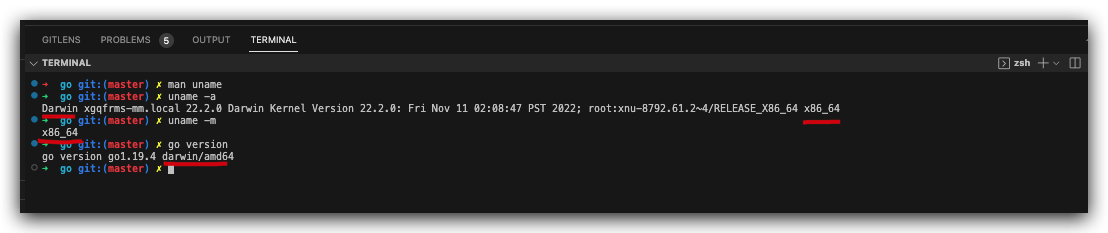
macOS 13 & Intel x86 64
$ uname -s
# Darwin
$ uname -m
# x86_64
# uname
$ uname
Darwin
$ uname -a
Darwin xgqfrms-mm.local 22.2.0 Darwin Kernel Version 22.2.0: Fri Nov 11 02:08:47 PST 2022; root:xnu-8792.61.2~4/RELEASE_X86_64 x86_64
$ go version
go version go1.19.4 darwin/amd64
Darwin/x86_64/darwin/amd64
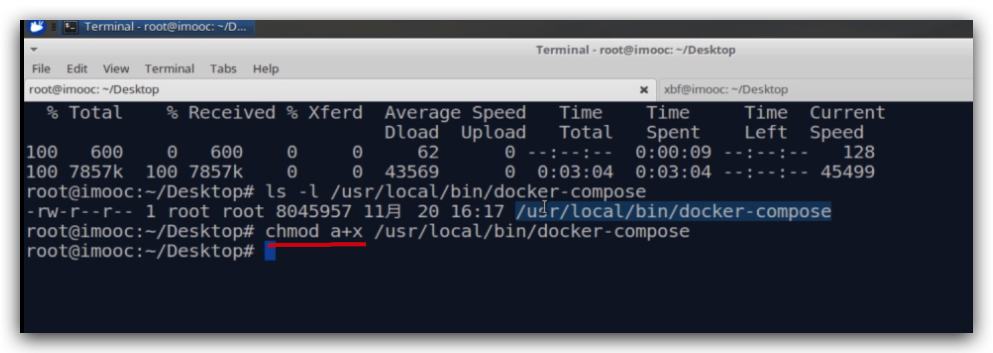
docker
docker-compose
# $ curl -L https://github.com/docker/compose/releases/download/v2.14.2/docker-compose-darwin-aarch64 > /usr/local/bin/docker-compose ❌
# $ curl -L https://github.com/docker/compose/releases/download/v2.14.2/docker-compose-darwin-x86_64 > /usr/local/bin/docker-compose ✅
# 动态生成对应的系统架构的下载版本 URL
$ curl -L https://github.com/docker/compose/releases/download/v2.14.2/docker-compose-$(uname -s)-$(uname -m) > /usr/local/bin/docker-compose
$ ls -l /usr/local/bin/docker-compose
$ chmod a+x /usr/local/bin/docker-compose
$ docker-compose --version
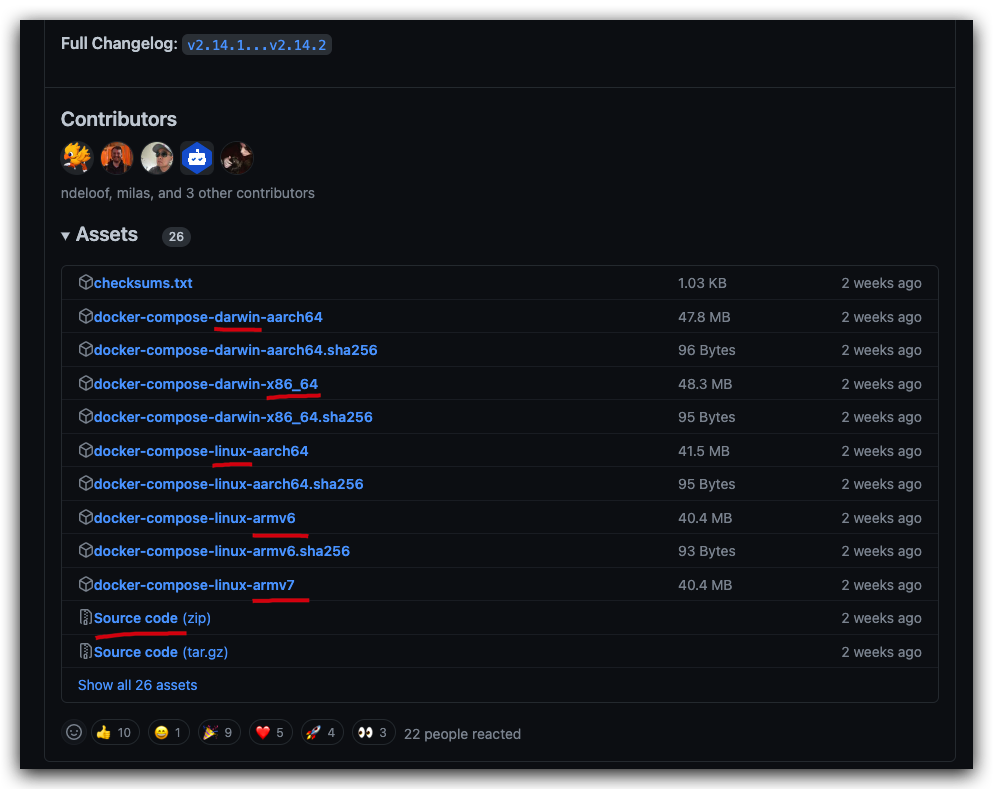
https://github.com/docker/compose/releases
https://github.com/docker/compose/releases/tag/v2.14.2
https://github.com/docker/compose/releases/download/v2.14.2/docker-compose-darwin-aarch64 ❌
https://github.com/docker/compose/releases/download/v2.14.2/docker-compose-darwin-x86_64 ✅
https://www.imooc.com/u/index/notebook
man chmod
# 点击查看详情
$ man chmod
$ man chmod > man-chmod.md
# 点击查看详情
$ man chmod
$ man chmod > man-chmod.md
$ man chmod
CHMOD(1) General Commands Manual CHMOD(1)
NAME
chmod – change file modes or Access Control Lists
SYNOPSIS
chmod [-fhv] [-R [-H | -L | -P]] mode file ...
chmod [-fhv] [-R [-H | -L | -P]] [-a | +a | =a] ACE file ...
chmod [-fhv] [-R [-H | -L | -P]] [-E] file ...
chmod [-fhv] [-R [-H | -L | -P]] [-C] file ...
chmod [-fhv] [-R [-H | -L | -P]] [-N] file ...
DESCRIPTION
The chmod utility modifies the file mode bits of the listed files as
specified by the mode operand. It may also be used to modify the Access
Control Lists (ACLs) associated with the listed files.
The generic options are as follows:
-f Do not display a diagnostic message if chmod could not modify the
mode for file, nor modify the exit status to reflect such
failures.
-H If the -R option is specified, symbolic links on the command line
