RSA(共模、低指数、素数分解、模不互质)
buuctf:rsa3
题目
c1=22322035275663237041646893770451933509324701913484303338076210603542612758956262869640822486470121149424485571361007421293675516338822195280313794991136048140918842471219840263536338886250492682739436410013436651161720725855484866690084788721349555662019879081501113222996123305533009325964377798892703161521852805956811219563883312896330156298621674684353919547558127920925706842808914762199011054955816534977675267395009575347820387073483928425066536361482774892370969520740304287456555508933372782327506569010772537497541764311429052216291198932092617792645253901478910801592878203564861118912045464959832566051361 n=22708078815885011462462049064339185898712439277226831073457888403129378547350292420267016551819052430779004755846649044001024141485283286483130702616057274698473611149508798869706347501931583117632710700787228016480127677393649929530416598686027354216422565934459015161927613607902831542857977859612596282353679327773303727004407262197231586324599181983572622404590354084541788062262164510140605868122410388090174420147752408554129789760902300898046273909007852818474030770699647647363015102118956737673941354217692696044969695308506436573142565573487583507037356944848039864382339216266670673567488871508925311154801 e1=11187289 c2=18702010045187015556548691642394982835669262147230212731309938675226458555210425972429418449273410535387985931036711854265623905066805665751803269106880746769003478900791099590239513925449748814075904017471585572848473556490565450062664706449128415834787961947266259789785962922238701134079720414228414066193071495304612341052987455615930023536823801499269773357186087452747500840640419365011554421183037505653461286732740983702740822671148045619497667184586123657285604061875653909567822328914065337797733444640351518775487649819978262363617265797982843179630888729407238496650987720428708217115257989007867331698397 e2=9647291
这是共模攻击。当使用相同的模数,不同的公钥加密同一个明文时即存在共模攻击。
c1 = me1 mod n
c2 = me2 mod n
根据扩展欧几里得算法,求出满足ae1+be2=1的a和b,下列共模关系成立:
c1ac2b ≡ mae1 mbe2
≡ m(ae1+be2)
≡ m (mod n)
即可求出明文m = c1ac2bmod n = ((c1a mod n) * (c2b mod n)) mod n。
使用sagemath计算结果
g, a, b = xgcd(e1, e2)
message = (power_mod(c1,a,n) * power_mod(c2, b, n)) % n
h=hex(message)
asc = [chr(int(h[i:i+2], 16)) for i in range(2, len(h), 2)]
"".join(asc)
buuctf:RSAROLL
获得n、e和一堆密文。先素数分解出p和q,求出d后即可求出明文
编写python脚本get.py
#!/usr/bin/env python3
cipher = [704796792,
752211152,
274704164,
18414022,
368270835,
483295235,
263072905,
459788476,
483295235,
459788476,
663551792,
475206804,
459788476,
428313374,
475206804,
459788476,
425392137,
704796792,
458265677,
341524652,
483295235,
534149509,
425392137,
428313374,
425392137,
341524652,
458265677,
263072905,
483295235,
828509797,
341524652,
425392137,
475206804,
428313374,
483295235,
475206804,
459788476,
306220148]
e = 19
n = 920139713
p = factor(n)[0][0]
q = factor(n)[1][0]
d = inverse_mod(19,(p-1)*(q-1))
message = ""
for c in cipher:
m = power_mod(c, d, n)
message += chr(m)
print(message)
在sagemath执行get.py
load("get.py")
![]()
buuctf:Dangerous Rsa
题目
#n: 0x52d483c27cd806550fbe0e37a61af2e7cf5e0efb723dfc81174c918a27627779b21fa3c851e9e94188eaee3d5cd6f752406a43fbecb53e80836ff1e185d3ccd7782ea846c2e91a7b0808986666e0bdadbfb7bdd65670a589a4d2478e9adcafe97c6ee23614bcb2ecc23580f4d2e3cc1ecfec25c50da4bc754dde6c8bfd8d1fc16956c74d8e9196046a01dc9f3024e11461c294f29d7421140732fedacac97b8fe50999117d27943c953f18c4ff4f8c258d839764078d4b6ef6e8591e0ff5563b31a39e6374d0d41c8c46921c25e5904a817ef8e39e5c9b71225a83269693e0b7e3218fc5e5a1e8412ba16e588b3d6ac536dce39fcdfce81eec79979ea6872793L #e: 0x3 #c:0x10652cdfaa6b63f6d7bd1109da08181e500e5643f5b240a9024bfa84d5f2cac9310562978347bb232d63e7289283871efab83d84ff5a7b64a94a79d34cfbd4ef121723ba1f663e514f83f6f01492b4e13e1bb4296d96ea5a353d3bf2edd2f449c03c4a3e995237985a596908adc741f32365 so,how to get the message?
低加密指数攻击,当e很小时:
由c = me mod n
得 m = (nk + c)1/e
爆破k,如果m为整数就是明文
python脚本
import gmpy2
N = 0x52d483c27cd806550fbe0e37a61af2e7cf5e0efb723dfc81174c918a27627779b21fa3c851e9e94188eaee3d5cd6f752406a43fbecb53e80836ff1e185d3ccd7782ea846c2e91a7b0808986666e0bdadbfb7bdd65670a589a4d2478e9adcafe97c6ee23614bcb2ecc23580f4d2e3cc1ecfec25c50da4bc754dde6c8bfd8d1fc16956c74d8e9196046a01dc9f3024e11461c294f29d7421140732fedacac97b8fe50999117d27943c953f18c4ff4f8c258d839764078d4b6ef6e8591e0ff5563b31a39e6374d0d41c8c46921c25e5904a817ef8e39e5c9b71225a83269693e0b7e3218fc5e5a1e8412ba16e588b3d6ac536dce39fcdfce81eec79979ea6872793
e = 0x3
c = 0x10652cdfaa6b63f6d7bd1109da08181e500e5643f5b240a9024bfa84d5f2cac9310562978347bb232d63e7289283871efab83d84ff5a7b64a94a79d34cfbd4ef121723ba1f663e514f83f6f01492b4e13e1bb4296d96ea5a353d3bf2edd2f449c03c4a3e995237985a596908adc741f32365
for k in range(100000):
res, flag = gmpy2.iroot(c + k*N, 3)
if flag:
res_hex = hex(res)
asc = [chr(int(res_hex[i:i+2], 16)) for i in range(2, len(res_hex), 2)]
print("".join(asc))
break
buuctf:rsa5
已知e,一堆n和c


