Java中使用OpenSSL生成的RSA公私钥进行数据加解密
参考自:https://www.cnblogs.com/yaowen/p/9226566.html
:https://www.cnblogs.com/wjqhuaxia/p/13829680.html
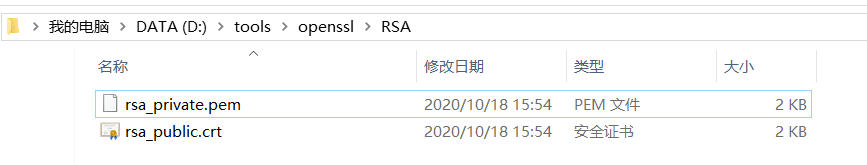
1.使用openssl生成RSA私钥及证书
生成 RSA 私钥和自签名证书,命令如下:
openssl req -newkey rsa:2048 -nodes -keyout rsa_private.pem -x509 -days 365 -out cert.crt
req是证书请求的子命令,-newkey rsa:2048 -keyout rsa_private.pem 表示生成私钥(PKCS8格式),-nodes 表示私钥不加密,若不带参数将提示输入密码;
-x509表示输出证书,-days365 为有效期,此后根据提示输入证书拥有者信息;
至此,可用的密钥对已经生成好了,私钥使用rsa_private.pem,公钥证书采用cert.crt。
说明:
如果生成的私钥文件是PKCS#1格式的,则在使用时需在java中进行相应处理。不能直接使用。
RSAPrivateKeyStructure asn1PrivKey = new RSAPrivateKeyStructure((ASN1Sequence) ASN1Sequence.fromByteArray(priKeyData));
RSAPrivateKeySpec rsaPrivKeySpec = new RSAPrivateKeySpec(asn1PrivKey.getModulus(), asn1PrivKey.getPrivateExponent());
KeyFactory keyFactory= KeyFactory.getInstance("RSA");
PrivateKey priKey= keyFactory.generatePrivate(rsaPrivKeySpec);
首先将PKCS#1的私钥文件读取出来(注意去掉减号开头的注释内容),然后使用Base64解码读出的字符串,便得到priKeyData,也就是第一行代码中的参数。最后一行得到了私钥。接下来的用法就没什么区别了。
2.使用java代码进行加密解
2.1 RSA加密解密类
import java.io.BufferedReader;
import java.io.BufferedWriter;
import java.io.FileInputStream;
import java.io.FileReader;
import java.io.FileWriter;
import java.io.IOException;
import java.security.InvalidKeyException;
import java.security.KeyFactory;
import java.security.KeyPair;
import java.security.KeyPairGenerator;
import java.security.NoSuchAlgorithmException;
import java.security.PublicKey;
import java.security.SecureRandom;
import java.security.cert.CertificateFactory;
import java.security.cert.X509Certificate;
import java.security.interfaces.RSAPrivateKey;
import java.security.interfaces.RSAPublicKey;
import java.security.spec.InvalidKeySpecException;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
import java.util.Base64;
import javax.crypto.BadPaddingException;
import javax.crypto.Cipher;
import javax.crypto.IllegalBlockSizeException;
import javax.crypto.NoSuchPaddingException;
public class RSAEncrypt {
/**
* 字节数据转字符串专用集合
*/
private static final char[] HEX_CHAR = { '0', '1', '2', '3', '4', '5', '6',
'7', '8', '9', 'a', 'b', 'c', 'd', 'e', 'f' };
/**
* 随机生成密钥对
*/
public static void genKeyPair(String filePath) {
// KeyPairGenerator类用于生成公钥和私钥对,基于RSA算法生成对象
KeyPairGenerator keyPairGen = null;
try {
keyPairGen = KeyPairGenerator.getInstance("RSA");
} catch (NoSuchAlgorithmException e) {
e.printStackTrace();
}
// 初始化密钥对生成器,密钥大小为96-1024位
keyPairGen.initialize(1024,new SecureRandom());
// 生成一个密钥对,保存在keyPair中
KeyPair keyPair = keyPairGen.generateKeyPair();
// 得到私钥
RSAPrivateKey privateKey = (RSAPrivateKey) keyPair.getPrivate();
// 得到公钥
RSAPublicKey publicKey = (RSAPublicKey) keyPair.getPublic();
try {
// 得到公钥字符串
String publicKeyString = new String(Base64.getEncoder().encodeToString(publicKey.getEncoded()));
// 得到私钥字符串
String privateKeyString = new String(Base64.getEncoder().encodeToString(privateKey.getEncoded()));
