在阿里云CentOS 7.4 简单快速搭建Strongswan IKEv2类型 教程模板
转载:https://blog.csdn.net/qq_29364417/article/details/80713440
1、安装strongswan
yum install strongswan
官网下载:https://pkgs.org/download/strongswan
如果提示没有包,到下方地址下载,然后使用 yum install strongswan-5.7.2-1.el7.aarch64.rpm 安装
链接: https://pan.baidu.com/s/1VcaOwzHutH9mlAE6lMu2HQ 密码: 5ofb
2、创建证书
strongswan pki --gen --outform pem > ca.key.pem
strongswan pki --self --in ca.key.pem --dn "C=CN, O=one, CN=one t CA" --ca --lifetime 3650 --outform pem > ca.cert.pem
strongswan pki --gen --outform pem > server.key.pem
strongswan pki --pub --in server.key.pem --outform pem > server.pub.pem
strongswan pki --pub --in server.key.pem | strongswan pki --issue --lifetime 3601 --cacert ca.cert.pem --cakey ca.key.pem --dn "C=CN, O=one, CN=one t CA" --san="你的服务器公网ip" --flag serverAuth --flag ikeIntermediate --outform pem > server.cert.pem
3、安装证书
cp -r ca.key.pem /etc/strongswan/ipsec.d/private/ cp -r ca.cert.pem /etc/strongswan/ipsec.d/cacerts/ cp -r server.cert.pem /etc/strongswan/ipsec.d/certs/ cp -r server.pub.pem /etc/strongswan/ipsec.d/certs/ cp -r server.key.pem /etc/strongswan/ipsec.d/private/
4、配置
vi /etc/strongswan/ipsec.conf
config setup uniqueids=never #允许多个客户端使用同一个证书 conn %default #定义连接项, 命名为 %default 所有连接都会继承它 compress = yes #是否启用压缩, yes 表示如果支持压缩会启用. dpdaction = clear #当意外断开后尝试的操作, hold, 保持并重连直到超时. dpddelay = 30s #意外断开后尝试重连时长 dpdtimeout = 60s #意外断开后超时时长, 只对 IKEv1 起作用 inactivity = 300s #闲置时长,超过后断开连接. leftdns = 8.8.8.8,8.8.4.4 #指定服务端与客户端的dns, 多个用","分隔 rightdns = 8.8.8.8,8.8.4.4 conn IKEv2-BASE leftca = "C=CN, O=one, CN=one t CA" #服务器端根证书DN名称,与 --dn 内容一致 leftsendcert = always #是否发送服务器证书到客户端 rightsendcert = never #客户端不发送证书 conn IKEv2-EAP keyexchange=ikev2 #默认的密钥交换算法, ike 为自动, 优先使用 IKEv2 left=%any #服务器端标识,%any表示任意 leftid= 你的服务器公网ip #服务器端ID标识,你的服务器公网ip leftsubnet=0.0.0.0/0 #服务器端虚拟ip, 0.0.0.0/0表示通配. leftcert = server.cert.pem #服务器端证书 leftauth=pubkey #服务器校验方式,使用证书 right=%any #客户端标识,%any表示任意 rightsourceip = 20.1.0.0/16 #客户端IP地址分配范围 rightauth=eap-mschapv2 #eap-md5#客户端校验方式#KEv2 EAP(Username/Password) also=IKEv2-BASE eap_identity = %any #指定客户端eap id rekey = no #不自动重置密钥 fragmentation = yes #开启IKE 消息分片 auto = add #当服务启动时, 应该如何处理这个连接项. add 添加到连接表中. #ios 和 mac Psk连接,无需证书 (EAP账号密码及psk) #android Psk 连接,无需证书(XAUTH账户密码及psk) conn Android_Ios_Mac_XauthPSK keyexchange=ikev1 ike=aes128-aes256-sha1-modp3072-modp2048,3des-sha1-md5-modp1024,aes256-sha512-modp4096,aes128-sha256-modp3072 esp=aes128-sha1,aes256-sha256_96,3des-sha1,aes256-sha1 left=%defaultroute leftauth=psk leftsubnet=0.0.0.0/0 right=%any rightauth=psk rightauth2=xauth rightsourceip=20.1.0.0/16 auto=add