如果找到两个模数不互质,通过欧几里得算法可快速进行素数分解得到p、q
ls = [n1,n2,n3,n4,n5,n6,n7,n8,n9,n10,n11,n12,n13,n14,n15,n16,n17,n18,n19,n20]
for i in range(len(ls)):
for j in range(i+1,len(ls)):
p = gcd(ls[i], ls[j])
if p != 1:
print(f'\n{i}\n{j}\n{p}\n')
break
sagemath执行,得到两个不互质的模数是n5、n18
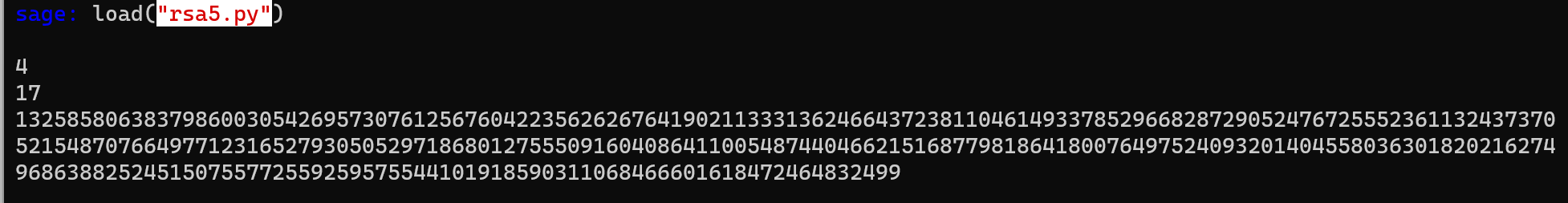
计算出q

sagemath由n18、c18、e、p、q,计算出明文
power_mod(c18, inverse_mod(65537, (p-1)*(q-1)), n18)


 浙公网安备 33010602011771号
浙公网安备 33010602011771号