// 将密钥对写入到文件
FileWriter pubfw = new FileWriter(filePath + "/publicKey.keystore");
FileWriter prifw = new FileWriter(filePath + "/privateKey.keystore");
BufferedWriter pubbw = new BufferedWriter(pubfw);
BufferedWriter pribw = new BufferedWriter(prifw);
pubbw.write(publicKeyString);
pribw.write(privateKeyString);
pubbw.flush();
pubbw.close();
pubfw.close();
pribw.flush();
pribw.close();
prifw.close();
} catch (Exception e) {
e.printStackTrace();
}
}
/**
* 从文件中输入流中加载公钥
*
* @param in
* 公钥输入流
* @throws Exception
* 加载公钥时产生的异常
*/
public static String loadPublicKeyByFile(String path) throws Exception {
try {
BufferedReader br = new BufferedReader(new FileReader(path
+ "/rsa_public.crt"));
String readLine = null;
StringBuilder sb = new StringBuilder();
while ((readLine = br.readLine()) != null) {
sb.append(readLine);
}
br.close();
return sb.toString();
} catch (IOException e) {
throw new Exception("公钥数据流读取错误");
} catch (NullPointerException e) {
throw new Exception("公钥输入流为空");
}
}
/**
* 从字符串中加载公钥
*
* @param publicKeyStr
* 公钥数据字符串
* @throws Exception
* 加载公钥时产生的异常
*/
public static RSAPublicKey loadPublicKeyByStr(String publicKeyStr)
throws Exception {
try {
byte[] buffer = Base64.getDecoder().decode(publicKeyStr);
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
X509EncodedKeySpec keySpec = new X509EncodedKeySpec(buffer);
return (RSAPublicKey) keyFactory.generatePublic(keySpec);
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此算法");
} catch (InvalidKeySpecException e) {
throw new Exception("公钥非法");
} catch (NullPointerException e) {
throw new Exception("公钥数据为空");
}
}
/**
* 获取证书公钥
* @param cerPath
* @return
* @throws Exception
*/
public static String getPublicKey(String cerPath) throws Exception {
CertificateFactory certificatefactory = CertificateFactory.getInstance("X.509");
FileInputStream fis = new FileInputStream(cerPath);
X509Certificate Cert = (X509Certificate) certificatefactory.generateCertificate(fis);
PublicKey pk = Cert.getPublicKey();
String publicKey = Base64.getEncoder().encodeToString(pk.getEncoded());
return publicKey;
}
/**
* 从文件中加载私钥
*
* @param keyFileName
* 私钥文件名
* @return 是否成功
* @throws Exception
*/
public static String loadPrivateKeyByFile(String path) throws Exception {
try {
BufferedReader br = new BufferedReader(new FileReader(path
+ "/rsa_private.pem"));
String readLine = null;
StringBuilder sb = new StringBuilder();
while ((readLine = br.readLine()) != null) {
sb.append(readLine);
}
br.close();
return sb.toString();
} catch (IOException e) {
throw new Exception("私钥数据读取错误");
} catch (NullPointerException e) {
throw new Exception("私钥输入流为空");
}
}
public static RSAPrivateKey loadPrivateKeyByStr(String privateKeyStr)
throws Exception {
try {
byte[] buffer = Base64.getDecoder().decode(privateKeyStr);
PKCS8EncodedKeySpec keySpec = new PKCS8EncodedKeySpec(buffer);