5、修改配置 (旧版,可选)
vi /etc/strongswan/strongswan.d/charon.conf
charon { duplicheck_enable = no #同时连接多个设备,把冗余检查关闭. i_dont_care_about_security_and_use_aggressive_mode_psk = yes # windows 公用 dns dns1 = 8.8.8.8 dns2 = 8.8.4.4 #以下是日志输出, 生产环境请关闭. filelog { /var/log/charon.log { # add a timestamp prefix time_format = %b %e %T # prepend connection name, simplifies grepping ike_name = yes # overwrite existing files append = no # increase default loglevel for all daemon subsystems default = 1 # flush each line to disk flush_line = yes } } }
5. 修改配置 (新版)
vi /etc/strongswan/strongswan.conf
charon { load_modular = yes i_dont_care_about_security_and_use_aggressive_mode_psk = yes compress = yes plugins { duplicheck{ enable=no } include strongswan.d/charon/*.conf } } include strongswan.d/*.conf
5-1.(新版)打开另一连接窗口 显示strongswan 所产生的日志(两种)
journalctl -f -u strongswan
tail -f /var/log/messages
6、配置用户和密码
vi /etc/strongswan/ipsec.secrets
# ipsec.secrets - strongSwan IPsec secrets file #使用证书验证时的服务器端私钥 #格式 : RSA <private key file> [ <passphrase> | %prompt ] : RSA server.key.pem #使用预设加密密钥, 越长越好 #格式 [ <id selectors> ] : PSK <secret> : PSK "pOneAA123456" #EAP 方式, 格式同 psk 相同 (用户名/密码 例:oneAA/oneTT) eOneAA : EAP "eOneTT" #XAUTH 方式, 只适用于 IKEv1 #格式 [ <servername> ] <username> : XAUTH "<password>" xOneAA : XAUTH "xOneTT"
7、开启内核转发
vi /etc/sysctl.conf
net.ipv4.ip_forward = 1
net.ipv6.conf.all.forwarding=1
sysctl -p
配置 伪装 及 添加隧道:( GCP专用,阿里云不用配置此项)
① 添加udp 端口
firewall-cmd --permanent --add-port=500-4500/udp
firewall-cmd --permanent --add-masquerade
② 调整MTU-MSS、添加GRE,否则隧道失败:
firewall-cmd --permanent --direct --add-rule ipv4 filter INPUT 0 -p gre -j ACCEPT
firewall-cmd --permanent --direct --add-rule ipv4 filter FORWARD 0 -p tcp -i eth0 -j TCPMSS --syn --set-mss 1299
查看是否已添加防火墙参数
firewall-cmd --get-active
firewall-cmd --get-default
vi /etc/firewalld/direct.xml
8、配置防火 (阿里云)
vi /etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?> <zone> <short>Public</short> <description>For use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.</description> <interface name="eth0"/> <service name="ssh"/> <service name="dhcpv6-client"/> <service name="ipsec"/> <port protocol="tcp" port="1723"/> <port protocol="tcp" port="47"/> <port protocol="tcp" port="1701"/> <port protocol="tcp" port="22"/> <masquerade/> <rule family="ipv4"> <source address="10.1.0.0/16"/> <masquerade/> </rule> <rule family="ipv4"> <source address="10.1.0.0/16"/> <forward-port to-port="4500" protocol="udp" port="4500"/> </rule> <rule family="ipv4"> <source address="10.1.0.0/16"/> <forward-port to-port="500" protocol="udp" port="500"/> </rule> <masquerade/> </zone>
