Error系列-CVE CIS-2023系统漏洞处理方案集合
问题1: CVE-2023-29491
- Type: OS
- 涉及到的包:ncurses-dev,ncurses-libs,ncurses-terminfo-base
- 描述:当前系统安装的ncurses,存在漏洞,当被setuid应用程序使用时,允许本地用户通过在$HOME/中找到的终端数据库文件中的畸形数据触发与安全相关的内存损坏。或通过terminfo或TERM环境变量到达。
解决方案:
升级包到最新版本或者优化稳定版本,如果你和我一样是写dockerfile来进行升级,就需要根据镜像中存在的命令来执行升级
例如我的包是基于nodejs14版本,所以我使用apk命令来进行更新,代码如下:
FROM node:16.14.2-alpine as build
USER root
WORKDIR /app
COPY package.json .npmrc ./
RUN yarn install
COPY . ./
RUN yarn run build
FROM nginx:stable-alpine
COPY --from=build /app/dist/ /usr/share/nginx/html
# 下面这行就是解决方案
RUN apk upgrade ncurses-dev ncurses-libs ncurses-terminfo-base
EXPOSE 80
CMD ["nginx", "-g", "daemon off;"]
如果上述代码没有解决问题,简单粗暴解决方案:
# 下面这行就是解决方案
RUN apk update && apk upgrade
EXPOSE 80
CMD ["nginx", "-g", "daemon off;"]
问题2: (CIS_Docker_v1.2.0 - 4.1) Image should be created with a non-root user 或者遇到 /var/run/nginx.pid" failed (13: Permission denied)也一样可以采用此方案解决
- Type: CIS
- 描述:当前镜像是使用默认root用户创建的,为保证安全,应该用非root用户创建
解决过程遇到的一些阻碍和收获
调试准备
- 准备好dockerfile
- 在dockerfile所在项目目录下运行命令build
- 等待构建成功后,运行构建的镜像
可参考指令如下:
docker build -t web-test01:v1 .| tee web-test07.build.log
docker run -d -p 8890:80 web-test01:v1
作为一名前端,我遇到了这个问题,刚开始的思路就是去网上搜索答案尝试解决问题,在这个过程中,做了很多尝试,但是某些尝试没有起作用,也许是我的用法不对,所以我把它写下来,希望路过的小伙伴如果有理解为何有些写法不起作用的话,不吝赐教哇,如果有着急看最终解决方案的小伙伴请直接往下拉,最下面是最终解决方案
尝试1:创建非root用户,使用/etc/sudoers给非root用户添加权限,失败告终
/etc/sudoers 的简单介绍:
- sudo的权限控制可以在/etc/sudoers文件中查看到
- 如果想要控制某个用户(或某个组用户)只能执行root权限中的一部分命令, 或者允许某些用户使用sudo时不需要输入密码
- 格式一般都是 root ALL=(ALL) ALL
在dockerfile中我添加了如下代码,尝试了各种写法,均不起作用,请原谅我完全不懂这个东西,我今天晚上写完这篇文章就去学习一下linux基础操作,Ծ‸Ծ
# ...此处省略一些基础代码
RUN adduser -D appuser
# 写法1
RUN echo "appuser ALL=(ALL) ALL" >> /etc/sudoers
# 写法2
# RUN echo 'appuser ALL=(ALL:ALL) ALL' >> /etc/sudoers # ^^ # tab
# 写法3
# RUN echo "appuser ALL=(root) NOPASSWD:HOSTS,HOST" >> /etc/sudoers;
# 写法4
# RUN echo "appuser ALL=(ALL) NOPASSWD: /usr/sbin/reboot,/use/sbin/useradd,/use/sbin/userdel " >> /etc/sudoers
USER appuse
EXPOSE 80
CMD ["nginx", "-g", "daemon off;"]
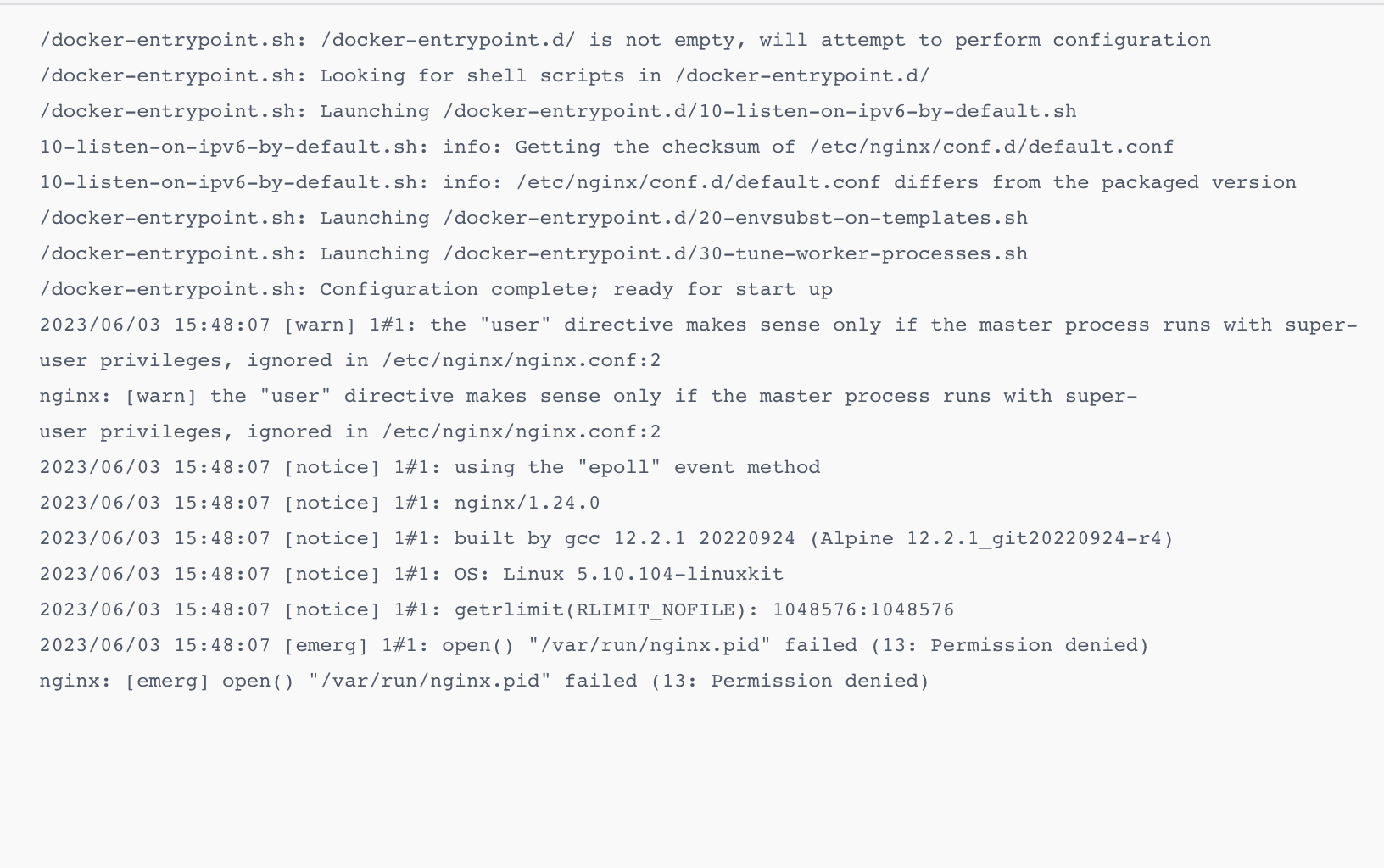
但是镜像build后,运行的时候还是会很多权限方面的报错,例如
2023/06/03 15:48:07 [emerg] 1#1: open() "/var/run/nginx.pid" failed (13: Permission denied)
nginx: [emerg] open() "/var/run/nginx.pid" failed (13: Permission denied)