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
return (RSAPrivateKey) keyFactory.generatePrivate(keySpec);
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此算法");
} catch (InvalidKeySpecException e) {
throw new Exception("私钥非法");
} catch (NullPointerException e) {
throw new Exception("私钥数据为空");
}
}
/**
* 公钥加密过程
*
* @param publicKey
* 公钥
* @param plainTextData
* 明文数据
* @return
* @throws Exception
* 加密过程中的异常信息
*/
public static byte[] encrypt(RSAPublicKey publicKey, byte[] plainTextData)
throws Exception {
if (publicKey == null) {
throw new Exception("加密公钥为空, 请设置");
}
Cipher cipher = null;
try {
// 使用默认RSA
cipher = Cipher.getInstance("RSA");
// cipher= Cipher.getInstance("RSA", new BouncyCastleProvider());
cipher.init(Cipher.ENCRYPT_MODE, publicKey);
byte[] output = cipher.doFinal(plainTextData);
return output;
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此加密算法");
} catch (NoSuchPaddingException e) {
e.printStackTrace();
return null;
} catch (InvalidKeyException e) {
throw new Exception("加密公钥非法,请检查");
} catch (IllegalBlockSizeException e) {
throw new Exception("明文长度非法");
} catch (BadPaddingException e) {
throw new Exception("明文数据已损坏");
}
}
/**
* 私钥加密过程
*
* @param privateKey
* 私钥
* @param plainTextData
* 明文数据
* @return
* @throws Exception
* 加密过程中的异常信息
*/
public static byte[] encrypt(RSAPrivateKey privateKey, byte[] plainTextData)
throws Exception {
if (privateKey == null) {
throw new Exception("加密私钥为空, 请设置");
}
Cipher cipher = null;
try {
// 使用默认RSA
cipher = Cipher.getInstance("RSA");
cipher.init(Cipher.ENCRYPT_MODE, privateKey);
byte[] output = cipher.doFinal(plainTextData);
return output;
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此加密算法");
} catch (NoSuchPaddingException e) {
e.printStackTrace();
return null;
} catch (InvalidKeyException e) {
throw new Exception("加密私钥非法,请检查");
} catch (IllegalBlockSizeException e) {
throw new Exception("明文长度非法");
} catch (BadPaddingException e) {
throw new Exception("明文数据已损坏");
}
}
/**
* 私钥解密过程
*
* @param privateKey
* 私钥
* @param cipherData
* 密文数据
* @return 明文
* @throws Exception
* 解密过程中的异常信息
*/
public static byte[] decrypt(RSAPrivateKey privateKey, byte[] cipherData)
throws Exception {
if (privateKey == null) {
throw new Exception("解密私钥为空, 请设置");
}
Cipher cipher = null;
try {
// 使用默认RSA
cipher = Cipher.getInstance("RSA");
// cipher= Cipher.getInstance("RSA", new BouncyCastleProvider());
cipher.init(Cipher.DECRYPT_MODE, privateKey);
byte[] output = cipher.doFinal(cipherData);
return output;
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此解密算法");
} catch (NoSuchPaddingException e) {
e.printStackTrace();
return null;
} catch (InvalidKeyException e) {
throw new Exception("解密私钥非法,请检查");
} catch (IllegalBlockSizeException e) {
throw new Exception("密文长度非法");
} catch (BadPaddingException e) {
throw new Exception("密文数据已损坏");
}
}
/**
* 公钥解密过程
*
* @param publicKey
* 公钥
* @param cipherData
