HUAWEI-基于流策略实现策略路由+NAT44
HUAWEI-基于流策略实现策略路由+NAT44
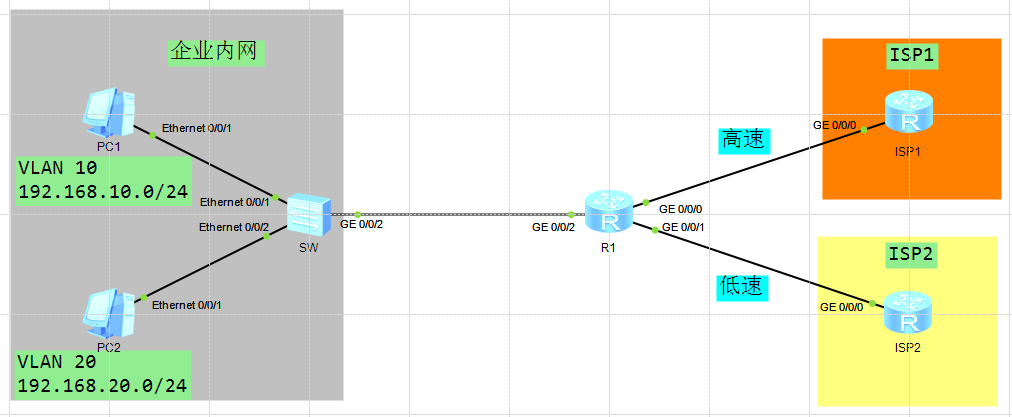
背景说明: 某公司内部两个网段,192.168.10.0/24和192.168.20.0/24,通过出口路由R1单臂路由实现VLAN间的路由,同时192.168.10.0/24由于业务原因对于流量需求较大,网络管理员决定通过流策略实现192.168.10.0/24通过高速链路使用NAT访问Internet,带宽需求就低的192.168.20.0/24通过低速链路使用NAT访问Internet
IP地址规划表:
| 本端设备 | 端口 | IP地址或所属VLAN | 对端设备 | 端口 | IP地址或所属VLAN |
|---|---|---|---|---|---|
| R1 | GE 0/0/0 | 202.100.1.2/29 | ISP1 | GE 0/0/0 | 202.100.1.1/29 |
| R1 | GE 0/0/1 | 104.114.128.2/29 | ISP2 | GE 0/0/0 | 104.114.128.1/29 |
| R1 | GE 0/0/2 | SW | GE 0/0/2 | ||
| R1 | GE 0/0/2.1 | 192.168.10.1/24 | SW | GE 0/0/2 | VLAN 10 |
| R1 | GE 0/0/2.2 | 192.168.20.1/24 | SW | GE 0/0/2 | VLAN 20 |
| SW | Eth 0/0/1 | VLAN 10 | PC1 | Eth 0/0/1 | 192.168.10.10/24 |
| SW | Eth 0/0/2 | VLAN 20 | PC2 | Eth 0/0/1 | 192.168.20.10/24 |
配置步骤:
项目实施:
一、配置配置VLAN并配置接口,配置单臂路由和静态路由实现网络互通。
[SW] vlan batch 10 20
Info: This operation may take a few seconds. Please wait for a moment...done.