尝试2: 在容器中装sudo, 在docker容器中使用非root用户修改/etc/hosts文件,失败告终
# ...此处省略一些基础代码
RUN adduser -D appuser
USER appuse
# 下面的代码没有起作用,请路过的小伙伴不吝赐教,/app/setup/hosts 是ip hostname 对应关系的文件
RUN apk add sudo
RUN sudo chmod 777 /etc/hosts;
RUN cat /app/setup/hosts >> /etc/hosts;
RUN sudo /bin/chmod 644 /etc/hosts;
EXPOSE 80
CMD ["nginx", "-g", "daemon off;"]
尝试3:先创建新用户,然后使用chown添加权限,部分失败告终
# ...此处省略一些基础代码
RUN adduser -D appuser
RUN chown -R appuser /var/cache
RUN chown -R appuser /etc/nginx
# 下面的/ var/run 代码没有起作用,请路过的小伙伴不吝赐教
RUN chown -R appuser /var/run
USER appuser
# RUN chmod -R 755 /etc/nginx
# RUN chmod -R 755 /var/cache
# RUN chmod -R 755 /var/run
EXPOSE 80
CMD ["nginx", "-g", "daemon off;"]
报错如下:
/docker-entrypoint.sh: /docker-entrypoint.d/ is not empty, will attempt to perform configuration
/docker-entrypoint.sh: Looking for shell scripts in /docker-entrypoint.d/
/docker-entrypoint.sh: Launching /docker-entrypoint.d/10-listen-on-ipv6-by-default.sh
10-listen-on-ipv6-by-default.sh: info: Getting the checksum of /etc/nginx/conf.d/default.conf
10-listen-on-ipv6-by-default.sh: info: /etc/nginx/conf.d/default.conf differs from the packaged version
/docker-entrypoint.sh: Launching /docker-entrypoint.d/20-envsubst-on-templates.sh
/docker-entrypoint.sh: Launching /docker-entrypoint.d/30-tune-worker-processes.sh
/docker-entrypoint.sh: Configuration complete; ready for start up
2023/06/03 15:48:07 [warn] 1#1: the "user" directive makes sense only if the master process runs with super-user privileges, ignored in /etc/nginx/nginx.conf:2
nginx: [warn] the "user" directive makes sense only if the master process runs with super-user privileges, ignored in /etc/nginx/nginx.conf:2
2023/06/03 15:48:07 [notice] 1#1: using the "epoll" event method
2023/06/03 15:48:07 [notice] 1#1: nginx/1.24.0
2023/06/03 15:48:07 [notice] 1#1: built by gcc 12.2.1 20220924 (Alpine 12.2.1_git20220924-r4)
2023/06/03 15:48:07 [notice] 1#1: OS: Linux 5.10.104-linuxkit
2023/06/03 15:48:07 [notice] 1#1: getrlimit(RLIMIT_NOFILE): 1048576:1048576
2023/06/03 15:48:07 [emerg] 1#1: open() "/var/run/nginx.pid" failed (13: Permission denied)
nginx: [emerg] open() "/var/run/nginx.pid" failed (13: Permission denied)
Search...
