物联网架构成长之路(50)-EMQ配置SSL证书,实现MQTTs协议
0. 前言
EMQ是带有SSL功能的,需要进行简单的配置,才能使用。下面就简单说一下如何实现自签证书。
1. 利用OpenSSL签发证书
1 ➜ cat createCA.sh 2 #/bin/sh 3 # 生成自签名的CA key和证书 4 openssl genrsa -out ca.key 2048 5 openssl req -x509 -new -nodes -key ca.key -sha256 -days 3650 -subj "/CN=www.wunaozai.com" -out ca.pem 6 7 # 生成服务器端的key和证书 8 openssl genrsa -out server.key 2048 9 openssl req -new -key ./server.key -out server.csr -subj "/CN=0.0.0.0" 10 openssl x509 -req -in ./server.csr -CA ca.pem -CAkey ca.key -CAcreateserial -out server.pem -days 3650 -sha256 11 12 # 生成客户端key和证书 13 openssl genrsa -out client.key 2048 14 openssl req -new -key ./client.key -out client.csr -subj "/CN=0.0.0.0" 15 openssl x509 -req -in ./client.csr -CA ca.pem -CAkey ca.key -CAcreateserial -out client.pem -days 3650 -sha256 16 17 # 最后生成如下文件 18 ➜ ls 19 ca.key ca.pem ca.srl client.csr client.key client.pem createCA.sh server.csr server.key server.pem
2. 配置到EMQX的emqx.conf
如果启用单向认证的话,客户端不需要证书都可以连接。这里的listener.ssl.external.fail_if_no_peer_cert = true 注释掉就启用单向认证。
启用双向认证。那么客户端就必须导入CA和client的证书才可以连接。
1 listener.ssl.external = 8883 2 listener.ssl.external.acceptors = 16 3 listener.ssl.external.max_connections = 102400 4 listener.ssl.external.max_conn_rate = 500 5 listener.ssl.external.active_n = 100 6 listener.ssl.external.zone = external 7 listener.ssl.external.access.1 = allow all 8 listener.ssl.external.handshake_timeout = 15s 9 listener.ssl.external.keyfile = ../certs/server.key 10 listener.ssl.external.certfile = ../certs/server.pem 11 listener.ssl.external.cacertfile = ../certs/ca.pem 12 listener.ssl.external.verify = verify_peer 13 listener.ssl.external.fail_if_no_peer_cert = true 14 listener.ssl.external.ciphers = ECDHE-ECDSA-AES256-GCM-SHA384,ECDHE-RSA-AES256-GCM-SHA384,ECDHE-ECDSA-AES256-SHA384,ECDHE-RSA-AES256-SHA384,ECDHE-ECDSA-DES-CBC3-SHAAES256-GCM-SHA384,ECDH-ECDSA-AES256-SHA384,ECDH-RSA-AES256-SHA384,DHE-DSS-AES256-GCM-SHA384,DHE-DSS-AES256-SHA256,AES256-GCM-SHA384,AES256-SHA256,ECDHE-ECDSA-AES128,ECDHE-ECDSA-AES128-SHA256,ECDHE-RSA-AES128-SHA256,ECDH-ECDSA-AES128-GCM-SHA256,ECDH-RSA-AES128-GCM-SHA256,ECDH-ECDSA-AES128-SHA256,ECDH-RSA-AES128-SHA256,DHE-DSS-AAES128-GCM-SHA256,AES128-SHA256,ECDHE-ECDSA-AES256-SHA,ECDHE-RSA-AES256-SHA,DHE-DSS-AES256-SHA,ECDH-ECDSA-AES256-SHA,ECDH-RSA-AES256-SHA,AES256-SHA,ECDHE-ECDSA-AES1128-SHA,ECDH-ECDSA-AES128-SHA,ECDH-RSA-AES128-SHA,AES128-SHA 15 listener.ssl.external.reuseaddr = true
重新启动EMQX
1 ./bin/emqx stop 2 ./bin/emqx start
3. 工具测试
可以用MQTT.fx工具测试。我这里使用EMQ官方出品的MQTTX工具。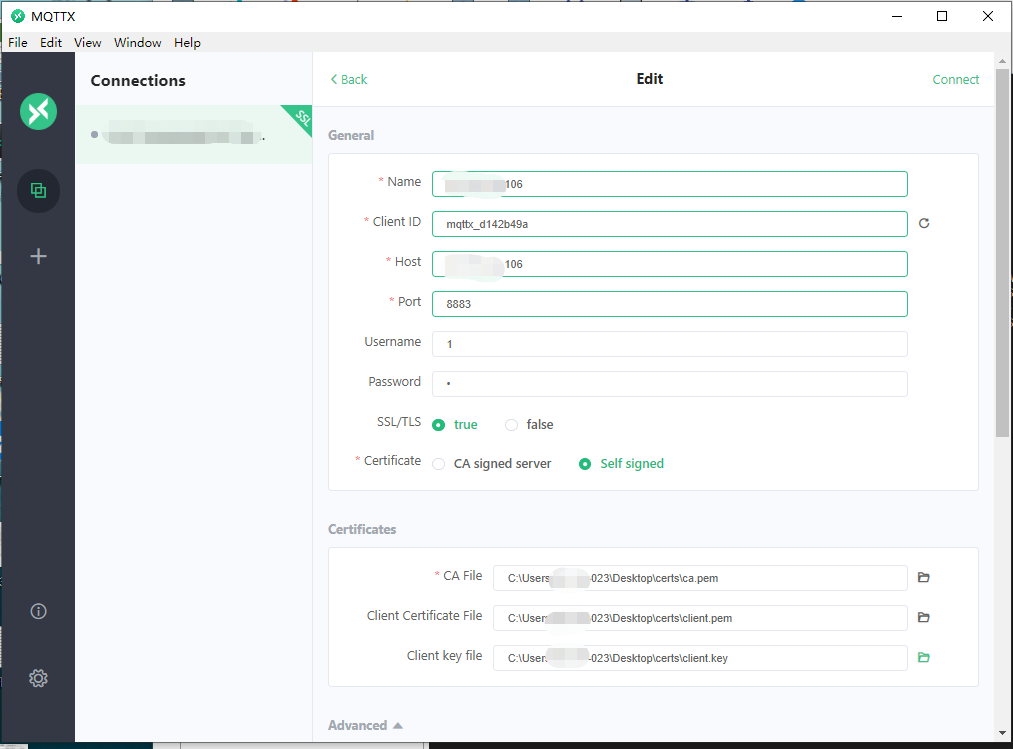
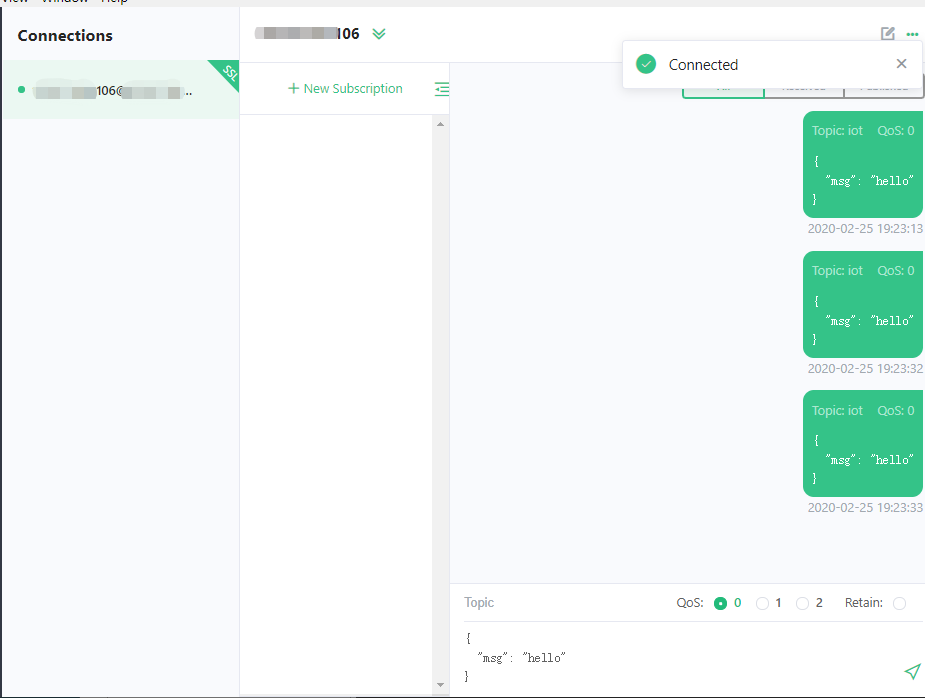
采用自签证书,可以签发多个client客户端的证书。可以做到一机一证。这样做的成本非常高,本身SSL加密对通信要求就高,如果还要管理那么多证书,就有点麻烦了。所以目前我采用的方式是,平台支持MQTTs通信,可以单向认证。只保证通讯安全。至于设备认证,就不通过证书认证,而是传统的设备ID与设备密码来认证。简单一点。平台改动也不大。
参考资料:
https://docs.emqx.io/cn/sdk_tools?category=MQTT_Tools
https://www.emqx.io/cn/downloads#broker
https://docs.emqx.io/broker/latest/cn/config.html?highlight=ssl#mqtt-ssl-8883
https://segmentfault.com/a/1190000020058373#item-2
https://blog.csdn.net/u011089760/article/details/89951214
本文地址:https://www.cnblogs.com/wunaozai/p/12367497.html
本系列目录: https://www.cnblogs.com/wunaozai/p/8067577.html
个人主页:https://www.wunaozai.com/
|
作者:无脑仔的小明 出处:http://www.cnblogs.com/wunaozai/ 本文版权归作者和博客园共有,欢迎转载,但未经作者同意必须保留此段声明,且在文章页面明显位置给出原文连接,否则保留追究法律责任的权利。 如果文中有什么错误,欢迎指出。以免更多的人被误导。有需要沟通的,可以站内私信,文章留言,或者关注“无脑仔的小明”公众号私信我。一定尽力回答。 |



 浙公网安备 33010602011771号
浙公网安备 33010602011771号