#
[SW]interface Ethernet0/0/1
[SW-Ethernet0/0/1] port link-type access
[SW-Ethernet0/0/1] port default vlan 10
#
[SW-Ethernet0/0/1]interface Ethernet0/0/2
[SW-Ethernet0/0/2] port link-type access
[SW-Ethernet0/0/2] port default vlan 20
#
[SW-Ethernet0/0/2]interface GigabitEthernet0/0/2
[SW-GigabitEthernet0/0/2] port link-type trunk
[SW-GigabitEthernet0/0/2] port trunk allow-pass vlan 10 20
[R1]interface GigabitEthernet0/0/0
[R1-GigabitEthernet0/0/0]
[R1-GigabitEthernet0/0/0]ip address 202.100.1.2 255.255.255.248
#
[R1-GigabitEthernet0/0/0]interface GigabitEthernet0/0/1
[R1-GigabitEthernet0/0/1]ip address 104.114.128.2 255.255.255.248
#
[R1-GigabitEthernet0/0/1]interface GigabitEthernet0/0/2.1
[R1-GigabitEthernet0/0/2.1]dot1q termination vid 10
[R1-GigabitEthernet0/0/2.1]ip address 192.168.10.1 255.255.255.0
[R1-GigabitEthernet0/0/2.1] arp broadcast enable
#
[R1-GigabitEthernet0/0/2.1]interface GigabitEthernet0/0/2.2
[R1-GigabitEthernet0/0/2.2]dot1q termination vid 20
[R1-GigabitEthernet0/0/2.2]ip address 192.168.20.1 255.255.255.0
[R1-GigabitEthernet0/0/2.2]arp broadcast enable
#
[R1]ip route-static 0.0.0.0 0.0.0.0 202.100.1.1
[R1]ip route-static 0.0.0.0 0.0.0.0 104.114.128.1
[ISP1]interface GigabitEthernet0/0/0
[ISP1-GigabitEthernet0/0/0] ip address 202.100.1.1 255.255.255.248
#
[ISP1]ip route-static 0.0.0.0 0.0.0.0 202.100.1.2
[ISP2]interface GigabitEthernet0/0/0
[ISP2-GigabitEthernet0/0/0]ip address 104.114.128.1 255.255.255.248
#
[ISP2]ip route-static 0.0.0.0 0.0.0.0 104.114.128.2
TIPS:如果设备上没有命中下一跳IP地址对应的ARP表项,设备会触发ARP学习,如果一直学习不到ARP,则报文按原始转发路径转发,重定向不生效。
[R1]ping 202.100.1.1
PING 202.100.1.1: 56 data bytes, press CTRL_C to break
Reply from 202.100.1.1: bytes=56 Sequence=1 ttl=255 time=40 ms