Stick to bottom
最终解决方案:
因为这个项目里有nginx,所以使用了nginx的自带用户,用户组来进行配置了权限,解决此问题
例如下面代码:
# ...此处省略一些基础代码
# 此处使用的是nginx自带的非root账号执行授权
RUN touch /var/run/nginx.pid \
# && chown -R nginx:nginx /app \
# && chmod -R 755 /app \
&& chown -R nginx:nginx /var/cache/nginx \
&& chown -R nginx:nginx /var/log/nginx \
&& chown -R nginx:nginx /etc/nginx/conf.d \
&& chown -R nginx:nginx /var/run/nginx.pid \
&& chown -R nginx:nginx /usr/share/nginx/html \
&& chown -R nginx:nginx /etc/nginx/nginx.conf
# 这部分代码是delete一些用不到的nginx包
RUN apk del nginx-module-image-filter \
&& apk del nginx-module-xslt \
&& apk del nginx-module-geoip \
&& apk del nginx-module-njs \
&& apk del curl
USER nginx
# 请注意,这里一般不要写80,非root用户容易没有权限绑定80端口
EXPOSE 8080
CMD ["nginx", "-g", "daemon off;"]
最终解决方案2:
dockerfile加入下面代码
RUN adduser -D xiaojin
USER xiaojin

k8s yaml 加入下面代码
securityContext:
runAsUser: 0

问题3:bind() to 0.0.0.0:80 failed (13: Permission denied)
XXXXXXXX pm2023/06/05 08:04:39 [warn] 1#1: the "user" directive makes sense only if the master process runs with super-user privileges, ignored in /etc/nginx/nginx.conf:2
XXXXXXXX pmnginx: [warn] the "user" directive makes sense only if the master process runs with super-user privileges, ignored in /etc/nginx/nginx.conf:2
Mon, Jun 5 2023 4:04:41 pm2023/06/05 08:04:39 [emerg] 1#1: bind() to 0.0.0.0:80 failed (13: Permission denied)
Mon, Jun 5 2023 4:04:41 pmnginx: [emerg] bind() to 0.0.0.0:80 failed (13: Permission denied)
