files_exploit翻译脚本
使用有道云翻译接口对exploit csv文件内容进行翻译
翻译最终结果存储到 sqlite 数据中,脚本所在目录下的db/vuln.db
# -*- coding: utf-8 -*-
"""
@author:随时静听
@file: getExpInfo.py
@time: 2019/03/29
@email:d1314ziting@163.com
"""
import sqlite3
import os
import requests
import time
import json
import random
import csv
# db 配置
DB_FILE='db/vulnDB.db'
TABLE_NAME='vuln'
TABLE='''
create table if not exists {}(id INTEGER primary key AUTOINCREMENT,
vuln_id CHAR(10) not null,
poc varchar(200),
descprition varchar(200),
time varchar(50),
author varchar(50),
type varchar(50),
platform varchar(20),
port varchar(10) DEFAULT ""
)
'''.format(TABLE_NAME)
def iniEnv(db_file=DB_FILE,table=TABLE):
'''
初始化环境
:return:
'''
if not os.path.exists(db_file):
path=os.path.dirname(db_file)
try:
os.makedirs(path)
except:
pass
conn=sqlite3.connect(DB_FILE)
cursor=conn.cursor()
cursor.execute(table)
return conn
def is_exists(vuln_id,conn,t_name=TABLE_NAME):
'''
判断是否已经存在数据
:param vuln_id:
:param cursor:
:param t_name:
:return:
'''
cursor=conn.cursor()
sql='select * from {} WHERE vuln_id=?'.format(t_name)
cursor.execute(sql,(str(vuln_id),))
result=cursor.fetchall()
cursor.close()
if len(result)>0:
return True
else:
return False
def insert(line,conn,t_name=TABLE_NAME):
'''
插入数据
:param line:
:param coursor:
:param t_name:
:return:
'''
cursor=conn.cursor()
try:
if line and cursor and t_name:
sql=''' insert into {}(vuln_id,poc,descprition,time,author,type,platform,port) VALUES (?,?,?,?,?,?,?,?)'''.format(t_name)
cursor.execute(sql,line)
conn.commit()
cursor.close()
return True
else:
print "[!] 数据插入失败!"
return False
except:
print "[!] 数据插入出错:",line
return None
def translate(word):
# 有道词典 api
url = 'http://fanyi.youdao.com/translate?smartresult=dict&smartresult=rule'
# 传输的参数,其中 i 为需要翻译的内容
tim_str=int(time.time()*1000)
headers={
"Origin":"http://fanyi.youdao.com",
"Referer":"http://fanyi.youdao.com/",
"User-Agent":"Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/73.0.3683.86 Safari/537.36",
"Content-Type": "application/x-www-form-urlencoded;charset=UTF-8",
}
key = {
'type': "AUTO",
'from':'en',
'to':'zh-CHS',
'i': word,
"doctype": "json",
"version": "2.1",
"keyfrom": "fanyi.web",
"ue": "UTF-8",
# "salt":str(tim_str),
# 'ts':str(int(time.time()/10)-random.randint(3,10)),
'ts':str(tim_str/10),
# "action": "FY_BY_CLICKBUTTON",
"action": "FY_BY_REALTlME",
"typoResult": "false"
}
# key 这个字典为发送给有道词典服务器的内容
response = requests.post(url, data=key,headers=headers)
# 判断服务器是否相应成功
if response.status_code == 200:
# 然后相应的结果
return response.text
else:
print("有道词典调用失败")
# 相应失败就返回空
return None
def get_translate_result():
conn=iniEnv()
cursor=conn.cursor()
for i, line in enumerate(csv.reader(open('files_exploits.csv', 'rb'))):
if i == 0:
continue
print line
if line[0] and (not is_exists(line[0],conn)) and line[0].isdigit():
word = translate(line[2])
time.sleep(random.randint(2, 5))
word = json.loads(word)
try:
word = word.get("translateResult")[0][0].get('tgt')
line[2] = word
insert(line, conn)
pass
except:
word = ""
print word
conn.close()
print "[-] Completed!"
if __name__ == '__main__':
get_translate_result()
有道云web防护破解方法
- 抓包分析,一旦修改i的参数值就返回不了正确的翻译结果
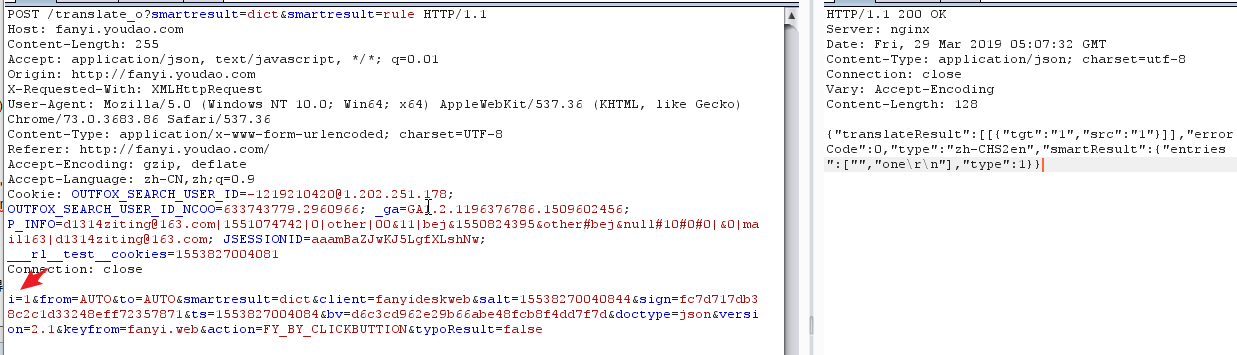
- 请求的内容被加密了,由salt,sign,来控制
- 真正加密方式应该时在翻译按钮上js中,由于js文件被处理过,就没倒腾,直接拿到网上现成的
def get_md(self, value):
'''md5加密'''
m = hashlib.md5()
# m.update(value)
m.update(value.encode('utf-8'))
return m.hexdigest()
def get_salt(self):
'''根据当前时间戳获取salt参数'''
s = int(time.time() * 1000) + random.randint(0, 10)
return str(s)
def get_sign(self):
'''使用md5函数和其他参数,得到sign参数'''
s = "fanyideskweb" + self.msg + self.salt + self.D
return self.get_md(s)
**破解 sign 参数加密反爬机制详细介绍:https://tendcode.com/article/youdao-spider/



 浙公网安备 33010602011771号
浙公网安备 33010602011771号