9、开启 防火墙/strongswan 以及 自动启动
systemctl enable firewalld
systemctl start firewalld
systemctl enable strongswan
systemctl start strongswan
10、阿里云开放端口
登录阿里云管理控制台- -> 云服务器ECS- ->网络和安全- ->安全组- ->添加安全组规则:
授权策略:允许
协议类型:自定义UDP
端口范围:500/4500
授权类型:地址段访问
授权对象:0.0.0.0/0
优先级:100
描述:随便填
注意!添加完成后必须 重启 服务器
XauthPSK 连接: Android 使用 XAUTH 账户密码及psk 连接
Mac 和 Ios 使用 EAP 账户密码及psk 连接
11、证书安装及连接,用ftp工具(例:FileZilla)下载 /etc/strongswan/ipsec.d/cacerts/ca.cert.pem 证书到本地。
ios证书安装:将之前创建的 ca.cert.pem 用 ftp 导出 , 写邮件以附件的方式发到邮箱, 在ios Safari浏览器登录邮箱, 下载附件, 安装证书。
步骤:
例:类型:IKEv2
描述:随便填
服务器:你的服务器公网ip
远程ID:你的服务器公网ip
本地ID:不用填,空着
选择- ->用户名,填写-用户名-密码 - ->点击--完成
mac证书安装:双击 ca.cert.pem -->选中你的证书-->显示简介-->信任-->始终信任(然后会弹框填写mac登录密码)。
步骤:系统编好设置- ->网络- ->左侧点击+号- ->接口:IKEv2 - ->服务名称:随便填- ->点击 创建。
接下来填写账户密码地址 例:服务器地址:你的服务器公网ip
远程ID:你的服务器公网ip
本地ID:不用填,空着
点击- -鉴定设置- ->选择- ->用户名,填写-用户名-密码 - ->点击--连接
android:去strongswan官网下载安装 例:https://download.strongswan.org/Android/strongSwan-1.9.6.apk
或:https://download.csdn.net/download/qq_29364417/10482582
或者编译源码:https://github.com/strongswan/strongswan/tree/master/src/frontends/android
步骤:右上角选项-->CA证书-->再选择右上角选项-->导入证书-->找到ca.cert.pem点击即可。
回到主界面-->添加配置-->例:服务器地址:你的服务器公网ip
类型:IKEv2 EAP(用户名/密码),填写用户名和密码
CA证书:选择刚才导入的ca.cert.pem证书
点击右上角--保存
回到主界面--点击配置连接即可
Windows10 连接的坑:
1. windows的vpn虚拟网卡默认mtu是1400
现象:如果服务端的mtu小于1400的话,会出现能ping通地址,但是网页不能打开的问题 解决办法:修改vpn虚拟网卡mtu值 连接vpn后,以管理员身份执行以下命令 netsh interface ipv4 set subinterface "vpn名称" mtu=1350 store=persistent
2. windows默认不支持DH2048_AES256协商协议
现象:提示策略匹配错误 解决办法:添加注册表项,不需要重启生效 HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Rasman\Parameters里新建类型为DWORD的NegotiateDH2048_AES256 键,值设置为1 0 禁用AES-256-CBC和MODP-2048 1 启用AES-256-CBC和MODP-2048 2 强制使用AES-256-CBC和MODP-2048
3. windows默认不支持Symmetric NAT类型路由器后的ikev2服务器
现象:提示809错误,或者提示路由器不支持nat 解决办法:添加注册表项,并需要重启生效 HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\PolicyAgent里新建类型为DWORD的AssumeUDPEncapsulationContextOnSendRule 键,值设置为2 0 A value of 0 (zero) configures Windows so that it cannot establish security associations with servers that are located behind NAT devices. This is the default value. 1 A value of 1 configures Windows so that it can establish security associations with servers that are located behind NAT devices. 2 A value of 2 configures Windows so that it can establish security associations when both the server and the Windows Vista-based or Windows Server 2008-based VPN client computer are behind NAT devices.