问题分析:
某些情况下,非Root用户不能绑定1024以下端口,否则会报错:没有权限绑定该端口
问题解决:
- 修改Dockerfile中的端口配置
- nginx.conf中的端口监听
- k8s.yml中的服务端口暴露配置
- containerPort配置
所有你项目中nginx绑定的都要修改一遍哦~~
代码举例:



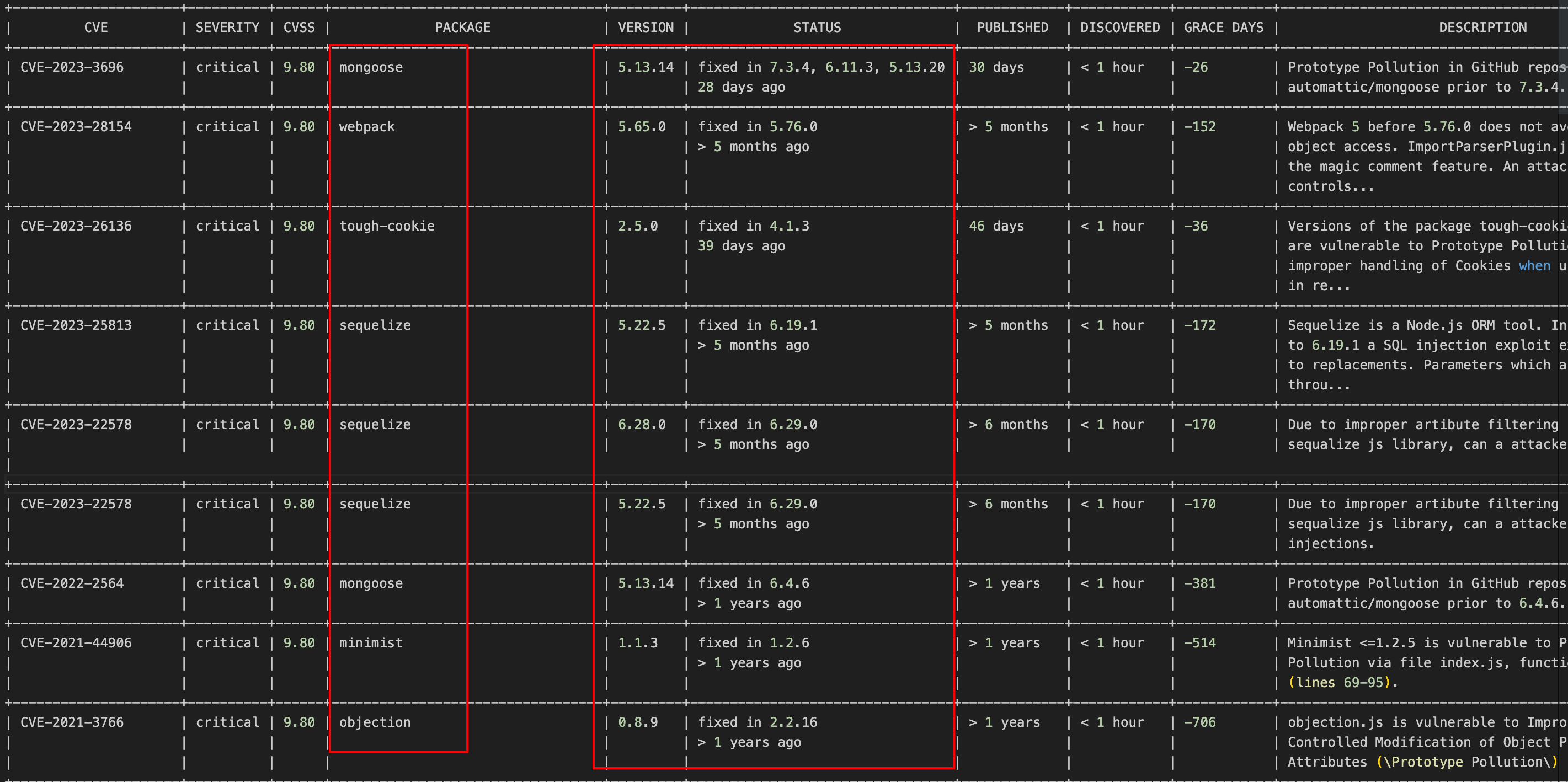
问题4:Twistlock扫描Type:javascript
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE | SEVERITY | CVSS | PACKAGE | VERSION | STATUS | PUBLISHED | DISCOVERED | GRACE DAYS | DESCRIPTION | TRIGGERED FAILURE |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-3696 | critical | 9.80 | mongoose | 5.13.14 | fixed in 7.3.4, 6.11.3, 5.13.20 | 30 days | < 1 hour | -26 | Prototype Pollution in GitHub repository | Yes |
| | | | | | 28 days ago | | | | automattic/mongoose prior to 7.3.4. | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-28154 | critical | 9.80 | webpack | 5.65.0 | fixed in 5.76.0 | > 5 months | < 1 hour | -152 | Webpack 5 before 5.76.0 does not avoid cross-realm | Yes |
| | | | | | > 5 months ago | | | | object access. ImportParserPlugin.js mishandles | |
| | | | | | | | | | the magic comment feature. An attacker who | |
| | | | | | | | | | controls... | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-26136 | critical | 9.80 | tough-cookie | 2.5.0 | fixed in 4.1.3 | 46 days | < 1 hour | -36 | Versions of the package tough-cookie before 4.1.3 | Yes |
| | | | | | 39 days ago | | | | are vulnerable to Prototype Pollution due to | |
| | | | | | | | | | improper handling of Cookies when using CookieJar | |