are followed and hence unaffected by the command. (Symbolic
links encountered during tree traversal are not followed.)
-h If the file is a symbolic link, change the mode of the link
itself rather than the file that the link points to.
-L If the -R option is specified, all symbolic links are followed.
-P If the -R option is specified, no symbolic links are followed.
This is the default.
-R Change the modes of the file hierarchies rooted in the files,
instead of just the files themselves. Beware of unintentionally
matching the “..” hard link to the parent directory when using
wildcards like “.*”.
-v Cause chmod to be verbose, showing filenames as the mode is
modified. If the -v flag is specified more than once, the old
and new modes of the file will also be printed, in both octal and
symbolic notation.
The -H, -L and -P options are ignored unless the -R option is specified.
In addition, these options override each other and the command's actions
are determined by the last one specified.
If chmod receives a SIGINFO signal (see the status argument for stty(1)),
then the current filename as well as the old and new modes are displayed.
Only the owner of a file or the super-user is permitted to change the
mode of a file.
EXIT STATUS
The chmod utility exits 0 on success, and >0 if an error occurs.
MODES
Modes may be absolute or symbolic. An absolute mode is an octal number
constructed from the sum of one or more of the following values:
4000 (the setuid bit). Executable files with this bit set will
run with effective uid set to the uid of the file owner.
Directories with this bit set will force all files and sub-
directories created in them to be owned by the directory
owner and not by the uid of the creating process, if the
underlying file system supports this feature: see chmod(2)
and the suiddir option to mount(8).
2000 (the setgid bit). Executable files with this bit set will
run with effective gid set to the gid of the file owner.
1000 (the sticky bit). See chmod(2) and sticky(7).
0400 Allow read by owner.
0200 Allow write by owner.
0100 For files, allow execution by owner. For directories,
allow the owner to search in the directory.