* 密文数据
* @return 明文
* @throws Exception
* 解密过程中的异常信息
*/
public static byte[] decrypt(RSAPublicKey publicKey, byte[] cipherData)
throws Exception {
if (publicKey == null) {
throw new Exception("解密公钥为空, 请设置");
}
Cipher cipher = null;
try {
// 使用默认RSA
cipher = Cipher.getInstance("RSA");
// cipher= Cipher.getInstance("RSA", new BouncyCastleProvider());
cipher.init(Cipher.DECRYPT_MODE, publicKey);
byte[] output = cipher.doFinal(cipherData);
return output;
} catch (NoSuchAlgorithmException e) {
throw new Exception("无此解密算法");
} catch (NoSuchPaddingException e) {
e.printStackTrace();
return null;
} catch (InvalidKeyException e) {
throw new Exception("解密公钥非法,请检查");
} catch (IllegalBlockSizeException e) {
throw new Exception("密文长度非法");
} catch (BadPaddingException e) {
throw new Exception("密文数据已损坏");
}
}
/**
* 字节数据转十六进制字符串
*
* @param data
* 输入数据
* @return 十六进制内容
*/
public static String byteArrayToString(byte[] data) {
StringBuilder stringBuilder = new StringBuilder();
for (int i = 0; i < data.length; i++) {
// 取出字节的高四位 作为索引得到相应的十六进制标识符 注意无符号右移
stringBuilder.append(HEX_CHAR[(data[i] & 0xf0) >>> 4]);
// 取出字节的低四位 作为索引得到相应的十六进制标识符
stringBuilder.append(HEX_CHAR[(data[i] & 0x0f)]);
if (i < data.length - 1) {
stringBuilder.append(' ');
}
}
return stringBuilder.toString();
}
}
2.2 签名及校验类
package cn.com.wjqhuaxia;
import java.security.KeyFactory;
import java.security.PrivateKey;
import java.security.PublicKey;
import java.security.spec.PKCS8EncodedKeySpec;
import java.security.spec.X509EncodedKeySpec;
import java.util.Base64;
/**
* RSA签名验签类
*/
public class RSASignature {
/**
* 签名算法
*/
public static final String SIGN_ALGORITHMS = "SHA1WithRSA";
/**
* RSA签名
*
* @param content
* 待签名数据
* @param privateKey
* 商户私钥
* @param encode
* 字符集编码
* @return 签名值
*/
public static String sign(String content, String privateKey, String encode) {
try {
PKCS8EncodedKeySpec priPKCS8 = new PKCS8EncodedKeySpec(Base64.getDecoder().decode(privateKey));
KeyFactory keyf = KeyFactory.getInstance("RSA");
PrivateKey priKey = keyf.generatePrivate(priPKCS8);
java.security.Signature signature = java.security.Signature.getInstance(SIGN_ALGORITHMS);
signature.initSign(priKey);
signature.update(content.getBytes(encode));
byte[] signed = signature.sign();
return new String(Base64.getEncoder().encodeToString(signed));
} catch (Exception e) {
e.printStackTrace();
}
return null;
}
public static String sign(String content, String privateKey) {
try {
PKCS8EncodedKeySpec priPKCS8 = new PKCS8EncodedKeySpec(Base64.getDecoder().decode(privateKey));
KeyFactory keyf = KeyFactory.getInstance("RSA");
PrivateKey priKey = keyf.generatePrivate(priPKCS8);
java.security.Signature signature = java.security.Signature.getInstance(SIGN_ALGORITHMS);
signature.initSign(priKey);
signature.update(content.getBytes());
byte[] signed = signature.sign();
return new String(Base64.getEncoder().encode(signed));