4. windows手动添加的vpn默认没有开启默认路由
现象:连接成功,但是对外ip没有改变
解决办法:手动添加修改或者使用powershell新建vpn连接,手动路径:控制面板网络和 Internet网络连接,vpn网卡,属性,网络,ipv4,属性,高级,勾选在远程网络上使用默认网关
5. windows10默认开启了smart multi-homed name resolution功能
现象:有线网络下连接vpn后不使用vpn的dns
解决办法:修改vpn网卡的跃点数,小于有线网卡即可。脚本自动解决待更新
批处理脚本如下,实际是使用批处理调用powershell命令,由于需要修改注册表,需要管理员权限运行

@echo off&PUSHD %~DP0 &TITLE ikev2 VPN安装/卸载程序 mode con cols=160 lines=50 set TempFile_Name=%SystemRoot%\System32\BatTestUACin_SysRt%Random%.batemp ( echo "BAT Test UAC in Temp" >%TempFile_Name% ) 1>nul 2>nul if exist %TempFile_Name% ( del %TempFile_Name% 1>nul 2>nul&&goto :address ) else ( echo;请以管理员身份运行,按任意键退出 &&goto :end ) :address cls echo;请输入办公地点: echo;1:北京 echo;2:成都 echo;3:重庆 set/p choose1=请输入选项并按回车: echo %choose1%|findstr /i "[123]">nul&&goto :install goto :address :install cls echo;请选择安装或者卸载VPN(ikev2): echo;i:安装 echo;u:卸载 echo;q:退出 set/p choose2=请输入选项并按回车: echo %choose2%|findstr /i "[iuq]">nul&&goto :%choose1%%choose2% goto :install :1i cls echo;安装北京VPN echo;=========================== echo;***步骤1:删除同名VPN*** (powershell -Command "& {Remove-VpnConnection -Name "北京办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功 echo; echo;***步骤2:安装新的VPN*** powershell -Command "& {Add-VpnConnection -Name "北京办公室" -ServerAddress "beijing.example.com" -AuthenticationMethod "Eap" -EncryptionLevel "Maximum" -RememberCredential -TunnelType "Ikev2" -PassThru;}" echo;成功 echo; echo;***步骤3:清理注册表*** (powershell -Command "& {Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256"; Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule ";}") 1>nul 2>nul echo;成功 echo; echo;***步骤4:添加注册表*** (powershell -Command "& {New-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1 -propertyType dword; New-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2 -propertyType dword;}") 1>nul 2>nul echo;成功 echo; echo;***步骤5:设置注册表*** powershell -Command "& {Set-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1; Set-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2;}" echo;成功 echo; echo;***步骤6:重启电脑*** echo;按任意键重启电脑,或按右上角 