0040 Allow read by group members.
0020 Allow write by group members.
0010 For files, allow execution by group members. For
directories, allow group members to search in the
directory.
0004 Allow read by others.
0002 Allow write by others.
0001 For files, allow execution by others. For directories
allow others to search in the directory.
For example, the absolute mode that permits read, write and execute by
the owner, read and execute by group members, read and execute by others,
and no set-uid or set-gid behaviour is 755 (400+200+100+040+010+004+001).
The symbolic mode is described by the following grammar:
mode ::= clause [, clause ...]
clause ::= [who ...] [action ...] action
action ::= op [perm ...]
who ::= a | u | g | o
op ::= + | - | =
perm ::= r | s | t | w | x | X | u | g | o
The who symbols ``u'', ``g'', and ``o'' specify the user, group, and
other parts of the mode bits, respectively. The who symbol ``a'' is
equivalent to ``ugo''.
The perm symbols represent the portions of the mode bits as follows:
r The read bits.
s The set-user-ID-on-execution and set-group-ID-on-execution
bits.
t The sticky bit.
w The write bits.
x The execute/search bits.
X The execute/search bits if the file is a directory or any
of the execute/search bits are set in the original
(unmodified) mode. Operations with the perm symbol ``X''
are only meaningful in conjunction with the op symbol
``+'', and are ignored in all other cases.
u The user permission bits in the original mode of the file.
g The group permission bits in the original mode of the file.
o The other permission bits in the original mode of the file.
The op symbols represent the operation performed, as follows:
+ If no value is supplied for perm, the ``+'' operation has no
effect. If no value is supplied for who, each permission bit
specified in perm, for which the corresponding bit in the file mode
creation mask (see umask(2)) is clear, is set. Otherwise, the mode
bits represented by the specified who and perm values are set.
- If no value is supplied for perm, the ``-'' operation has no
effect. If no value is supplied for who, each permission bit
specified in perm, for which the corresponding bit in the file mode
creation mask is set, is cleared. Otherwise, the mode bits
represented by the specified who and perm values are cleared.
= The mode bits specified by the who value are cleared, or, if no who
value is specified, the owner, group and other mode bits are
cleared. Then, if no value is supplied for who, each permission
bit specified in perm, for which the corresponding bit in the file
mode creation mask (see umask(2)) is clear, is set. Otherwise, the
mode bits represented by the specified who and perm values are set.
Each clause specifies one or more operations to be performed on the mode
bits, and each operation is applied to the mode bits in the order
specified.
Operations upon the other permissions only (specified by the symbol ``o''
by itself), in combination with the perm symbols ``s'' or ``t'', are
ignored.
The ``w'' permission on directories will permit file creation,
relocation, and copy into that directory. Files created within the
directory itself will inherit its group ID.
EXAMPLES OF VALID MODES
644 make a file readable by anyone and writable by the owner
only.
go-w deny write permission to group and others.
=rw,+X set the read and write permissions to the usual defaults,
but retain any execute permissions that are currently set.
+X make a directory or file searchable/executable by everyone
if it is already searchable/executable by anyone.
755
u=rwx,go=rx
u=rwx,go=u-w make a file readable/executable by everyone and writable by
the owner only.
go= clear all mode bits for group and others.
g=u-w set the group bits equal to the user bits, but clear the
group write bit.
ACL MANIPULATION OPTIONS
ACLs are manipulated using extensions to the symbolic mode grammar. Each
file has one ACL, containing an ordered list of entries. Each entry
refers to a user or group, and grants or denies a set of permissions. In
cases where a user and a group exist with the same name, the user/group
name can be prefixed with "user:" or "group:" in order to specify the
type of name.
If the user or group name contains spaces you can use ':' as the
delimiter between name and permission.
The following permissions are applicable to all filesystem objects:
delete Delete the item. Deletion may be granted by either this
permission on an object or the delete_child right on the
containing directory.
readattr
Read an object's basic attributes. This is implicitly
granted if the object can be looked up and not explicitly
denied.
writeattr
Write an object's basic attributes.
readextattr
Read extended attributes.
writeextattr
Write extended attributes.
readsecurity
Read an object's extended security information (ACL).
writesecurity
Write an object's security information (ownership, mode,
ACL).
chown Change an object's ownership.
The following permissions are applicable to directories:
list List entries.
search Look up files by name.
add_file
Add a file.
add_subdirectory
Add a subdirectory.
delete_child
Delete a contained object. See the file delete permission
above.
The following permissions are applicable to non-directory filesystem
objects:
read Open for reading.
write Open for writing.
append Open for writing, but in a fashion that only allows writes
into areas of the file not previously written.
execute
Execute the file as a script or program.