| | | | | | | | | | in re... | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-25813 | critical | 9.80 | sequelize | 5.22.5 | fixed in 6.19.1 | > 5 months | < 1 hour | -172 | Sequelize is a Node.js ORM tool. In versions prior | Yes |
| | | | | | > 5 months ago | | | | to 6.19.1 a SQL injection exploit exists related | |
| | | | | | | | | | to replacements. Parameters which are passed | |
| | | | | | | | | | throu... | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-22578 | critical | 9.80 | sequelize | 6.28.0 | fixed in 6.29.0 | > 6 months | < 1 hour | -170 | Due to improper artibute filtering in the | Yes |
| | | | | | > 5 months ago | | | | sequalize js library, can a attacker peform SQL | |
|
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2023-22578 | critical | 9.80 | sequelize | 5.22.5 | fixed in 6.29.0 | > 6 months | < 1 hour | -170 | Due to improper artibute filtering in the | Yes |
| | | | | | > 5 months ago | | | | sequalize js library, can a attacker peform SQL | |
| | | | | | | | | | injections. | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2022-2564 | critical | 9.80 | mongoose | 5.13.14 | fixed in 6.4.6 | > 1 years | < 1 hour | -381 | Prototype Pollution in GitHub repository | Yes |
| | | | | | > 1 years ago | | | | automattic/mongoose prior to 6.4.6. | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2021-44906 | critical | 9.80 | minimist | 1.1.3 | fixed in 1.2.6 | > 1 years | < 1 hour | -514 | Minimist <=1.2.5 is vulnerable to Prototype | Yes |