Reply from 202.100.1.1: bytes=56 Sequence=2 ttl=255 time=20 ms
Reply from 202.100.1.1: bytes=56 Sequence=3 ttl=255 time=30 ms
Reply from 202.100.1.1: bytes=56 Sequence=4 ttl=255 time=30 ms
Reply from 202.100.1.1: bytes=56 Sequence=5 ttl=255 time=30 ms
--- 202.100.1.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 20/30/40 ms
[R1]ping 104.114.128.1
PING 104.114.128.1: 56 data bytes, press CTRL_C to break
Reply from 104.114.128.1: bytes=56 Sequence=1 ttl=255 time=30 ms
Reply from 104.114.128.1: bytes=56 Sequence=2 ttl=255 time=20 ms
Reply from 104.114.128.1: bytes=56 Sequence=3 ttl=255 time=20 ms
Reply from 104.114.128.1: bytes=56 Sequence=4 ttl=255 time=10 ms
Reply from 104.114.128.1: bytes=56 Sequence=5 ttl=255 time=30 ms
--- 104.114.128.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 10/22/30 ms
[R1]display arp all
IP ADDRESS MAC ADDRESS EXPIRE(M) TYPE INTERFACE VPN-INSTANCE
VLAN/CEVLAN PVC
------------------------------------------------------------------------------
202.100.1.2 00e0-fc32-2036 I - GE0/0/0
202.100.1.1 00e0-fc78-6477 19 D-0 GE0/0/0
104.114.128.2 00e0-fc32-2037 I - GE0/0/1
104.114.128.1 00e0-fcc5-13c9 20 D-0 GE0/0/1
192.168.10.1 00e0-fc32-2038 I - GE0/0/2.1
192.168.10.10 5489-984a-4326 16 D-0 GE0/0/2.1
10/-
192.168.20.1 00e0-fc32-2038 I - GE0/0/2.2
------------------------------------------------------------------------------
Total:7 Dynamic:3 Static:0 Interface:4
二、配置ACL访问控制列表,匹配192.168.10.0和192.168.20.0的流量(需要注意先把内网互访的数据流放行)
[R1]acl 3000
[R1-acl-adv-3000]
[R1-acl-adv-3000]rule 5 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
[R1-acl-adv-3000]rule 10 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