X 退出后手动重启电脑 pause>nul shutdown -r -t 0 goto :end :1u cls echo;卸载北京VPN echo;=========================== (powershell -Command "& {Remove-VpnConnection -Name "北京办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功,按任意键退出... goto :end :2i cls echo;安装成都VPN echo;=========================== echo;***步骤1:删除同名VPN*** (powershell -Command "& {Remove-VpnConnection -Name "成都办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功 echo; echo;***步骤2:安装新的VPN*** powershell -Command "& {Add-VpnConnection -Name "成都办公室" -ServerAddress "chengdu.example.com" -AuthenticationMethod "Eap" -EncryptionLevel "Maximum" -RememberCredential -TunnelType "Ikev2" -PassThru;}" echo;成功 echo; echo;***步骤3:清理注册表*** (powershell -Command "& {Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256"; Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule ";}") 1>nul 2>nul echo;成功 echo; echo;***步骤4:添加注册表*** (powershell -Command "& {New-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1 -propertyType dword; New-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2 -propertyType dword;}") 1>nul 2>nul echo;成功 echo; echo;***步骤5:设置注册表*** powershell -Command "& {Set-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1; Set-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2;}" echo;成功 echo; echo;***步骤6:重启电脑*** echo;按任意键重启电脑,或按右上角 X 退出后手动重启电脑 pause>nul shutdown -r -t 0 goto :end :2u cls echo;卸载成都VPN echo;=========================== (powershell -Command "& {Remove-VpnConnection -Name "成都办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功,按任意键退出... goto :end :3i cls echo;安装重庆VPN echo;=========================== echo;***步骤1:删除同名VPN*** (powershell -Command "& {Remove-VpnConnection -Name "重庆办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功 echo; echo;***步骤2:安装新的VPN*** powershell -Command "& {Add-VpnConnection -Name "重庆办公室" -ServerAddress "chongqing.example.com" -AuthenticationMethod "Eap" -EncryptionLevel "Maximum" -RememberCredential -TunnelType "Ikev2" -PassThru;}" echo;成功 echo; echo;***步骤3:清理注册表*** (powershell -Command "& {Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256"; Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule ";}") 1>nul 2>nul echo;成功 echo; echo;***步骤4:添加注册表*** (powershell -Command "& {New-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1 -propertyType dword; New-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2 -propertyType dword;}") 1>nul 2>nul echo;成功 echo; echo;***步骤5:设置注册表*** powershell -Command "& {Set-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1; Set-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2;}" echo;成功 echo; echo;***步骤6:重启电脑*** echo;按任意键重启电脑,或按右上角 X 退出后手动重启电脑 pause>nul shutdown -r -t 0 goto :end :3u cls echo;卸载重庆VPN echo;=========================== (powershell -Command "& {Remove-VpnConnection -Name "重庆办公室" -Force -PassThru;}") 1>nul 2>nul echo;成功,按任意键退出... goto :end :end pause>nul
powershell脚本,需要以管理员身份运行powershell然后执行install.ps1

Remove-VpnConnection -Name "成都办公室" -Force Add-VpnConnection -Name "成都办公室" -ServerAddress "chengdu.example.com" -AuthenticationMethod "Eap" -EncryptionLevel "Maximum" -RememberCredential -TunnelType "Ikev2" Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" Remove-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule" New-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1 -propertyType dword New-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule" -value 2 -propertyType dword Set-ItemProperty HKLM:\System\CurrentControlSet\Services\Rasman\Parameters -name "NegotiateDH2048_AES256" -value 1 Set-ItemProperty HKLM:\System\CurrentControlSet\Services\PolicyAgent -name "AssumeUDPEncapsulationContextOnSendRule " -value 2
6. 安装证书的坑
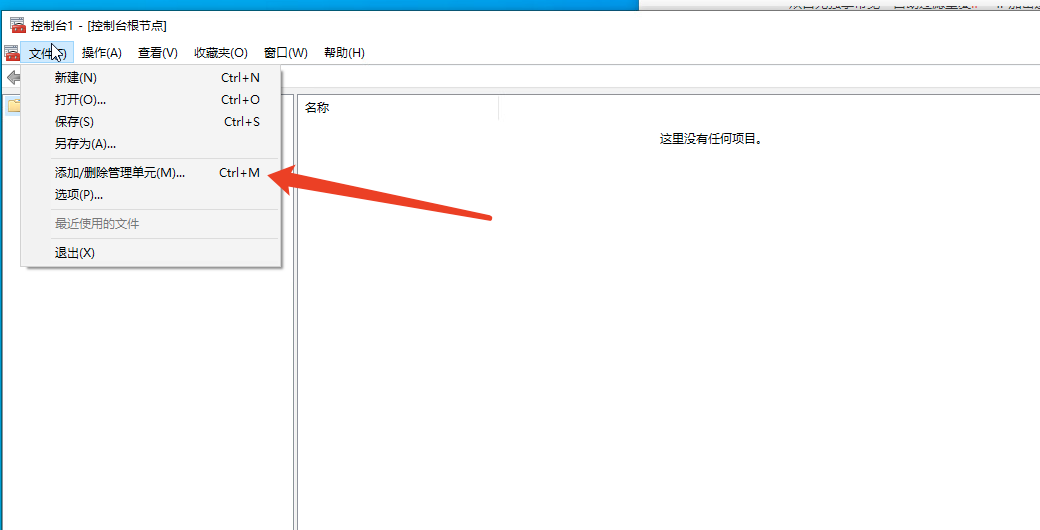
1. 运行-> 输入mmc->添加/删除单元
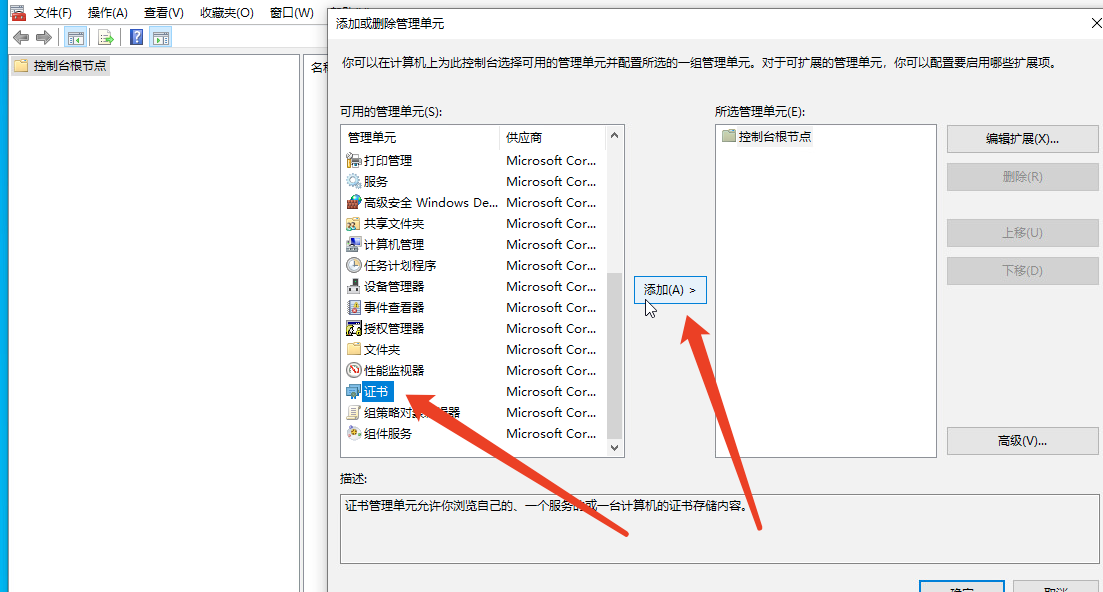
2.找到证书->添加
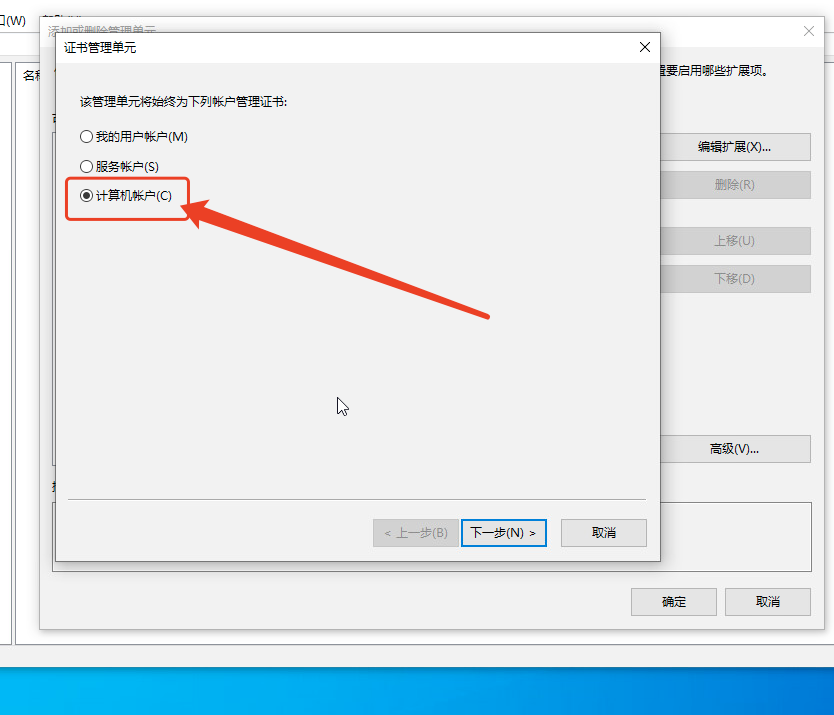
3.坑来了,一定要选择计算机账户!!!(否则导入证书无效会出现 IKE身份验证凭证不可接受 错误)
4. 后面直接选默认然后完成
5. 导入证书,导入的位置一定要正确
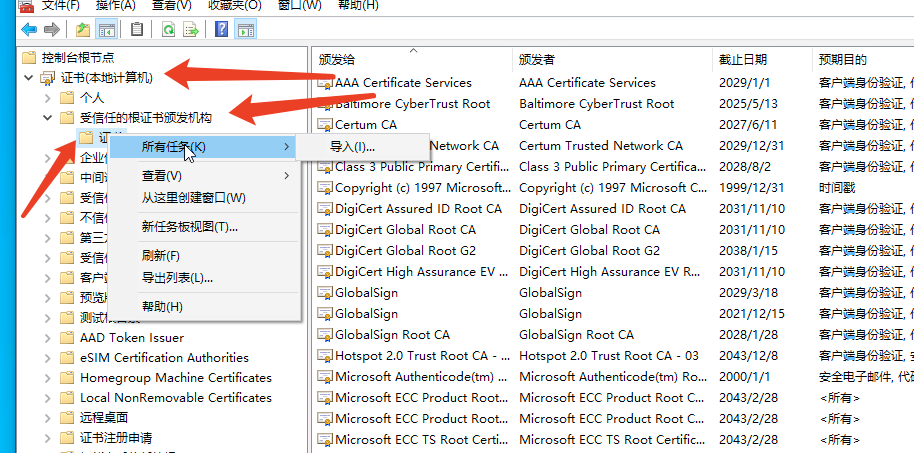
6. 选择证书导入,找证书的时候选择所有文件




 浙公网安备 33010602011771号
浙公网安备 33010602011771号