【转载】OpenSSL自建CA和签发二级CA及颁发SSL证书
自己签发CA证书再签发服务器证书的场景非常简单。把根CA证书导入到浏览器后,就可以信任由这个根CA直接签发的服务器证书。
但是实际上网站使用的证书肯定都不是由根CA直接签发的,比如
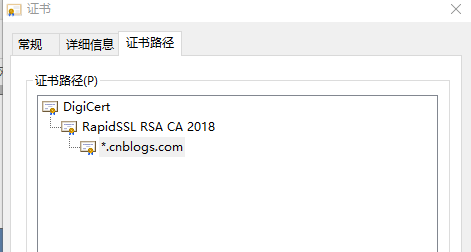
像这种,网站使用的证书就是由二级CA颁发的证书。
本文就来演示,自签CA,由自签CA签发二级CA,最后由二级CA签发网站证书
一:创建根CA
1:依次创建如下目录
mkdir -p /opt/ca/root
mkdir /opt/ca/root/key
2:vim /opt/ca/root/openssl.cnf
[ ca ] default_ca = CA_default [ CA_default ] dir = /opt/ca/root certs = $dir/certs crl_dir = $dir/crl database = $dir/index.txt new_certs_dir = $dir/newcerts certificate = $dir/key/cacert.crt serial = $dir/serial crlnumber = $dir/crlnumber crl = $dir/crl.pem private_key = $dir/key/cakey.pem RANDFILE = $dir/key/.rand unique_subject = no x509_extensions = usr_cert copy_extensions = copy name_opt = ca_default cert_opt = ca_default default_days = 365 default_crl_days= 30 default_md = sha256 preserve = no policy = policy_ca [ policy_ca ] countryName = supplied stateOrProvinceName = supplied organizationName = supplied organizationalUnitName = supplied commonName = supplied emailAddress = optional [ req ] default_bits = 2048 default_keyfile = privkey.pem distinguished_name = req_distinguished_name attributes = req_attributes x509_extensions = v3_ca string_mask = utf8only utf8 = yes prompt = no [ req_distinguished_name ] countryName = CN stateOrProvinceName = beijing localityName = beijing organizationName = Global Google CA Inc organizationalUnitName = Root CA commonName = Global Google Root CA [ usr_cert ] basicConstraints = CA:TRUE [ v3_ca ] basicConstraints = CA:TRUE [ req_attributes ]
3:创建如下目录及文件
mkdir /opt/ca/root/newcerts
touch /opt/ca/root/index.txt
touch /opt/ca/root/index.txt.attr
echo 01 > /opt/ca/root/serial
4:创建根CA私钥
openssl genrsa -out /opt/ca/root/key/cakey.pem 2048
5:创建根CA证书请求文件
openssl req -new -key /opt/ca/root/key/cakey.pem -out /opt/ca/root/key/ca.csr -config /opt/ca/root/openssl.cnf
6:自签根CA证书
openssl ca -selfsign -in /opt/ca/root/key/ca.csr -out /opt/ca/root/key/cacert.crt -config /opt/ca/root/openssl.cnf
7:查看证书信息(可选)
openssl x509 -text -in /opt/ca/root/key/cacert.crt
经过以上几个步骤,就生成了根CA的相关证书和私钥,可以用于签发其他的CA(二级CA),不可签发服务器证书
二:创建二级CA
1:依次创建如下目录
mkdir /opt/ca/agent
mkdir /opt/ca/agent/key
2:vim /opt/ca/agent/openssl.cnf
[ ca ] default_ca = CA_default [ CA_default ] dir = /opt/ca/agent certs = $dir/certs crl_dir = $dir/crl database = $dir/index.txt new_certs_dir = $dir/newcerts certificate = $dir/key/cacert.crt serial = $dir/serial crlnumber = $dir/crlnumber crl = $dir/crl.pem private_key = $dir/key/cakey.pem RANDFILE = $dir/key/.rand unique_subject = no x509_extensions = usr_cert copy_extensions = copy name_opt = ca_default cert_opt = ca_default default_days = 365 default_crl_days= 30 default_md = sha256 preserve = no policy = policy_ca [ policy_ca ] countryName = supplied stateOrProvinceName = supplied organizationName = supplied organizationalUnitName = supplied commonName = supplied emailAddress = optional [ req ] default_bits = 2048 default_keyfile = privkey.pem distinguished_name = req_distinguished_name attributes = req_attributes x509_extensions = v3_ca string_mask = utf8only utf8 = yes prompt = no [ req_distinguished_name ] countryName = CN stateOrProvinceName = Guangdong localityName = Guangzhou organizationName = Global Google CA Inc organizationalUnitName = Google 2019 CA commonName = Google 2019 CA [ usr_cert ] basicConstraints = CA:FALSE [ v3_ca ] basicConstraints = CA:TRUE [ req_attributes ]
3:创建如下目录及文件
mkdir /opt/ca/agent/newcerts
touch /opt/ca/agent/index.txt
touch /opt/ca/agent/index.txt.attr
echo 01 > /opt/ca/agent/serial
4:创建二级CA私钥
openssl genrsa -out /opt/ca/agent/key/cakey.pem 2048
5:创建二级CA证书请求文件
openssl req -new -key /opt/ca/agent/key/cakey.pem -out /opt/ca/agent/key/ca.csr -config /opt/ca/agent/openssl.cnf
6:使用根CA签发二级CA
openssl ca -in /opt/ca/agent/key/ca.csr -out /opt/ca/agent/key/cacert.crt -config /opt/ca/root/openssl.cnf
7:查看证书信息(可选)
openssl x509 -text -in /opt/ca/agent/key/cacert.crt
经过以上几个步骤,就生成了一个二级CA,这个二级CA可以签发服务器证书(不能签发其他的CA)
三:使用二级CA签发服务器端证书
1:mkdir /opt/ca/taobao
2:vim /opt/ca/taobao/openssl.cnf
[ req ] prompt = no distinguished_name = server_distinguished_name req_extensions = req_ext x509_extensions = v3_req attributes = req_attributes [ server_distinguished_name ] commonName = taobao2018.cn stateOrProvinceName = zhejiang countryName = CN organizationName = Alibaba Taobao Inc organizationalUnitName = Taobao IT [ v3_req ] basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment [ req_attributes ] [ req_ext ] subjectAltName = @alternate_names [ alternate_names ] DNS.1 = taobao2018.cn DNS.2 = bbs.taobao2018.cn DNS.3 = taobao2019.cn
3:生成网站私钥
openssl genrsa -out /opt/ca/taobao/privkey.pem 2048
4:生成证书请求文件(csr文件)
openssl req -new -key /opt/ca/taobao/privkey.pem -out /opt/ca/taobao/taobao.csr -config /opt/ca/taobao/openssl.cnf
5:使用二级CA进行签发证书(这里不能用根CA签发)
openssl ca -in /opt/ca/taobao/taobao.csr -out /opt/ca/taobao/taobao.crt -config /opt/ca/agent/openssl.cnf
6:聚合证书(重要)
由于是二级CA颁发的证书,所以,服务器需要把根CA、二级CA等证书都要发送给浏览器,所以给到web服务器的证书是要一个聚合的证书
cat /opt/ca/taobao/taobao.crt /opt/ca/agent/key/cacert.crt /opt/ca/root/key/cacert.crt | tee /opt/ca/taobao/taobao_all.crt
PS:注意顺序
7:查看证书信息(可选)
openssl x509 -text -in /opt/ca/taobao/taobao_all.crt
经过以上几个步骤,就生成了由二级CA签发的证书了
注意:
一:
CA和证书是有区别的,CA是用来颁发证书和签发二级CA的,且两者是互斥的。也就是说,一个CA要么是用来签发二级CA的,要么是用来签发证书的。
如何判断?
在 /opt/ca/root/openssl.cnf配置文件中,有如下配置
[ usr_cert ] basicConstraints = CA:TRUE [ v3_ca ] basicConstraints = CA:TRUE
usr_cert下面的basicConstraints代表的是当前CA的配置,
CA:TRUE是当前CA签发的是CA(二级CA),不能签发证书,
CA:FALSE是当前CA签发的是证书,不能签发CA(二级CA)
v3_ca下面的basicConstraints代表的是请求的证书是CA还是证书
CA:TRUE表示当前请求的是CA(二级CA)
CA:FALSE表示当前请求的是证书
二:
如果是CA(二级CA),则证书请求中的commonName不需要填写域名,可以填写组织机构
如果是证书,则证书请求中的commonName需要填写域名(一般是主域名),当然了,这个主域名也要在后面的subjectAltName属性中
转自:https://blog.csdn.net/mn960mn/article/details/85645805