| | | | | | > 1 years ago | | | | Pollution via file index.js, function setKey() | |
| | | | | | | | | | (lines 69-95). | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
| CVE-2021-3766 | critical | 9.80 | objection | 0.8.9 | fixed in 2.2.16 | > 1 years | < 1 hour | -706 | objection.js is vulnerable to Improperly | Yes |
| | | | | | > 1 years ago | | | | Controlled Modification of Object Prototype | |
| | | | | | | | | | Attributes (\Prototype Pollution\) | |
+---------------------+----------+------+----------------------------------+---------+---------------------------------+-------------+------------+------------+----------------------------------------------------+-------------------+
解决方案
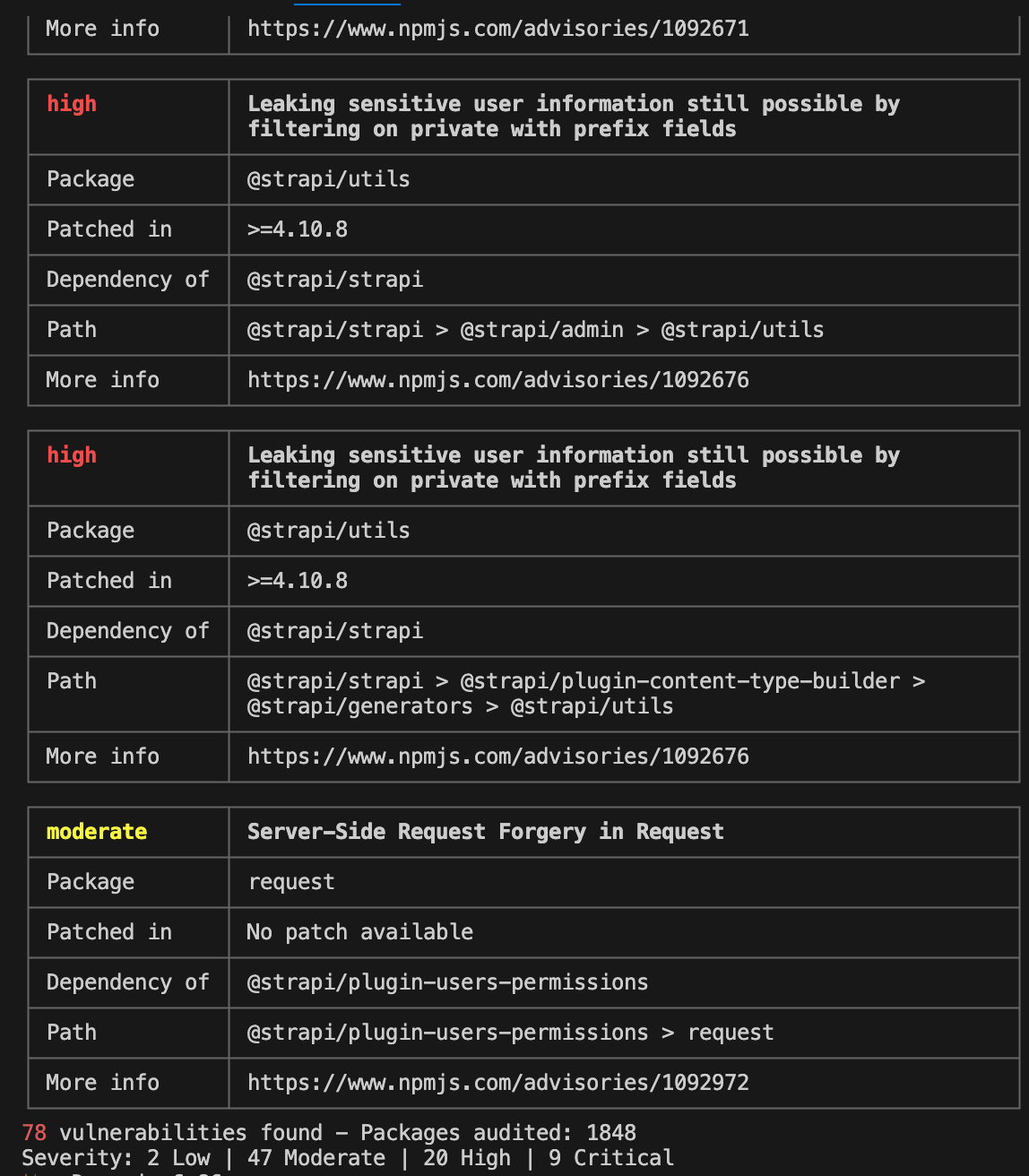
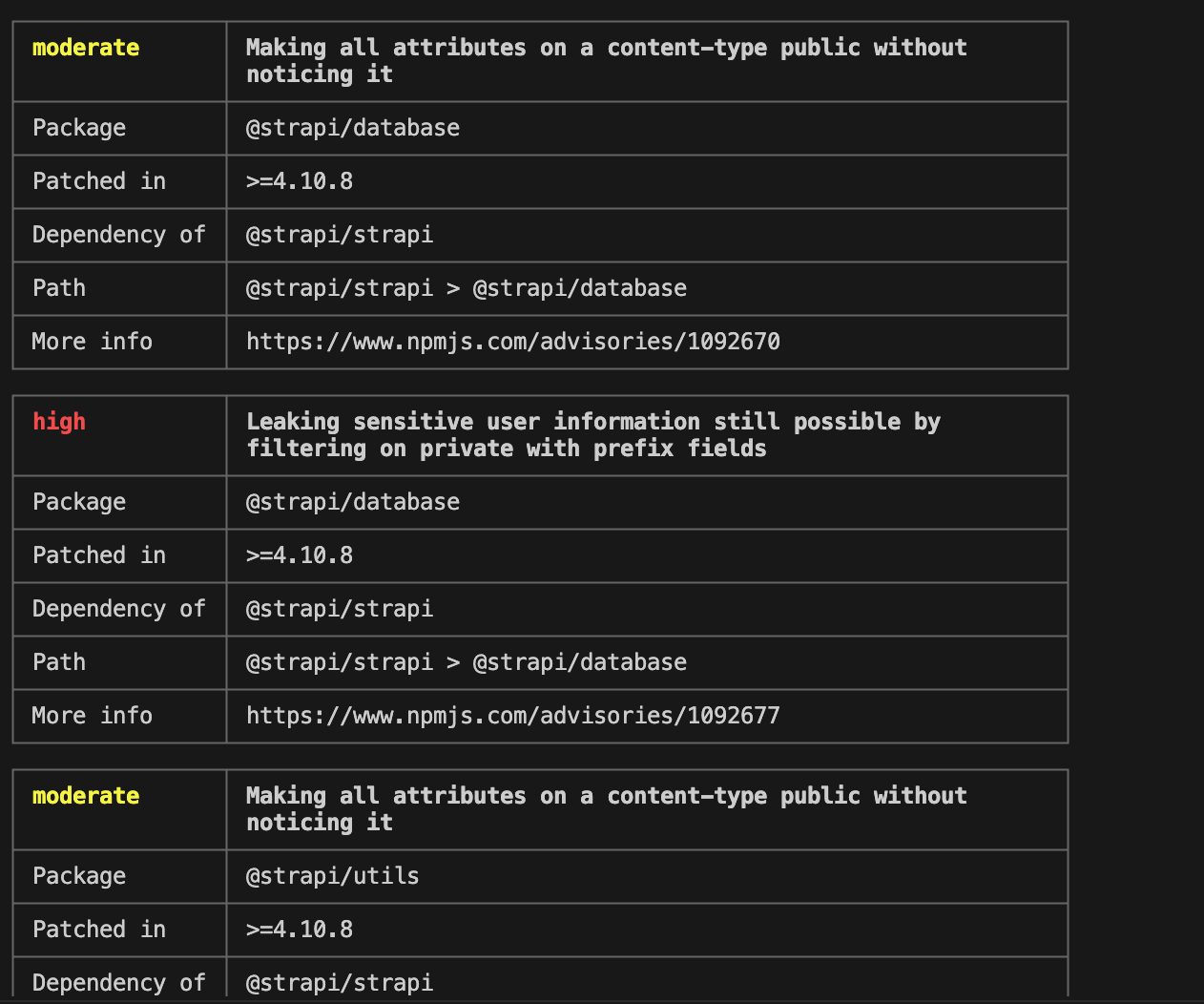
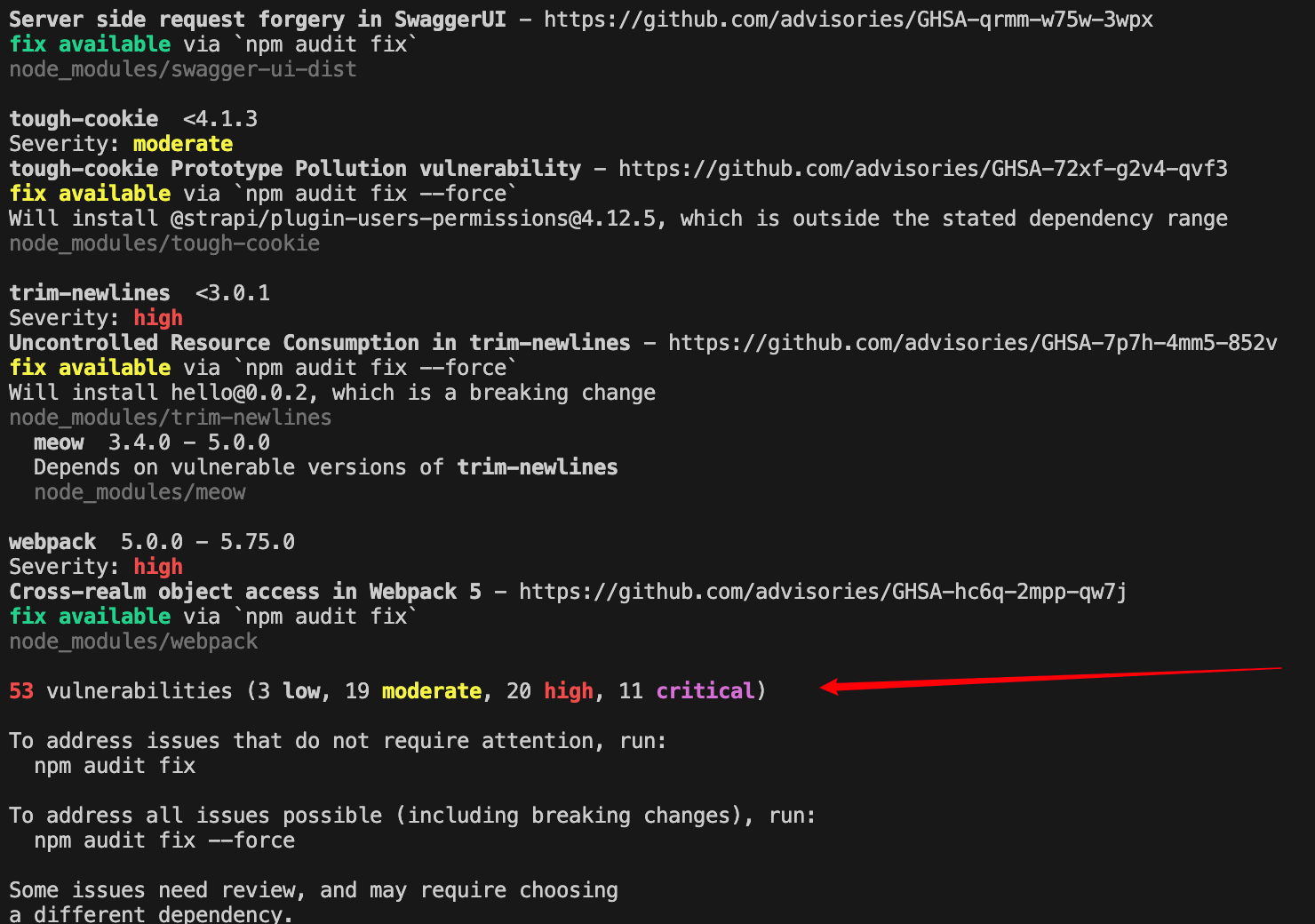
打开代码,如果我们在npm 源下,执行 npm audit,会展示该漏洞的信息
- npm audit 返回的漏洞数据来源于 Github Advisory Database
- 关于 npm audit 详细解释,可以打开我的这篇文档
npm audit
或
yarn audit
查看漏洞检查结果
┌───────────────┬──────────────────────────────────────────────────────────────┐
│ high │ Leaking sensitive user information still possible by │
│ │ filtering on private with prefix fields │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Package │ @strapi/utils │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Patched in │ >=4.10.8 │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Dependency