} catch (Exception e) {
e.printStackTrace();
}
return null;
}
/**
* RSA验签名检查
*
* @param content
* 待签名数据
* @param sign
* 签名值
* @param publicKey
* 分配给开发商公钥
* @param encode
* 字符集编码
* @return 布尔值
*/
public static boolean doCheck(String content, String sign, String publicKey, String encode) {
try {
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
byte[] encodedKey = Base64.getDecoder().decode(publicKey);
PublicKey pubKey = keyFactory.generatePublic(new X509EncodedKeySpec(encodedKey));
java.security.Signature signature = java.security.Signature.getInstance(SIGN_ALGORITHMS);
signature.initVerify(pubKey);
signature.update(content.getBytes(encode));
boolean bverify = signature.verify(Base64.getDecoder().decode(sign));
return bverify;
} catch (Exception e) {
e.printStackTrace();
}
return false;
}
public static boolean doCheck(String content, String sign, String publicKey) {
try {
KeyFactory keyFactory = KeyFactory.getInstance("RSA");
byte[] encodedKey = Base64.getDecoder().decode(publicKey);
PublicKey pubKey = keyFactory.generatePublic(new X509EncodedKeySpec(encodedKey));
java.security.Signature signature = java.security.Signature.getInstance(SIGN_ALGORITHMS);
signature.initVerify(pubKey);
signature.update(content.getBytes());
boolean bverify = signature.verify(Base64.getDecoder().decode(sign));
return bverify;
} catch (Exception e) {
e.printStackTrace();
}
return false;
}
}
2.3 测试类
package cn.com.wjqhuaxia;
import java.util.Base64;
public class MainTest {
public static final String PRIVATE_KEY_FILE = "D:/tools/openssl/RSA/rsa_private.pem";
//公钥文件路径
// public static final String PUBLIC_KEY_FILE = RSAUtil.class.getClassLoader().getResource("").getPath() + "rsa_private.key";
public static final String PUBLIC_KEY_FILE = "D:/tools/openssl/RSA/rsa_public.crt";
public static void main(String[] args) throws Exception {
// RSAEncrypt.genKeyPair(filepath);
String filepath = "D:/tools/openssl/RSA/";
System.out.println("--------------公钥加密私钥解密过程-------------------");
// 公钥
String publicKeyString = RSAEncrypt.getPublicKey(PUBLIC_KEY_FILE);
// 私钥
// String loadPrivateKeyByFile = RSAEncrypt.loadPrivateKeyByFile(filepath); //获取私钥
String privateKeyString = "MIIEvgIBADANBgkqhkiG9w0BAQEFAASCBKgwggSkAgEAAoIBAQC3Vs7ndTzw9lS+3KijEY26RistYbOx0qNTlrq49vDg+2fVQurNh41uzeIdjwKZfpe9Gtsy7ZRzGv+3EH5rK8Bo+rPteBGKt2tjsZAcaR78RZ8PVOmozJYX2aZqpirPf/vSLhB/vaKeyJpvp6WQG6gLSbZRgFzb+vACgE2m7Pt9rD2pNjPowEsPf6jcqQ19I7FY9TtYRU4ypRR4MXFJw6pLfrIfof/TPpgXdp5AaQ8OaPmxsOsiYHG3Nvv0HWLRYtq/JYhQrh8bCOklPI/jdusxvXpTBfJLrQmruVfRJ3HyqXuY1R4/IP2iyZdPdnncnqKPr8UdOk9SDB9CR32dH2V7AgMBAAECggEAJwOH/+UI1NX2bq8SC7FekXcBFSUnUf3a15zJmzahR574F3+n65ie1idlqJiYGwW/UHR4lLvNzTi/lbsiy7eBuFUxGKVmRjiF168fVYxhFZnTITYWit8OSYD9UtCNZ556fd1jkWtPQa66fmwUZTgdaFmFPI6uM/mQPVgELjNbyQATZ7i9rZKUuDhT5QwWjn+uk/qcsv80gDjHCesdrzfwbWbnlPMFLY8f7rKOyTnwuBIR07UqagiLrHdli8NpWw6viNymdxmqgteiG4LBXERdV3/vA0Zr+naX4rGpmgMum