用wireshark查看 tcpdump 抓取的mysql交互数据
用tcpdump 抓取 mysql客户端与服务器端的交互
1开启tcpdump
tcpdump -i eth0 -s 3000 port 3306 -w ~/sql.pcap
先故意输入一个错误的密码
[root@localhost ~]# mysql -h192.168.100.206 -uroot -p Enter password: ERROR 1045 (28000): Access denied for user 'root'@'192.168.11.201' (using password: YES)
输入正确的密码进入并进行一系列操作
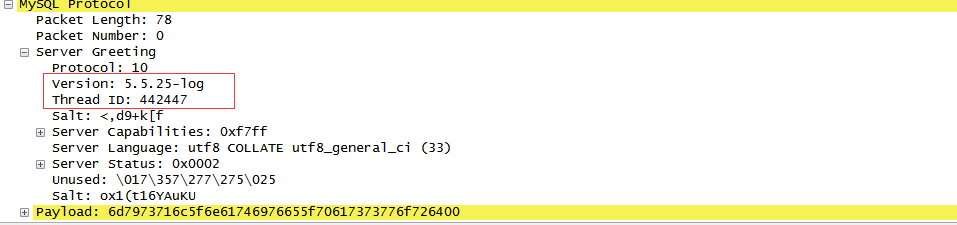
[root@localhost ~]# mysql -h192.168.100.206 -uroot -p Enter password: Welcome to the MySQL monitor. Commands end with ; or \g. Your MySQL connection id is 442447 Server version: 5.5.25-log Source distribution Copyright (c) 2000, 2013, Oracle and/or its affiliates. All rights reserved. Oracle is a registered trademark of Oracle Corporation and/or its affiliates. Other names may be trademarks of their respective owners. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. mysql> use jwbx; Database changed mysql> select * from jwbx_customer limit 10;
用wireshark 打开sql.pcap 文件
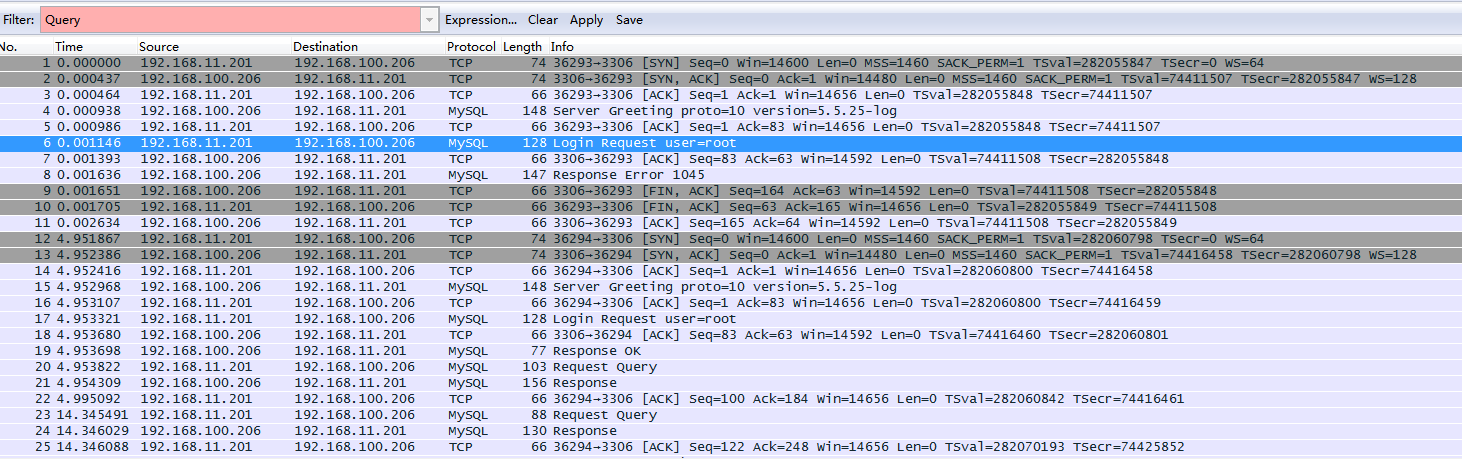