[R1-acl-adv-3000]acl number 3101
[R1-acl-adv-3101]rule 5 permit ip source 192.168.10.0 0.0.0.255
#
[R1-acl-adv-3101]acl number 3102
[R1-acl-adv-3102] rule 5 permit ip source 192.168.20.0 0.0.0.255
三、配置流分类,使设备可以对报文进行区分
[R1]traffic classifier c2 operator or
[R1-classifier-c2] if-match acl 3102
#
[R1-classifier-c2]traffic classifier c0 operator or
[R1-classifier-c0] if-match acl 3000
#
[R1-classifier-c0]traffic classifier c1 operator or
[R1-classifier-c1] if-match acl 3101
四、配置流行为,满足不同ACL规则的数据流走不同的链路
[R1]traffic behavior b0
[R1-behavior-b0]permit
#
[R1-behavior-b0]traffic behavior b1
[R1-behavior-b1] redirect ip-nexthop 202.100.1.1
#
[R1-behavior-b1]traffic behavior b2
[R1-behavior-b2] redirect ip-nexthop 104.114.128.1
五、配置流策略,绑定流分类和流行为,应用到接口
[R1]traffic policy p1
[R1-trafficpolicy-p1]classifier c0 behavior b0
[R1-trafficpolicy-p1] classifier c1 behavior b1
[R1-trafficpolicy-p1] classifier c2 behavior b2
#
[R1-GigabitEthernet0/0/2]
[R1-GigabitEthernet0/0/2] traffic-policy p1 inbound
六、配置动态NAT,实现内网对外网的转换
[R1]nat address-group 0 202.100.1.3 202.100.1.5
[R1]nat address-group 1 104.114.1.3 104.114.1.5
#
[R1]interface GigabitEthernet0/0/0
[R1-GigabitEthernet0/0/0] nat outbound 2000 address-group 0 no-pat
#
[R1-GigabitEthernet0/0/0]interface GigabitEthernet0/0/1
[R1-GigabitEthernet0/0/1] nat outbound 2001 address-group 1 no-pat
#路由黑洞(可选)
[R1]ip route-static 202.100.1.3 32 NULL 0
[R1]ip route-static 202.100.1.4 32 NULL 0
[R1]ip route-static 202.100.1.5 32 NULL 0
[R1]ip route-static 104.114.1.3 32 NULL 0
[R1]ip route-static 104.114.1.4 32 NULL 0
[R1]ip route-static 104.114.1.5 32 NULL 0
项目验证:
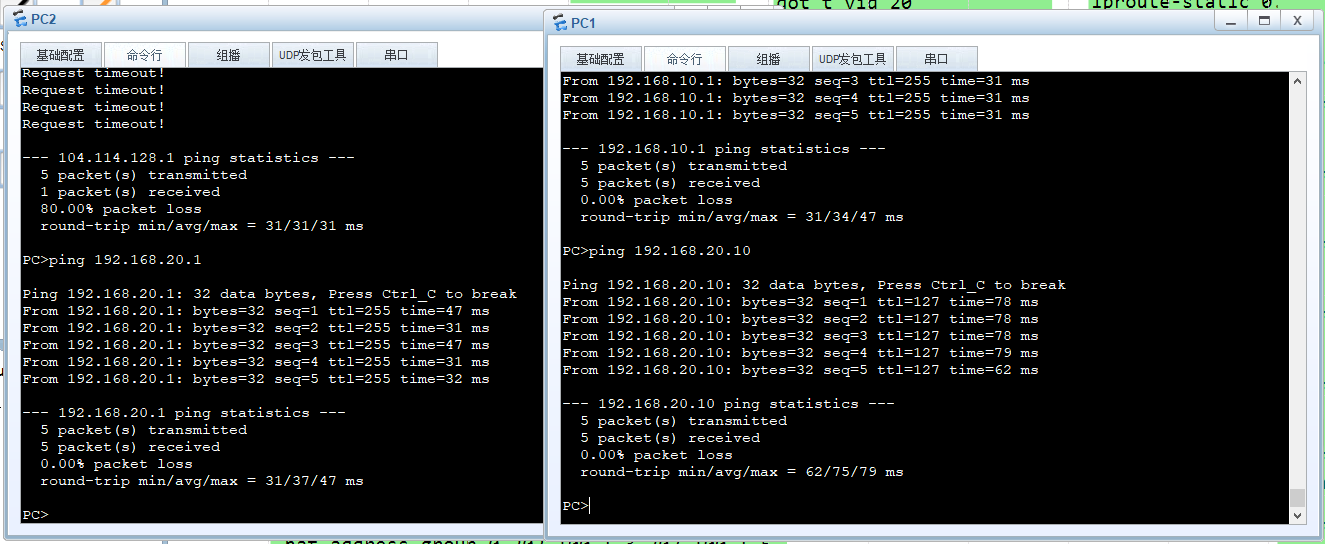
验证单臂路由:
验证流行为:
[R1]display traffic classifier user-defined