77mbyKqFZ8Q3j4MYVCA29SVH9OeYJRUJqIy8hnKU5faIQKBgQDv8Cn/ng5xHiI9emDDryIDmZmDZaswkL2Wm010ccgcoyMzYUiHmHRUYy47yrk0VVlqnJObZlUSHNTrTkamjMqXrIF4Q69ndXDVRoF8VXzmJvYuSEeClg0YvkLSQV87dZu6DI7R0ucIrrGY/hXIxNSmzZIbDuDTBexvK3puy6bxKQKBgQDDnLPY1Xca6QMHpWTlIHWsEJ58szNKsJpMNsxHQT7tozrW0iBztAw13d6fs3Yt4LJF4XpNqBd1GSuVKRtnrClXT1xf3pZZbo7999OfFQMht6xp53kZYYE0toMJEt6039uHgQUvFXPOv3eVLvYcU1kJXwzrXWqd+3V1DItoOc5CAwKBgQDiPA89qGhxnDoowZUvrZhi0JeA34I0vqUktranjwlihygPsDDVOZimYQYc9p7+i2NONOiw5CJee7T/UcUoESSNMui43wkqgf+r+VjqRSkJUb9aEGjs5lLe+7bBzUXgKJp3KJQZn8Sb2Sw314vuzDi+NqMGxFaUYsd2YwaEJZ35UQKBgQC8rCyb/GlBP3Z4rYK/ratSJ0V2qbHTXLu2vzQRllEIDOT3xv0eHI+adUIBb6uRXKUW2gCJXpQhkgGDgX65ZEkLubQzlBIYeJbbR2qKik3W+74E+ArJ/E4Pdeq1mcnNVA3+iOdjHqHwzKSe9AjWEV5Tt6ZSbmwjrSMBnvPnt7nF2QKBgAS0/YHxPU4QDsb6PqoGJ64utjgmqrqDAjp4OgCpdtP9gJqKYSi60b54NF50JKnpxVunq8+kOp38LsDdp+9RdD8+xvPMPFM3wGRHhnFvbd1ZnwSjsCj7bw1ARSHldQ2N3aUhtSyCjj0Gdc1jDquORMTGGgUA0jQ2/blTFw+WRE9b";
String plainText = "ihep_公钥加密私钥解密";
System.out.println("原文:" + plainText);
// 公钥加密过程
byte[] cipherData = RSAEncrypt.encrypt(RSAEncrypt.loadPublicKeyByStr(publicKeyString),
plainText.getBytes());
String cipher = new String(Base64.getEncoder().encode(cipherData));
System.out.println("加密:" + cipher);
// 私钥解密过程
byte[] res = RSAEncrypt.decrypt(RSAEncrypt.loadPrivateKeyByStr(privateKeyString),
Base64.getDecoder().decode(cipher));
String restr = new String(res);
System.out.println("解密:" + restr);
System.out.println();
System.out.println("--------------私钥加密公钥解密过程-------------------");
plainText = "ihep_私钥加密公钥解密";
// 私钥加密过程
cipherData = RSAEncrypt.encrypt(RSAEncrypt.loadPrivateKeyByStr(privateKeyString),
plainText.getBytes());
cipher = new String(Base64.getEncoder().encode(cipherData));
// 公钥解密过程
res = RSAEncrypt.decrypt(RSAEncrypt.loadPublicKeyByStr(publicKeyString),
Base64.getDecoder().decode(cipher));
restr = new String(res);
System.out.println("原文:" + plainText);
System.out.println("加密:" + cipher);
System.out.println("解密:" + restr);
System.out.println();
System.out.println("---------------私钥签名过程------------------");
String content = "ihep_这是用于签名的原始数据";
String signstr = RSASignature.sign(content, privateKeyString);
System.out.println("签名原串:" + content);
System.out.println("签名串:" + signstr);
System.out.println();
System.out.println("---------------公钥校验签名------------------");
System.out.println("签名原串:" + content);
System.out.println("签名串:" + signstr);
System.out.println("验签结果:" + RSASignature.doCheck(content, signstr, publicKeyString));
System.out.println();
}
}
使用到的maven配置如下:
<dependencies>
<!-- https://mvnrepository.com/artifact/commons-codec/commons-codec -->
<dependency>
<groupId>commons-codec</groupId>
<artifactId>commons-codec</artifactId>
<version>1.10</version>
</dependency>
<dependency>
<groupId>org.bouncycastle</groupId>
<artifactId>bcprov-jdk15on</artifactId>
<version>1.56</version>
</dependency>
</dependencies>