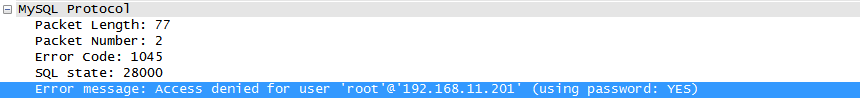
输入的错误密码
Request 6 0.001146 192.168.11.201 192.168.100.206 MySQL 128 Login Request user=root
Response 8 0.001636 192.168.100.206 192.168.11.201 MySQL 147 Response Error 1045
登陆成功
17 4.953321 192.168.11.201 192.168.100.206 MySQL 128 Login Request user=root
来自服务器端的问候
15 4.952968 192.168.100.206 192.168.11.201 MySQL 148 Server Greeting proto=10 version=5.5.25-log
服务器端的状态
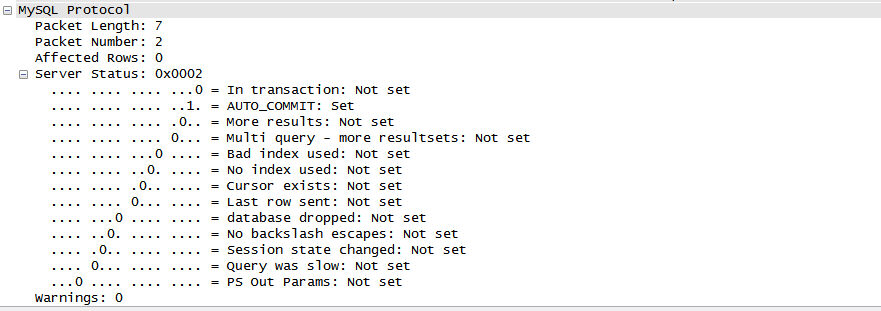
访问
select @@version_comment limit 1 返回 Source distribution
SELECT DATABASE()
USE DataBase 返回数据库名
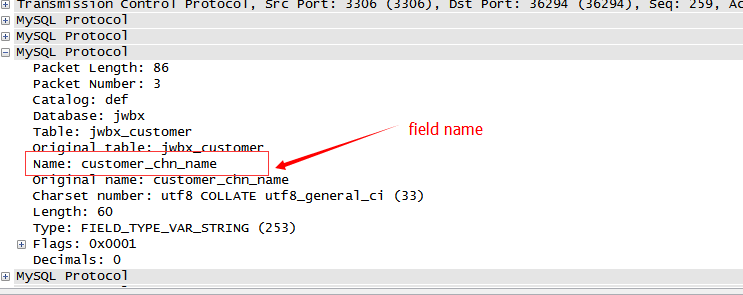
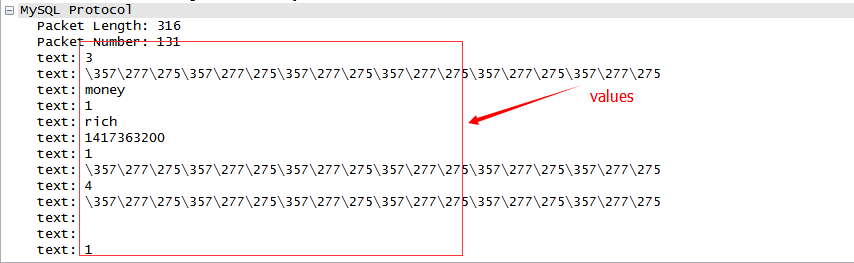
访问的sql
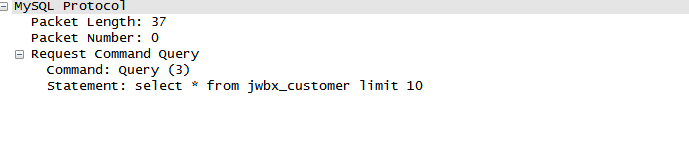
Return
同样可以在抓取程序访问mysql的数据,可以查看执行了哪些sql语句
也可以不用wireshark 方式如下:
#tcpdump -i any -A -s 3000 port 3306 >~/sql.log
#grep "select * from " ~/sql.log|head
备注:-A 以ASCII格式打印出所有分组,并将链路层的头最小化。向mysql服务端传输的sql语句就是以ASCII码形式进行传输。我们就可以使用-A参数查看传输的具体sql语句。



 浙公网安备 33010602011771号
浙公网安备 33010602011771号