of │ @strapi/strapi │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Path │ @strapi/strapi > @strapi/admin > @strapi/utils │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ More info │ https://www.npmjs.com/advisories/1092676 │
└───────────────┴──────────────────────────────────────────────────────────────┘
┌───────────────┬──────────────────────────────────────────────────────────────┐
│ high │ Leaking sensitive user information still possible by │
│ │ filtering on private with prefix fields │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Package │ @strapi/utils │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Patched in │ >=4.10.8 │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Dependency of │ @strapi/strapi │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Path │ @strapi/strapi > @strapi/plugin-content-type-builder > │
│ │ @strapi/generators > @strapi/utils │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ More info │ https://www.npmjs.com/advisories/1092676 │
└───────────────┴──────────────────────────────────────────────────────────────┘
┌───────────────┬──────────────────────────────────────────────────────────────┐
│ moderate │ Server-Side Request Forgery in Request │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Package │ request │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Patched in │ No patch available │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Dependency of │ @strapi/plugin-users-permissions │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ Path │ @strapi/plugin-users-permissions > request │
├───────────────┼──────────────────────────────────────────────────────────────┤
│ More info │ https://www.npmjs.com/advisories/1092972 │
└───────────────┴──────────────────────────────────────────────────────────────┘
78 vulnerabilities found - Packages audited: 1848
Severity: 2 Low | 47 Moderate | 20 High | 9 Critical
✨ Done in 6.86s.
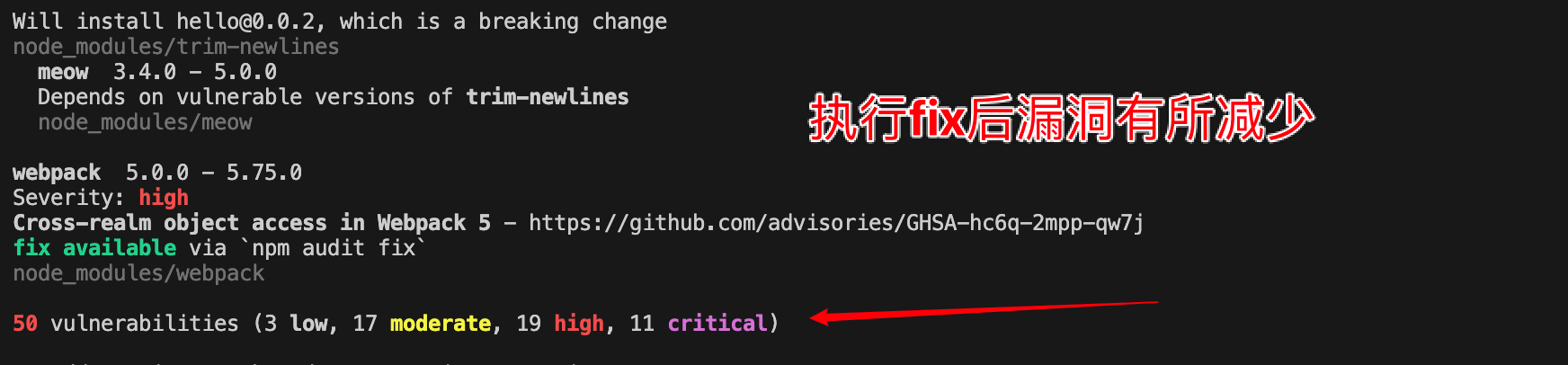
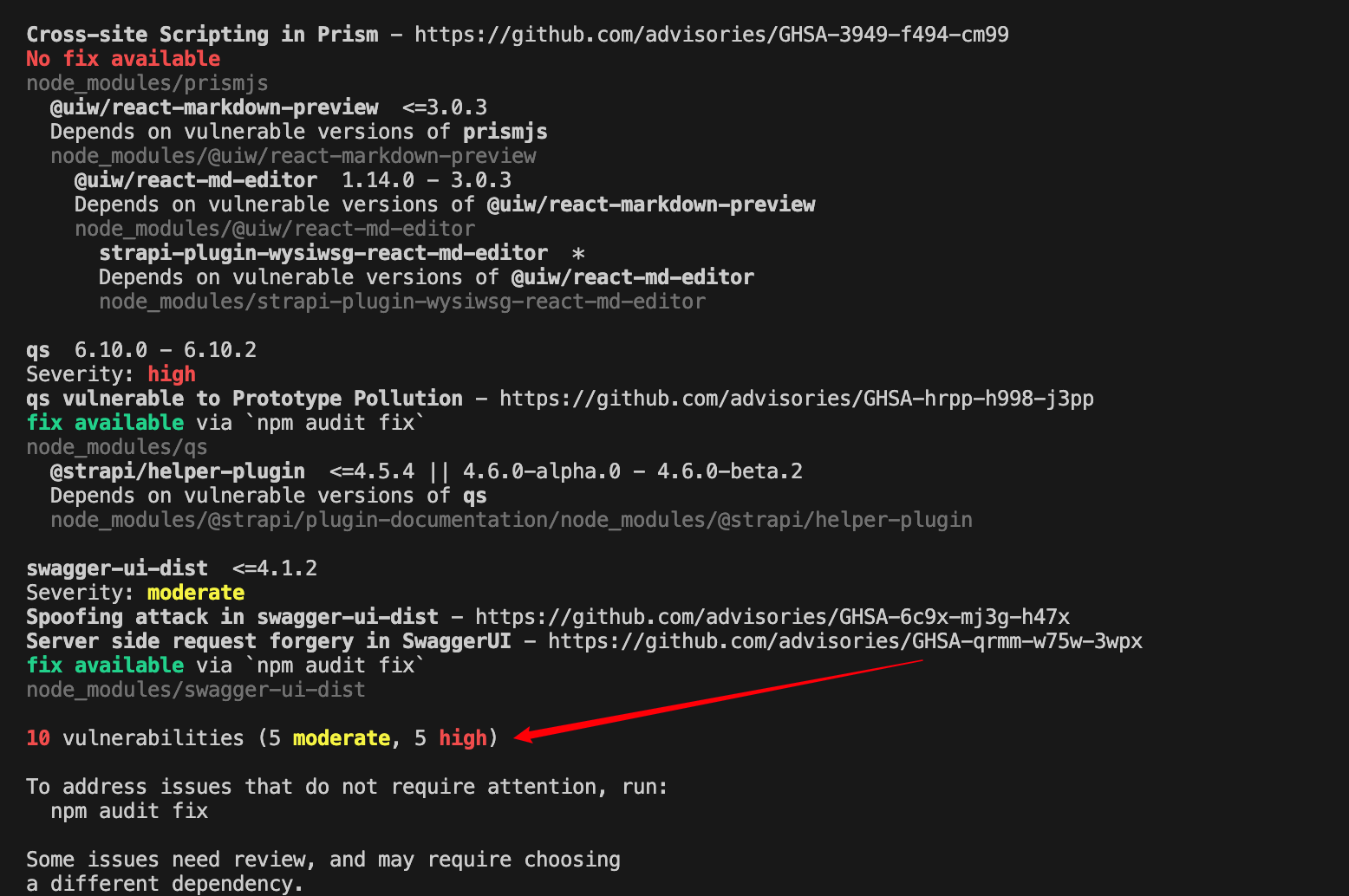
修复漏洞
扫描项目漏洞把不安全的依赖项自动更新到兼容性版本
npm audit fix
问题5:npm audit 报错 npm WARN audit 501 Method Not Implemented
npm WARN audit 501 Method Not Implemented - POST https://registry.npmmirror.com/-/npm/v1/security/audits/quick - [NOT_IMPLEMENTED] /-/npm/v1/security/audits/quick not implemented yet
{
error: '[NOT_IMPLEMENTED] /-/npm/v1/security/audits/quick not implemented yet'
}
npm ERR! audit endpoint returned an error
解决方案(可以直接尝试方案3)
如果是因为版本问题导致的,我们就需要升级版本,如果不是版本问题,我们需要采用其他方案解决哦~
方案1.升级npm版本
npm install -g npm
方案2.清空npm缓存
npm cache clean --force
方案3.更改npm registry
1. 切换为官方源
npm install -g nrm
nrm use npm
2. 查看漏洞
npm audit
3. 修复漏洞
npm audit fix
4. 下面命令慎重使用:强制解决漏洞
--force是一个危险的选择,因为它会升级依赖项而不考虑任何规则。例如,这可能导致依赖关系从一个版本转到另一个1.2.0版本2.3.0。这意味着您在项目中使用的函数可能不再存在或具有不同的行为,从而有效地破坏了您的应用程序。
npm audit fix --force
小伙伴们,先写到这里啦,我们明天再见啦~~
大家要天天开心哦
欢迎大家指出文章需要改正之处~
学无止境,合作共赢