User Defined Classifier Information:
Classifier: c2
Operator: OR
Rule(s) :
if-match acl 3102
Classifier: c0
Operator: OR
Rule(s) :
if-match acl 3000
Classifier: c1
Operator: OR
Rule(s) :
if-match acl 3101
验证流分类:
[R1]display traffic behavior user-defined
User Defined Behavior Information:
Behavior: b2
Redirect:
Redirect ip-nexthop 104.114.128.1
Behavior: b0
Behavior: b1
Redirect:
Redirect ip-nexthop 202.100.1.1
statistic: enable
验证流策略:
[R1]dis traffic policy user-defined
User Defined Traffic Policy Information:
Policy: p1
Classifier: c0
Operator: OR
Behavior: b0
Classifier: c1
Operator: OR
Behavior: b1
Redirect:
Redirect ip-nexthop 202.100.1.1
statistic: enable
Classifier: c2
Operator: OR
Behavior: b2
Redirect:
Redirect ip-nexthop 104.114.128.1
[R1]traffic behavior b1
[R1-behavior-b1]statistic enable
#
[R1]traffic behavior b2
[R1-behavior-b2]statistic enable
#
[R1]display traffic policy statistics interface GigabitEthernet 0/0/2 inbound
Interface: GigabitEthernet0/0/2
Traffic policy inbound: p1
Rule number: 4
Current status: OK!
Item Sum(Packets/Bytes) Rate(pps/bps)
-------------------------------------------------------------------------------
Matched 5/ 0/
510 0
+--Passed 5/ 0/
510 0
+--Dropped 0/ 0/
0 0
+--Filter 0/ 0/
0 0
+--CAR 0/ 0/
0 0
+--Queue Matched 0/ 0/
0 0
+--Enqueued 0/ 0/
0 0
+--Discarded 0/ 0/
0 0
+--Car 0/ 0/
0 0
+--Green packets 0/ 0/
0 0
+--Yellow packets 0/ 0/
0 0
+--Red packets 0/ 0/
0 0
[R1]
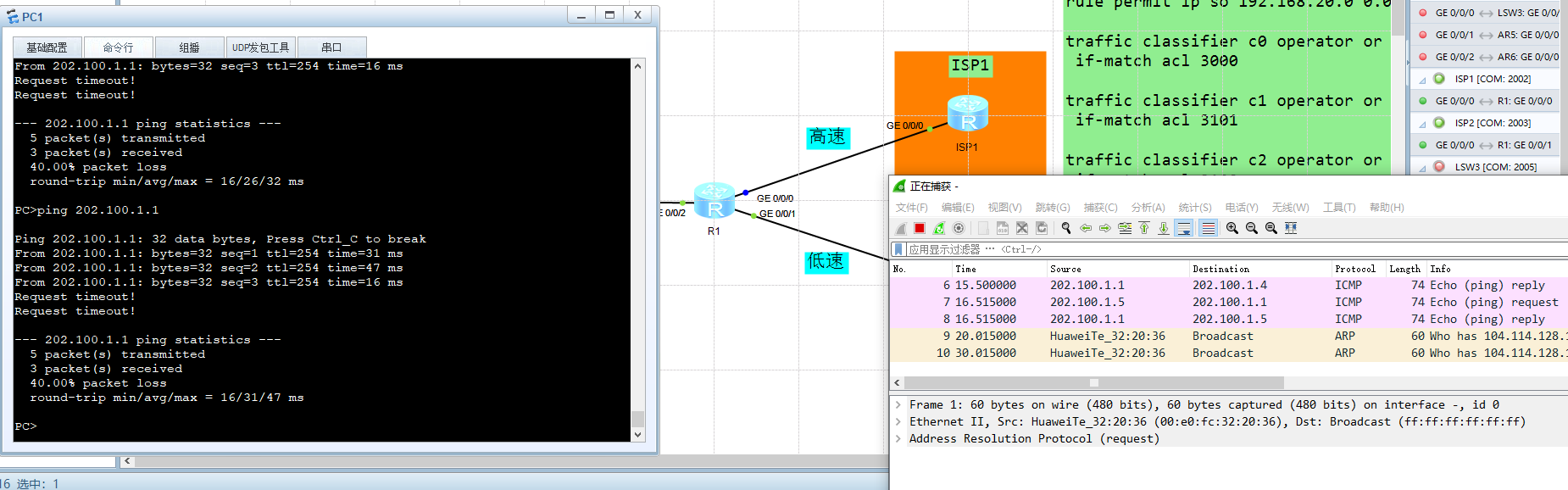
PC1流策略验证:抓包验证流量走向
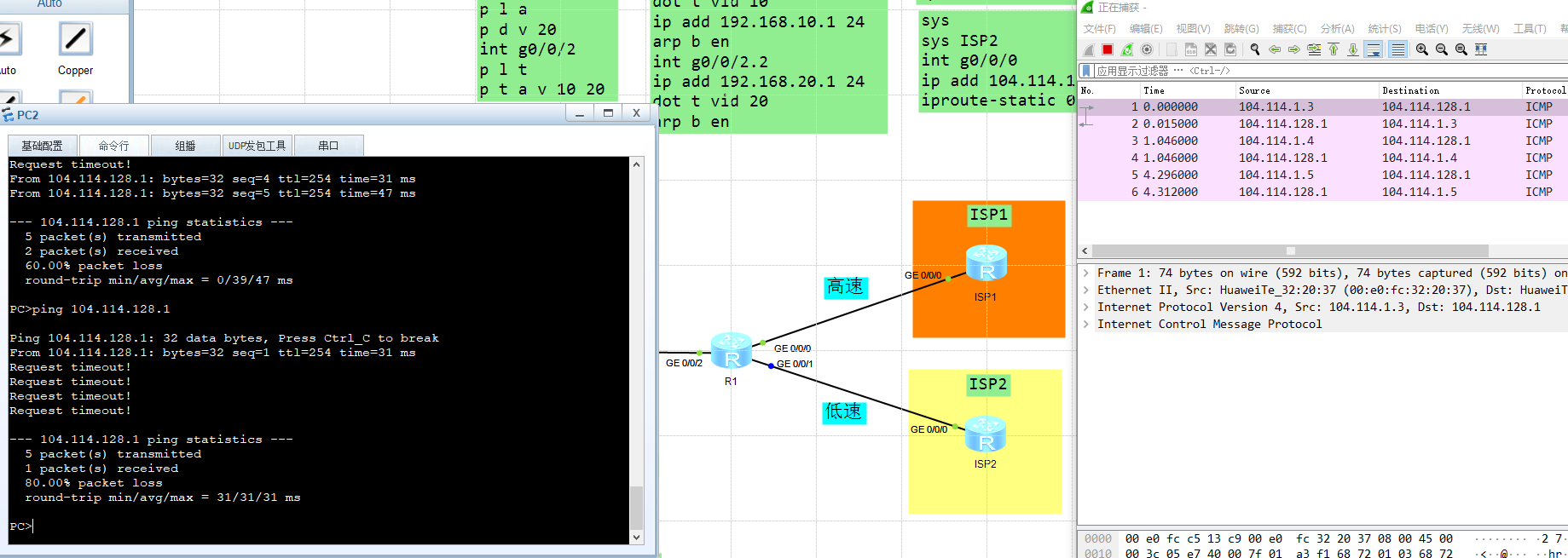
PC2流策略验证:抓包验证流量走向
相关参考链接:
[1] :https://support.huawei.com/enterprise/zh/doc/EDOC1000069579/a8457dec


 浙公网安备 33010602011771号
浙公网安备 33010602011771号