ACL inheritance is controlled with the following permissions words, which
may only be applied to directories:
file_inherit
Inherit to files.
directory_inherit
Inherit to directories.
limit_inherit
This flag is only relevant to entries inherited by
subdirectories; it causes the directory_inherit flag to be
cleared in the entry that is inherited, preventing further
nested subdirectories from also inheriting the entry.
only_inherit
The entry is inherited by created items but not considered
when processing the ACL.
The ACL manipulation options are as follows:
+a The +a mode parses a new ACL entry from the next argument on the
commandline and inserts it into the canonical location in the
ACL. If the supplied entry refers to an identity already listed,
the two entries are combined.
Examples
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
# chmod +a "admin allow write" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: admin allow write
# chmod +a "guest deny read" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write
# chmod +a "admin allow delete" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write,delete
.
# chmod +a "User 1:allow:read" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: User 1 allow read
3: admin allow write,delete
The +a mode strives to maintain correct canonical form for the
ACL.
local deny
local allow
inherited deny
inherited allow
By default, chmod adds entries to the top of the local deny and
local allow lists. Inherited entries are added by using the +ai
mode.
Examples
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write,delete
3: juser inherited deny delete
4: admin inherited allow delete
5: backup inherited deny read
6: admin inherited allow write-security
# chmod +ai "others allow read" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write,delete
3: juser inherited deny delete
4: admin inherited allow delete
5: backup inherited deny read
6: admin inherited allow write-security
# chmod +ai "others allow read" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write,delete
3: juser inherited deny delete
4: others inherited allow read
5: admin inherited allow delete
6: backup inherited deny read
7: admin inherited allow write-security
+a# When a specific ordering is required, the exact location at which
an entry will be inserted is specified with the +a# mode.
Examples
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write
# chmod +a# 2 "others deny read" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: others deny read
3: admin allow write
The +ai# mode may be used to insert inherited entries at a
specific location. Note that these modes allow non-canonical ACL
ordering to be constructed.
-a The -a mode is used to delete ACL entries. All entries exactly
matching the supplied entry will be deleted. If the entry lists a
subset of rights granted by an entry, only the rights listed are
removed. Entries may also be deleted by index using the -a# mode.
Examples
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: guest deny read
2: admin allow write,delete
# chmod -a# 1 file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: admin allow write,delete
# chmod -a "admin allow write" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: admin allow delete
Inheritance is not considered when processing the -a mode; rights
and entries will be removed regardless of their inherited state.
If the user or group name contains spaces you can use ':' as the
Example
# chmod +a "User 1:allow:read" file1
=a# Individual entries are rewritten using the =a# mode.
Examples
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: admin allow delete
# chmod =a# 1 "admin allow write,chown" file1
# ls -le
-rw-r--r--+ 1 juser wheel 0 Apr 28 14:06 file1
owner: juser
1: admin allow write,chown
This mode may not be used to add new entries.
-E Reads the ACL information from stdin, as a sequential list of
ACEs, separated by newlines. If the information parses
correctly, the existing information is replaced.
-C Returns false if any of the named files have ACLs in non-
canonical order.
-i Removes the 'inherited' bit from all entries in the named file(s)
ACLs.
-I Removes all inherited entries from the named file(s) ACL(s).
-N Removes the ACL from the named file(s).
COMPATIBILITY
The -v option is non-standard and its use in scripts is not recommended.
SEE ALSO
chflags(1), install(1), chmod(2), stat(2), umask(2), fts(3), setmode(3),
sticky(7), symlink(7), chown(8), mount(8)
STANDARDS
The chmod utility is expected to be IEEE Std 1003.2 (“POSIX.2”)
compatible with the exception of the perm symbol “t” which is not
included in that standard.
HISTORY
A chmod command appeared in Version 1 AT&T UNIX.
macOS 13.0 January 7, 2017 macOS 13.0
(🐞 反爬虫测试!打击盗版⚠️)如果你看到这个信息, 说明这是一篇剽窃的文章,请访问 https://www.cnblogs.com/xgqfrms/ 查看原创文章!
refs
Linux & chmod & 777 & 755 All In One
https://www.cnblogs.com/xgqfrms/p/9546961.html
https://www.imooc.com/video/15734
©xgqfrms 2012-2021
www.cnblogs.com/xgqfrms 发布文章使用:只允许注册用户才可以访问!
原创文章,版权所有©️xgqfrms, 禁止转载 🈲️,侵权必究⚠️!
本文首发于博客园,作者:xgqfrms,原文链接:https://www.cnblogs.com/xgqfrms/p/17020855.html
未经授权禁止转载,违者必究!


